How Do I Configure a VPN on an On-premises Device? (Configuring the VPN on a Huawei USG6600 Series Firewall)
Due to the symmetry of the tunnel, the VPN parameters configured on the cloud must be the same as those configured in your on-premises data center. If they are different, a VPN cannot be established.
To set up a VPN, you also need to configure the IPsec VPN on your on-premises router or firewall. The configuration method may vary depending on your network device in use. For details, see the configuration guide of your network device.
The following uses a Huawei USG6600 series firewall running V100R001C30SPC300 as an example to describe how to configure a VPN on an on-premises device.
Assume that the on-premises subnets are 192.168.3.0/24 and 192.168.4.0/24, the VPC subnets are 192.168.1.0/24 and 192.168.2.0/24, and the public IP address of the IPsec tunnel egress in the VPC is XXX.XXX.XX.XX, which can be obtained from the local gateway parameters of the IPsec VPN in the VPC.
Procedure
- Log in to the CLI of the firewall.
- Check firewall version information.
display version 17:20:502017/03/09 Huawei Versatile Security Platform Software Software Version: USG6600 V100R001C30SPC300 (VRP (R) Software, Version 5.30)
- Create an access control list (ACL) and bind it to the target VPN instance.
acl number 3065 vpn-instance vpn64 rule 1 permit ip source 192.168.3.0 0.0.0.255 destination 192.168.1.0 0.0.0.255 rule 2 permit ip source 192.168.3.0 0.0.0.255 destination 192.168.2.0 0.0.0.255 rule 3 permit ip source 192.168.4.0 0.0.0.255 destination 192.168.1.0 0.0.0.255 rule 4 permit ip source 192.168.4.0 0.0.0.255 destination 192.168.2.0 0.0.0.255 q
- Create an IKE proposal.
ike proposal 64 dh group5 authentication-algorithm sha1 integrity-algorithm hmac-sha2-256 sa duration 3600 q
- Create an IKE peer and refer to the created IKE proposal. The peer IP address is 93.188.242.110.
ike peer vpnikepeer_64 pre-shared-key ******** (******** specifies the pre-shared key.) ike-proposal 64 undo version 2 remote-address vpn-instance vpn64 93.188.242.110 sa binding vpn-instance vpn64 q
- Create an IPsec protocol.
IPsec proposal IPsecpro64 encapsulation-mode tunnel esp authentication-algorithm sha1 q
- Create an IPsec policy, and bind the IKE policy and IPsec proposal to it.
IPsec policy vpnIPsec64 1 isakmp security acl 3065 pfs dh-group5 ike-peer vpnikepeer_64 proposal IPsecpro64 local-address xx.xx.xx.xx q
- Apply the IPsec policy to the subinterface.
interface GigabitEthernet0/0/2.64 IPsec policy vpnIPsec64 q
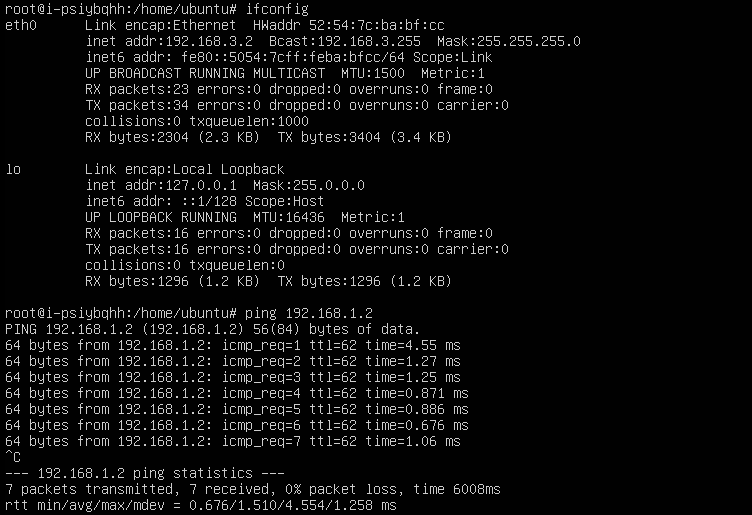
- Test connectivity.
Test the connectivity between your ECSs on the cloud and servers in your on-premises data center, as shown in Figure 1.
VPN Negotiation and Interconnection FAQs
- What Devices Can Be Connected to Huawei Cloud Through a VPN?
- What Are VPN Negotiation Parameters? What Are Their Default Values?
- Will an IPsec VPN Connection Be Established Automatically?
- How Do I Configure a VPN on an On-premises Device? (Configuring the VPN on a Huawei USG6600 Series Firewall)
- How Should I Configure an On-premises Gateway When I Use a VPN to Connect to the Cloud?
- Can Huawei Cloud VPN Connect to a Remote Gateway Through a Domain Name?
- How Many Tunnels Does My VPN Connection Have?
- How Do I Allow Specific Servers to Access a VPC Subnet Through a Created VPN Connection?
- Do Huawei Cloud VPNs Have the DPD Mechanism Enabled?
- How Can I Use Security Groups to Prevent ECSs in a VPC From Being Accessed Through a VPN to Implement Security Isolation?
- Will a VPN Connection Be Reestablished After Its Configuration Is Modified?
- Why Cannot I Initiate Negotiation from Amazon Web Services to Huawei Cloud After They Are Interconnected?
- How Do I Configure DPD for Interconnecting with Huawei Cloud?
- What Should I Do If My Firewall Cannot Receive Response Packets from the Huawei Cloud VPN Gateway in the IKE Phase?
- What Should I Do If My Firewall Cannot Receive Response Packets from the Huawei Cloud VPN Subnet?
- What Are the Bits of the DH Groups Used by Huawei Cloud VPN?
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbotmore