Este conteúdo foi traduzido por máquina para sua conveniência e a Huawei Cloud não pode garantir que o conteúdo foi traduzido com precisão. Para exibir o conteúdo original, use o link no canto superior direito para mudar para a página em inglês.
Web Application Firewall
Web Application Firewall
- Visão geral de serviço
- Primeiros passos
-
Guia de usuário
- Visão geral
-
Compra de WAF
- Compra de uma instância do Cloud WAF
- Compra de uma instância dedicada do WAF
- Atualização de Cloud WAF edição e as especificações (console antigo)
- Pacotes de expansão de largura de banda domodo de nuvem de WAF
- Pacotes de expansão de domínio doModo de Nuvem WAF
- Pacotes de expansão da regra do modo de nuvem do WAF
- Ativação de proteção de WAF
-
Gerenciamento de nomes de domínio do site
- Exibição de informações básicas
- Alternação de modo de trabalho do WAF
- Configuração de verificação de certificação PCI DSS/3DS e a versão do TLS
- Ativação de proteção WAF IPv6
- Ativação de protocolo HTTP/2
- Configuração de tempo limite de conexão
- Configuração de proteção de conexão
- Alternação de algoritmo de balanceamento de carga
- Atualização de um certificado
- Configuração de um identificador de tráfego para uma origem de ataque conhecida
- Edição de informações do servidor
- Modificação de página de alarme
- Remoção de um site protegido do WAF
- Gerenciamento de certificado
- Gerenciamento de grupos de lista negra e lista branca de endereço de IP
-
Configuração da regra
- Guia de configuração
- Configuração de regras básicas de proteção de Web
- Configuração de controle de acesso inteligente
- Configuração de uma regra de proteção contra ataques CC
- Configuração de uma regra de proteção precisa
- Adição de uma tabela de referência
- Configuração de uma regra de lista negra ou de lista branca de endereços IP
- Configuração de uma regra de origem de ataque conhecido
- Configuração de uma regra de controle de acesso de geolocalização
- Configuração de uma regra de proteção contra adulteração da Web
- Configuring Anti-Crawler Rules
- Configuração de uma regra de prevenção de vazamento de informações
- Configuring a Global Protection Whitelist (Formerly False Alarm Masking) Rule
- Configuração de uma regra de mascaramento de dados
- Painel de controle
- Gerenciamento de eventos
- Ativa LTS para registro em log do WAF
- Ativação de notificações de alarme
- Gerenciamento de políticas
- Gerenciamento dedicado do motor WAF
- Visualização de detalhes do produto
- Gerenciamento de projetos e projetos corporativos
- Gerenciamento de permissões
- Principais operações gravadas pelo CTS
- Monitoramento
-
Referência de API
- Antes de começar
- Visão geral da API
- Chamada de API
-
API
-
Gerenciamento de sites protegidos no modo nuvem
- Essa API é usada para consultar a lista de nomes de domínio protegidos no modo nuvem.
- Adição de um nome de domínio ao Cloud WAF
- Consulta de detalhes sobre um nome de domínio por ID de nome de domínio no modo nuvem
- Atualização de configurações de nomes de domínio protegidos com o Cloud WAF
- Exclusão de um nome de domínio do Cloud WAF
- Alteração de status de proteção de um nome de domínio
- Obtenção de informações de roteamento de nome de domínio (no modo nuvem)
-
Gerenciamento de sites protegidos por mecanismos dedicados do WAF
- Consulta de nomes de domínio protegidos por mecanismos WAF dedicados
- Adição de um nome de domínio a uma instância dedicada do WAF
- Modificação de um nome de domínio protegido por uma instância WAF dedicada
- Consulta de configurações de nome de domínio no modo dedicado
- Exclusão de um nome de domínio de uma instância dedicada do WAF
- Modificação de status de proteção de um nome de domínio no modo dedicado
- Gerenciamento de políticas
-
Gerenciamento de regras
- Alteração de status de uma regra
- Consulta de regras da lista branca de proteção global (Anteriormente mascaramento de alarmes falsos)
- Criação de uma regra de lista branca de proteção global (Anteriormente mascaramento de alarme falso)
- Exclusão de uma regra de lista branca de proteção global (Anteriormente mascaramento de alarme falso)
- Consulta de lista de regras da lista negra e da lista branca
- Criação de uma regra de lista negra/lista branca
- Atualização de uma regra de proteção de lista negra ou lista branca
- Exclusão de uma regra de lista negra ou de lista branca
- Consulta de uma regra de mascaramento de dados
- Criação de uma regra de mascaramento de dados
- Atualização de uma regra de mascaramento de dados
- Exclusão de uma regra de mascaramento de dados
- Consulta de lista de regras de controle de acesso de geolocalização
- Atualização de uma regra de controle de acesso de geolocalização
- Atualização de uma regra de controle de acesso de geolocalização
- Exclusão de uma regra de controle de acesso de geolocalização
- Consulta de lista de regras de proteção contra intrusão na Web
- Criação de uma regra de proteção contra violação da Web
- Exclusão de uma regra de proteção contra violação da Web
- Consulta de lista de tabelas de referência
- Criação de uma tabela de referência
- Modificação de uma tabela de referência
- Exclusão de uma tabela de referência
- Gerenciamento de certificado
- Gerenciamento de eventos
- Painel de controle
- Consulta de nome de domínio de um inquilino
- Consulta de recursos disponíveis em um site
-
Gerenciamento de sites protegidos no modo nuvem
- Apêndice
- No momento, o conteúdo não está disponível no seu idioma selecionado. Consulte a versão em inglês.
- What's New
- Function Overview
-
Product Bulletin
- Java Spring Framework Remote Code Execution Vulnerability
- Apache Dubbo Deserialization Vulnerability
- DoS Vulnerability in the Open-Source Component Fastjson
- Remote Code Execution Vulnerability of Fastjson
- Oracle WebLogic wls9-async Deserialization Remote Command Execution Vulnerability (CNVD-C-2019-48814)
-
Billing
- WAF Billing Overview
- Billing Modes
- Billing Items
- Billing Examples
- Changing the Billing Mode
- Renewing Your Subscription
- Bills
- About Arrears
- Billing Termination
- Cost Management
-
Billing FAQs
- Can I Switch Between Yearly/Monthly and Pay-per-Use Payments for WAF?
- Can I Use WAF for Free?
- How Is WAF Billed?
- Can WAF Continue Protecting a Domain Name When It Expires?
- How Do I Unsubscribe from WAF?
- Can I Retain the Original Configurations When I Unsubscribe from a WAF Instance and Then Purchase Another One?
- How Do I Know When My WAF Expires?
-
Best Practices
- WAF Best Practices You May Need
-
Website Access Configuration
- Connecting a Website Without a Proxy to WAF in CNAME Access Mode
- Combining AAD and WAF to Get All-Round Protection
- Combining CDN and WAF to Get Improved Protection and Load Speed
- Combining WAF and Layer-7 Load Balancers to Protect Services over Any Ports
- Using WAF, ELB, and NAT Gateway to Protect Services Not Deployed on Our Cloud
- Website Protection Configuration Suggestions
-
Mitigating Web Security Vulnerabilities
- Java Spring Framework Remote Code Execution Vulnerability
- Apache Dubbo Deserialization Vulnerability
- DoS Vulnerability in the Open-Source Component Fastjson
- Remote Code Execution Vulnerability of Fastjson
- Oracle WebLogic wls9-async Deserialization Remote Command Execution Vulnerability (CNVD-C-2019-48814)
- Defending Against Challenge Collapsar (CC) Attacks
- Using WAF to Block Crawler Attacks
- Verifying a Global Protection Whitelist Rule by Simulating Requests with Postman
- Combining WAF and HSS to Improve Web Page Tampering Protection
- Configuring Header Field Forwarding to Disable Response Packet Compression
- Configuring Origin Server Security
- Using LTS to Analyze WAF Logs
- Obtaining the Real Client IP Addresses
- Configuring Alarms on Cloud Eye for Abnormal WAF Metrics
- Migrating Protection Policies for Your Website
- SDK Reference
-
FAQs
-
About WAF
- WAF Basics
- Can WAF Protect an IP Address?
- What Objects Does WAF Protect?
- Does WAF Block Customized POST Requests?
- Does WAF Protect Traffic from Both IPv4 and IPv6 Addresses?
- What Are the Differences Between the Web Tamper Protection Functions of WAF and HSS?
- Which Web Service Framework Protocols Does WAF Support?
- Can WAF Protect Websites Accessed Through HSTS or NTLM Authentication?
- What Are the Differences Between WAF Forwarding and Nginx Forwarding?
- What Are the Differences Between WAF and CFW?
- Can I Configure Session Cookies in WAF?
- How Does WAF Detect SQL Injection, XSS, and PHP Injection Attacks?
- Can WAF Defend Against the Apache Struts2 Remote Code Execution Vulnerability (CVE-2021-31805)?
- Why Does the Vulnerability Scanning Tool Report Disabled Non-standard Ports for My WAF-Protected Website?
- What Are the Restrictions on Using WAF in Enterprise Projects?
- What Are Local File Inclusion and Remote File Inclusion?
- What Is the Difference Between QPS and the Number of Requests?
- Does WAF Support Custom Authorization Policies?
- Why Do Cookies Contain the HWWAFSESID or HWWAFSESTIME field?
- Can I Switch Between the WAF Cloud Mode and Dedicated Mode?
- Can I Add a Domain Name or IP Address to WAF Under Different Accounts?
- What Are Regions and AZs?
- Can I Use WAF Across Regions?
- In Which Regions Is WAF Available?
- Can I Use WAF Across Enterprise Projects?
- Can I Use a WAF Instance in a Specific Enterprise Project for Other Enterprise Projects?
-
About Purchase and Specifications Change
- Can I Buy Multiple WAF Instances Using the Same Account?
- What Are the Differences Between the Permissions of an Account and Those of IAM Users?
- Can I Share My WAF with Other Accounts?
- How Does WAF Calculate Domain Name Quota Usage?
- Can I Add More Protection Rules?
- What Can I Do If the Website Traffic Exceeds the WAF Service Request Limit?
- What Are the Impacts When QPS Exceeds the Allowed Peak Rate?
- Can I Change WAF Specifications During Renewal?
- Where and When Can I Buy a Domain, QPS, or Rule Expansion Package?
- How Do I Select Service QPS When Purchasing WAF?
- Is Service QPS Calculated Based on Incoming Traffic or Outgoing Traffic?
- Does WAF Have a Limit on the Protection Bandwidth or Shared Bandwidth?
- Where Can I View the Inbound and Outbound Bandwidths of a Protected Website?
-
Website Connect Issues
- How Do I Configure Domain Names to Be Protected When Adding Domain Names?
- Do I Have to Configure the Same Port as That of the Origin Server When Adding a Website to WAF?
- How Do I Whitelist Back-to-Source IP Addresses of Cloud WAF?
- How Long Will CNAME Records Be Retained After I Delete a Domain Name from WAF?
- What Are the Precautions for Configuring Multiple Server Addresses for Backend Servers?
- Does WAF Support Wildcard Domain Names?
- Does WAF Protect Chinese Domain Names?
- How Does WAF Forward Access Requests When Both a Wildcard Domain Name and a Single Domain Name Are Connected to WAF?
- What Can I Do If the Message "Illegal server address" Is Displayed When I Add a Domain Name?
- Why Am I Seeing the "Someone else has already added this domain name. Please confirm that the domain name belongs to you" Error Message?
- Why Cannot I Select a Client Protocol When Adding a Domain Name?
- Can I Set the Origin Server Address to a CNAME Record If I Use Cloud WAF?
- How Do I Verify Domain Ownership Using Huawei Cloud DNS?
- What Are Impacts If No Subdomain Name and TXT Record Are Configured?
- How Do I Query a Domain Name Provider?
- What Are the Differences Between the Old and New CNAME Records?
- Can I Access a Website Using an IP Address After a Domain Name Is Connected to WAF?
- How Can I Forward Requests Directly to the Origin Server Without Passing Through WAF?
- Why Cannot the Protection Mode Be Enabled After a Domain Name Is Connected to WAF?
-
Protection Rules
- Which Protection Levels Can Be Set for Basic Web Protection?
- What Is the Peak Rate of CC Attack Protection?
- When Is Cookie Used to Identify Users?
- What Are the Differences Between Rate Limit and Allowable Frequency in a CC Rule?
- Why Cannot the Verification Code Be Refreshed When Verification Code Is Configured in a CC Attack Protection Rule?
- How Can I Allow Access from .js Files?
- Can I Batch Add IP Addresses to a Blacklist or Whitelist Rule?
- Can I Import or Export a Blacklist or Whitelist into or from WAF?
- Why Does a Requested Page Fail to Respond to the Client After the JavaScript-based Anti-Crawler Is Enabled?
- Is There Any Impact on Website Loading Speed If Other Crawler Check in Anti-Crawler Is Enabled?
- How Does JavaScript Anti-Crawler Detection Work?
- In Which Situations Will the WAF Policies Fail?
- How Do I Allow Requests from Only IP Addresses in a Specified Geographical Region?
- How Do I Allow Only Specified IP Addresses to Access Protected Websites?
- Which Protection Rules Are Included in the System-Generated Policy?
- Why Does the Page Fail to Be Refreshed After WTP Is Enabled?
- What Are the Differences Between Blacklist/Whitelist Rules and Precise Protection Rules on Blocking Access Requests from Specified IP Addresses?
- What Do I Do If a Scanner, such as AppScan, Detects that the Cookie Is Missing Secure or HttpOnly?
- How Do I Block Layer-4 IP Addresses?
- IPv6 Protection
- Certificate Management
-
Protection Event Logs
- Can WAF Log Protection Events?
- Can I Obtain WAF Logs Using APIs?
- How Do I Obtain Data about Block Actions?
- What Does "Mismatch" for "Protective Action" Mean in the Event List?
- How Does WAF Obtain the Real Client IP Address for a Request?
- Can WAF Logs Be Transferred to OBS?
- How Long Can WAF Protection Logs Be Stored?
- Can I Query Protection Events of a Batch of Specified IP Addresses at Once?
- Will WAF Record Unblocked Events?
- Why Is the Traffic Statistics on WAF Inconsistent with That on the Origin Server?
- Why Is the Number of Logs on the Dashboard Page Inconsistent with That on the Configure Logs Tab?
- Why Are There Garbled Characters in Event Data I Exported from WAF?
-
About WAF
-
Troubleshooting
- Troubleshooting Website Connection Exceptions
-
Troubleshooting Certificate and Cipher Suite Issues
- How Do I Fix an Incomplete Certificate Chain?
- Why Does My Certificate Not Match the Key?
- Why Are HTTPS Requests Denied on Some Mobile Phones?
- What Do I Do If the Protocol Is Not Supported and the Client and Server Do Not Support Common SSL Protocol Versions or Cipher Suites?
- Why Is the Bar Mitzvah Attack on SSL/TLS Detected?
-
Troubleshooting Traffic Forwarding Exceptions
- How Do I Troubleshoot 404/502/504 Errors?
- Why Am I Seeing Error Code 418?
- Why Am I Seeing Error Code 523?
- Why Was My Website Redirected So Many Times?
- Why Am I Seeing Error Code 414 Request-URI Too Large?
- What Do I Do If the CPU Usage of the Origin Server Reaches 100%?
- What Is the Connection Timeout Duration of WAF? Can I Manually Set the Timeout Duration?
- Checking Whether Normal Requests Are Blocked Mistakenly
- Checking for Permission Exceptions
- Videos
-
More Documents
-
User Guide (Paris)
- Introduction
- Monitoring Metrics
- Ports Supported by WAF
- Cloud WAF
-
Dedicated WAF Mode
- WAF Operation Guide
- Applying for a Dedicated WAF Instance
- Dashboard
- Events
-
Policies
- How to Configure WAF Protection
- Configuring Basic Protection Rules to Defend Against Common Web Attacks
- Configuring a CC Attack Protection Rule
- Configuring Custom Precise Protection Rules
- Configuring IP Address Blacklist and Whitelist Rules to Block or Allow Specified IP Addresses
- Configuring Geolocation Access Control Rules to Block or Allow Requests from Specific Locations
- Configuring Web Tamper Protection Rules to Prevent Static Web Pages from Being Tampered With
- Configuring Anti-Crawler Rules
- Configuring Information Leakage Prevention Rules to Protect Sensitive Information from Leakage
- Configuring a Global Protection Whitelist Rule to Ignore False Alarms
- Configuring Data Masking Rules to Prevent Privacy Information Leakage
- Creating a Reference Table to Configure Protection Metrics In Batches
- Configuring a Known Attack Source Rule to Block Specific Visitors for a Specified Duration
- Condition Field Description
- Managing Policies
- Website Settings
- Certificate Management
- System Management
- Authorizing and Associating an Enterprise Project
- Auditing
-
Best Practices
-
Mitigating Web Security Vulnerabilities
- Java Spring Framework Remote Code Execution Vulnerability
- Apache Dubbo Deserialization Vulnerability
- DoS Vulnerability in the Open-Source Component Fastjson
- Remote Code Execution Vulnerability of Fastjson
- Oracle WebLogic wls9-async Deserialization Remote Command Execution Vulnerability (CNVD-C-2019-48814)
- Configuring the Minimum TLS Version and Cipher Suite to Better Secure Connections
- Configuring CC Attack Protection
- Configuring Anti-Crawler Rules to Prevent Crawler Attacks
- Configuring an Access Control Policy on an ECS or ELB to Protect Origin Servers
- Configuring Basic Web Protection
- Handling False Alarms to Get Improved Basic Web Protection
- Verifying a Global Protection Whitelist (Formerly False Alarm Masking) Rule by Simulating Requests with Postman
- WAF Cloud Mode Access Configuration
- Upgrading a Dedicated WAF Instance
- Obtaining Real Client IP Addresses
- Using LTS to Quickly Query and Analyze WAF Access Logs
- Using LTS to Analyze How WAF Blocks Spring Core RCE Vulnerability in Real Time
- Using LTS to Configure Block Alarms for WAF Rules
- Combining WAF and Layer-7 Load Balancers to Protect Services over Any Ports
- Combining WAF and HSS to Get Improved Web Tamper Protection
-
Mitigating Web Security Vulnerabilities
- IAM Permissions Management
-
FAQs
-
About the Product
- FAQs for Beginners
-
WAF Functions
- Can WAF Protect an IP Address?
- What Objects Does WAF Protect?
- About WAF Protection
- Can I Configure Session Cookies in WAF?
- Does WAF Block Customized POST Requests?
- What Are the Differences Between the Web Tamper Protection Functions of WAF and HSS?
- Which Web Service Framework Protocols Does WAF Support?
- Can WAF Protect Websites Accessed Through HSTS or NTLM Authentication?
- What Are the Differences Between WAF Forwarding and Nginx Forwarding?
- How Does WAF Detect SQL Injection, XSS, and PHP Injection Attacks?
- Can WAF Defend Against the Apache Struts2 Remote Code Execution Vulnerability (CVE-2021-31805)?
-
WAF Usage
- Why Does the Vulnerability Scanning Tool Report Disabled Non-standard Ports for My WAF-Protected Website?
- How Do I Obtain the Real IP Address of a Web Visitor?
- What Are Local File Inclusion and Remote File Inclusion?
- What Is the Difference Between QPS and the Number of Requests?
- Does WAF Support Custom Authorization Policies?
- Can I Add a Domain Name or IP Address to WAF Under Different Accounts?
- How Do I Configure My Server to Allow Only Requests from WAF?
- Why Do Cookies Contain the HWWAFSESID or HWWAFSESTIME field?
- Can I Switch Between the WAF Cloud Mode and Dedicated Mode?
- How Do I Configure WAF If a Reverse Proxy Server Is Deployed for My Website?
- How Does WAF Forward Access Requests When Both a Wildcard Domain Name and a Single Domain Name Are Connected to WAF?
- Enterprise Project
- Service Request/Specification
- About Billing
-
Website Access Configuration
-
Domain Name and Port Configuration
- How Do I Add a Domain Name/IP Address to WAF?
- Which Non-Standard Ports Does WAF Support?
- How Do I Use a Dedicated WAF Instance to Protect Non-Standard Ports That Are Not Supported by the Dedicated Instance?
- How Do I Configure Domain Names to Be Protected When Adding Domain Names?
- Do I Have to Configure the Same Port as That of the Origin Server When Adding a Website to WAF?
- How Do I Configure Non-standard Ports When Adding a Protected Domain Name?
- What Can I Do If One of Ports on an Origin Server Does Not Require WAF Protection?
- What Data Is Required for Connecting a Domain Name/IP Address to WAF?
- How Do I Safely Delete a Protected Domain Name?
- Can I Change the Domain Name That Has Been Added to WAF?
- What Are the Precautions for Configuring Multiple Server Addresses for Backend Servers?
- Does WAF Support Wildcard Domain Names?
- How Do I Route Website Traffic to My Cloud WAF Instance?
- Can I Configure Multiple Load Balancers for a Dedicated WAF Instance?
- Certificate Management
- Server Configuration
- Domain Name Resolution
- Operations After Connecting Websites to WAF
-
Domain Name and Port Configuration
-
Service Interruption Check
- How Do I Troubleshoot 500/502/504 Errors?
- Why Is My Domain Name or IP Address Inaccessible?
- How Do I Handle False Alarms as WAF Blocks Normal Requests to My Website?
