Configuring a Blocklist/Trustlist Access Policy for a LoadBalancer Service
When using a LoadBalancer Service, you can configure a trustlist or blocklist to specify the IP addresses that are allowed or denied accessing a load balancer listener.
- Trustlist: Only the IP addresses in the list can access the listener.
- Blocklist: The IP addresses in the list are not allowed to access the listener.

After a blocklist or trustlist access policy is configured, if you delete the blocklist or trustlist access policy configuration on the CCE console or delete the target annotation from the YAML file, the configuration on the ELB will be retained.
Prerequisites
- A Kubernetes cluster is available and the cluster version meets the following requirements:
- v1.23: v1.23.12-r0 or later
- v1.25: v1.25.7-r0 or later
- v1.27: v1.27.4-r0 or later
- v1.28: v1.28.2-r0 or later
- Other clusters of later versions
- An IP address group has been created on the ELB console. For details, see Creating an IP Address Group.
Creating a LoadBalancer Service and Configuring a Blocklist/Trustlist Access Policy
- Log in to the CCE console and click the cluster name to access the cluster console.
- Choose Services & Ingresses in the navigation pane, click the Services tab, and click Create Service in the upper right corner.
- Configure Service parameters.
- Service Name: Enter a service name, for example, service-acl.
- Service Type: Select LoadBalancer.
- Service Affinity: Select cluster level or node level as needed. For details about the differences, see Service Affinity (externalTrafficPolicy).
- Selector: Add a label and click Confirm. The Service will use this label to select pods. You can also click Reference Workload Label to use the label of an existing workload. In the dialog box that is displayed, select a workload and click OK.
- Load Balancer
Select a load balancer to be accessed. Only load balancers in the same VPC as the cluster are supported. If no load balancer is available, click Create Load Balancer to create one on the ELB console. Alternatively, select Auto create to create a load balancer. For details about parameter settings, see Table 1.
- Health Check: defaults to Global health check. You can configure this parameter as needed.
- Port
- Protocol: the protocol used by the Service.
- Service Port: the port used by the Service. The port ranges from 1 to 65535.
- Container Port: the port that the workload listens on. For example, Nginx uses port 80 by default.
- Access Control
- Inherit ELB Configurations: CCE does not modify the existing access control configurations on the ELB console.
- Allow all IP addresses: No access control is configured.
- Trustlist: Only the selected IP address group can access the load balancer.
- Blocklist: The selected IP address group cannot access the load balancer.

For clusters of v1.25.16-r10, v1.27.16-r10, v1.28.15-r0, v1.29.10-r0, v1.30.6-r0, v1.31.1-r0, or later, when using a dedicated load balancer, you can select a maximum of five IP address groups at a time for access control.
- Click OK.
apiVersion: v1
kind: Service
metadata:
name: nginx
annotations:
kubernetes.io/elb.id: <your_elb_id> # Load balancer ID. Replace it with the actual value.
kubernetes.io/elb.class: performance # Load balancer type
kubernetes.io/elb.acl-id: <your_acl_id> # ID of an IP address group for accessing a load balancer
kubernetes.io/elb.acl-status: 'on' # Enable access control.
kubernetes.io/elb.acl-type: 'white' # Trustlist for access control
spec:
selector:
app: nginx
ports:
- name: service0
port: 80
protocol: TCP
targetPort: 80
type: LoadBalancer
|
Parameter |
Type |
Description |
|---|---|---|
|
kubernetes.io/elb.acl-id |
String |
|
|
kubernetes.io/elb.acl-status |
String |
This parameter is mandatory when you configure an IP address blocklist or trustlist for a load balancer. Options:
|
|
kubernetes.io/elb.acl-type |
String |
This parameter is mandatory when you configure an IP address blocklist or trustlist for a load balancer. Options:
|
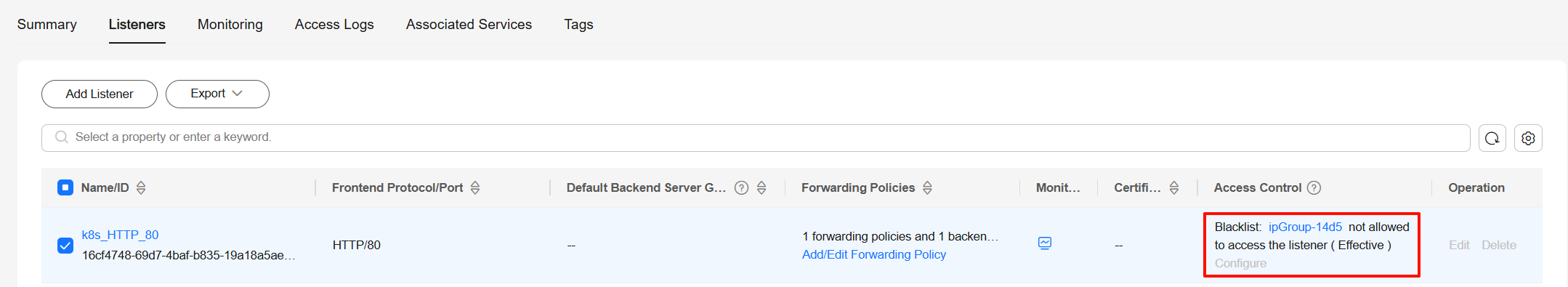
Verifying Configuration
- Log in to the CCE console and click the cluster name to access the cluster console.
- In the navigation pane, choose Services & Ingresses. Locate the row that contains the created Service and click the load balancer name to go to the ELB console.
- Switch to the Listeners tab, locate the listener of the created port, and check whether the option is enabled.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





