Pay-per-Use Billing
Pay-per-use billing means you pay nothing up front and are not tied into any contract or commitment. Only CFW of professional edition supports the pay-per-use billing mode.
This section describes the billing rules for pay-per-use CFW resources.
Currently, the professional edition CFW can be purchased in pay-per-use mode only in certain regions. You can query the supported regions on the console.
Application Scenarios
Pay-per-use billing is good for short-term, bursty, or unpredictable workloads that cannot tolerate any interruptions, such as applications for e-commerce flash sales and temporary testing.
This mode applies to scenarios where the number of public network assets (EIPs to be protected) is less than 1,000 and the traffic is moderate (generally, the peak bandwidth is less than 1 Gbit/s).
Billed Items
Service edition: the purchased service edition. Only CFW of professional edition supports the pay-per-use billing mode.
Actual traffic (GB): total traffic generated during service usage.
Billed Usage Period
Pay-per-use CFW resources are billed by second. Bills are settled on each integer hour (UTC+ 08:00). After the settlement is complete, a new billing period starts. The billing starts when the CFW instance is launched and ends when the instance is deleted.
It takes a certain time to launch a CFW instance. The billing starts from the time when the CFW instance is successfully created.
For example, if you purchased a pay-per-use CFW of the professional edition at 8:45:30 and deleted it at 8:55:00, you are billed for the 600 seconds from 8:45:30 to 8:55:30.
Billing Examples
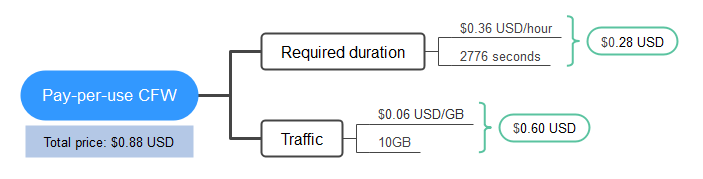
Suppose you purchased a pay-per-use CFW of the professional edition on April 18, 2024, 9:59:30 and deleted it on April 18, 2024, 10:45:46. During the usage period, a maximum of 10 GB traffic was generated. The billing resources include the service edition (professional edition) and the generated traffic (10 GB). Two usage periods will be billed:
- Usage of 30 seconds from 9:59:30 to 10:00:00 (between 9:00:00 and 10:00:00)
- Usage of 2,746 seconds from 10:00:00 to 10:45:46 (between 10:00:00 and 11:00:00)
You need to pay for each billing cycle. Each resource is billed separately. For details, see Formula. The prices displayed in the pricing details are per hour, so you need to divide them by 3,600 to obtain the prices per second.
|
Resource |
Formula |
|---|---|
|
Service edition |
Service edition x Required duration |
|
Actual traffic |
Used traffic x Unit price of the traffic |
Figure 1 shows the billing calculation.

The prices in the figure are examples only. The actual prices are those displayed on CFW Pricing Details.
Impact of Arrears
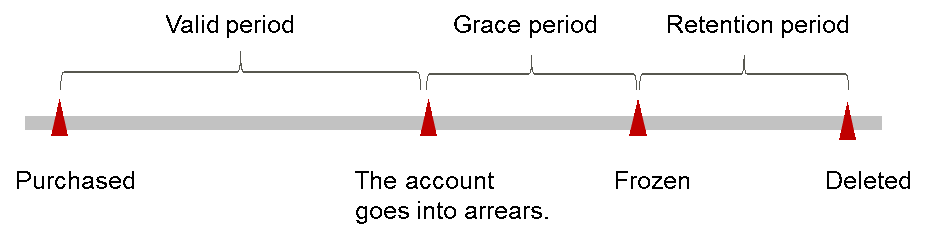
Figure 2 shows the statuses a pay-per-use CFW can have throughout its lifecycle. After a CFW is purchased, it enters the validity period and runs normally during this period. If your account goes into arrears, the CFW instance enters a grace period and then a retention period.
Arrears Reminder
The system will bill you for pay-per-use resources after each billing cycle ends. If your account is in arrears, we will notify you by email, SMS, or in-app message.
Impact of Arrears
Your account may fall into arrears if it cannot cover the bill you need to pay. In this case, relevant cloud services will not be stopped immediately. There will be a grace period for pay-per-use resources. You are still responsible for expenditures generated during the grace period. You can view the charges on the Billing Center > Overview page and pay any past due balance as needed.
If you do not bring your account current before the grace period expires, CFW resources turn to Frozen and enter a retention period. You cannot perform any operations on a pay-per-use CFW resource in the Frozen status.
If you do not bring your account balance current before the retention period ends, your CFW instance and protection configurations will be automatically deleted and data cannot be restored.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot