Using CFW to Defend Against Access Control Attacks
You can use CFW to defend against access control attacks.
Application Scenarios
Access control is a key method to protect system resources from unauthorized access. It restricts users' or processes' access to system resources to enhance system security. Attackers may try to bypass or invalidate control measures to gain unauthorized access.
The IPS rule library of CFW provides rules to defend against access control attacks. It can effectively identify and block the behaviors that bypass or damage the system access control mechanism, reducing the risk of such attacks.
What Is an Access Control Attack?
In access control attacks, attackers exploit access control vulnerabilities in systems or applications to illegally obtain or elevate their access permissions in the systems or applications, perform unauthorized operations, or access sensitive resources.
Common access control attacks include:
- Unauthorized access attack
- Vertical privilege escalation: Common users can access or operate resources or functions that require administrator permissions.
- Horizontal privilege escalation: A user can access or operate resources or functions that only another user has permissions for.
- Multi-phase privilege escalation: In an operation that requires multiple steps (such as fund transfer), an attacker may skip steps and directly perform the last step.
- Password attack
- Brute-force attack: Attackers crack usernames and passwords by attempting all possible combinations, including pure brute-force attacks (blanket search) and dictionary-based brute-force attacks (using a password dictionary).
- Rainbow table attack: A batch processing dictionary attack implemented by searching the pre-generated password and hash string mapping table to crack the password.
- Session hijacking
An attacker obtains the session ID of a user, uses the session ID to log in to the target account, and performs unauthorized operations. This usually takes place when the user session identifier is leaked or predicted.
- Access aggregation attack
A method that is often used in in-depth testing. It collects multiple pieces of non-sensitive information, combines the information to obtain sensitive information, and compares the information to complete an attack.
Harms of Access Control Attacks
Access control attacks severely threaten system security. The major impacts are as follows:
- Data leakage: Attackers can bypass the access control mechanism to obtain sensitive data, such as personal information and financial data, without authorization.
- Data tampering: Attackers can bypass the access control mechanism to tamper with system data, generating false and unreliable data.
- System breakdown: Attackers can bypass the access control mechanism to obtain administrator rights in the system, causing the system to be damaged or crashed.
- Information security risks: Access control attacks damage the security mechanism in the system and increase information security risks, such as malware, virus, and Trojan attacks.
How to Defend Against Access Control Attacks
In addition to access control policy design, identity authentication, security audit and monitoring, security configuration and patch management, access control, vulnerability defense, security training and awareness improvement, and security technologies and tools, you can use the CFW intrusion prevention function to block access control attacks.
- Log in to the CFW console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - (Optional) Switch to another firewall instance. Select a firewall from the drop-down list in the upper left corner of the page.
- In the navigation pane, choose .
- Click View Effective Rules under Basic Protection.
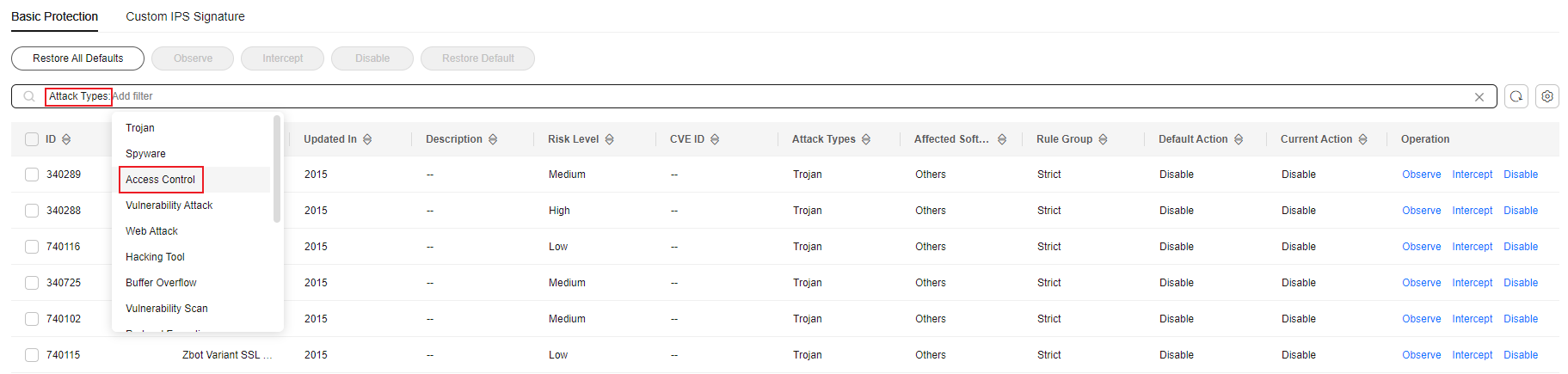
- Filter the rules for access control prevention. In the filter above the list, select Access-Control from the Attack Types drop-down list.
Figure 1 Access control
- Enable protection in batches. Select multiple rules at a time and click Intercept.
Intercept: The firewall records the traffic that matches the current rule in attack event logs and blocks the traffic.
- For details about how to view attack event logs, see Attack Event Logs.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





