Configuração de acesso entre CIDRs
Quando uma instância do conjunto de réplicas é conectada por meio de uma rede interna, um nó do conjunto de réplicas é configurado com uma NIC de gerenciamento (para receber instruções de gestão e comunicações internas da instância) e uma NIC de dados (para receber e responder a pedidos de serviço do cliente) e o mapeamento entre endereços IP de gerenciamento e endereços IP de dados de três blocos CIDR padrão é configurado por padrão.
- Se o cliente e a instância do conjunto de réplicas forem implementados em blocos CIDR diferentes e o bloco CIDR do cliente for 192.168.0.0/16, 172.16.0.0/12 ou 10.0.0.0/8, você não precisará configurar Access Across CIDR Blocks para a instância.
- Se o cliente e a instância do conjunto de réplicas forem implementados em blocos CIDR diferentes e o bloco CIDR do cliente não for 192.168.0.0/16, 172.16.0.0/12 ou 10.0.0.0/8, você pode configurar Access Across CIDR Blocks para que a instância se comunique com seu cliente.
- Nenhum segmento de rede padrão está configurado para instâncias do conjunto de réplicas criadas antes de setembro de 2021. Se o cliente e a instância do conjunto de réplicas forem implementados em diferentes segmentos de rede, será necessário configurar o acesso entre blocos CIDR para habilitar a conectividade de rede.
Esta seção descreve como configurar Access Across CIDR Blocks para uma instância.
Precauções
- Somente instâncias do conjunto de réplicas suportam essa função.
- Durante a configuração do acesso entre CIDRs, os serviços são executados corretamente sem interrupção ou desconexão intermitente.
- Se o cliente e a instância do conjunto de réplicas estiverem em VPCs e blocos CIDR diferentes, crie uma conexão de emparelhamento de VPC entre as VPCs e configure o acesso entre CIDRs.
Procedimento
- Faça logon no console de gerenciamento.
- Clique em
 no canto superior esquerdo e selecione uma região e um projeto.
no canto superior esquerdo e selecione uma região e um projeto. - Clique em
 no canto superior esquerdo da página e escolha Databases > Document Database Service.
no canto superior esquerdo da página e escolha Databases > Document Database Service. - Na página Instances, clique no nome da instância.
- No painel de navegação à esquerda, escolha Connections.
- Na guia Private Connection, clique em Enable à direita de Cross-CIDR Access. Você pode adicionar ou excluir os blocos conforme necessário.
- Clique em
 para adicionar novos blocos CIDR.
para adicionar novos blocos CIDR. - Clique em
 para excluir blocos CIDR existentes.
para excluir blocos CIDR existentes.
Figura 1 Acesso entre CIDRs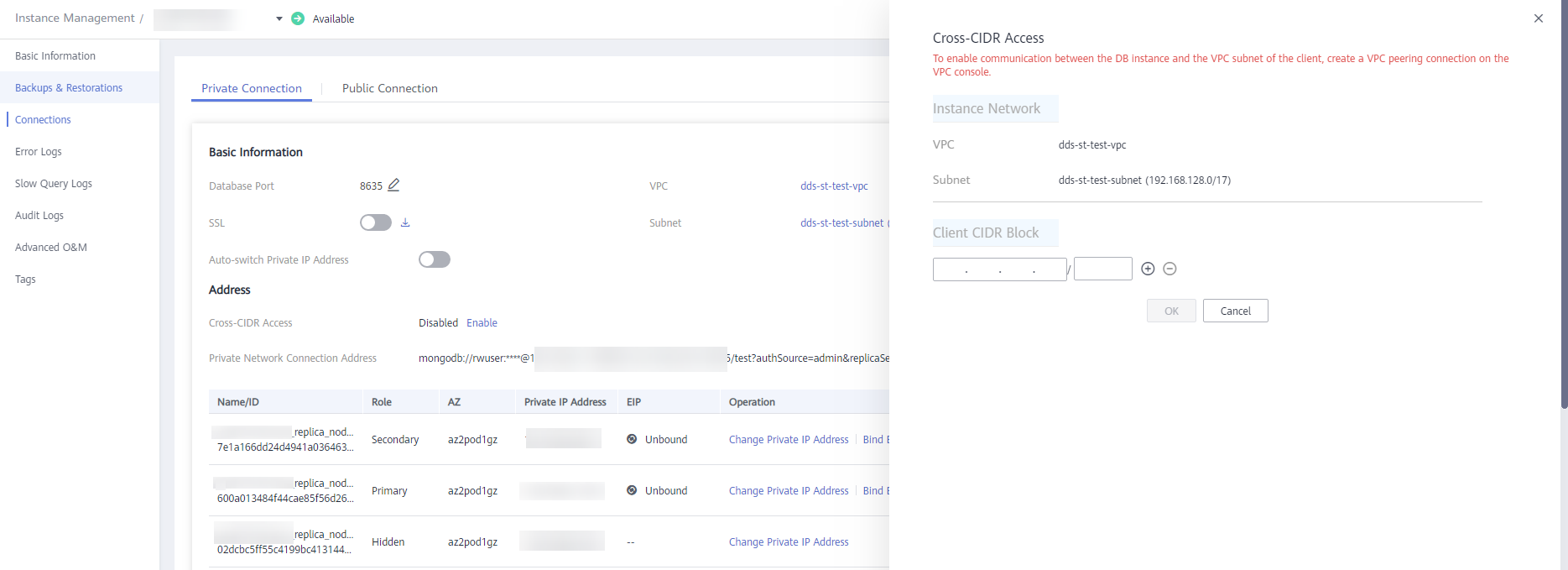
Até 30 blocos CIDR podem ser configurados, e cada um deles pode se sobrepor, mas eles não podem ser os mesmos. Ou seja, os blocos CIDR de origem podem se sobrepor, mas não pode ser o mesmo. Os blocos CIDR não podem começar com 127. A máscara de IP permitida varia de 8 a 32.
- Clique em
- Veja os resultados da alteração. Depois que o acesso CIDR cruzado é habilitado, Enabled é exibido à direita de Cross-CIDR Access.
Se você precisar alterar o bloco CIDR do cliente, clique em Change à direita de Cross-CIDR Access.
Figura 2 Alterar um bloco CIDR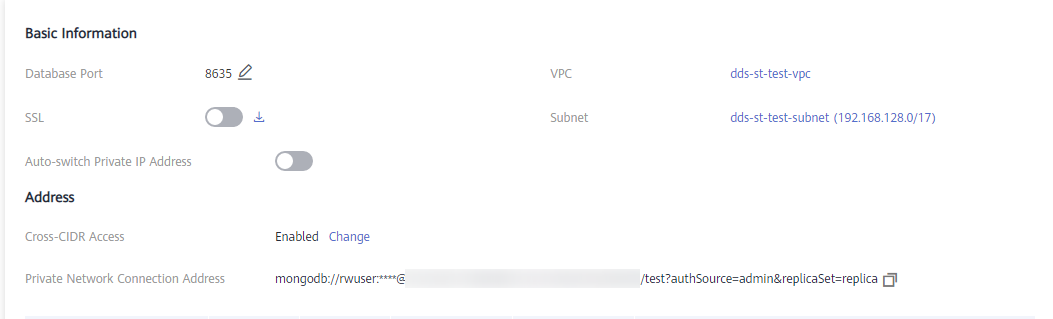
Operações de acompanhamento
Depois que o acesso entre CIDRs for configurado, você poderá usar o MongoShell para se conectar a uma instância do conjunto de réplicas em uma rede privada. Para obter detalhes, consulte Conexão a uma instância de cluster usando o Mongo Shell.






