Classification and Grading of Data Assets on the Cloud
Data asset classification and grading involve categorizing data based on identification rules and assigning it to different levels according to its sensitivity, importance, and potential impact of leakage. This ensures data is protected appropriately to its significance and impact, while also meeting compliance requirements.
DSC offers a sensitive data identification function and defines 10 sensitivity levels for refined data management. It assists enterprises or organizations in monitoring the flow of sensitive data, formulating corresponding data security policies, and quickly identifying and addressing issues when data leakage or other security events occur.
This section describes how to quickly classify and grade cloud data assets (DSC Standard Edition), including purchasing DSC, authorizing the database, creating a sensitive data identification task, and viewing the classification and grading result.
Procedure
|
Procedure |
Description |
|---|---|
|
Step 1: Purchase DSC and authorize DSC to access your cloud assets. |
Purchase DSC and choose the version specifications (using the standard edition as an example) and the extension package. Complete the cloud asset authorization to streamline access policy permissions between other cloud services and DSC. |
|
Step 2: Authorize DSC to access database assets for data identification. |
Sensitive data identification, data masking, and database watermark injection/extraction can only be performed once the database and big data assets are authorized. Upon completion of database authorization, DSC can access the database to retrieve data for sensitive data identification and masking. |
|
Create an identification task to identify sensitive data of assets and classify and grade data based on the selected identification template. |
|
|
View the classification and grading result to implement protection for data assets. |
Preparations
- Before purchasing DSC, create a Huawei account and subscribe to Huawei Cloud. For details, see Signing Up for a HUAWEI ID and Enabling Huawei Cloud Services and Real-Name Authentication.
If you have enabled Huawei Cloud services and completed real-name authentication, skip this step.

Real-name authentication is required only when you buy or use cloud services provisioned in the Chinese mainland.
- When purchasing yearly/monthly resources, make sure that your account has sufficient balance, or you may fail to pay to your DSC orders.
- Make sure your account has DSC permissions assigned. For details, see Creating a User Group and Assigning DSC Permissions.
Table 1 DSC system-defined permissions Policy
Description
Type
Dependency
DSC DashboardReadOnlyAccess
Read-only permission for the dashboard of DSC
System-defined policy
None
DSC FullAccess
All permissions for DSC
System-defined policy
To purchase a yearly/monthly RDS DB instance, you need to configure the following actions:
bss:order:update
bss:order:pay
DSC ReadOnlyAccess
Read-only permission for DSC
System-defined policy
None
Step 1: Purchase DSC and Authorize DSC to Access Your Cloud Assets
- Log in to the management console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane on the left, click
 . Choose .
. Choose . - If you are a first-time user, click Buy DSC.
- On the Buy DSC page, set the purchase parameters listed in Table 2 and complete the payment.
Table 2 Parameters for purchasing an instance Parameter
Example Value
Description
Edition and specifications
Standard
The standard edition supports the asset map, sensitive data identification, and data risk detection functions. If data masking and watermark injection/extraction are required, upgrade the edition by referring to section Upgrading Edition and Specifications.
OBS expansion package
1
An OBS expansion package offers 1 TB (1,024 GB) of OBS storage.
Database expansion package
1
One database expansion package supports the addition of one database (RDS, DWS, self-built databases on ECS, DLI, Elasticsearch, and self-built big data on ECS). For details about the supported database types and versions, see section Constraints.
Required duration
1 month
Select the required duration from one month to three years.
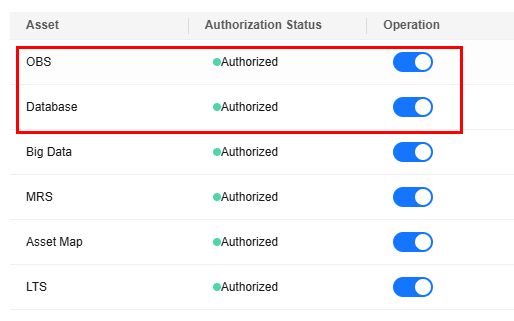
- After the purchase is complete, return to the console and go to the Asset Map page. In the upper left corner of the page, click Modify next to Cloud Asset Authorization to perform authorization, as shown in Figure 1.
After you agree to the authorization, DSC will create agency policies to access your cloud assets based on your choice. For details about the agency policies, see Allowing or Disallowing Access to Cloud Assets.
To stop authorization, ensure that your assets have no ongoing tasks. DSC will delete your authorization information and assets and all related data. Exercise caution when performing this operation.
Step 2: Authorize DSC to Access Database Assets
DSC can automatically discover cloud assets and add self-built data assets. After connecting to DSC and authorizing DSC to access to cloud assets, you can delegate and manage your assets in the asset center.
Sensitive data identification, data masking, and database watermark injection and extraction can be performed only after databases and big data assets are authorized.
- Log in to the management console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane on the left, click
 . Choose .
. Choose . - In the navigation pane on the left, choose .
- On the asset type menu, choose . The Databases tab is displayed.
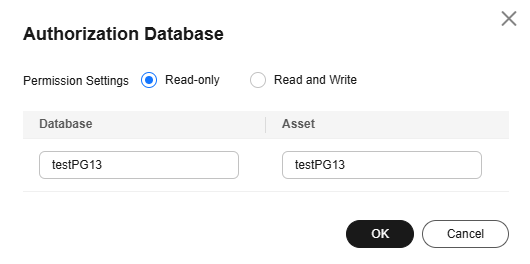
- Click the Database Instances tab. In the Operation column of the target database instance, click Authorize and enter information according to Figure 2.
Read-only permission: Only the sensitive data identification function can be used.
Read and Write permission: The sensitive data identification and data masking functions can be used.
DSC cannot scan and mask sensitive data in MySQL databases within RDS instances where SSL has been enabled.
- After the authorization is complete, click the Databases tab to view the connection status of the authorized database.
Figure 3 Connection status
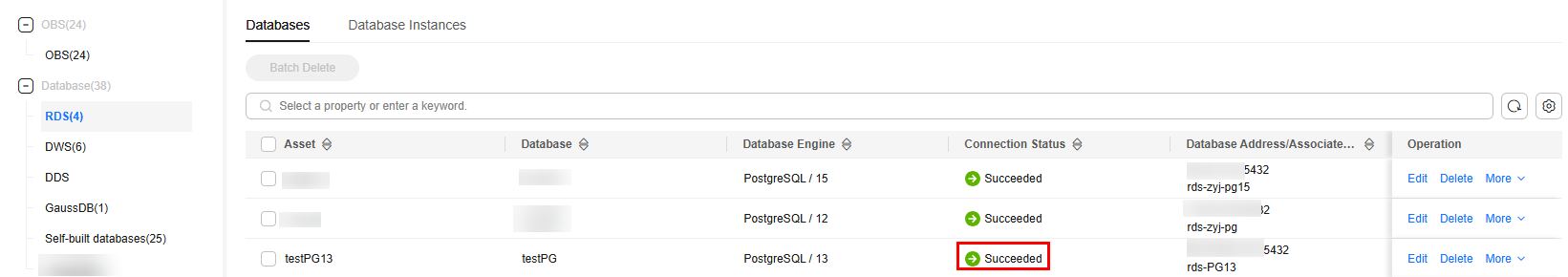
After the asset authorization is complete, the Connection Status of the asset is Checking, which means DSC is checking the database connectivity.
DSC can access the added database normally if the Connection Status of the database is Succeeded.
Step 3: Create a Sensitive Data Identification Task.
DSC identifies sensitive asset data based on the data type and the identification template selected during the creation of the identification task, and then generates an identification result.
- Log in to the management console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane on the left, click
 . Choose .
. Choose . - In the navigation pane on the left, choose Sensitive Data Identification > Identification Task.
- In the upper left corner of the task list, click Create Task.
- In the displayed dialog box, set required parameters based on Table 3.
Table 3 Parameters for creating a task Parameter
Example Value
Description
Task Name
Test task_01
You can customize the task name.
The task name must:
- Contain 4 to 255 characters.
- Consist of letters, digits, underscores (_), and hyphens (-).
- The name must start with a letter.
- Be unique.
Data Type
Database > testPG13
Type of data to be identified. You can select multiple types.
- OBS: DSC is authorized to access your Huawei Cloud OBS assets and identify sensitive data in the assets. For details about how to add OBS assets, see Adding OBS Assets.
- Database: DSC identifies sensitive data of authorized database assets. For details about how to authorize database assets, see Adding a Self-Built Database Instance.
- Big Data: DSC identifies sensitive data of authorized big data assets. For details about how to authorize big data assets, see Adding a Big Data Asset.
- MRS: DSC identifies sensitive data of authorized MRS assets. For details about how to authorize MRS assets, see Adding a Big Data Asset.
- LTS: DSC will identify sensitive data of authorized LTS assets. For details about how to add a log stream, see Adding a Log Stream.
Identification Template
Huawei Cloud Data Security Classification Template
You can select a built-in or custom template. DSC displays data by level and category based on the template you select. For details about how to create an identification template, see Customizing a Rule.
Identification Period
Once
Set the execution policy of the data identification task.
- Once: The task will be executed once at a specified time or immediately.
- Daily: The task is executed at a fixed time every day.
- Weekly: The task is executed at a specified time every week.
- Monthly: The task is executed at a specified time every month.
When to Execute
Now
This parameter is displayed when Identification Period is set to Once.- Now: Select the option and click OK, the system executes the data identification task immediately.
- As scheduled: The task will be executed at a specified time.
(Optional) Topic
None
- Select an existing topic from the drop-down list or click View Topic to create a topic for receiving alarm notifications.
- If no notification topic is configured, you can view the identification result in the identification task list. For details, see Identification Results.
Figure 4 Parameters for creating a task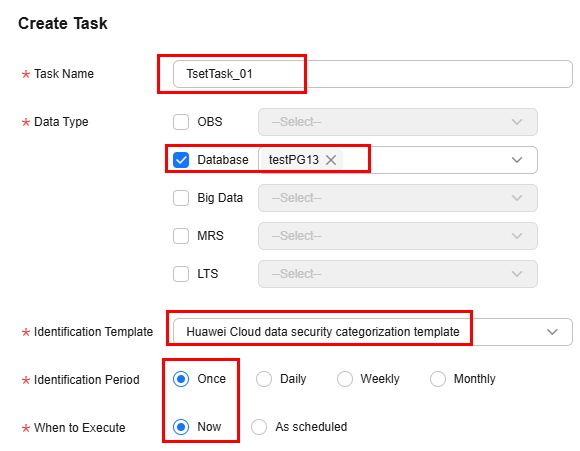
- Click OK. A message is displayed indicating the task is created successfully.
Step 4: View the Classification and Grading Result
- Log in to the management console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - In the navigation pane on the left, click
 . Choose .
. Choose . - In the navigation pane on the left, choose Sensitive Data Identification > Identification Task.
- Click Identification Result in the Operation column of the target task. The result details page is displayed.
Figure 5 Identification result details
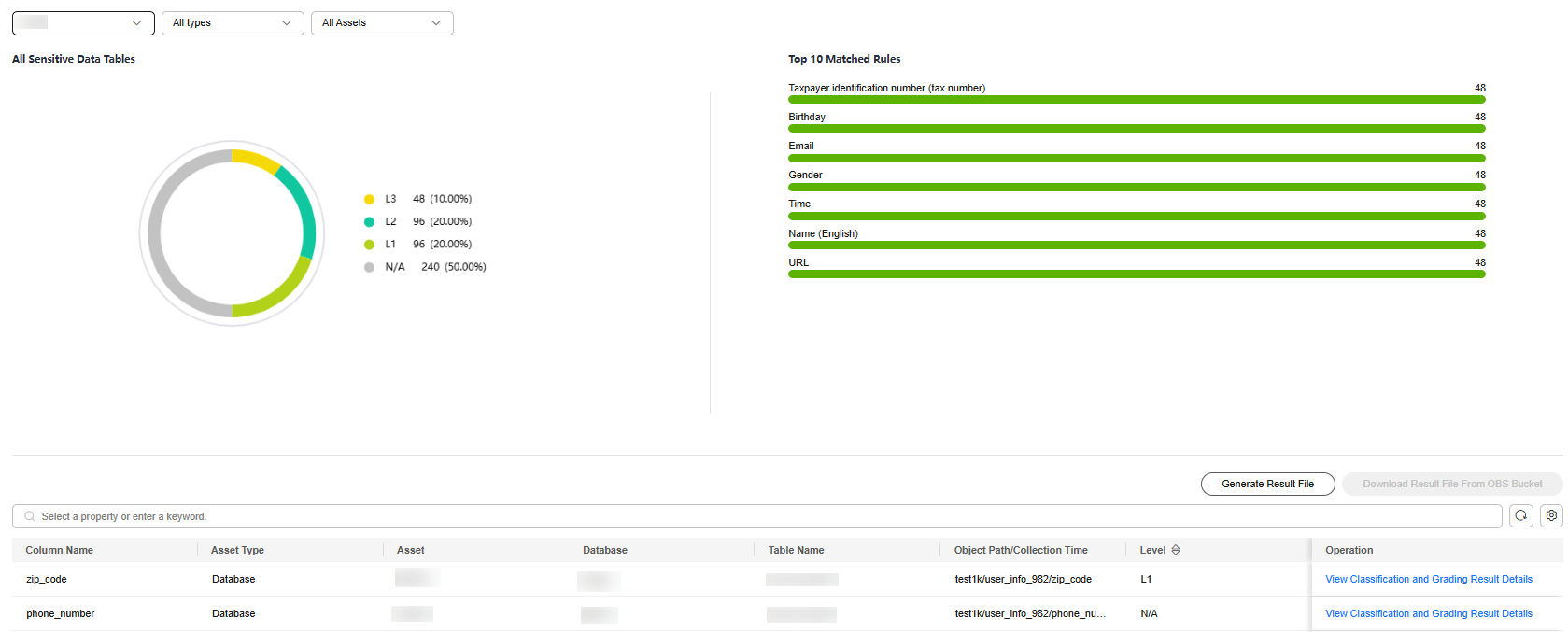
- In the row containing the desired scan object, click View Classification and Grading Result Details in the Operation column. The Classification and Grading Result Details page is displayed.
View the result details and sample data. For details about how to download the identification result, see Downloading the Identification Result.

Click the Sample Data tab to view the sample data that matches the rule. Currently, sample data of the big data and LTS types cannot be viewed.
Related Operations
To protect sensitive information and privacy data after classification and grading and prevent unauthorized access or leakage, you can mask data and add watermarks to the data using the professional edition. For details about how to upgrade to the professional edition, see Upgrading Edition and Specifications.
- For details about how to mask data, see Data Masking. The masked data can be used for development and test, data sharing, and data research.
- For details about how to add data watermarks, see Data Watermarking. A data watermark uniquely identifies an asset to protect the copyright of the asset, helping you track the data leakage source.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot