Using HSS to Monitor the Integrity of Linux Server Files
Scenario
File integrity means that the file content is not modified, deleted, or damaged without authorization during storage, transmission, and processing, ensuring the authenticity and reliability. Ensure file integrity in server security protection includes but is not limited to the following aspects:
- Data tampering prevention: File integrity monitoring prevents attackers from maliciously tampering with or damaging data and prevents data damage caused by software faults or misoperations of internal personnel, ensuring data integrity and authenticity.
- Improving server security: File integrity monitoring helps you quickly identify unauthorized file modification and take corresponding security measures, reducing potential security risks and improving server defense capabilities.
- Meet compliance requirements: Many industry standards and regulations require enterprises and organizations to protect the integrity and security of sensitive data. By monitoring file integrity, you can avoid legal risks and fines for data security issues.
HSS provides the server security alarm and file integrity management functions. HSS can monitor files or directories on the server and generate alarms for suspicious file or directory modification. This section describes how to use HSS functions to monitor the integrity of Linux server files.
Differentiated File Protection in Server Security Alarm and File Integrity Management
Both the server security alarm function and file integrity management function of HSS provide file integrity monitoring capabilities. The two functions can provide comprehensive security protection for files. For details about the differences, see Table 1.
|
Type |
Server Alarms |
File Integrity Monitoring (FIM) |
|---|---|---|
|
Monitoring type |
Files and directories |
File |
|
Alarm type |
|
Key file change: Monitors key system files (such as ls, ps, login, and top) in real time and generates alarms for file content modification operations. |
|
File protection principle |
Conduct analysis based on behavior characteristics and focus on suspicious behaviors or activities. |
Focus on the integrity of the file and determine whether the current file status is different from the last time by comparing the file status. |
|
Supported OS |
|
Linux |
|
Advantages |
You can monitor not only files, but also directories, and monitor more types for changing files. |
File change records are stored permanently, helping O&M personnel investigate the behavior of attackers. |
Prerequisites
The HSS professional, enterprise, premium, WTP, or container edition has been enabled for the server. For details, see HSS Access Overview.
Procedure
- Configuration file protection policy.
- Log in to the HSS console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane, choose Security Operations > Policies.
- (Optional) If you have enabled the enterprise project function, select an enterprise project from the Enterprise Project drop-down list in the upper part of the page to view its data.
- Click the name of the policy group to access the policy detail list.
HSS provides multiple preset policy groups. After protection is enabled for a server, the preset system group is bound by default. You can also click Copy in the Operation column of a policy group. For details, see Creating a Custom Policy Group.
- Select the File Protection policy and click Enable in the Operation column to enable file protection detection.
The file protection policy is enabled by default. If you have disabled the policy, you need to enable it.
- Click the File Protection policy. The policy details page is displayed.
- Customize the monitoring file directory and monitoring operation type. For details about the parameters, see Table 2.
Table 2 displays the default values of file protection policies. You can customize file protection policies based on the site requirements. To prevent a large number of false alarms caused by file integrity changes and increase the O&M workload, you are advised to configure file protection policies as follows:
- Small-scale trial: When configuring the file protection policy for the first time, you are advised to perform the trial on a few servers.
- Policy tuning: Pay attention to the accuracy and applicability of policies during the validity period, and further improve the configured policies based on the results to reduce false positives.
- Formal application: After multiple policies tuning, if the matching result becomes stable and the false positives almost do not exist, the policy can be applied to more servers.
Figure 1 File protection policy
Table 2 Parameter description Policy Module
Parameter
Default Parameter Value
Description
File Privilege Escalation
Check
Enabled
Whether to enable privilege escalation.
 : enabled
: enabled : disabled
: disabled
Ignored File Paths
- /usr/lib64/hal/hald-runner
- /usr/sbin/hald
- /opt/nfast/sbin/privconn
- /usr/sbin/dhclient
- /usr/sbin/tcpdump
Path of the file to be ignored.
Start the path with a slash (/) and do not end it with a slash (/). Each path occupies a line. No spaces are allowed between path names.
