Using CFW to Protect Enterprise Resources
Context
Huawei Cloud provides Enterprise Project Management Service (EPS) to help enterprises manage people, funds, resources, permissions, and services on the cloud, standardize enterprise operations on Huawei Cloud, and meet cloud IT governance requirements.
You can create enterprise projects based on your organizational structure to centrally manage resources in different regions. You can also grant different permissions to users and user groups in enterprise projects.
Application Scenarios
If a large enterprise wants to manage services by branch or department, but finds it difficult to divide bills and allocate resources, the enterprise can use EPS.
- Different services can be put under different enterprise projects. Bills are generated for each enterprise project, facilitating budget management and fee splitting.
- Enterprise projects can be assigned to users and user groups for refined resource management.
This section describes how to plan CFW when an enterprise manages services through EPS.
Resource and Cost Planning
|
Resource |
Description |
Quantity |
Cost |
|---|---|---|---|
|
Enterprise Project Management Service (EPS) |
EPS manages enterprise resources. |
At least 2 |
Free of charge |
|
Cloud Firewall (CFW) |
CFW protects cloud resources. |
At least 2 |
For details, see CFW Pricing Details. |
|
Elastic IP (EIP) |
(Optional) EIP, a type of cloud resource. |
Configure based on service demands. |
For details, see EIP Pricing Details. |
|
Virtual Private Cloud (VPC) |
(Optional) VPC, a type of cloud resource. |
Configure based on service demands. |
For details, see VPC Pricing Details. |
|
Enterprise Router |
(Optional) An enterprise router routes traffic between VPC and CFW. When CFW is used to protect VPCs, traffic diversion depends on Enterprise Router. |
At least 1 |
For details, see Enterprise Router Pricing Details. |
Example
An enterprise has services A and B on the cloud. Each service has a production team and a test team. The enterprise creates enterprise projects as follows:
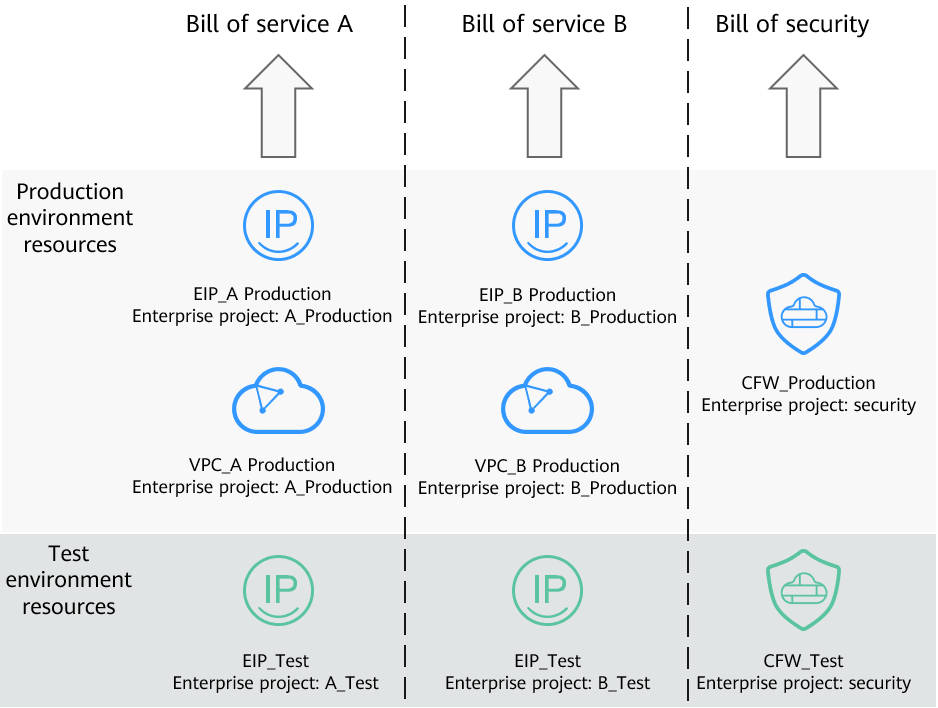
- To manage services A and B separately, the enterprise creates enterprise projects A_Production and A_Test for service A, and B_Production and B_Test for service B. Cloud resources are bound to the corresponding enterprise projects based on service teams during purchase.
- The enterprise creates an enterprise project named Security for the security department. When purchasing security products, the enterprise binds the products to Security so that the financial team can distinguish bills and manage security-related budget usage.
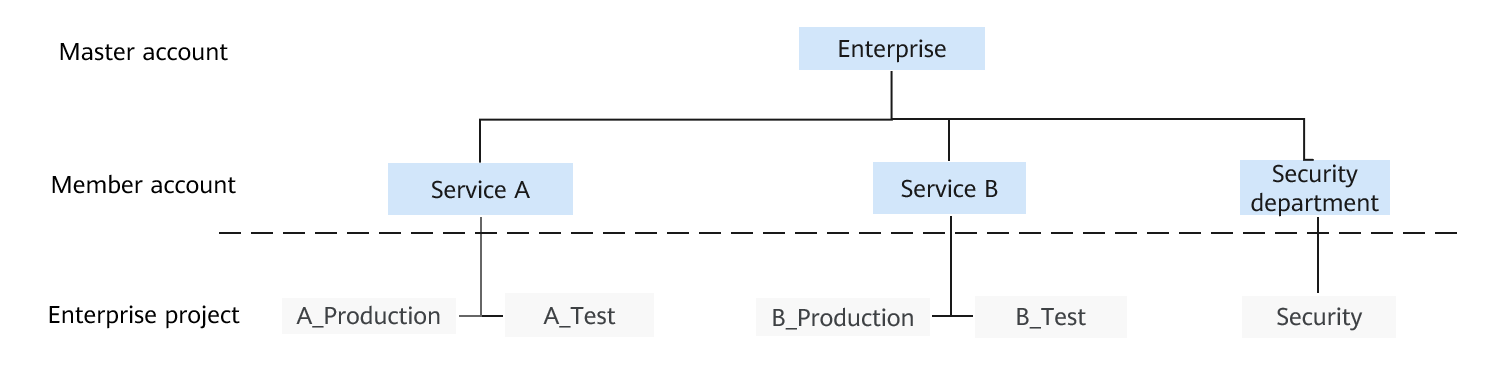
- To protect EIPs and VPCs in the production environment, the security administrator purchases the professional edition firewall.
- To protect EIPs in the test environment, the security administrator purchases the standard edition firewall.
In each environment, the firewall is shared by services A and B, and the bills are paid by the security department, as shown in Figure 2.
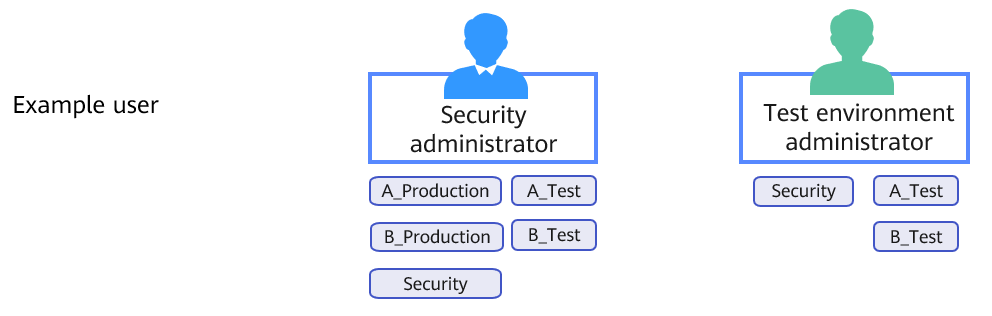
Enterprises can authorize member accounts by enterprise project in IAM to isolate the resources of different services. Take a security administrator and a test environment administrator as an example:
- The enterprise authorizes the security administrator to access all enterprise projects. The security administrator can view resources on both firewalls, configure different protection policies and security protection modes for the firewalls, and enable protection in different environments.
- On the CFW in the production environment, protection is enabled for the EIPs and VPCs in enterprise projects A_Production and B_Production.
- On the CFW in the test environment, protection is enabled for the EIPs in enterprise projects A_Test and B_Test.
- The enterprise authorizes the test environment administrator to manage A_Test, B_Test, and Security enterprise projects, but does not authorize the test administrator to manage resources (EIPs and VPCs) in the production environments. The test environment administrator can perform operations on the two firewalls under its account, and can only view the resource information in the test environments.
Related Operations
- For details about how to create an enterprise project, see Creating an Enterprise Project .
- For details about how to purchase a CFW, see Purchasing a CFW .
- For details about how to create and grant permissions to a user group using IAM, see Creating a User Group and Assigning Permissions. For details about how to grant permissions to a user using IAM, see Assigning Permissions to an IAM User.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot