ROLLBACK PREPARED
Description
Cancels a transaction ready for two-phase committing.
Precautions
- The function is only available in maintenance mode (when the GUC parameter xc_maintenance_mode is set to on). Exercise caution when enabling the mode. It is used by maintenance engineers for troubleshooting. Common users should not use the mode.
- Only the user who initiates a transaction or a system administrator can roll back the transaction.
- The transaction function is maintained automatically by the database, and should be not visible to users.
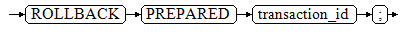
Syntax
ROLLBACK PREPARED transaction_id;

The distributed environment does not support the ROLLBACK PREPARED syntax.
Parameters
transaction_id
Specifies the identifier of the transaction to be committed. The identifier must be different from those for current prepared transactions.
Helpful Links
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





