- What's New
- Function Overview
- Service Overview
- Billing
- Getting Started
-
User Guide
- Key Management Service
- Cloud Secret Management Service
- Key Pair Service
- Dedicated HSM
- Tag Management
- Auditing Logs
- Sharing
- Permission Control
-
Best Practices
- Key Management Service
- Cloud Secret Management Service
- General
- KMS Best Practices
- CSMS Best Practices
-
API Reference
- Before You Start
- Calling APIs
- API Overview
-
APIs
- Key Management APIs
-
Key Pair Management APIs
-
Key Pair Management
- Creating and Importing an SSH Key Pair
- Accessing the page for clearing private keys
- Querying the SSH Key Pair List
- Querying SSH Key Pair Details
- Deleting an SSH Key Pair
- Updating SSH Key Pair Description
- Accessing the page for importing private keys
- Exporting a private key
- Importing SSH Key Pairs in Batches
- Exporting Private Keys of Key Pairs in Batches
- Key pair task management
-
Key Pair Management
- Secret Management APIs
- Historical APIs
- Application Examples
- Permissions Policies and Supported Actions
- Appendix
- SDK Reference
-
FAQs
-
KMS Related
- What Is Key Management Service?
- What Is a Customer Master Key?
- What Is a Default Key?
- What Are the Differences Between a Custom Key and a Default Key?
- What Is a Data Encryption Key?
- Why Cannot I Delete a CMK Immediately?
- Which Cloud Services Can Use KMS for Encryption?
- How Do Huawei Cloud Services Use KMS to Encrypt Data?
- What Are the Benefits of Envelope Encryption?
- Is There a Limit on the Number of Custom Keys That I Can Create on KMS?
- Can I Export a CMK from KMS?
- Can I Decrypt My Data if I Permanently Delete My Custom Key?
- How Do I Use the Online Tool to Encrypt or Decrypt Small Volumes of Data?
- Can I Update CMKs Created by KMS-Generated Key Materials?
- When Should I Use a CMK Created with Imported Key Materials?
- What Should I Do When I Accidentally Delete Key Materials?
- How Are Default Keys Generated?
- What Should I Do If I Do Not Have the Permissions to Perform Operations on KMS?
- Why Can't I Wrap Asymmetric Keys by Using -id-aes256-wrap-pad in OpenSSL?
- Key Algorithms Supported by KMS
- What Should I Do If KMS Failed to Be Requested and Error Code 401 Is Displayed?
- What Is the Relationship Between the Ciphertext and Plaintext Returned by the encrypt-data API?
- How Does KMS Protect My Keys?
- How Do I Use an Asymmetric Key to Verify the Signature Result of a Public Key Pair?
- Does an Imported Key Support Rotation?
- Does KMS Support Offline Data Encryption and Decryption?
- How Do I Convert an Original EC Private Key into a Private Key in PKCS8 Format?
- CSMS Related
-
KPS Related
- How Do I Create a Key Pair?
- What Are a Private Key Pair and an Account Key Pair?
- How Do I Handle an Import Failure of a Key Pair Created Using PuTTYgen?
- What Should I Do When I Fail to Import a Key Pair Using Internet Explorer 9?
- How Do I Log In to a Linux ECS with a Private Key?
- How Do I Use a Private Key to Obtain the Password to Log In to a Windows ECS?
- How Do I Handle the Failure in Binding a Key Pair?
- How Do I Handle the Failure in Replacing a Key Pair?
- How Do I Handle the Failure in Resetting a Key Pair?
- How Do I Handle the Failure in Unbinding a Key Pair?
- Do I Need to Restart Servers After Replacing Its Key Pair?
- How Do I Enable the Password Login Mode for an ECS?
- How Do I Handle the Failure in Logging In to ECS After Unbinding the Key Pair?
- What Should I Do If My Private Key Is Lost?
- How Do I Convert the Format of a Private Key File?
- Can I Change the Key Pair of a Server?
- Can a Key Pair Be Shared by Multiple Users?
- How Do I Obtain the Public or Private Key File of a Key Pair?
- What Can I Do If an Error Is Reported When an Account Key Is Created or Upgraded for the First Time?
- Will the Account Key Pair Quota Be Occupied After a Private Key Pair Is Upgraded to an Account Key Pair?
- Why Is the Private Key Pair Invisible After It Is Upgraded to an Account Key Pair When Logging in as a Federated User?
-
Dedicated HSM Related
- What Is Dedicated HSM?
- How Does Dedicated HSM Ensure the Security for Key Generation?
- Do Equipment Room Personnel Has the Super Administrator Role to Steal Information by Using a Privileged UKey?
- What HSMs Are Used for Dedicated HSM?
- What APIs Does Dedicated HSM Support?
- How Do I Enable Public Access to a Dedicated HSM Instance?
- Pricing
-
General
- What Functions Does DEW Provide?
- What Cryptography Algorithms Does DEW Use?
- In Which Regions Are DEW Services Available?
- What Is a Quota?
- What Is the Resource Allocation Mechanism of DEW?
- What Are Regions and AZs?
- Can DEW Be Shared Across Accounts?
- How Do I Access the Functions of DEW?
- Why Do DEW Pemissions Fail to Take Effect Immediately?
-
KMS Related
- Videos
-
More Documents
- User Guide (ME-Abu Dhabi Region)
- User Guide (Paris and Amsterdam Regions)
-
User Guide (Kuala Lumpur Region)
- Service Overview
-
User Guide
- Key Management Service
- Cloud Secret Management Service
- Auditing Logs
- Permission Control
-
FAQs
-
KMS Related
- What Is Key Management Service?
- What Is a Customer Master Key?
- What Is a Default Key?
- What Are the Differences Between a Custom Key and a Default Key?
- What Is a Data Encryption Key?
- Why Cannot I Delete a CMK Immediately?
- Which Cloud Services Can Use KMS for Encryption?
- How Do Cloud Services Use KMS to Encrypt Data?
- What Are the Benefits of Envelope Encryption?
- Is There a Limit on the Number of Custom Keys That I Can Create on KMS?
- Can I Export a CMK from KMS?
- Can I Decrypt My Data if I Permanently Delete My Custom Key?
- How Do I Use the Online Tool to Encrypt or Decrypt Small Volumes of Data?
- Can I Update CMKs Created by KMS-Generated Key Materials?
- When Should I Use a CMK Created with Imported Key Materials?
- What Types of Keys Can I Import?
- What Should I Do When I Accidentally Delete Key Materials?
- How Are Default Keys Generated?
- What Should I Do If I Do Not Have the Permissions to Perform Operations on KMS?
- Why Can't I Wrap Asymmetric Keys by Using -id-aes256-wrap-pad in OpenSSL?
- Key Algorithms Supported by KMS
- What Should I Do If KMS Failed to Be Requested and Error Code 401 Is Displayed?
- What Is the Relationship Between the Ciphertext and Plaintext Returned by the encrypt-data API?
- How Does KMS Protect My Keys?
- Credential Related
-
KMS Related
- Change History
-
API Reference (ME-Abu Dhabi Region)
- Before You Start
- Calling APIs
- API Overview
-
APIs
- Creating a CMK
- Enabling a CMK
- Disabling a CMK
- Scheduling the Deletion of a CMK
- Canceling the Scheduled Deletion of a CMK
- Querying the List of CMKs
- Querying the Information About a CMK
- Creating a Random Number
- Creating a DEK
- Creating a Plaintext-Free DEK
- Encrypting a DEK
- Decrypting a DEK
- Querying the Number of Instances
- Querying the Quota of a User
- Changing the Alias of a CMK
- Changing the Description of a CMK
- Encrypting Data
- Decrypting Data
- Obtaining CMK Import Parameters
- Importing CMK Material
- Deleting CMK Material
- Querying CMK Instances
- Querying CMK Tags
- Querying Project Tags
- Adding or Deleting CMK Tags in Batches
- Adding a CMK Tag
- Deleting a CMK Tag
- Permissions Policies and Supported Actions
- Appendix
- Change History
-
API Reference (Paris and Amsterdam Regions)
- Before You Start
- Calling APIs
- API Overview
-
APIs
- Creating a CMK
- Enabling a CMK
- Disabling a CMK
- Scheduling the Deletion of a CMK
- Canceling the Scheduled Deletion of a CMK
- Querying the List of CMKs
- Querying the Information About a CMK
- Creating a Random Number
- Creating a DEK
- Creating a Plaintext-Free DEK
- Encrypting a DEK
- Decrypting a DEK
- Querying the Number of Instances
- Querying the Quota of a User
- Changing the Alias of a CMK
- Changing the Description of a CMK
- Creating a Grant
- Revoking a Grant
- Retiring a Grant
- Querying Grants on a CMK
- Querying Grants That Can Be Retired
- Encrypting Data
- Decrypting Data
- Obtaining CMK Import Parameters
- Importing CMK Material
- Deleting CMK Material
- Enabling Rotation for a CMK
- Changing the Rotation Interval for a CMK
- Disabling Rotation for a CMK
- Querying the Rotation Status of a CMK
- Appendix
- Change History
-
API Reference (Kuala Lumpur Region)
- Before You Start
- Calling APIs
- API Overview
-
APIs
- Creating a CMK
- Enabling a CMK
- Disabling a CMK
- Scheduling the Deletion of a CMK
- Canceling the Scheduled Deletion of a CMK
- Querying the List of CMKs
- Querying the Information About a CMK
- Creating a Random Number
- Creating a DEK
- Creating a Plaintext-Free DEK
- Encrypting a DEK
- Decrypting a DEK
- Querying the Number of Instances
- Querying the Quota of a User
- Changing the Alias of a CMK
- Changing the Description of a CMK
- Creating a Grant
- Revoking a Grant
- Retiring a Grant
- Querying Grants on a CMK
- Querying Grants That Can Be Retired
- Encrypting Data
- Decrypting Data
- Obtaining CMK Import Parameters
- Importing CMK Material
- Deleting CMK Material
- Enabling Rotation for a CMK
- Changing the Rotation Interval for a CMK
- Disabling Rotation for a CMK
- Querying the Rotation Status of a CMK
- Appendix
- Change History
- General Reference
Copied.
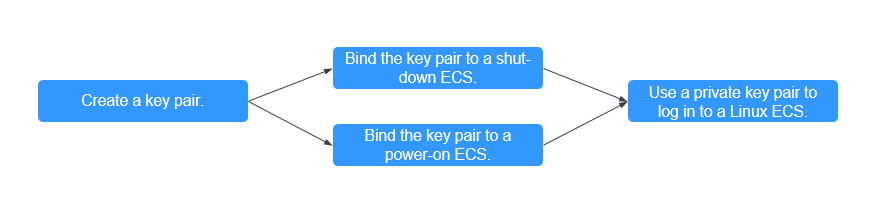
Binding a Key Pair and Logging In to an ECS Using a Private Key
A key pair, including one public key and one private key, are generated based on a cryptographic algorithm. The public key is automatically saved in Key Pair Service (KPS), while the private key can be saved to the user's local host. If you have configured the public key in a Linux ECS, you can use the private key to log in to the ECS for better security.
This section describes how to bind a key pair and log in to an ECS using a private key.
Procedure
The following uses an SSH_RSA_2048 key pair as an example to describe how to create a key pair and use the key to log in to an ECS. The following figure shows the process.
|
Procedure |
Description |
|---|---|
|
Register a Huawei ID, enable Huawei Cloud services, top up the account, and grant KPS permissions to the account. |
|
|
Create a key pair and select the key pair type. |
|
|
Bind a key pair to the ECS. |
|
|
After the key pair is bound, use the private key to log in to the ECS. |
Preparations
- Before creating key pair, register a Huawei Cloud account and enable Huawei Cloud services. For details, see Signing up for a Huawei ID and Enabling Huawei Cloud Services and Real-Name Authentication.
If you have enabled Huawei Cloud services and completed real-name authentication, skip this step.
- An ECS has been created. For details, see Purchasing a Custom ECS.
The SSH port (22 by default) of the ECS security group must allow traffic from the 100.125.0.0/16 CIDR block in advance. For details about ports and CIDR blocks, see Enhancing Security for SSH Logins to Linux ECSs.
- You have created an encryption key on KMS.
- The default key is kps/default.
- Select the custom keys created on KMS. For details, see Creating a Key.
Step 1: Creating a Key Pair
- Log in to the management console. Click
 on the left and choose Security & Compliance > Data Encryption Workshop.
on the left and choose Security & Compliance > Data Encryption Workshop. - In the navigation pane on the left, choose Key Pair Service. Click the Private Key Pairs tab and click Create Key Pair in the upper left corner.
- Configure the parameters as follows:
- Type: Choose SSH_RSA_2048.
- Select I agree to manage the private key of the key pair.
- KMS Encryption Key: Choose the default key or a created key from the list.
- Select I have read and agree to the Key Pair Service Disclaimer.
- Click OK. The private key file is downloaded automatically. When a message is displayed, indicating that the download is complete, save the private key file.
- Log in to the management console. Click
 on the left and choose Security & Compliance > Data Encryption Workshop.
on the left and choose Security & Compliance > Data Encryption Workshop. - In the navigation pane on the left, choose Key Pair Service. In the ECS List tab, locate the target ECS in the Shut down state, and click Bind in the Operation column.
- Configure the parameters as follows:
- New Key Pair: Choose the target key pair from the drop-down list.
- Select Disable the password login mode.
- Select I have read and agree to the Key Pair Service Disclaimer.
- Click OK.
- Log in to the management console. Click
 on the left and choose Security & Compliance > Data Encryption Workshop.
on the left and choose Security & Compliance > Data Encryption Workshop. - In the navigation pane on the left, choose Key Pair Service. In the ECS List tab, locate the target ECS in the Running state, and click Bind in the Operation column.
- Configure the parameters as follows:
- New Key Pair: Choose the target key pair from the drop-down list.
- Enter the password of user root.
- The default port is 22.
- Select Disable the password login mode.
- Select I have read and agree to the Key Pair Service Disclaimer.
- Click OK.
- Log in to the management console. Click
 on the left and choose Security & Compliance > Data Encryption Workshop.
on the left and choose Security & Compliance > Data Encryption Workshop. - In the navigation pane on the left, choose Key Pair Service. In the ECS List tab, locate the target ECS in the Shut down state, and click Bind in the Operation column.
- Configure the parameters as follows:
- New Key Pair: Choose the target key pair from the drop-down list.
- Select Disable the password login mode.
- Select I have read and agree to the Key Pair Service Disclaimer.
- Click OK.
- Log in to the management console. Click
 on the left and choose Security & Compliance > Data Encryption Workshop.
on the left and choose Security & Compliance > Data Encryption Workshop. - In the navigation pane on the left, choose Key Pair Service. In the ECS List tab, locate the target ECS in the Running state, and click Bind in the Operation column.
- Configure the parameters as follows:
- New Key Pair: Choose the target key pair from the drop-down list.
- Enter the password of user root.
- The default port is 22.
- Select Disable the password login mode.
- Select I have read and agree to the Key Pair Service Disclaimer.
- Click OK.
Step 3: Logging in to an ECS Using a Private Key
- Check whether the private key file has been converted to .ppk format.
- If yes, log in to the ECS server.
- If no, perform the following operations to convert the format of the private key file and then log in to ECS.
Open the third-party PuTTY, import the .pem private key file, and export the converted .ppk private key file.
Figure 2 Converting the format of the private key file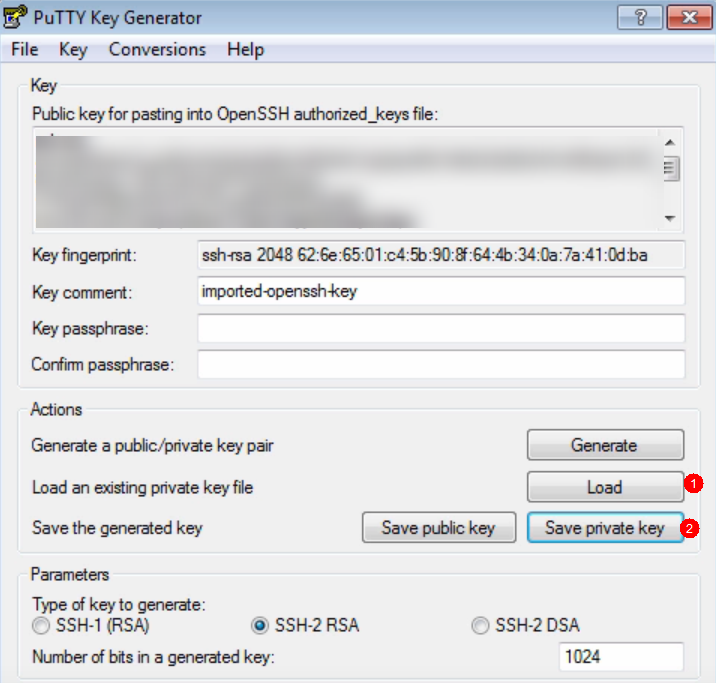
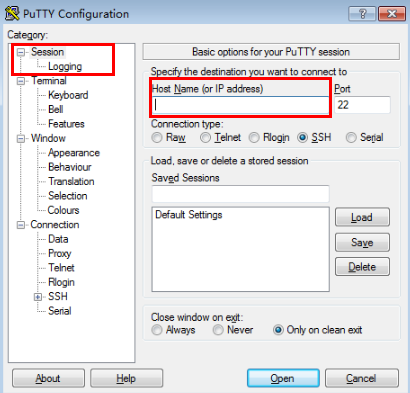
- Use PuTTY to log in to ECS.
- Enter the IP address of the ECS. Port 22 is used by default.
Figure 3 IP address of ECS
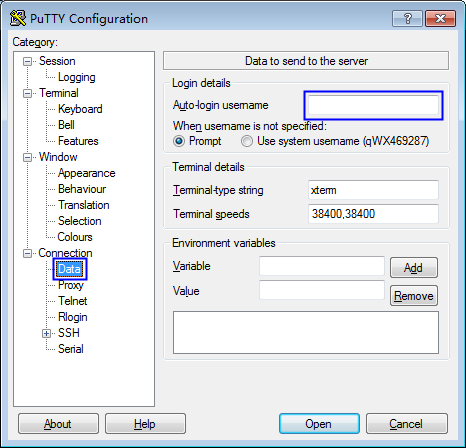
- Enter the username of the ECS image.
Figure 4 Username
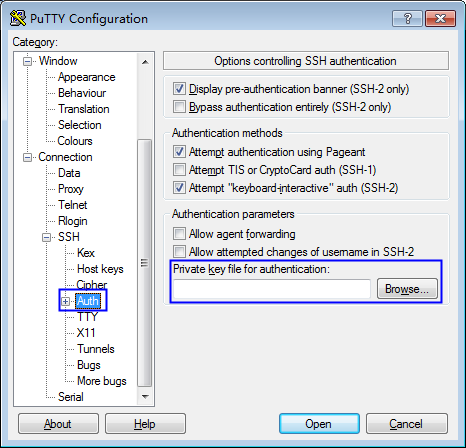
- Upload the private key file in .ppk format.
Figure 5 Uploading the private key file
- Click Open.
- Enter the IP address of the ECS. Port 22 is used by default.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





