Using Third-Party Images
Scenario
Third-party images are container images provided by organizations or individuals other than those in the official image repository and SWR image repository. These images usually contain custom applications, tools, or OSs of specific versions to meet specific service requirements. In a CCE Autopilot cluster, you can create workloads using third-party images pulled through secret authentication.
Prerequisites
If third-party images are used, the CCE Autopilot cluster can access the network environment where the third-party image repository is deployed. The network environment is classified into the following types:
- Private network: If the third-party image repository supports intranet access, consider the following scenarios:
- If the third-party image repository is in the VPC where the cluster is located, the pod can directly pull images over the private network without extra configurations.
- If the third-party image repository and the cluster are in different VPCs in the same region, you can use a VPC peering connection to enable the network connectivity between the two VPCs. Then, the pod can directly pull images over the private network. For details about VPC peering connections, see VPC Peering Connections.
- Public network: If the third-party image repository can only be accessed over the public network, pods need to pull images over the public network. In this case, ensure that the pod can access the public network. You can use either of the following methods to ensure that the pods can access the public network:

When pods pull images over the public network, ensure that the bandwidth is sufficient. If the bandwidth is insufficient, the images may fail to be pulled or may be pulled slowly.
- Configure an SNAT rule for the cluster so that all pods in the cluster can access the public network. After the SNAT rule is configured, you can create workloads by pulling images over the public network. For details, see Accessing the Public Network from a Container.
- Configure an EIP for each pod when creating a workload. Only pods with EIPs bound can access the public network. This method can be used when you create a workload. For more information, see Configuring an EIP for a Pod.
- Direct Connect or VPN: To use images from an on-premises image repository, you need to use Direct Connect or VPN to connect the network environment where the on-premises image repository is located to the VPC where the cluster is located in advance. After the network environment is connected to the VPC, no additional configuration is required.
Using Third-Party Images
Before using a third-party image, create an image pull secret and reference it in the workload to authorize access. This section describes operations performed using the console and kubectl.
The following are operations for you to create a secret on the console and pull a third-party image to create a workload.
- If the third-party image repository has an account and password, create a secret in the cluster as the identity credential for pulling images.
- Log in to the CCE console and click the cluster name to access the cluster console.
- In the navigation pane, choose ConfigMaps and Secrets. On the Secrets tab, click Create Secret.
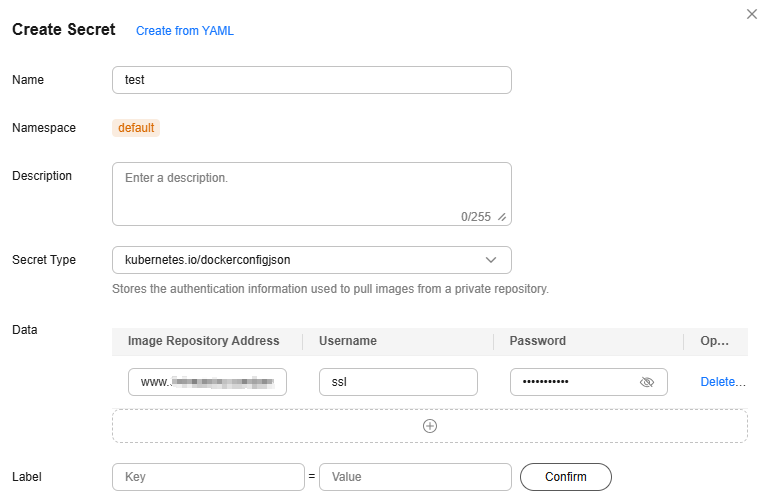
- In the Create Secret dialog box, configure the parameters based on Figure 1 and Table 1. For more information about secrets, see Creating a Secret.
Table 1 Parameters for creating a secret Parameter
Example Value
Description
Name
test
Name for the secret.
Enter up to 253 characters, starting and ending with a lowercase letter or digit. Only lowercase letters, digits, hyphens (-), and periods (.) are allowed.
Secret Type
kubernetes.io/dockerconfigjson
Type of the secret.
The value is fixed at kubernetes.io/dockerconfigjson, indicating that the secret is used for authentication when third-party images are pulled.
Data
Image Repository Address: www.example.com
Username: ssl
Password: xxx
- Image Repository Address: Enter the address of the third-party image repository.
- Username: Enter the username for accessing the third-party image repository.
- Password: Enter the password for accessing the third-party image repository.
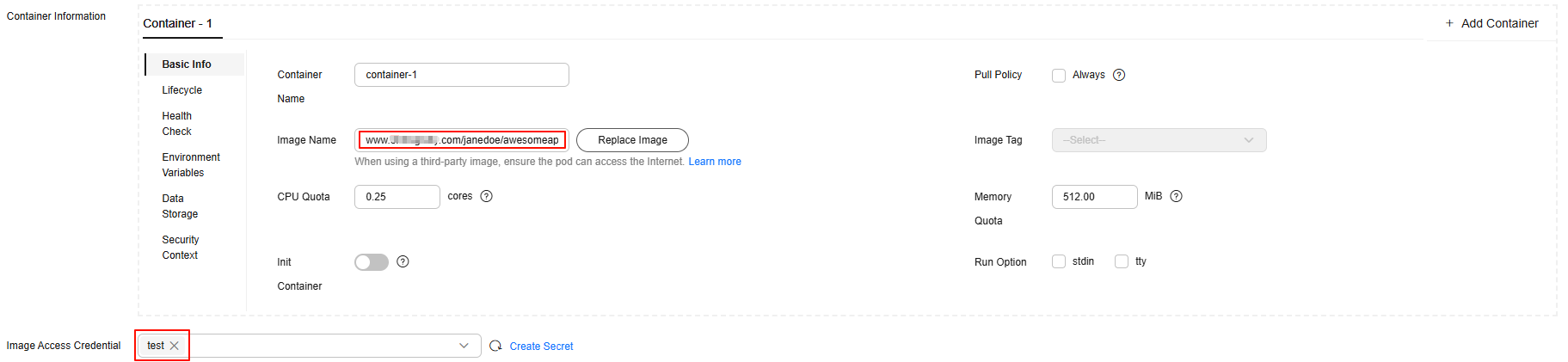
- In the navigation pane, choose Workloads. In the upper right corner of the displayed page, click Create Workload. On the Create Workload page, set Image Name (Container Settings > Container Information > Basic Info) to the third-party image path. Select the secret created in 1 for Image Access Credential.
Figure 2 Third-party image path
- (This step is required only when you need to configure an EIP for a pod.) Add an annotation (Advanced Settings > Labels and Annotations > Pod Annotation) based on Table 2. In this example, the pod's EIP uses a dedicated bandwidth. If you need to configure an EIP with a shared bandwidth, see Configuring an EIP for a Pod.
Figure 3 Adding an annotation
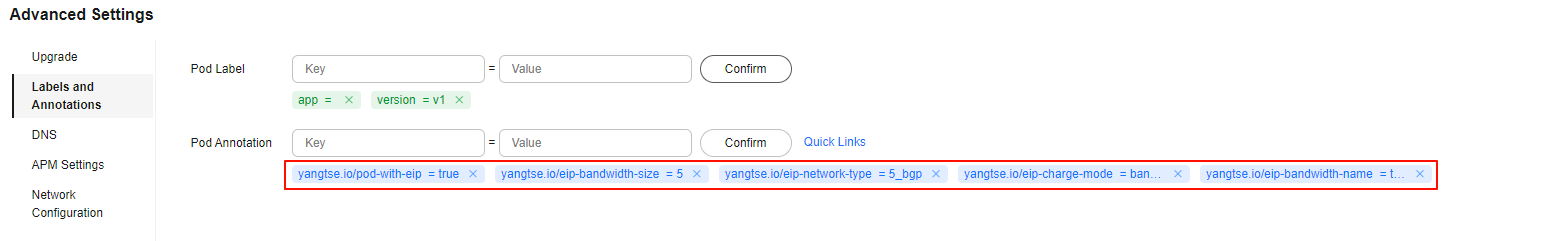
Table 2 Annotations for an EIP with a dedicated bandwidth Annotation
Mandatory
Default Value
Description
Value
yangtse.io/pod-with-eip
Yes
false
Whether to bind an EIP to a pod
false or true
yangtse.io/eip-bandwidth-size
No
5
Bandwidth, in Mbit/s
The value range varies depending on the region and bandwidth billing mode. For details, see the purchase page on the EIP console.
For example, in the CN East-Shanghai1 region, if an EIP is billed by bandwidth, the bandwidth ranges from 1 Mbit/s to 2,000 Mbit/s; if an EIP is billed by traffic, the bandwidth ranges from 1 Mbit/s to 300 Mbit/s.
yangtse.io/eip-network-type
No
5_bgp
EIP type
The types vary by region. For details, see the EIP console.
For example, the following types are supported in the CN East-Shanghai1 region:
- 5_bgp: dynamic BGP
- 5_sbgp: static BGP
yangtse.io/eip-charge-mode
No
None
Billed by traffic or bandwidth
You are advised to configure this parameter. If this parameter is left blank, no billing mode is specified. In this case, the default value of the EIP API in the region is used.
- bandwidth: billed by bandwidth
- traffic: billed by traffic
yangtse.io/eip-bandwidth-name
No
Pod name
Bandwidth name
Enter 1 to 64 characters. Only letters, digits, hyphens (-), underscores (_), and periods (.) are allowed.
- Configure other parameters and click Create Workload. If the workload status changes to Running, the third-party image is successfully pulled.
The following are operations for you to create a secret using kubectl and pull a third-party image to create a workload.
- Use kubectl to connect to the cluster. For details, see Connecting to a Cluster Using kubectl.
- If the third-party image repository has an account and password, you need to create a secret in the cluster as the identity credential for pulling images.
- Create a secret. The secret type is kubernetes.io/dockerconfigjson by default, which indicates that the secret is used for authentication when third-party images are pulled.
kubectl create secret docker-registry test -n default --docker-server=www.example.com --docker-username=ssl --docker-password=xxx --docker-email=example@123.com
In the command, test indicates the secret name, default indicates the namespace where the secret is located, and other parameters are described in the following table.
Table 3 Secret parameters Parameter
Example Value
Description
docker-server
www.example.com
Enter the address of the third image repository.
docker-username
ssl
Enter the username for accessing the third-party image repository.
docker-password
xxx
Enter the password for accessing the third-party image repository.
docker-email
example@123.com
Email address of the third-party image repository. This parameter is optional.
Information similar to the following is displayed:
secret/test created
- Check whether the secret has been created.
kubectl get secret
If the following information is displayed, the secret has been created:
NAME TYPE DATA AGE default-secret kubernetes.io/dockerconfigjson 1 41h paas.elb cfe/secure-opaque 1 41h test kubernetes.io/dockerconfigjson 1 16s
- Create a secret. The secret type is kubernetes.io/dockerconfigjson by default, which indicates that the secret is used for authentication when third-party images are pulled.
- Create a workload using a third-party image.
- Create a YAML file for creating a workload. In this example, the file name is deployment.yaml. You can change it as needed.
vim deployment.yamlExample file content:apiVersion: apps/v1 kind: Deployment metadata: name: foo namespace: default spec: replicas: 1 selector: matchLabels: app: foo strategy: type: RollingUpdate template: metadata: labels: app: foo annotations: # Parameters in annotations are involved only when an EIP is required for the pod. yangtse.io/eip-bandwidth-name: test yangtse.io/eip-bandwidth-size: '5' yangtse.io/eip-charge-mode: bandwidth yangtse.io/eip-network-type: 5_bgp yangtse.io/pod-with-eip: 'true' spec: containers: - image: www.example.com/janedoe/awesomeapp:v1 # Third-party image path imagePullPolicy: Always name: foo imagePullSecrets: - name: test # Use the created secret for identity authentication when images are pulled.
Parameters in annotations are involved only when an EIP is required for a pod. In this example, the EIP uses a dedicated bandwidth. If you need to configure an EIP with a shared bandwidth, see Configuring an EIP for a Pod.
Table 4 Annotations for an EIP with a dedicated bandwidth Annotation
Mandatory
Default Value
Description
Value
yangtse.io/pod-with-eip
Yes
false
Whether to bind an EIP to a pod
false or true
yangtse.io/eip-bandwidth-size
No
5
Bandwidth, in Mbit/s
The value range varies depending on the region and bandwidth billing mode. For details, see the purchase page on the EIP console.
For example, in the CN East-Shanghai1 region, if an EIP is billed by bandwidth, the bandwidth ranges from 1 Mbit/s to 2,000 Mbit/s; if an EIP is billed by traffic, the bandwidth ranges from 1 Mbit/s to 300 Mbit/s.
yangtse.io/eip-network-type
No
5_bgp
EIP type
The types vary by region. For details, see the EIP console.
For example, the following types are supported in the CN East-Shanghai1 region:
- 5_bgp: dynamic BGP
- 5_sbgp: static BGP
yangtse.io/eip-charge-mode
No
None
Billed by traffic or bandwidth
You are advised to configure this parameter. If this parameter is left blank, no billing mode is specified. In this case, the default value of the EIP API in the region is used.
- bandwidth: billed by bandwidth
- traffic: billed by traffic
yangtse.io/eip-bandwidth-name
No
Pod name
Bandwidth name
Enter 1 to 64 characters. Only letters, digits, hyphens (-), underscores (_), and periods (.) are allowed.
- Create the workload.
kubectl create -f deployment.yamlIf information similar to the following is displayed, the workload is being created:
deployment.apps/foo created
- Check the workload status.
kubectl get deployment
If the value of READY is 1/1, the pod created for the workload is available. This means the workload has been created.
NAME READY UP-TO-DATE AVAILABLE AGE foo 1/1 1 1 4m59s
- Create a YAML file for creating a workload. In this example, the file name is deployment.yaml. You can change it as needed.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot