Enabling Internet Border Traffic Protection
CFW protects Internet border traffic by protecting EIPs. After EIP protection is enabled, your service traffic will pass through CFW. By default, all traffic is allowed.
After protection is enabled, you can configure an access control policy or IPS mode. CFW will block or allow traffic based on the configuration. For details about how to configure access control, see Configuring Protection Rules. For details about IPS, see Configuring Intrusion Prevention.
What Is Internet Border Traffic?
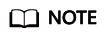
Internet border traffic, a type of north-south traffic, is exchanged between cloud assets and the Internet. It includes inbound traffic (from the Internet to cloud assets) and outbound traffic (from cloud assets to the Internet).
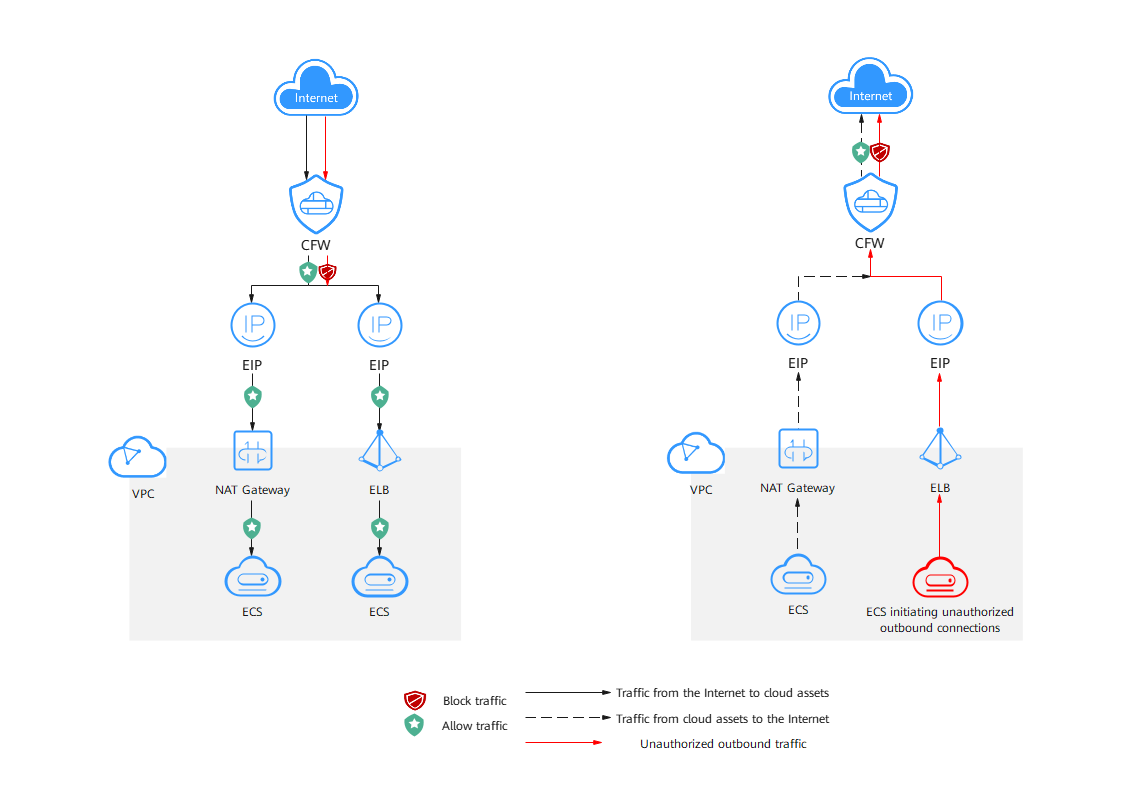
Introduction to Internet Border Traffic Protection
Protected Objects
ECSs, NAT gateways, ELBs, and other resources bound to EIPs.
Protection Specifications
The Internet border protection specifications include the number of protected EIPs and the Internet border protection bandwidth.
|
Specifications |
Description |
Yearly/Monthly Billing |
Pay-per-Use Billing |
|---|---|---|---|
|
Protected EIPs |
Total number of EIPs that can be protected by the current firewall instance. |
It depends on the number of added EIP protection quota you purchased. For details about the default quota, see Features. If the quota is insufficient, you can purchase an extension package. For details, see Modifying an Extension Package. |
Up to 1,000 EIPs, and up to 1 Gbit/s traffic protection for Internet and VPC borders are available. The capacities cannot be expanded. If you need higher protection bandwidth, submit a service ticket. |
|
Internet Border Protection Bandwidth |
Maximum Internet border traffic that can be protected by the current firewall instance. The value is the maximum inbound or outbound traffic. |
Constraints
- Currently, IPv6 addresses cannot be protected.
- An EIP can only be protected by one firewall.
- The number of EIPs that can be protected by a single firewall instance by default is as follows:
- Yearly/Monthly CFW:
- Standard edition: 20
- Professional edition: 50
You can purchase expansion packages to increase the number to a maximum of 2,000. For details, see Changing the Number of CFW Expansion Packages.
- Pay-per-use firewall (professional edition): 1,000. It cannot be increased.
- Yearly/Monthly CFW:
Impacts on Services
- If no protection rule or blacklist is configured to block all traffic, enabling or disabling EIP protection will not interrupt services.
- If there is a protection rule or blacklist in effect that blocks all traffic, enabling EIP protection may interrupt services. Before enabling protection, check for persistent connections and services that do not support session reestablishment.
- For details about how to edit a protection rule, see Managing Protection Rules.
- For details about how to edit a blacklist, see Managing the Blacklist and the Whitelist.
Enabling Internet Border Traffic Protection
- Log in to the CFW console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - (Optional) Switch to another firewall instance. Select a firewall from the drop-down list in the upper left corner of the page.
- In the navigation pane, choose . The EIPs page is displayed. The EIP information is automatically updated to the list.
- Enable EIP protection.
IPv6 protection is not supported for EIPs. An EIP can be protected by only one firewall.
- Enable protection for a single EIP: In the row of the EIP, click Enable Protection in the Operation column.
- Enable protection for multiple EIPs: Select the EIPs that you want to enable protection and click Enable Protection above the list.
- On the page that is displayed, check the information and click Bind and Enable. Then the Protection Status changes to Protected.
After EIP protection is enabled, the default action of the access control policy is Allow.
Auto-protecting New EIPs
If auto-protection on new EIPs is enabled, CFW automatically synchronizes EIPs on the hour and enables protection for new EIPs. The traffic of the EIPs will be protected by the firewall.
How to enable: Go to the Assets > EIPs page and enable Auto Protect New EIP.
- If you wait for CFW to automatically synchronize and protect new EIPs, all the new EIPs under all accounts (including the current account) will be protected.
- If you opened the page or call the API for querying EIPs before the automatic synchronization and protection, the EIPs under the current account will be automatically protected, but you will need to manually enable protection for the new EIPs under other accounts.
Follow-up Operations
- For details about how to view the traffic trend and statistics of CFW, see Traffic Analysis. For details about traffic records, see Traffic Logs.
- After protection is enabled, all traffic is allowed by default. CFW will block traffic based on the policies you configure.
- To implement traffic control, configure a protection policy. For details, see Configuring Protection Rules to Block or Allow Internet Border Traffic or Adding Blacklist or Whitelist Items to Block or Allow Traffic.
- Allow or block traffic based on protection rules.
- Traffic allowing rule: The allowed traffic will be checked by functions such as intrusion prevention system (IPS) and antivirus.
- Traffic blocking rule: Traffic will be directly blocked.
- Allow or block traffic based on the blacklist and whitelist:
- Whitelist: Traffic will be directly allowed without being checked by other functions.
- Blacklist: Traffic will be directly blocked.
- Allow or block traffic based on protection rules.
- For details about how to block network attacks, see Configuring Intrusion Prevention.
- To implement traffic control, configure a protection policy. For details, see Configuring Protection Rules to Block or Allow Internet Border Traffic or Adding Blacklist or Whitelist Items to Block or Allow Traffic.
Related Operations
- Disabling EIP protection

If EIP protection is disabled, CFW no longer protects the EIP traffic, and EIPs may be exposed to attacks. Exercise caution when performing this operation.
- To disable an EIP, click Disable Protection in the column of the EIP.
- To disable multiple EIPs, select them and click Disable Protection above the table.
- Exporting the EIP list: Click Export above the list and select an export scope.
- To protect the EIPs of other accounts, see Multi-account Protection.
- To disable firewall protection for EIPs, click CFW Kill Switch in the upper right corner of the list. In the dialog box that is displayed, click OK.
- To restore EIP protection, click One-Click Restore in the upper part of the page.
- The EIP cannot be enabled or disabled during the escape or recovery. After the operation is successful, the EIP can be enabled or disabled.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