File Integrity
Check
Disabled
Whether to check the integrity of important files. : enabled
: enabled : disabled
: disabled
File Paths
- /bin/ls
- /usr/bin/ls
- /bin/ps
- /usr/bin/ps
- /bin/bash
- /usr/bin/bash
- /bin/login
- /usr/bin/login
- /usr/bin/passwd
- /usr/bin/top
- /usr/bin/killall
- /usr/bin/ssh
- /usr/bin/wget
- /usr/bin/curl
Path of the file to be monitored.
Start the path with a slash (/) and do not end it with a slash (/). Each path occupies a line. No spaces are allowed between path names.
Important File Directory Change
Check
Enabled
Whether to check for the directory changes of important files. : enabled
: enabled : disabled
: disabled
Session IP Whitelist
-
If the file process belongs to the sessions of the whitelisted IP addresses, the process is not audited.
Unmonitored File Types
- swo
- swp
- swpx
- lck
Suffix of the file type that is ignored.
Unmonitored File Paths
- /etc/init.d/.depend.start
- /etc/init.d/.depend.stop
- /etc/init.d/.depend.halt
- /etc/init.d/.depend.boot
- /var/spool/cron/sed*
Path of the file to be ignored.
Monitoring Login Keys
Enable and select Monitor Creation, Monitor Deletion, Monitor Movement, and Monitor Modification.
Whether to enable the monitoring of login keys. : enabled
: enabled : disabled
: disabled
Directory Monitoring Mode
There are many file directories to be monitored. The following describes only some monitoring paths. For details, go to the HSS management console.
- /etc/rc.d/rc.local
- /etc/cron.allow
- /etc/crontab
- /var/spool/cron/root
- /var/spool/cron/root
- /etc/cron.allow
- /etc/passwd
- /etc/profile.d/zzz_euleros_history.sh
- /etc/profile
The value of directory monitoring modes can be Conservative or Sensitive. Compared with the Conservative mode, the Sensitive mode monitors more file or directory paths by default.
In the two modes, some file or directory monitoring paths are preset. You can add or delete them as required.
- File or Directory Path: path of the file or directory to be monitored. Up to 50 paths can be added. Ensure the specified paths are valid.
- Alias: alias of a file or directory path. You can enter a name that is easy to distinguish.
- Monitor Subdirectory: If this option is selected, all files in the corresponding subdirectories are monitored. If it is not selected, subdirectories are not monitored.
- Monitor Creation, Monitor Deletion, Monitor Movement, and Monitor Modification: Select them as needed.
- (Optional) Deploy a policy for the server.
If you configure a file protection policy based on a newly created custom policy group in 1, you need to deploy the new policy group and apply it to the target server after creating and configuring the policy group. For details, see Deploying a Protection Policy.
- View and handle file change alarms.
HSS monitors the files or directory paths configured in the file protection policy in real time and generates alarms once detecting abnormal changes. After receiving an alarm, handle the alarm in a timely manner.
- In the navigation pane on the left, choose Detection & Response > Alarms. The Server Alarms page is displayed.
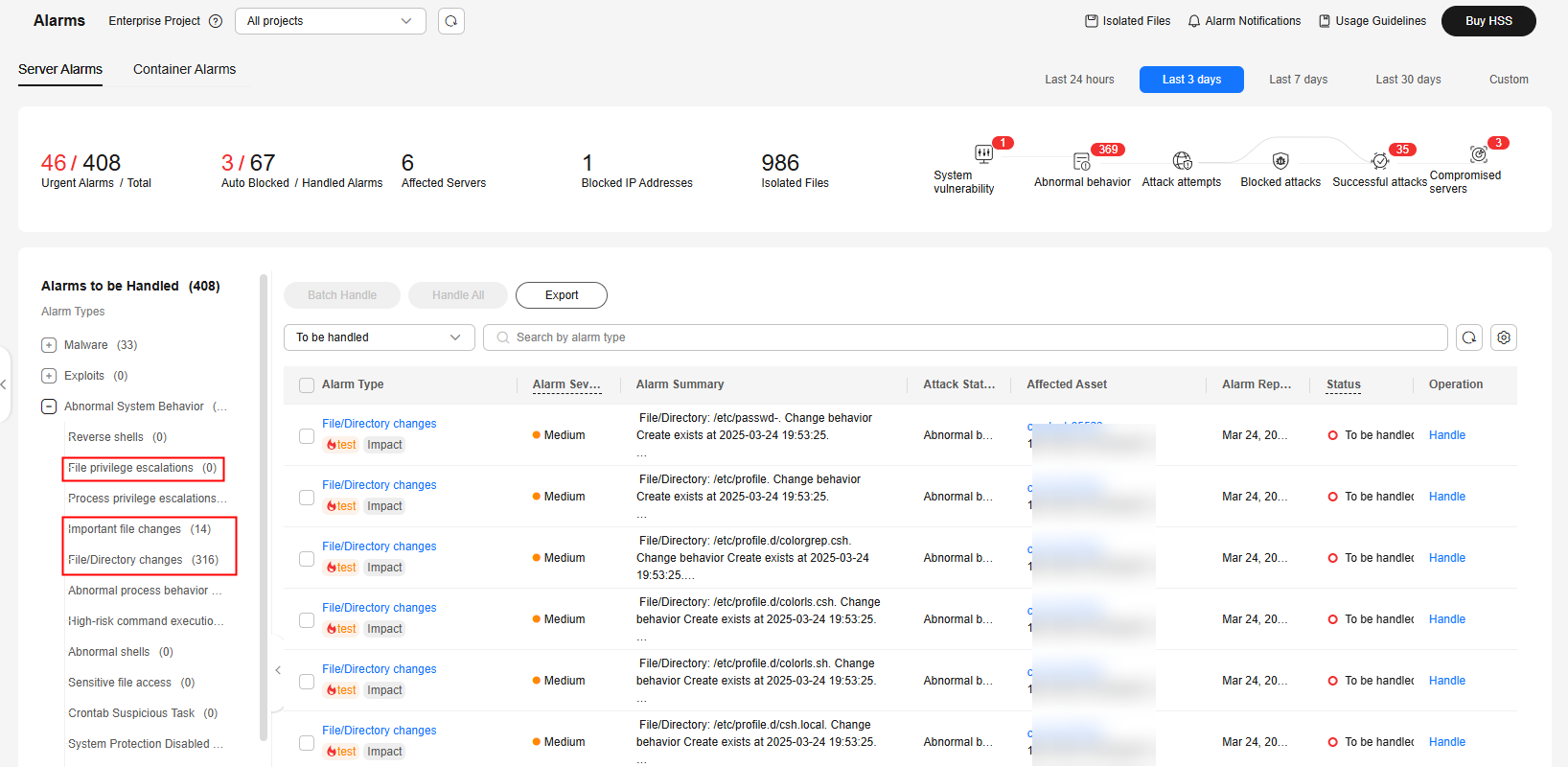
- In the list of alarms to be handled, expand Abnormal System Behavior and focus on several types of alarms related to file changes, as shown in Figure 2.
- Click an alarm of any type. In the alarm list on the right, click the alarm name to view the details.
Figure 3 Viewing alarm details
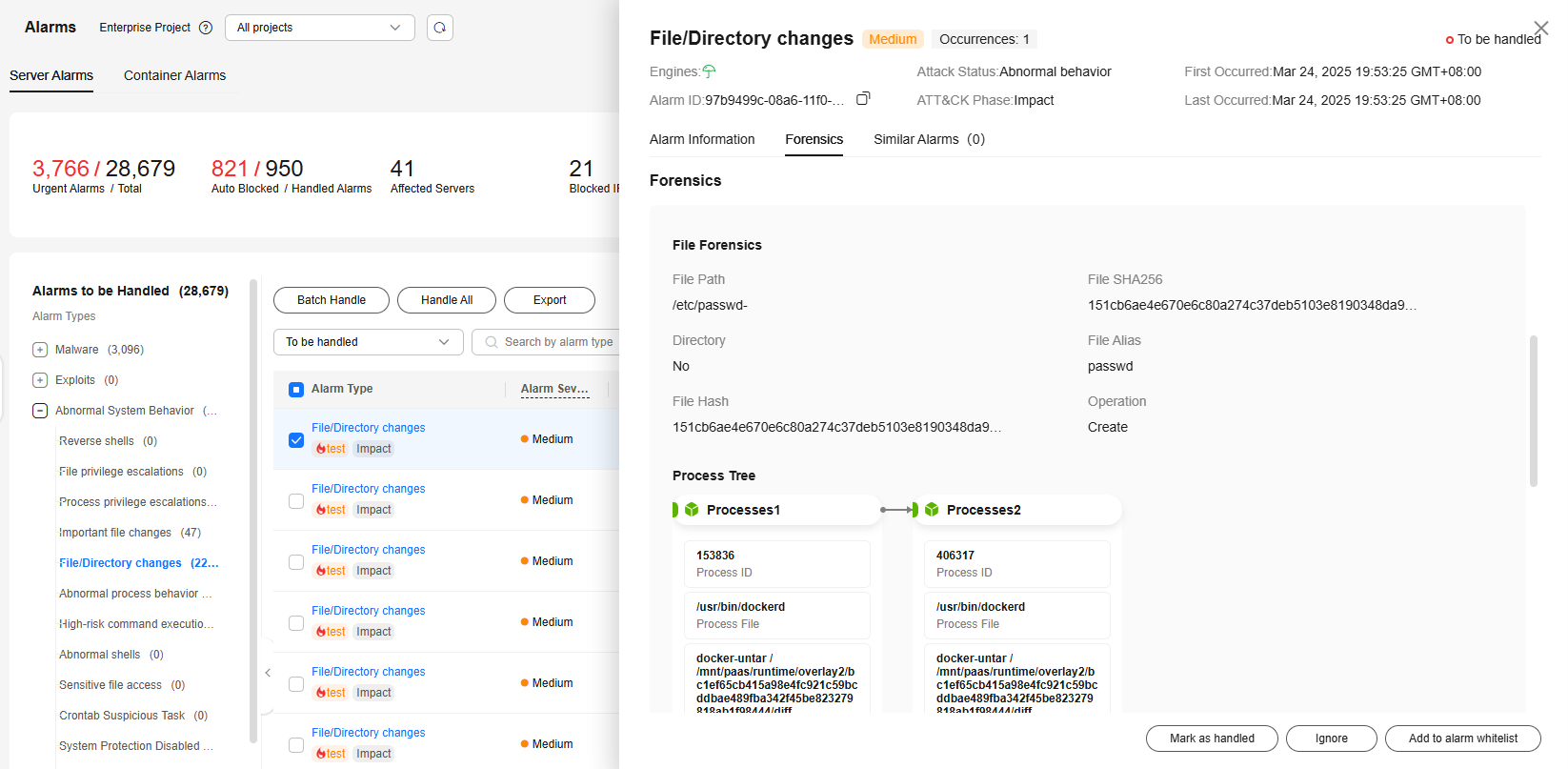
- Handle the alarm based on the Forensics information in the alarm details.
- Alarms caused by normal operations.
In the lower right corner of the alarm details page, click Ignore to ignore the alarm.
- Alarms caused by malicious files or programs.
- Check whether high-risk alarms, such as reverse shell, abnormal login, and malware, are generated on the server. If yes, the server may be attacked. Perform a security check on the server immediately.
- In the lower right corner of the alarm details page, click Mark as handled to clear the alarm.
- Alarms caused by normal operations.
- View the file change history.
The file integrity management page keeps file change records on the server, helping you locate suspicious changes.
- In the navigation pane on the left, choose . The File Integrity Monitoring page is displayed.
- View the file changes on the ECS.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot