Creating a Security Group
Scenarios
A security group is a collection of access control rules for ECSs that have the same security protection requirements and are mutually trusted. It controls the traffic that flows in and out of ECSs. This section describes how to create a security group.
Security groups are commonly used to allow or deny network traffic from specific sources or over specific protocols, block certain ports, and define specific access permissions for instances.
When creating an ECS, you must associate it with a security group. If no security group has been created yet, a default security group will be automatically created and associated with the ECS. You can also create a security group and add inbound and outbound rules to allow specific traffic. For more information about security groups, see Overview.
Security Group Template
When creating a security group, you can select a template. The templates have preset inbound and outbound rules. You can select one as needed to quickly create a security group. Table 1 describes the security group template parameters.
|
Template |
Direction |
Protocol & Port |
Source/Destination |
Description |
Scenario |
|---|---|---|---|---|---|
|
General-purpose web server |
Inbound rules |
TCP: 22 (IPv4) |
0.0.0.0/0 |
Allows all IPv4 addresses to access instances in the security group over port 22 (SSH) for remotely logging in to Linux instances. |
|
|
TCP: 3389 (IPv4) |
0.0.0.0/0 |
Allows all IPv4 addresses to access instances in a security group over port 3389 (RDP) for remotely logging in to Windows instances. |
|||
|
TCP: 80 (IPv4) |
0.0.0.0/0 |
Allows all IPv4 addresses to access instances in a security group over port 80 (HTTP) for visiting websites. |
|||
|
TCP: 443 (IPv4) |
0.0.0.0/0 |
Allows all IPv4 addresses to access instances in a security group over port 443 (HTTPS) for visiting websites. |
|||
|
ICMP: All (IPv4) |
0.0.0.0/0 |
Allows all IPv4 addresses to access instances in a security group over any port for using the ping command to test connectivity. |
|||
|
All (IPv4) |
Current security group |
Allows the instances in a security group to communicate with each other over a private network over any protocol and port. |
|||
|
All (IPv6) |
|||||
|
Outbound rules |
All (IPv4) |
0.0.0.0/0 |
Allows all traffic from the instances in the security group to external resources over any protocol and port. |
||
|
All (IPv6) |
::/0 |
||||
|
All ports open |
Inbound Rules |
All (IPv4) |
0.0.0.0/0 |
Allows any IP address to access the instances in a security group over any protocol and port. |
Allow any traffic to enter and leave a security group over any port. This operation has security risks. |
|
All (IPv6) |
::/0 |
||||
|
All (IPv4) |
Current security group |
Allows the instances in a security group to communicate with each other over a private network over any protocol and port. |
|||
|
All (IPv6) |
|||||
|
Outbound rules |
All (IPv4) |
0.0.0.0/0 |
Allows all traffic from the instances in the security group to external resources over any protocol and port. |
||
|
All (IPv6) |
::/0 |
||||
|
Custom |
Inbound rules |
All (IPv4) |
Current security group |
Allows the instances in a security group to communicate with each other over a private network over any protocol and port. |
Deny any external traffic to the instances in a security group. You can add security group rules as required. |
|
All (IPv6) |
|||||
|
Outbound rules |
All (IPv4) |
0.0.0.0/0 |
Allows all traffic from the instances in the security group to external resources over any protocol and port. |
||
|
All (IPv6) |
::/0 |
Procedure
- Log in to the management console and go to the Security Groups page.
- In the upper right corner, click Create Security Group.
The Create Security Group page is displayed.
- Configure basic parameters in the Summary area.
Figure 1 Configuring basic parameters
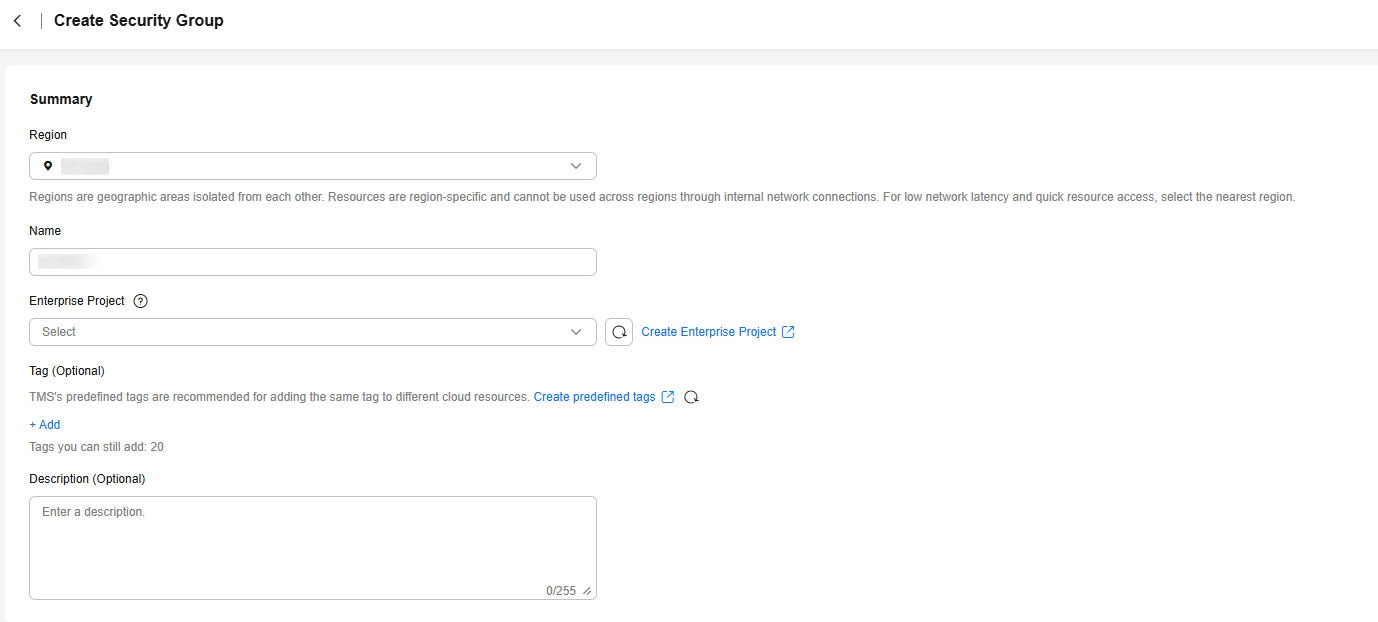
Table 2 Basic parameters Parameter
Description
Example Value
Region
Mandatory
The region where the security group belongs. Select the region nearest to you to ensure the lowest latency possible.
An instance must be in the same region as its associated security group.
CN-Hong Kong
Name
Mandatory
A security group name. The name can contain:- 1 to 64 characters
- Only letters, digits, underscores (_), hyphens (-), and periods (.)
NOTE:You can change the security group name after a security group is created. It is recommended that you give each security group a different name.
sg-AB
Enterprise Project
Mandatory
When creating a security group, you can add the security group to an enabled enterprise project.
An enterprise project facilitates project-level management and grouping of cloud resources and users. The name of the default project is default.
For details about creating and managing enterprise projects, see the Enterprise Management User Guide.
default
Tag
Tag (Optional)
You can add tags to the security group. Tags help you to identify, classify, and search for your security groups.
For details, see Overview.
Tag key: test
Tag value: 01
Description (Optional)
Optional
Supplementary information about the security group.
The security group description can contain a maximum of 255 characters and cannot contain angle brackets (< or >).
N/A
- In the Manage Rules area, configure security group rules as instructed.
- Select a template.
Figure 2 Managing rules
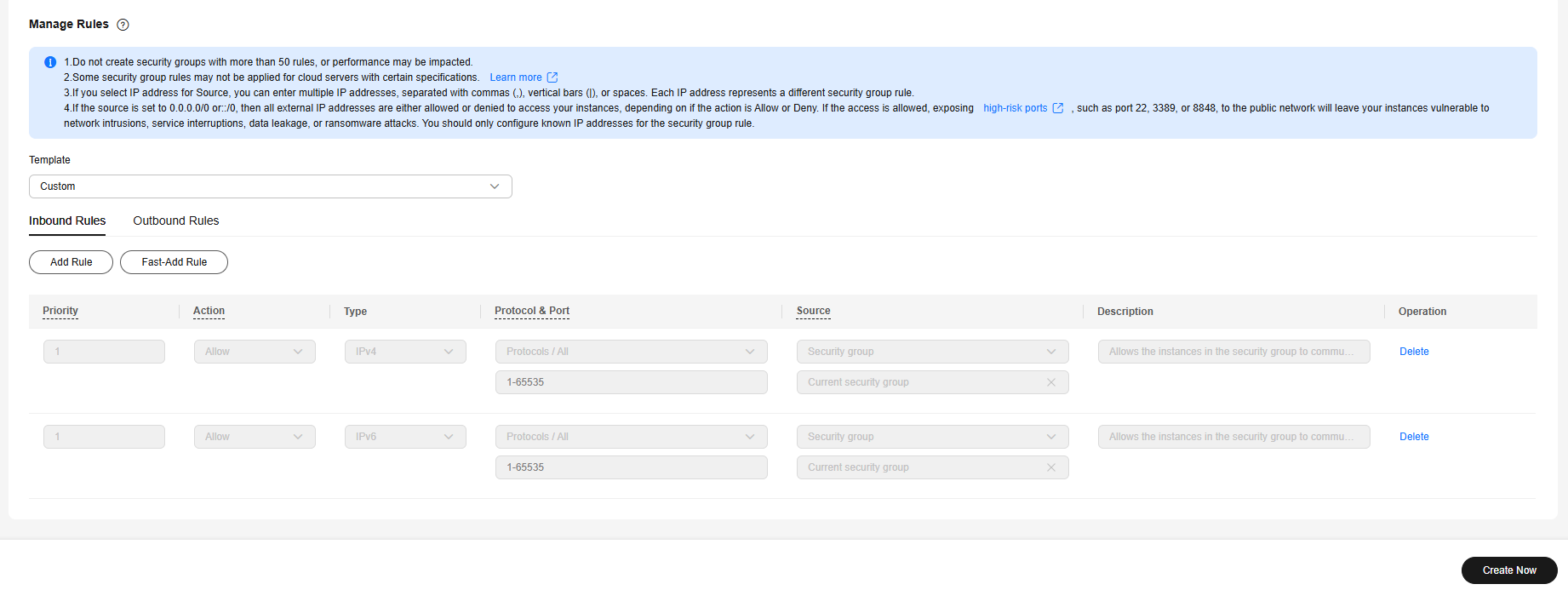
Table 3 Template parameters Parameter
Description
Example Value
Template
Mandatory
There are three templates preset with different inbound and outbound rules for you to select.
- General-purpose web server (default value): The security group that you create using this template is for general-purpose web servers and includes default rules that allow all inbound ICMP traffic and allow inbound traffic on ports 22, 80, 443, and 3389.
- All ports open: Inbound traffic on any port is allowed. This poses security risks, so exercise caution when selecting this template.
- Custom: No port is allowed. You need to customize security group rules.
For details about template parameters and scenarios, see Table 1.
General-purpose web server
- Modify security group rules.
If the preset rules in templates cannot meet service requirements, you can add security group rules or delete or modify preset rules.

- For details about inbound rule parameters, see Table 6. For details about outbound rule parameters, see Table 7.
- If the source of an inbound rule is set to the current security group, you cannot delete this rule. Doing so will prevent instances in the security group from communicating with each other.
- If the destination of an outbound rule is set to 0.0.0.0/0 or ::/0, you cannot delete this rule. Doing so will prevent instances in the security group from accessing external networks.
- Select a template.
- Click Create Now.
- Go to the Security Groups page of the ECS and click the security group name to view the security group details.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





