What Is Host Security Service?
Host Security Service (HSS) helps you identify and manage the assets on your servers; manage programs, file integrity, security operations, and vulnerabilities; check for unsafe settings; and defend against intrusions and web page tampering. There are also advanced protection and security operations functions available to help you easily detect and handle threats.
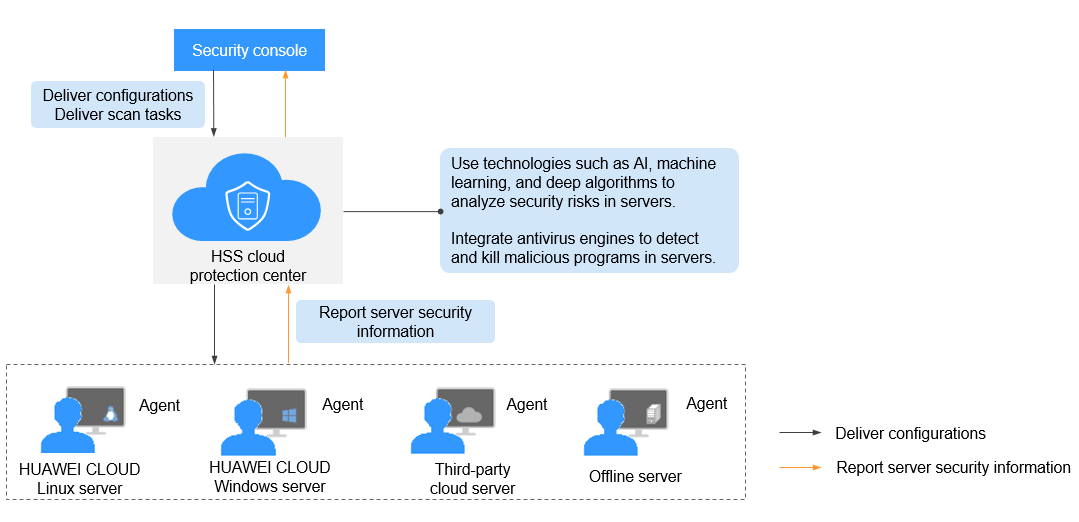
Working Principles
Install the HSS agent on your servers, and you will be able to check the server security status and risks in a region on the HSS console.
Figure 1 illustrates how HSS works.
The following table describes HSS components.
Component |
Description |
|---|---|
Management console |
A visualized management platform, where you can apply configurations in a centralized manner and view the defense status and scan results of servers in a region. |
HSS cloud protection center |
|
Agent |
NOTE:
|
About HSS FAQs
- What Is Host Security Service?
- Where Is HSS Available?
- How Do I Use HSS?
- Can I Upgrade My HSS Edition?
- Does the HSS Agent Conflict with Any Other Security Software?
- What Are the Differences Between HSS and WAF?
- Can HSS Quota Be Shared Between Accounts?
- What Is the HSS Agent?
- Can HSS Quota Be Shared Across Regions?
- Can I Use HSS If My Services Are Not Deployed on HUAWEI CLOUD?
- Can HSS Protect Offline Servers Using the Same Public IP Address?
- Which HSS Edition Do I Need to Purchase to Pass the DJCP MLPS Assessment?
- Can HSS Automatically Detect and Remove Viruses?
- What Are the Differences Between HSS and SA Baseline Checks?
- Can I Add an IP Blacklist in HSS?
- Do I Need to Enable HSS Again After My Server OS Is Reinstalled?
- How Often Does HSS Detect, Isolate, and Kill Malicious Programs?
- How Often Are the HSS Virus Database and Vulnerability Database Updated?
- Do I Have to Deploy HSS on All My Cloud Servers?
- How Do I Enable the HSS Basic Edition?
- How Does HSS Transfer Data?
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbotmore