How Do I Troubleshoot an Unhealthy Backend Server?
Symptom
If a client cannot access a backend server through a load balancer, the backend server is declared unhealthy. You can view the health check results for a backend server on the ELB console.
On the Load Balancers page, click the name of the load balancer to view its details. Click Backend Server Groups and locate the server group. You can find the health check results for backend servers in the Basic Information area.
Background
Load balancers use the IP addresses from the backend subnet where the load balancers work to send heartbeat requests to backend servers. To ensure that health checks can be performed normally, you need to ensure that the IP addresses from the backend subnet where the load balancers work are allowed to access the backend servers.

- Ensure that security group rules allow access from IP addresses in the backend subnet where the backend server resides.
- If IP as a Backend is not enabled for a load balancer and a TCP or UDP listener is added to the load balancer, there is no need to configure security group rules to allow traffic from the VPC where the load balancer backend subnet works to the backend servers associated with TCP or UDP listener.
If a backend server is considered unhealthy, ELB will not route traffic to it until it is declared healthy again.
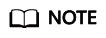
Troubleshooting
Possible causes are described here in order of how likely they are to occur.
Check these causes one by one until you find the cause of this issue.
It takes a while for the modification to take effect after you change the health check configuration. The required time depends on health check interval and timeout duration. You can view the health check result in the backend server list of target load balancer.
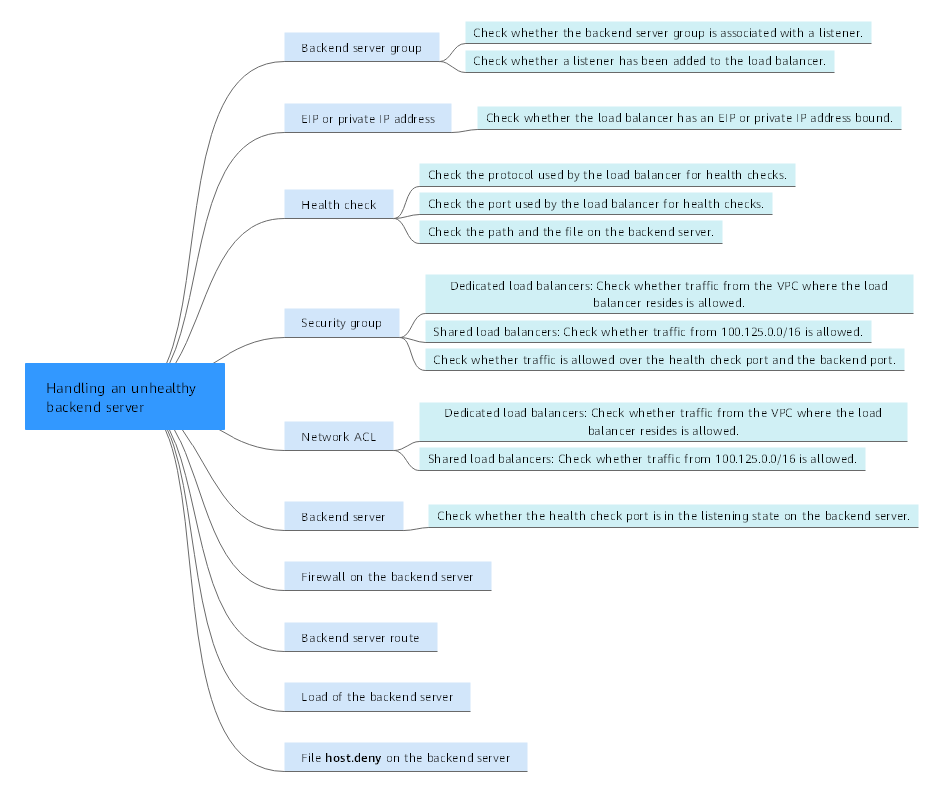
|
Possible Cause |
Solution |
|---|---|
|
Backend server group |
Checking Whether the Backend Server Group Is Associated with a Listener |
|
EIP or private IP address |
Checking Whether an EIP or a Private IP Address Is Bound to the Load Balancer |
|
Health check configuration |
|
|
Security group rules |
|
|
Network ACL rules |
|
|
Backend server listening configuration |
|
|
Network ACL rules |
|
|
Backend server route |
|
|
Backend server load |
|
|
Backend server host.deny file |
Checking Whether the Backend Server Group Is Associated with a Listener
Check whether the backend server group that the unhealthy backend server belongs to is associated with a listener.
- If the backend server group is not associated with a listener, check whether a listener has been added to the load balancer.
- If there is a listener, associate the backend server group with the listener.
- If there are no listeners, add a listener. Select Use existing and then select the backend server group when you add the listener.
- If the backend server group has been associated with a listener, proceed with the following operations.
Checking Whether an EIP or a Private IP Address Is Bound to the Load Balancer
- Check this only when you add a TCP or UDP listener to the load balancer.
- If you add an HTTP or HTTPS listener to the load balancer, health checks will not be affected no matter whether an EIP or private IP address is bound to the load balancer.
If you add a TCP or UDP listener to the load balancer, check whether the load balancer has an EIP or private IP address bound.
If the load balancer has no EIP or private IP address bound, bind one.
When you create a load balancer for the first time, if no EIP or private IP address is bound to the load balancer, the health check result of backend servers associated with a TCP or UDP listener is Unhealthy. After you bind an EIP or private IP address to the load balancer, the health check result becomes Healthy. If you unbind the EIP or private IP address from the load balancer, the health check result is still Healthy.
Checking the Health Check Configuration
- Domain Name: If you use HTTP for health checks and the backend server is configured to verify the Host header, enter the domain name configured for the backend server.
- Protocol: The protocol used for health checks.
- Port: The port must be the one used on the backend server, and it cannot be changed. Check whether the health check port is in the listening state on the backend server. If it is not, the backend server will be identified as unhealthy.
- Check Path: If HTTP is used for health checks, you must check this parameter. A simple static HTML file is recommended.
- If the health check protocol is HTTP, the port and the path are used for health checks.
- If the health check protocol is TCP, only the port is used for health checks.
- If health check protocol is HTTP and the health check port is normal, change the path or change the health check protocol to TCP.
- Enter an absolute path.
If the URL is http://www.example.com or http://192.168.63.187:9096, enter / as the health check path.
If the URL is http://www.example.com/chat/try/, enter /chat/try/ as the health check path.
If the URL is http://192.168.63.187:9096/chat/index.html, enter /chat/index.html as the health check path.
Checking Security Group Rules
- TCP, HTTP, or HTTPS listeners: Verify that the inbound security group rule allows TCP traffic from the VPC where the load balancer works to the backend server over the health check port.
- If the health check port is the same as the backend port, the inbound rule must allow traffic over the backend port, for example, port 80.
- If the port (port 80 as an example) for health check is different from that used by the backend server (port 443 as an example), inbound security group rules must allow traffic over both ports.
You can check the protocol and port in the Basic Information area of the backend server group.
Figure 3 Example inbound rule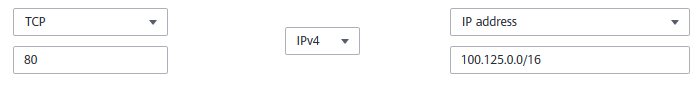
- UDP listeners: Verify that the inbound security group rule allows traffic from the VPC where the load balancer works to the backend server using the health check protocol and over the health check port. In addition, the rule must allow inbound ICMP traffic.
Figure 4 Example inbound rule that allows ICMP traffic
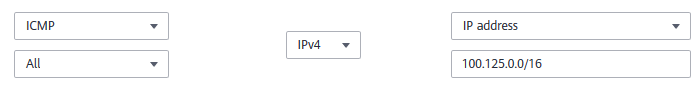
- If you are not sure about the security group rules, change the Protocol & Port to All for testing.
- For UDP listeners, see How Does ELB Perform UDP Health Checks? What Are the Precautions for UDP Health Checks?
Checking Network ACL Rules
To control traffic in and out of a subnet, you can associate a network ACL with the subnet. Network ACL rules control access to subnets and add an additional layer of defense to your subnets. Default network ACL rules reject all inbound and outbound traffic. If the subnet of a load balancer or associated backend servers has a network ACL associated, the load balancer cannot receive traffic from the Internet or route traffic to backend servers, and backend servers cannot receive traffic from and respond to the load balancer.
Configure an inbound network ACL rule to allow traffic from the VPC where the load balancer resides to backend servers.
Checking the Backend Server
If the backend server runs on Windows, use a browser to access https://{Backend server IP address}:{Health check port}. If a 2xx or 3xx code is returned, the backend server is running normally.
- Run the following command on the backend server to check whether the health check port is listened on:
netstat -anlp | grep port
If the health check port and LISTEN are displayed, the health check port is in the listening state. As shown in Figure 5, TCP port 880 is listened on.
If you do not specify a health check port, backend ports are used by default.Figure 6 Backend server port not listened on
If the health check port is not in the listening state, the backend server is not listened on. You need to start the application on the backend server and check whether the health check port is listened on.
- For HTTP health checks, run the following command on the backend server to check the status code:
curl Private IP address of the backend server:Health check port/Health check path -iv
To perform an HTTP health check, the load balancer initiates a GET request to the backend server. If the following response status codes are displayed, the backend server is considered healthy:
TCP listeners: 200
The status code is 200, 202, or 401 if the backend server is healthy.
Figure 7 Unhealthy backend server Figure 8 Healthy backend server
Figure 8 Healthy backend server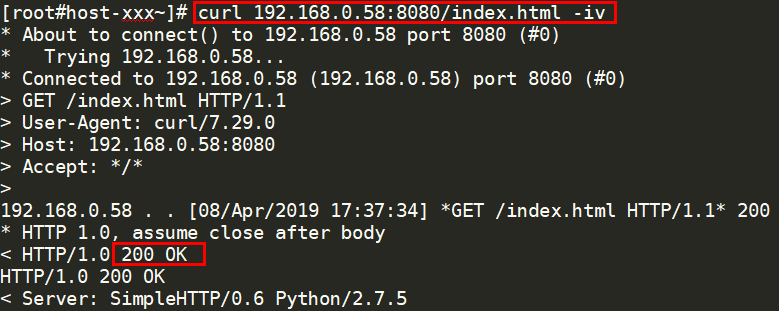
- If HTTP is used for health checks and the backend server is detected unhealthy, perform the following steps to configure a TCP health check:
On the Listeners tab page, modify the target listener, select the backend server group for which TCP health check has been configured, or add a backend server group and select TCP as the health check protocol. After you complete the configuration, wait for a while and check the health check result.
Checking the Firewall on the Backend Server
If the firewall or other security software is enabled on the backend server, the software may block the IP addresses in the backend subnet of the load balancer, or 100.125.0.0/16.
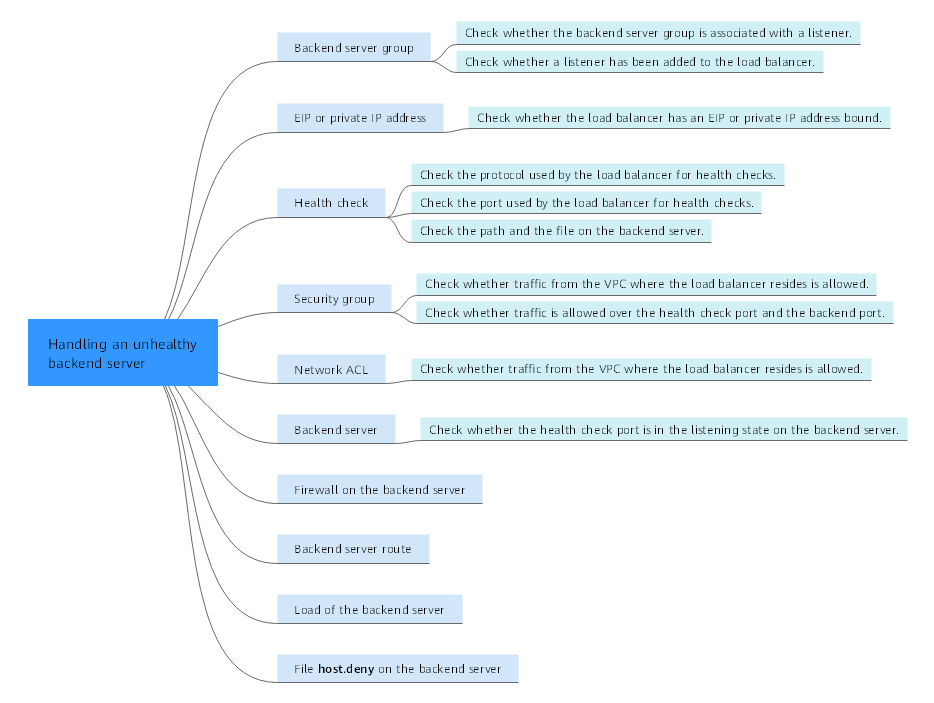
Checking the Backend Server Route
Check whether the default route configured for the primary NIC (for example, eth0) has been manually modified. If the default route is changed, health check packets may fail to reach the backend server.
ip route
Alternatively, run the following command:
route -n
Figure 9 shows the command output when the backend server route is normal.
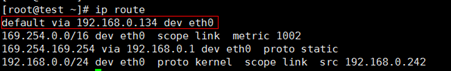
If the command output does not contain the first route, or the route does not point to the gateway, configure or modify the default route to point to the gateway.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot