Access Keys
An access key comprises an access key ID (AK) and secret access key (SK), and is used as a long-term identity credential to sign your requests for Huawei Cloud APIs. AK is used together with SK to sign requests cryptographically, ensuring that the requests are secret, complete, and correct.
After logging in to the management console, users authorized by the administrator can create and delete access keys on the My Credentials page.
If an IAM user does not have permissions to log in to the management console, the administrator of the user can manage access keys for the user in IAM. For details, see Managing Access Keys for an IAM User.

- If the user accesses cloud services only by using the management console, specify the access type as Management console access and the credential type as Password.
- If the user accesses cloud services only through programmatic calls, specify the access type as Programmatic access and the credential type as Access key.
- If the user needs to use a password as the credential for programmatic access to certain APIs, specify the access type as Programmatic access and the credential type as Password.
- If the user needs to perform access key verification when using certain services in the console, specify the access type as "Programmatic access + Management console access" and the credential type as "Access Key + Password". For example, the user needs to perform access key verification when creating a data migration job in the Cloud Data Migration (CDM) console.
Important Notes
- You can create a maximum of two access keys with identical permissions and unlimited validity. Each access key can be downloaded only once when created. Keep your access keys secure and change them periodically for security purposes. To change an access key, delete it and create a new one.
- Federated users cannot create access keys, but can create temporary access credentials (temporary AK/SK and security tokens). For details, see Temporary Access Key (for Federated Users)
- If you are an IAM user, hover over the username in the upper right corner of the management console, choose Security Settings, click the Critical Operations tab, and check the enabling status of the Access Key Management feature.
- Disabled: All IAM users under the account can manage (create, enable, disable, and delete) their own access keys.
- Enabled: Only the administrator can manage users' access keys.
- If you cannot manage your access keys, request the administrator to perform either of the following operations:
- Manage access keys and send it to you.
- Assign required permissions to you or change access key status. For details about how to assign permissions, see Assigning Permissions to an IAM User. For details about how to change access key status, see Access Key Management.
- If you are an administrator, you can view the AK of an IAM user on the user details page. The SK is kept by the user.
Creating an Access Key
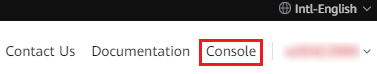
- Log in to Huawei Cloud and click Console in the upper right corner. Figure 1 Accessing the console
- On the management console, hover over the username in the upper right corner and choose My Credentials from the drop-down list. Figure 2 Choosing My Credentials

- Choose Access Keys from the navigation pane.
- Click Create Access Key. If operation protection is enabled, you (the administrator) need to enter a verification code or password for identity authentication when creating an access key.Figure 3 Creating an access key


- You can create a maximum of two access keys. The quota cannot be increased. If you already have two access keys, you can only delete an access key and create a new one.
- To change an access key, delete it and create a new one.
- For newly created access keys, the last used time is the same as the creation time, but will change the next time you use them.
- Download the access key file. After the access keys are created, view the access key ID (AK) in the access key list and view the secret access key (SK) in the downloaded CSV file.

- Download the access key file and keep it properly. If the download page is closed, you will not be able to download the access key. However, you can create a new one.
- Open the CSV file in the lower left corner, or choose Downloads in the browser and open the CSV file.
- Keep your access keys secure and change them periodically for security purposes. To change an access key, delete it and create a new one.
Deleting an Access Key
If your access keys are forgotten or leaked, delete them on the My Credentials page or contact the administrator to delete them in IAM.

Deleted access keys cannot be restored. Make sure that the deleted access keys have not been used for more than one week.
- On the Access Keys page, locate the access key to be deleted and click Disable in the Operation column.
- In the displayed dialog box, click OK.
- Click Delete in the Operation column of the disabled access key. Ensure that the deletion will not affect your services.
If operation protection is enabled, you (the administrator) need to enter a verification code or password for identity authentication when deleting an access key.
Figure 4 Deleting an access key
- In the displayed dialog box, click Yes.
Enabling/Disabling an Access Key
Access keys are enabled by default once being created. To disable an access key, perform the following steps:
- On the Access Keys page, locate the access key to be disabled and click Disable in the Operation column.
- In the displayed dialog box, click Yes.
The method of enabling an access key is similar to that of disabling an access key.
Viewing Access Keys
You can view the access key ID, status, and creation time in the Access Keys area.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





