How Do I Handle a Brute-force Attack Alarm?
- If a brute-force attack succeeded, take immediate measures to prevent attackers from further actions, such as breaching data, performing DDoS attacks, or implanting ransomware, miners, or Trojans.
- If a brute-force attack was blocked, take immediate measures to enhance your servers.
Mind Map for Troubleshooting
The following mind map describes how to handle a brute-force attack alarm.

Handling the Alarm of a Successful Brute-force Attack
If you received an alarm notification indicating that your account had been cracked, you are advised to harden your servers as soon as possible.
- Log in to the HSS console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - Check whether the IP address that triggered the alarm is valid.
- In the navigation pane, choose .
- In the Alarm Types area, select Abnormal User Behavior > Abnormal logins to view abnormal login alarm events.
- Click the alarm event name. On the details page that is displayed, check the login IP address.
- If the IP address is from a normal user (for example, who entered incorrect password for multiple times but logged in before their account is blocked), your server is not intruded. In this case, you can click Handle and ignore the event.
- If the IP address is invalid, your server may have been intruded.
In this case, mark this event as handled, log in to the intruded server, and change its password to a stronger one. For details, see How Do I Set a Secure Password?
Figure 2 Abnormal logins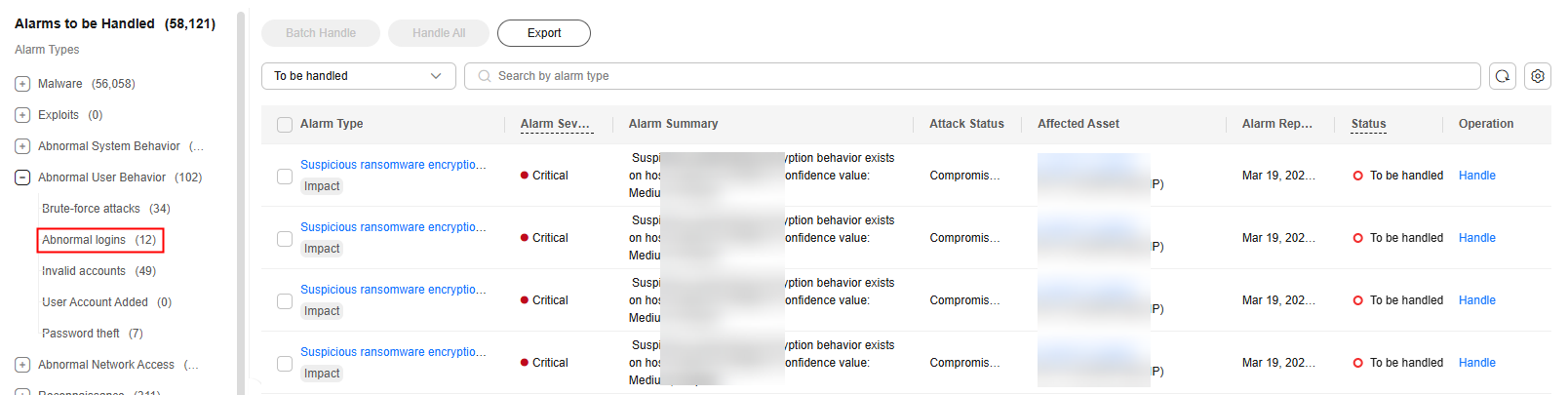
- Check for and eliminate malicious programs.
- In the navigation pane, choose .
- In the Alarm Types area, select Malware > Unclassified malware to filter the unclassified malware.
- In the Alarm Type column, select Malicious program and check alarm events.
You can click an alarm name to view alarm event details.
- If you find malicious programs implanted in your servers, locate them based on their process paths, users running them, and startup time.
To kill a malicious program in an alarm event, click Handle in the Operation column of an alarm and select Isolate and kill.
- If you have confirmed that all the malicious program alarms are false, go to 5.
- If you find malicious programs implanted in your servers, locate them based on their process paths, users running them, and startup time.
- Check for suspicious account change records.
- In the navigation pane on the left, choose Asset Management > Server Fingerprints.
- Click the Account Information tab. Detect suspicious account change records to prevent attackers from creating accounts or escalating account permissions (for example, adding login permissions to an account). For details, see Managing Account Information.
- Check and handle invalid accounts.
- In the navigation pane, choose .
- In the Alarm Types area, select Abnormal User Behavior > Invalid accounts. View and handle the invalid account alarms. For details, see Handling Server Alarms.
- Check for and fix unsafe settings.
Check for and fix weak password complexity policies and unsafe software settings on your servers. For details, see Fixing Unsafe Settings.
- Harden your servers.
For more information, see Hardening Security for SSH Logins to Linux ECSs.
Handling the Alarm of a Blocked Brute-force Attack
If you have enabled the HSS basic edition or higher, HSS will protect your servers against brute-force attacks.
In the basic edition and higher, you can configure a login security policy to specify the brute force cracking determination mode and blocking duration. For details, see Login Security Check
If you have not configured any login security check policies, the default policy is as follows: If five or more consecutive incorrect passwords are entered from the same IP address within 30 seconds, or the total number of incorrect passwords entered from the same IP address reaches 15 within 1 hour, HSS will generate an alarm for the latest user who entered an incorrect password from the IP address, and will block the IP address (for 12 hours by default) to prevent server intrusions caused by brute-force attacks.
If you receive an alarm indicating that an attack source IP address is blocked, check whether the source IP address is a trusted IP address.
Constraints
Procedure
- Log in to the HSS console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - Choose . Choose Abnormal User Behavior > Brute-force attacks to view account brute force events.
Brute-force attack alarms will be generated if:
- The system uses weak passwords, is under brute-force attacks, and attacker IP addresses are blocked.
- Users fail to log in after several incorrect password attempts, and their IP addresses are blocked.
- Check whether the login IP address triggering the alarm is valid.
- If the source IP address is valid,
- To handle a false alarm, click Handle in the row of the alarm event. Mark this event as Ignore or Add to Login Whitelist.
This does not unblock the IP address.
- To unblock the IP address, click View Details under Blocked IP Addresses, select the IP address, and unblock it. Alternatively, you can just wait for it to be automatically unblocked when its blocking duration expires. The default blocking duration is 12 hours.
- To handle a false alarm, click Handle in the row of the alarm event. Mark this event as Ignore or Add to Login Whitelist.
- If the source IP address is invalid or unknown,
Click Handle in the Operation column of the brute-force attack event and select Mark as handled.
Immediately log in to your server and change your password to a stronger one. You can also enhance the defense against brute-force attacks by following the instructions provided in How Do I Defend Against Brute-force Attacks?
- If the source IP address is valid,
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





