Before You Start
Intended Audience
The Identity and Access Management (IAM) service is intended for administrators, including:
- Account administrator (with full permissions for all services, including IAM)
- IAM users added to the admin group (with full permissions for all services, including IAM)
- IAM users assigned the Security Administrator role (with permissions to access IAM)
If you want to view, audit, and track the records of key operations performed on IAM, enable Cloud Trace Service (CTS). For details, see Key IAM Operations Supported by CTS.
Accessing the IAM Console
- Log in to Huawei Cloud and click Console in the upper right corner.
Figure 1 Accessing the console

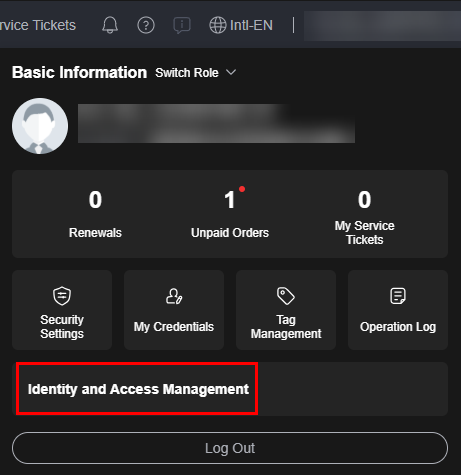
- On the management console, hover over the username in the upper right corner, and choose Identity and Access Management from the drop-down list.
Figure 2 Accessing the IAM console
Account
An account is created after you successfully register with Huawei Cloud. Your account owns resources and pays for the use of these resources. It has full access permissions for your resources. You cannot modify or delete your account in IAM, but you can do so in My Account.
After you log in to your account, you will see a user marked Enterprise administrator on the Users page of the IAM console.

IAM User
You can create users in IAM as the administrator and assign permissions for specific resources. As shown in the following figure, James is an IAM user created by the administrator. IAM users can log in to Huawei Cloud using their account name, usernames, and passwords, and then use resources based on the assigned permissions. IAM users do not own resources and cannot make payments. You can use your account to pay for the resources they use.

Relationship Between an Account and Its IAM Users
An account and its IAM users have a parent-child relationship. The account owns the resources and makes payments for the resources used by IAM users. It has full permissions for these resources.
IAM users are created by the account administrator, and only have the permissions granted by the administrator. The administrator can modify or revoke the IAM users' permissions at any time. Resources used by IAM users in your account are billed to your account. IAM users do not need to make payments themselves.

User Group
You can use user groups to assign permissions to IAM users. After an IAM user is added to a user group, the user has the permissions of the group and can perform operations on cloud services as specified by the permissions. If a user is added to multiple user groups, the user inherits the permissions assigned to all these groups.
The default user group admin has all permissions required to use all of the cloud resources. Users in this group can perform operations on all the resources, including but not limited to creating user groups and users, modifying permissions, and managing resources.

Permission
IAM provides common permissions for different services, such as administrator and read-only permissions. New IAM users do not have any permissions assigned by default. The administrator must add them to one or more groups and attach permissions policies or roles to these groups so that the IAM users can inherit permissions from the groups. IAM users can also assign permissions to themselves. Then the IAM users can perform specific operations on cloud services.
- Roles: A coarse-grained authorization strategy that defines permissions by job responsibility. Only a limited number of service-level roles are available for authorization. Cloud services often depend on each other. When you grant permissions using roles, you also need to attach any existing role dependencies. Roles are not ideal for fine-grained authorization and least privilege access.
- Policies: A fine-grained authorization strategy that defines permissions required to perform operations on specific cloud resources under certain conditions. This type of authorization is more flexible and is ideal for least privilege access. For example, you can grant users only permission to manage a certain type of Elastic Cloud Servers (ECSs).
When an IAM user granted only ECS permissions accesses other services, a message similar to the following will be displayed.

Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