- Why Are HTTPS Requests Denied on Some Mobile Phones?
- How Do I Fix an Incomplete Certificate Chain?
- Why Does My Certificate Not Match the Key?
- Why Am I Seeing Error Code 418?
- How Can I Upload Files After the Website Is Connected to WAF?
- Why Does WAF Block Normal Requests as Invalid Requests?
- How Do I Whitelist IP Address Ranges of Cloud WAF?
- What Is the Connection Timeout Duration of WAF? Can I Manually Set the Timeout Duration?
- How Do I Solve the Problem of Excessive Redirection Times?
- Why Am I Seeing Error Code 523?
- Why Does the Website Login Page Continuously Refreshed After a Domain Name Is Connected to WAF?
- Why Does the Requested Page Respond Slowly After the HTTP Forwarding Policy Is Configured?
- Why Am I Seeing Error Code 414 Request-URI Too Large?
- What Do I Do If the Protocol Is Not Supported and the Client and Server Do Not Support Common SSL Protocol Versions or Cipher Suites?
- Why Cannot I Access the Dedicated Engine Page?
- Why Is the Bar Mitzvah Attack on SSL/TLS Detected?
-
Protection Rule Configuration
- Basic Web Protection
- CC Attack Protection Rules
- Precise Protection rules
- Anti-Crawler Protection
-
Others
- In Which Situations Will the WAF Policies Fail?
- Can I Export or Back Up the WAF Configuration?
- What Working Modes and Protection Mechanisms Does WAF Have?
- Which Protection Rules Are Included in the System-Generated Policy?
- What Types of Protection Rules Does WAF Support?
- Which of the WAF Protection Rules Support the Log-Only Protective Action?
- Why Does the Page Fail to Be Refreshed After WTP Is Enabled?
- What Are the Differences Between Blacklist/Whitelist Rules and Precise Protection Rules on Blocking Access Requests from Specified IP Addresses?
- What Do I Do If a Scanner, such as AppScan, Detects that the Cookie Is Missing Secure or HttpOnly?
-
About the Product
- Change History
-
User Guide (ME-Abu Dhabi Region)
- Service Overview
- WAF Operation Guide
- Enabling WAF
- Dashboard
- Events
-
Policies
- How to Configure WAF Protection
- Configuring Basic Protection Rules to Defend Against Common Web Attacks
- Configuring a CC Attack Protection Rule
- Configuring Custom Precise Protection Rules
- Configuring IP Address Blacklist and Whitelist Rules to Block or Allow Specified IP Addresses
- Configuring Geolocation Access Control Rules to Block or Allow Requests from Specific Locations
- Configuring Web Tamper Protection Rules to Prevent Static Web Pages from Being Tampered With
- Configuring Anti-Crawler Rules
- Configuring Information Leakage Prevention Rules to Protect Sensitive Information from Leakage
- Configuring a Global Protection Whitelist Rule to Ignore False Alarms
- Configuring Data Masking Rules to Prevent Privacy Information Leakage
- Creating a Reference Table to Configure Protection Metrics In Batches
- Configuring a Known Attack Source Rule to Block Specific Visitors for a Specified Duration
- Condition Field Description
- Managing Policies
- Website Settings
- Object Management
- System Management
- Permissions Management
- Monitoring and Auditing
-
FAQs
-
About WAF
- FAQs for Beginners
-
WAF Functions
- Can WAF Protect an IP Address?
- What Objects Does WAF Protect?
- Does WAF Block Customized POST Requests?
- What Are the Differences Between the Web Tamper Protection Functions of WAF and HSS?
- Which Web Service Framework Protocols Does WAF Support?
- Can WAF Protect Websites Accessed Through HSTS or NTLM Authentication?
- What Are the Differences Between WAF Forwarding and Nginx Forwarding?
- Can I Configure Session Cookies in WAF?
- How Does WAF Detect SQL Injection, XSS, and PHP Injection Attacks?
- Can WAF Defend Against the Apache Struts2 Remote Code Execution Vulnerability (CVE-2021-31805)?
-
WAF Usage
- Why Does the Vulnerability Scanning Tool Report Disabled Non-standard Ports for My WAF-Protected Website?
- How Do I Obtain the Real IP Address of a Web Visitor?
- Will Traffic Be Permitted After WAF Is Switched to the Bypassed Mode?
- What Are Local File Inclusion and Remote File Inclusion?
- What Is the Difference Between QPS and the Number of Requests?
- Does WAF Support Custom Authorization Policies?
- How Do I Configure My Server to Allow Only Requests from WAF?
- Why Do Cookies Contain the HWWAFSESID or HWWAFSESTIME field?
- Can I Switch Between the WAF Cloud Mode and Dedicated Mode?
- How Do I Configure WAF If a Reverse Proxy Server Is Deployed for My Website?
- How Does WAF Forward Access Requests When Both a Wildcard Domain Name and a Single Domain Name Are Connected to WAF?
- Service Request/Specification
-
Website Domain Name Access Configuration
-
Domain Name and Port Configuration
- How Do I Add a Domain Name/IP Address to WAF?
- Which Non-Standard Ports Does WAF Support?
- How Do I Use a Dedicated WAF Instance to Protect Non-Standard Ports That Are Not Supported by the Dedicated Instance?
- How Do I Configure Domain Names to Be Protected When Adding Domain Names?
- Do I Have to Configure the Same Port as That of the Origin Server When Adding a Website to WAF?
- How Do I Configure Non-standard Ports When Adding a Protected Domain Name?
- What Can I Do If One of Ports on an Origin Server Does Not Require WAF Protection?
- What Data Is Required for Connecting a Domain Name/IP Address to WAF?
- How Do I Safely Delete a Protected Domain Name?
- Can I Change the Domain Name That Has Been Added to WAF?
- What Are the Precautions for Configuring Multiple Server Addresses for Backend Servers?
- Does WAF Support Wildcard Domain Names?
- How Do I Route Website Traffic to My Cloud WAF Instance?
- Can I Configure Multiple Load Balancers for a Dedicated WAF Instance?
- Why Am I Seeing the "Someone else has already added this domain name. Please confirm that the domain name belongs to you" Error Message?
- Certificate Management
- Server Configuration
- Operations After Connecting Websites to WAF
-
Domain Name and Port Configuration
-
Service Interruption Check
- How Do I Troubleshoot 404/502/504 Errors?
- Why Is My Domain Name or IP Address Inaccessible?
- How Do I Handle False Alarms as WAF Blocks Normal Requests to My Website?
- Why Does WAF Block Normal Requests as Invalid Requests?
- How Do I Whitelist IP Address Ranges of Cloud WAF?
- What Is the Connection Timeout Duration of WAF? Can I Manually Set the Timeout Duration?
- How Do I Solve the Problem of Excessive Redirection Times?
- Why Are HTTPS Requests Denied on Some Mobile Phones?
- How Do I Fix an Incomplete Certificate Chain?
- Why Does My Certificate Not Match the Key?
- Why Am I Seeing Error Code 418?
- Why Am I Seeing Error Code 523?
- Why Does the Website Login Page Continuously Refreshed After a Domain Name Is Connected to WAF?
- Why Does the Requested Page Respond Slowly After the HTTP Forwarding Policy Is Configured?
- How Can I Upload Files After the Website Is Connected to WAF?
- Why Am I Seeing Error Code 414 Request-URI Too Large?
- What Do I Do If the Protocol Is Not Supported and the Client and Server Do Not Support Common SSL Protocol Versions or Cipher Suites?
- Why Cannot I Access the Dedicated Engine Page?
- Why Is the Bar Mitzvah Attack on SSL/TLS Detected?
-
Protection Rule Configuration
- Basic Web Protection
-
CC Attack Protection Rules
- What Is the Peak Rate of CC Attack Protection?
- How Do I Configure a CC Attack Protection Rule?
- When Is Cookie Used to Identify Users?
- What Are the Differences Between Rate Limit and Allowable Frequency in a CC Rule?
- Why Cannot the Verification Code Be Refreshed When Verification Code Is Configured in a CC Attack Protection Rule?
- Precise Protection rules
- IP Address Blacklist and Whitelist
- Anti-Crawler Protection
-
Others
- In Which Situations Will the WAF Policies Fail?
- What Working Modes and Protection Mechanisms Does WAF Have?
- What Types of Protection Rules Does WAF Support?
- Which of the WAF Protection Rules Support the Log-Only Protective Action?
- How Do I Allow Only Specified IP Addresses to Access Protected Websites?
- Which Protection Rules Are Included in the System-Generated Policy?
- Why Does the Page Fail to Be Refreshed After WTP Is Enabled?
- What Are the Differences Between Blacklist/Whitelist Rules and Precise Protection Rules on Blocking Access Requests from Specified IP Addresses?
- What Do I Do If a Scanner, such as AppScan, Detects that the Cookie Is Missing Secure or HttpOnly?
-
Protection Event Logs
- Can WAF Log Protection Events?
- How Do I Obtain Data about Block Actions?
- What Does "Mismatch" for "Protective Action" Mean in the Event List?
- How Long Can WAF Protection Logs Be Stored?
- Can I Query Protection Events of a Batch of Specified IP Addresses at Once?
- Will WAF Record Unblocked Events?
- Why Is the Traffic Statistics on WAF Inconsistent with That on the Origin Server?
-
About WAF
- Change History
-
User Guide (Kuala Lumpur Region)
- Service Overview
- WAF Operation Guide
- Enabling WAF
- Dashboard
- Events
-
Policies
- How to Configure WAF Protection
- Configuring Basic Protection Rules to Defend Against Common Web Attacks
- Configuring a CC Attack Protection Rule
- Configuring Custom Precise Protection Rules
- Configuring IP Address Blacklist and Whitelist Rules to Block or Allow Specified IP Addresses
- Configuring Geolocation Access Control Rules to Block or Allow Requests from Specific Locations
- Configuring Web Tamper Protection Rules to Prevent Static Web Pages from Being Tampered With
- Configuring Anti-Crawler Rules
- Configuring Information Leakage Prevention Rules to Protect Sensitive Information from Leakage
- Configuring a Global Protection Whitelist Rule to Ignore False Alarms
- Configuring Data Masking Rules to Prevent Privacy Information Leakage
- Creating a Reference Table to Configure Protection Metrics In Batches
- Configuring a Known Attack Source Rule to Block Specific Visitors for a Specified Duration
- Condition Field Description
- Managing Policies
- Website Settings
- Object Management
- System Management
- Permissions Management
- Monitoring and Auditing
-
FAQs
-
About WAF
- FAQs for Beginners
-
WAF Functions
- Can WAF Protect an IP Address?
- What Objects Does WAF Protect?
- Does WAF Block Customized POST Requests?
- What Are the Differences Between the Web Tamper Protection Functions of WAF and HSS?
- Which Web Service Framework Protocols Does WAF Support?
- Can WAF Protect Websites Accessed Through HSTS or NTLM Authentication?
- What Are the Differences Between WAF Forwarding and Nginx Forwarding?
- Can I Configure Session Cookies in WAF?
- How Does WAF Detect SQL Injection, XSS, and PHP Injection Attacks?
- Can WAF Defend Against the Apache Struts2 Remote Code Execution Vulnerability (CVE-2021-31805)?
-
WAF Usage
- Why Does the Vulnerability Scanning Tool Report Disabled Non-standard Ports for My WAF-Protected Website?
- How Do I Obtain the Real IP Address of a Web Visitor?
- What Are Local File Inclusion and Remote File Inclusion?
- What Is the Difference Between QPS and the Number of Requests?
- How Do I Configure My Server to Allow Only Requests from WAF?
- Why Do Cookies Contain the HWWAFSESID or HWWAFSESTIME field?
- Can I Switch Between the WAF Cloud Mode and Dedicated Mode?
- How Do I Configure WAF If a Reverse Proxy Server Is Deployed for My Website?
- How Does WAF Forward Access Requests When Both a Wildcard Domain Name and a Single Domain Name Are Connected to WAF?
- Service Request/Specification
-
Website Domain Name Access Configuration
-
Domain Name and Port Configuration
- How Do I Add a Domain Name/IP Address to WAF?
- Which Non-Standard Ports Does WAF Support?
- How Do I Use a Dedicated WAF Instance to Protect Non-Standard Ports That Are Not Supported by the Dedicated Instance?
- How Do I Configure Domain Names to Be Protected When Adding Domain Names?
- Do I Have to Configure the Same Port as That of the Origin Server When Adding a Website to WAF?
- How Do I Configure Non-standard Ports When Adding a Protected Domain Name?
- What Can I Do If One of Ports on an Origin Server Does Not Require WAF Protection?
- What Data Is Required for Connecting a Domain Name/IP Address to WAF?
- How Do I Safely Delete a Protected Domain Name?
- Can I Change the Domain Name That Has Been Added to WAF?
- What Are the Precautions for Configuring Multiple Server Addresses for Backend Servers?
- Does WAF Support Wildcard Domain Names?
- How Do I Route Website Traffic to My Cloud WAF Instance?
- Can I Configure Multiple Load Balancers for a Dedicated WAF Instance?
- Why Am I Seeing the "Someone else has already added this domain name. Please confirm that the domain name belongs to you" Error Message?
- Certificate Management
- Server Configuration
- Operations After Connecting Websites to WAF
-
Domain Name and Port Configuration
-
Service Interruption Check
- How Do I Troubleshoot 404/502/504 Errors?
- Why Is My Domain Name or IP Address Inaccessible?
- How Do I Handle False Alarms as WAF Blocks Normal Requests to My Website?
- Why Does WAF Block Normal Requests as Invalid Requests?
- How Do I Whitelist IP Address Ranges of Cloud WAF?
- What Is the Connection Timeout Duration of WAF? Can I Manually Set the Timeout Duration?
- How Do I Solve the Problem of Excessive Redirection Times?
- Why Are HTTPS Requests Denied on Some Mobile Phones?
- How Do I Fix an Incomplete Certificate Chain?
- Why Does My Certificate Not Match the Key?
- Why Am I Seeing Error Code 418?
- Why Am I Seeing Error Code 523?
- Why Does the Website Login Page Continuously Refreshed After a Domain Name Is Connected to WAF?
- Why Does the Requested Page Respond Slowly After the HTTP Forwarding Policy Is Configured?
- How Can I Upload Files After the Website Is Connected to WAF?
- Why Am I Seeing Error Code 414 Request-URI Too Large?
- What Do I Do If the Protocol Is Not Supported and the Client and Server Do Not Support Common SSL Protocol Versions or Cipher Suites?
- Why Cannot I Access the Dedicated Engine Page?
- Why Is the Bar Mitzvah Attack on SSL/TLS Detected?
-
Protection Rule Configuration
- Basic Web Protection
- CC Attack Protection Rules
- Precise Protection rules
- IP Address Blacklist and Whitelist
- Anti-Crawler Protection
-
Others
- In Which Situations Will the WAF Policies Fail?
- What Working Modes and Protection Mechanisms Does WAF Have?
- What Types of Protection Rules Does WAF Support?
- Which of the WAF Protection Rules Support the Log-Only Protective Action?
- Which Protection Rules Are Included in the System-Generated Policy?
- Why Does the Page Fail to Be Refreshed After WTP Is Enabled?
- What Are the Differences Between Blacklist/Whitelist Rules and Precise Protection Rules on Blocking Access Requests from Specified IP Addresses?
- What Do I Do If a Scanner, such as AppScan, Detects that the Cookie Is Missing Secure or HttpOnly?
-
Protection Event Logs
- Can WAF Log Protection Events?
- How Do I Obtain Data about Block Actions?
- What Does "Mismatch" for "Protective Action" Mean in the Event List?
- How Long Can WAF Protection Logs Be Stored?
- Can I Query Protection Events of a Batch of Specified IP Addresses at Once?
- Will WAF Record Unblocked Events?
- Why Is the Traffic Statistics on WAF Inconsistent with That on the Origin Server?
-
About WAF
- Change History
-
User Guide (Ankara Region)
- Service Overview
- Overview
- Applying for a Dedicated WAF Engine
- Enabling WAF Protection
-
Website Domain Name Management
- Viewing Basic Information
- Switching WAF Working Mode
- Configuring the Minimum TLS Version and Cipher Suite
- Configuring Connection Timeout
- Configuring Connection Protection
- Updating a Certificate
- Configuring a Traffic Identifier for a Known Attack Source
- Editing Server Information
- Modifying the Alarm Page
- Removing a Protected Website from WAF
- Certificate Management
- Managing IP Address Blacklist and Whitelist Groups
-
Rule Configuration
- Configuration Guidance
- Configuring Basic Web Protection Rules
- Configuring a CC Attack Protection Rule
- Configuring a Precise Protection Rule
- Adding a Reference Table
- Configuring an IP Address Blacklist or Whitelist Rule
- Configuring a Known Attack Source Rule
- Configuring a Geolocation Access Control Rule
- Configuring a Web Tamper Protection Rule
- Configuring Anti-Crawler Rules
- Configuring an Information Leakage Prevention Rule
- Configuring a Global Protection Whitelist (Formerly False Alarm Masking) Rule
- Configuring a Data Masking Rule
- Dashboard
- Event Management
- Enabling Alarm Notifications
- Policy Management
- Dedicated WAF Engine Management
- Viewing Product Details
- Permissions Management
-
FAQs
-
About WAF
-
WAF Functions
- Can WAF Protect an IP Address?
- What Objects Does WAF Protect?
- Which OSs Does WAF Support?
- Which Layers Does WAF Provide Protection At?
- Does WAF Support File Caching?
- About WAF Protection
- Does WAF Support Two-Way SSL Authentication?
- Does WAF Support Application Layer Protocol- and Content-Based Access Control?
- Can WAF Check the Body I Add to a POST Request?
- Can WAF Limit the Access Speed of a Domain Name?
- Can WAF Block Data Packets in multipart/form-data Format?
- Can a WAF Instance Be Deployed in the VPC?
- Can WAF Block URL Requests That Contain Special Characters?
- Can WAF Block Spam and Malicious User Registrations?
- Can WAF Block Requests for Calling Other APIs from Web Pages?
- Can I Configure Session Cookies in WAF?
- Does WAF Block Customized POST Requests?
- Can WAF Limit Access Through Domain Names?
- Does WAF Have the IPS Module?
- Which Web Service Framework Protocols Does WAF Support?
- Can WAF Protect Websites Accessed Through HSTS or NTLM Authentication?
- What Are the Differences Between WAF Forwarding and Nginx Forwarding?
- Does WAF Cache Website Data?
- Is WAF a Hardware Firewall or a Software Firewall?
- Is There Any Impact on Origin Servers If I Enable HTTP/2 in WAF?
- How Does WAF Detect SQL Injection and XSS Attacks?
- Can WAF Defend Against the Apache Struts2 Remote Code Execution Vulnerability (CVE-2021-31805)?
- Does a Dedicated WAF Instance Support Cross-VPC Protection?
-
WAF Usage
- Why Does the Vulnerability Scanning Tool Report Disabled Non-standard Ports for My WAF-Protected Website?
- Does WAF Affect Email Ports or Email Receiving and Sending?
- How Do I Obtain the Real IP Address of a Web Visitor?
- How Does WAF Block Requests?
- What Are Local File Inclusion and Remote File Inclusion?
- What Is the Difference Between QPS and the Number of Requests?
- What Are Concurrent Requests?
- Can WAF Block Requests When a Certificate Is Mounted on ELB?
- Does WAF Affect My Existing Workloads and Server Running?
- How Do I Configure My Server to Allow Only Requests from WAF?
- Why Do Cookies Contain the HWWAFSESID or HWWAFSESTIME field?
- How Do I Configure WAF If a Reverse Proxy Server Is Deployed for My Website?
- How Does WAF Forward Access Requests When Both a Wildcard Domain Name and a Single Domain Name Are Connected to WAF?
- Does WAF Affect Data Transmission from the Internal Network to an External Network?
- Do I Need to Make Some Changes in WAF If the Security Group for Origin Server (Address) Is Changed?
-
WAF Functions
-
Website Domain Name Access Configuration
-
Domain Name and Port Configuration
- How Do I Add a Domain Name/IP Address to WAF?
- Which Non-Standard Ports Does WAF Support?
- Can WAF Protect Multiple Domain Names That Point to the Same Origin Server?
- How Do I Configure Domain Names to Be Protected When Adding Domain Names?
- Do I Have to Configure the Same Port as That of the Origin Server When Adding a Website to WAF?
- What Can I Do If One of Ports on an Origin Server Does Not Require WAF Protection?
- What Data Is Required for Connecting a Domain Name/IP Address to WAF?
- How Do I Safely Delete a Protected Domain Name?
- Can I Change the Domain Name That Has Been Added to WAF?
- What Are the Precautions for Configuring Multiple Server Addresses for Backend Servers?
- Does WAF Support Wildcard Domain Names?
- Can I Configure Multiple Load Balancers for a Dedicated WAF Instance?
- Why Am I Seeing the "Someone else has already added this domain name. Please confirm that the domain name belongs to you" Error Message?
- Certificate Management
-
Domain Name and Port Configuration
-
Service Interruption Check
- How Do I Troubleshoot 404/502/504 Errors?
- Why Is My Domain Name or IP Address Inaccessible?
- How Do I Handle False Alarms as WAF Blocks Normal Requests to My Website?
- Why Does WAF Block Normal Requests as Invalid Requests?
- What Is the Connection Timeout Duration of WAF? Can I Manually Set the Timeout Duration?
- How Do I Solve the Problem of Excessive Redirection Times?
- Why Are HTTPS Requests Denied on Some Mobile Phones?
- How Do I Fix an Incomplete Certificate Chain?
- Why Does My Certificate Not Match the Key?
- Why Am I Seeing Error Code 418?
- Why Am I Seeing Error Code 523?
- Why Does the Website Login Page Continuously Refreshed After a Domain Name Is Connected to WAF?
- Why Does the Requested Page Respond Slowly After the HTTP Forwarding Policy Is Configured?
- How Can I Upload Files After the Website Is Connected to WAF?
- Why Is the Bar Mitzvah Attack on SSL/TLS Detected?
-
Protection Rule Configuration
- Basic Web Protection
- CC Attack Protection Rules
- Precise Protection rules
- Anti-Crawler Protection
-
Others
- In Which Situations Will the WAF Policies Fail?
- Is the Path of a WAF Protection Rule Case-sensitive?
- What Protection Rules Does WAF Support?
- Which of the WAF Protection Rules Support the Log-Only Protective Action?
- Why Does the Page Fail to Be Refreshed After WTP Is Enabled?
- What Are the Differences Between Blacklist/Whitelist Rules and Precise Protection Rules on Blocking Access Requests from Specified IP Addresses?
- What Do I Do If a Scanner, such as AppScan, Detects that the Cookie Is Missing Secure or HttpOnly?
-
About WAF
- Change History
-
API Reference (Paris)
- Before You Start
- API Overview
- API Calling
-
APIs
-
Cloud Mode
- Resource Quotas
- Domain Names
- Certificate Management
- Protection Status and Domain Setup
- Policies
- Blacklist and Whitelist Rules
- CC Attack Protection Rules
- Precise Protection Rules
- Data Masking Rules
- Web Tamper Protection Rules
- False Alarm Masking Rules
-
Event Logs
- Querying Attack Event Logs
- Querying Attack Event Logs by ID
- Querying Event Distribution
- Querying Request Statistics and Attack Statistics in a Specified Time Range
- Querying the Total Number of Attacks
- Querying Top N Attack Source IP Addresses
- Querying the Number of Attack Source IP Addresses
- Querying the Total Number of Requests per Second
- Querying the List of Event Log Files
- Alarm Notification
- Obtaining Option Details
- Interconnecting with Cloud Eye
-
Dedicated Mode
- Dedicated Instance Management
- Domain Names Protected by WAF
- Protection Status and Domain Name Access
- Policy Management
- Blacklist and Whitelist Rule Management
- CC Attack Protection Rule Management
- Precise Protection Rule Management
- Data Masking Rule Management
- Web Tamper Protection Rule Management
- False Alarm Masking Rule Management
- Dashboard
- Protection Event Management
- Certificate Management
-
Cloud Mode
- Permissions and Supported Actions
- Appendix
- Change History
-
API Reference (Kuala Lumpur Region)
- Before You Start
- API Overview
- API Calling
-
API
- Policy Management
-
Rule Management
- Querying False Alarm Masking Rules
- Querying the Reference Table List
- Creating a Reference Table
- Modifying a Reference Table
- Deleting a Reference Table
- Querying the List of Blacklist and Whitelist Rules
- Creating a Whitelist or Blacklist Rule
- Updating a Whitelist or Blacklist Rule
- Deleting a Whitelist or Blacklist Rule
- Adding a Data Masking Rule
- Querying a Data Masking Rule
- Updating a Data Masking Rule
- Deleting a Data Masking Rule
- Querying the Geolocation Access Control Rule List
- Creating a Geolocation Access Control Rule
- Updating a Geolocation Access Control Rule
- Deleting a Geolocation Access Control Rule
- Querying the List of Web Tamper Protection Rules
- Creating a Web Tamper Protection Rule
- Deleting a Web Tamper Protection Rule
- Changing the Status of a Rule
- Certificate Management
- Event Management
-
Protected Website Management in Dedicated Mode
- Connecting a Domain Name to a Dedicated WAF Instance
- Querying the List of Domain Names Connected to Dedicated WAF Instances
- Modifying the Configuration of a Domain Name Connected to a Dedicated WAF Instance
- Querying the Domain Name Configuration in Dedicated Mode
- Deleting a Domain Name from a Dedicated WAF Instance
- Modifying the Protection Status of a Domain Name Connected to a Dedicated WAF Instance
- Dashboard
- Querying the Protected Domain Names
- Querying Features Available in a Site
-
Managing Websites Protected by Cloud WAF
- Querying Domain Names Protected by Cloud WAF
- Adding a Domain Name to Cloud WAF
- Modifying the Protection Status for a Domain Name
- Obtaining Domain Name Route Information in Cloud Mode
- Querying a Domain Name Protected by Cloud WAF by ID
- Updating a Domain Name Protected by Cloud WAF
- Removing a Domain Name from Cloud WAF
- Appendix
- Change History
-
API Reference (Ankara Region)
- Before You Start
- API Overview
- API Calling
-
APIs
-
Managing Websites Protected by Dedicated WAF Engines
- Querying Domain Names Protected by Dedicated WAF Engines
- Adding a Domain Name to a Dedicated WAF Instance
- Modifying a Domain Name Protected by a Dedicated WAF Instance
- Querying Domain Name Settings in Dedicated Mode
- Deleting a Domain Name from a Dedicated WAF Instance
- Modifying the Protection Status of a Domain Name in Dedicated Mode
- Policy Management
-
Rule Management
- Changing the Status of a Rule
- Querying Global Protection Whitelist (Formerly False Alarm Masking) Rules
- Creating a Global Protection Whitelist (Formerly False Alarm Masking) Rule
- Deleting a Global Protection Whitelist (Formerly False Alarm Masking) Rule
- Querying the Blacklist and Whitelist Rule List
- Creating a Blacklist/Whitelist Rule
- Updating a Blacklist or Whitelist Protection Rule
- Deleting a Blacklist or Whitelist Rule
- Querying a Data Masking Rule
- Creating a Data Masking Rule
- Updating a Data Masking Rule
- Deleting a Data Masking Rule
- Querying the List of Geolocation Access Control Rules
- Creating a Geolocation Access Control Rule
- Updating a Geolocation Access Control Rule
- Deleting a Geolocation Access Control Rule
- Querying the List of Web Tamper Protection Rules
- Creating a Web Tamper Protection Rule
- Deleting a Web Tamper Protection Rule
- Querying the Reference Table List
- Creating a Reference Table
- Modifying a Reference Table
- Deleting a Reference Table
- Certificate Management
- Event Management
- Querying the Domain Name of a Tenant
-
Managing Websites Protected by Dedicated WAF Engines
- Appendix
- Change History
-
API Reference (ME-Abu Dhabi Region)
- Before You Start
- API Calling
-
APIs
-
Managing Websites Protected by Dedicated WAF Engines
- Querying Domain Names Protected by Dedicated WAF Engines
- Adding a Domain Name to a Dedicated WAF Instance
- Modifying a Domain Name Protected by a Dedicated WAF Instance
- Querying Domain Name Settings in Dedicated Mode
- Deleting a Domain Name from a Dedicated WAF Instance
- Modifying the Protection Status of a Domain Name in Dedicated Mode
- Policy Management
-
Rule Management
- Changing the Status of a Rule
- Querying Global Protection Whitelist (Formerly False Alarm Masking) Rules
- Creating a Global Protection Whitelist (Formerly False Alarm Masking) Rule
- Deleting a Global Protection Whitelist (Formerly False Alarm Masking) Rule
- Querying the Blacklist and Whitelist Rule List
- Creating a Blacklist/Whitelist Rule
- Updating a Blacklist or Whitelist Protection Rule
- Deleting a Blacklist or Whitelist Rule
- Querying a Data Masking Rule
- Creating a Data Masking Rule
- Updating a Data Masking Rule
- Deleting a Data Masking Rule
- Querying the List of Geolocation Access Control Rules
- Creating a Geolocation Access Control Rule
- Updating a Geolocation Access Control Rule
- Deleting a Geolocation Access Control Rule
- Querying the List of Web Tamper Protection Rules
- Creating a Web Tamper Protection Rule
- Deleting a Web Tamper Protection Rule
- Querying the Reference Table List
- Creating a Reference Table
- Modifying a Reference Table
- Deleting a Reference Table
- Certificate Management
- Event Management
- Querying the Domain Name of a Tenant
-
Managing Websites Protected by Dedicated WAF Engines
- Querying Domain Names Protected by Dedicated WAF Engines
- Adding a Domain Name to a Dedicated WAF Instance
- Modifying a Domain Name Protected by a Dedicated WAF Instance
- Querying Domain Name Settings in Dedicated Mode
- Deleting a Domain Name from a Dedicated WAF Instance
- Modifying the Protection Status of a Domain Name in Dedicated Mode
- Policy Management
-
Rule Management
- Changing the Status of a Rule
- Querying Global Protection Whitelist (Formerly False Alarm Masking) Rules
- Creating a Global Protection Whitelist (Formerly False Alarm Masking) Rule
- Deleting a Global Protection Whitelist (Formerly False Alarm Masking) Rule
- Querying the Blacklist and Whitelist Rule List
- Creating a Blacklist/Whitelist Rule
- Updating a Blacklist or Whitelist Protection Rule
- Deleting a Blacklist or Whitelist Rule
- Querying a Data Masking Rule
- Creating a Data Masking Rule
- Updating a Data Masking Rule
- Deleting a Data Masking Rule
- Querying the List of Geolocation Access Control Rules
- Creating a Geolocation Access Control Rule
- Updating a Geolocation Access Control Rule
- Deleting a Geolocation Access Control Rule
- Querying the List of Web Tamper Protection Rules
- Creating a Web Tamper Protection Rule
- Deleting a Web Tamper Protection Rule
- Querying the Reference Table List
- Creating a Reference Table
- Modifying a Reference Table
- Deleting a Reference Table
- Certificate Management
- Event Management
- Querying the Domain Name of a Tenant
-
Protected Website Management in Cloud Mode
- This API is used to query the list of domain names protected in cloud mode.
- Adding a Domain Name to the Cloud WAF
- Querying Details About a Domain Name by Domain Name ID in Cloud Mode
- Updating Configurations of Domain Names Protected with Cloud WAF
- Deleting a Domain Name from the Cloud WAF
- Changing Protection Status of a Domain Name
- Dedicated Instance Management
-
Managing Websites Protected by Dedicated WAF Engines
- Querying Domain Names Protected by Dedicated WAF Engines
- Adding a Domain Name to a Dedicated WAF Instance
- Modifying a Domain Name Protected by a Dedicated WAF Instance
- Querying Domain Name Settings in Dedicated Mode
- Deleting a Domain Name from a Dedicated WAF Instance
- Modifying the Protection Status of a Domain Name in Dedicated Mode
- Policy Management
-
Rule Management
- Changing the Status of a Rule
- Querying False Alarm Masking Rules
- Creating a Global Protection Whitelist (Formerly False Alarm Masking) Rule
- Deleting a False Alarm Masking Rule
- Querying the Blacklist and Whitelist Rule List
- Creating a Blacklist/Whitelist Rule
- Updating a Blacklist or Whitelist Protection Rule
- Deleting a Blacklist or Whitelist Rule
- Querying a Data Masking Rule
- Creating a Data Masking Rule
- Updating a Data Masking Rule
- Deleting a Data Masking Rule
- Querying the List of Geolocation Access Control Rules
- Creating a Geolocation Access Control Rule
- Updating a Geolocation Access Control Rule
- Deleting a Geolocation Access Control Rule
- Querying the List of Web Tamper Protection Rules
- Creating a Web Tamper Protection Rule
- Deleting a Web Tamper Protection Rule
- Querying the Reference Table List
- Creating a Reference Table
- Modifying a Reference Table
- Deleting a Reference Table
- Certificate Management
- Dashboard
- Event Management
- Querying the Domain Name of a Tenant
-
Managing Websites Protected by Dedicated WAF Engines
- Appendix
- Change History
-
User Guide (Paris)
Nesta página
Mostrar todos
Central de ajuda/
Web Application Firewall/
Guia de usuário/
Monitoramento/
Configuração de regras de monitoramento de alarmes
Copiado.
Configuração de regras de monitoramento de alarmes
Atualizado em 2023-09-21 GMT+08:00
Você pode definir regras de alarme do WAF para personalizar os objetos monitorados e as políticas de notificação e definir parâmetros como o nome da regra de alarme, o objeto monitorado, a métrica, o limite, o escopo de monitoramento e se deseja enviar notificações. Isso ajuda você a aprender o status de proteção do WAF em tempo hábil.
Pré-requisitos
Você conectou um nome de domínio ao WAF ou adquiriu uma instância dedicada do WAF.
Procedimento
- Efetue login no console de gerenciamento.
- Clique em
 no canto superior esquerdo do console de gerenciamento e selecione uma região ou projeto.
no canto superior esquerdo do console de gerenciamento e selecione uma região ou projeto. - Clique em
 no canto superior esquerdo da página e escolha Management & Governance > Cloud Eye.
no canto superior esquerdo da página e escolha Management & Governance > Cloud Eye. - No painel de navegação à esquerda, escolha Alarm Management > Alarm Rules.
- No canto superior direito da página, clique em Create Alarm Rule.
- Defina o nome da regra de alarme e selecione um projeto empresarial ao qual a regra de alarme pertence.
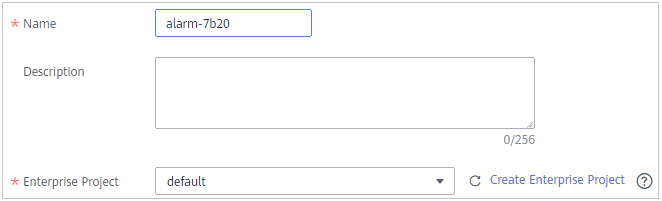
- Selecione Web Application Firewall na lista suspensa Resource Type e selecione uma dimensão, escopo de monitoramento, modelo de alarme e se deseja enviar uma notificação. Figura 1 mostra um exemplo.
- Clique em Create. Na caixa de diálogo exibida, clique em OK.
Tópico principal: Monitoramento
Feedback
Esta página foi útil?
Deixar um comentário
Obrigado por seus comentários. Estamos trabalhando para melhorar a documentação.
O sistema está ocupado. Tente novamente mais tarde.







