Using HSS to Handle Mining Attacks
Scenario
Mining, also called cryptocurrency mining, is a process of obtaining encrypted currencies through intensive computational operations. The process occupies victims' system and network resources and obtaining digital currency. To reduce costs, mining programs are implanted into personal or enterprise computers and mobile devices without permissions.
Take immediate measures to contain the attack to your server, preventing miners from occupying CPU or affecting other applications. If a server is intruded by a mining program, the mining program may penetrate the intranet and persist on the intruded server. In addition, attackers may use mining programs to obtain confidential information, such as confidential files and the usernames and passwords of key assets.
HSS can detect and respond to mining attacks. It can detect and isolate mining virus software. This section describes how to harden your servers to better block intrusions using HSS.
Prerequisites
HSS professional, enterprise, premium, WTP, or container edition has been enabled for the server. For details, see HSS Access Overview.
During Attack: Quickly Block the Mining Program
- Handle the mining alarm and terminate the malicious process.
- Log in to the HSS console.
- Click
 in the upper left corner and select a region or project.
in the upper left corner and select a region or project. - In the navigation pane on the left, choose Detection & Response > Alarms. The Server Alarms page is displayed.
- (Optional) If you have enabled the enterprise project function, select an enterprise project from the Enterprise Project drop-down list in the upper part of the page to view its data.
- Check and handle Mining alarms.
When a mining program is implanted on a server, HSS sends a mining alarm. You need to determine whether the detected mining alarm file is normal. If it is an attack event, you are advised to isolate and kill mining program.
- In the Alarms to Be Handled area, choose .
Figure 1 Mining alarm
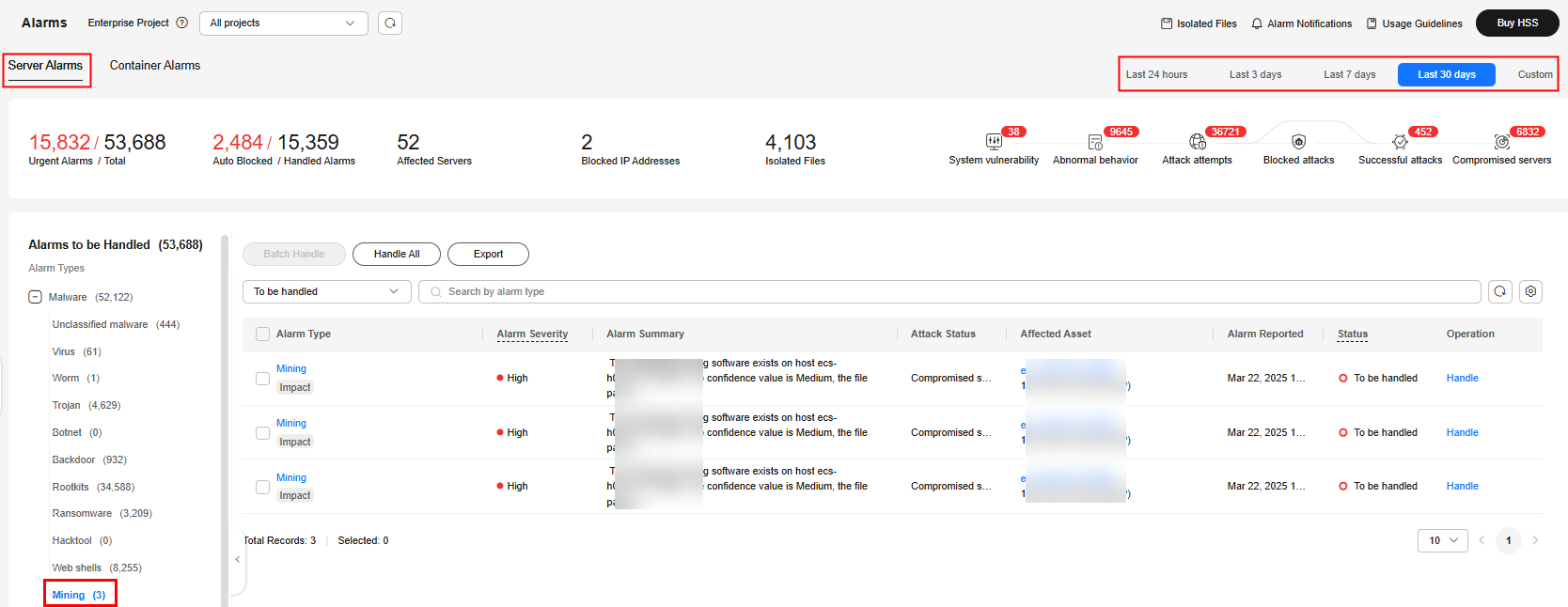
- In the alarm list on the right, click the alarm name to view the alarm details.
- In the alarm list, click Handle in the Operation column.
- In the dialog box that is displayed, set Action to Isolate and kill. Click OK.
If a program is isolated and killed, it will be terminated immediately and no longer able to perform read or write operations. Isolated source files of programs or processes are displayed on the Isolated Files slide-out panel and cannot harm your servers.
- In the upper right corner of the Alarms page, click Isolated Files to view the isolated files.
- In the Alarms to Be Handled area, choose .
- View and handle the Abnormal Process Behavior alarm.
Check Abnormal process behavior events. You need to determine whether the detected abnormal processes are proper. If it is confirmed that processes are unreasonable, you are advised to isolate and kill them.
- In the Alarms to Be Handled area, choose .
Figure 2 Abnormal process behavior

- In the alarm list on the right, click the alarm name to view the alarm details.
- In the alarm list, click Handle in the Operation column.
- In the dialog box that is displayed, set Action to Isolate and kill. Click OK.
- In the upper right corner of the Alarms page, click Isolated Files to view the isolated files.
- In the Alarms to Be Handled area, choose .
- Check auto-startup items to eliminate mining threats.
Some of your auto-startup items were probably created by attackers to start mining programs upon server restart.
- In the navigation tree on the left, choose . The Server Fingerprints page is displayed.
- Click Auto-startup and click the Operation History tab to view the historical changes.
- Scan the attacked server and scan for viruses.
HSS provides the virus scanning and removal function. The function uses the virus detection engine to scan virus files on the server. You can quickly scan attacked servers to eliminate potential malicious threats. You need to determine whether the scanned virus files are proper. If not, you are advised to isolate them.
- In the navigation tree on the left, choose . The Virus Scan page is displayed.
- Click Quick Scan.
- Set parameters related to the Quick Scan task as prompted.
Select the server that is attacked by mining and retain the default values for other parameters. For more information, see Quick Scan.
- Click Scan.
- After the scanning task is complete, you can view the virus files in the lower part of the Virus Scan page.
- In the Operation column of a virus file, click Handle.
- In the dialog box that is displayed, set Action to Manual isolation.
After a file is isolated, the read/write operation cannot be performed on the virus-infected file. Files that have been isolated are added to the Isolated Files. You can restore or delete them in the Isolated Files.
- In the upper right corner of the Virus Scan page, click Isolated Files to view the isolated files.
After Attack: Perform Security Hardening on the Server
After you delete miner programs, harden your servers to better defend against intrusions.
- Linux servers
- Let HSS automatically scan your servers and applications in the early morning every day to help you detect and eliminate security risks.
- Set stronger passwords for all accounts (including system and application accounts), or change the login mode to key-based login.
- Set the security password. For details, see How Do I Set a Secure Password?.
- Use the key to log in to the server. For details, see Using a Private Key to Log In to the Linux ECS.
- Strictly control the usage of system administrator accounts. Grant only the least permissions required for applications and middleware and strictly control their usage.
- Configure access rules in security groups. Open only necessary ports. For special ports (such as remote login ports), only allow access from specified IP addresses or use VPN or bastion hosts to establish your own O&M channels. For details, see Security Group Rules.
- Windows servers
Use HSS to comprehensively check for and eliminate security risks. Improve your account, password, and authorization security.
- Account hardening
Account
Description
Procedure
Ensure default account security.
- Disable user Guest.
- Disable and delete unnecessary accounts. (You are advised to disable inactive accounts for three months before deleting them.)
- Open Control Panel.
- Click Administrative Tools. Open Computer Management.
- Choose System Tools > Local Users and Groups > Users.
- Double-click Guest. In the Guest Properties window, select Account is disabled.
- Click OK.
Assign accounts with only necessary permissions to users.
Create users and user groups of specific types.
Example: administrators, database users, audit users
- Open Control Panel.
- Click Administrative Tools. Open Computer Management.
- Choose System Tools > Local Users and Groups. Create users and groups as needed.
Periodically check and delete unnecessary accounts.
Periodically delete or lock unnecessary accounts.
- Open Control Panel.
- Click Administrative Tools. Open Computer Management.
- Choose System Tools > Local Users and Groups.
- Choose Users or User Groups and delete unnecessary users or user groups.
Do not display the last username.
Forbid the login page from displaying the latest logged in user.
- Open Control Panel.
- Click Administrative Tools. Open Local Security Policy.
- Choose Local Policies > Security Options.
- Double-click Interactive logon: Do not display last user name.
- In the displayed dialog box, select Enable and click OK.
- Password hardening
Password
Description
Procedure
Complexity
In line with the requirements set in How Do I Set a Secure Password.
- Open Control Panel.
- Click Administrative Tools. Open Local Security Policy.
- Choose Account Policies > Password Policy.
- Enable the policy Password must meet complexity requirements.
Maximum password age
In static password authentication mode, force users to change their passwords every 90 days or at shorter intervals.
- Open Control Panel.
- Click Administrative Tools. Open Local Security Policy.
- Choose Account Policies > Password Policy.
- Set Maximum password age to 90 days or shorter.
Account lockout policy
In static password authentication mode, lock a user account if authentication for the user fails for 10 consecutive times.
- Open Control Panel.
- Click Administrative Tools. Open Local Security Policy.
- Choose Account Policies > Account Lockout Policy.
- Set Account lockout threshold to 10 or smaller.
- Authorization hardening
Authorization
Description
Procedure
Remote shutdowns
Assign the permission Force shutdown from a remote system only to the Administrators group.
- Open Control Panel.
- Click Administrative Tools. Open Local Security Policy.
- Choose Local Policies > User Rights Assignment.
- Assign the permission Force shutdown from a remote system only to the Administrators group.
Local shutdown
Assign the permission Shut down the system only to the Administrators group.
- Open Control Panel.
- Click Administrative Tools. Open Local Security Policy.
- Choose Local Policies > User Rights Assignment.
- Assign the permission Shut down the system only to the Administrators group.
User rights assignment
Assign the permission Take ownership of files or other objects only to the Administrators group.
- Open Control Panel.
- Click Administrative Tools. Open Local Security Policy.
- Choose Local Policies > User Rights Assignment.
- Assign the permission Shut down the system only to the Administrators group.
Login
Authorize users to log in to the computer locally.
- Open Control Panel.
- Click Administrative Tools. Open Local Security Policy.
- Choose Local Policies > User Rights Assignment.
- Assign the permission Allow log on locally to the users you want to authorize.
Access from the network
Allow only the authorized users to access this computer from the network (for example, by network sharing). Access from other terminals are not allowed.
- Open Control Panel.
- Click Administrative Tools. Open Local Security Policy.
- Choose Local Policies > User Rights Assignment.
- Assign the permission Access this computer from the network to the users you want to authorize.
- Account hardening
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





