Why Does the docker pull Command Fail to Be Executed?
x509: certificate signed by unknown authority
Symptom: When you run docker pull to pull an image, error message "x509: certificate signed by unknown authority" is displayed.
Possible causes:
- The container engine client communicates with SWR through HTTPS. The client verifies the server certificate. If the root certificate installed on the client is incomplete, the error message "x509: certificate signed by unknown authority" is displayed.
- A proxy is configured on the container engine client.
Solutions:
- If you trust the server, skip certificate authentication. Specifically, manually configure the container engine startup parameters using either of the following two methods. Replace Image registry address with the actual SWR registry address.
- Add the following configuration to the /etc/docker/daemon.json file. If the file does not exist, manually create it. Ensure that two-space indents are used in the configuration.
{ "insecure-registries":["image-registry-address"] } - /etc/sysconfig/docker:
INSECURE_REGISTRY='--insecure-registry=image-registry-address'
After configuration, run the systemctl restart docker or service restart docker command to restart the container engine.
- Add the following configuration to the /etc/docker/daemon.json file. If the file does not exist, manually create it. Ensure that two-space indents are used in the configuration.
- Run the docker info command to check whether the proxy is correctly configured. If not, modify the configuration.
Error: remote trust data does not exist
Problem: When you run the docker pull command to pull an image from SWR, message "Error: remote trust data does not exist" is displayed.
Possible cause: The image signature verification is enabled on the client. However, the image to be pulled does not contain a signature layer.
Solution: Check whether the environment variable DOCKER_CONTENT_TRUST is set to 1 in the /etc/profile file. If yes, change the value to 0 and run source /etc/profile for the setting to take effect.
repository does not exist or may require 'docker login'
Symptom: When you pull an image, an error occurs.
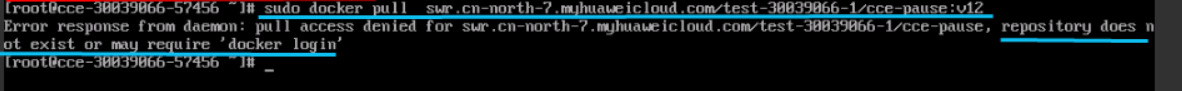
Possible cause: You do not have the swr:repo:download permission to pull images from the target organization.
Solutions
On either the SWR or IAM console, grant the required permission to the IAM user you are using.
Method 1: Log in to the SWR console as an SWR administrator. In the organization list, locate the organization. On the details page of the organization, grant the IAM user the permission to manage this organization. For details, see User Permissions.
Method 2: Use IAM fine-grained authorization to assign a custom policy to the user. This policy contains the permission to pull images.
- Log in to the IAM console.
- In the navigation pane, choose Permissions > Policies/Roles. Click Create Custom Policy. Enter a policy name and set Policy View to JSON. Enter the policy content as follows (replace namespace1 with the organization name) and click OK.
{ "Version": "1.1", "Statement": [ { "Effect": "Allow", "Action": [ "swr:repo:download" ], "Resource": [ "SWR:*:*:repo:namespace1/*" ] }, ] } - In the navigation pane, choose User Groups. Click the name of the user group that the IAM user belongs to. Click Authorize. Select the policy created in Step 2 for the user group.
- Wait for 1 minute. After the policy takes effect, pull the image again.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





