Configuring Security Group Rules
Scenarios
A security group consists of inbound and outbound rules to control the traffic that is allowed to flow into or out of ECSs in the security group. This section describes how to add and modify security group rules.
Before configuring security group rules, you need to plan rules for communications among instances in the security group. For details about examples of configuring common security group rules, see Security Group Configuration Examples. For details about default security group rules, see Default Security Groups and Rules. For details about common security group ports, see Common ECS Ports.
You can use security group rules in the following scenarios:
- If an instance needs to provide services for external systems, add an inbound rule to allow external requests to the instance.
- If there are attacks to an instance from external networks, add an inbound rule to deny external requests that have security risks.
- If an instance needs to access the Internet, add an outbound rule to allow requests from the instance to the Internet.
- If you no longer need to control certain inbound or outbound traffic, you can delete the corresponding security group rules to simplify the rule configuration.
- If you need to copy rules from other security groups, you can import or export security group rules or clone a security group.
Notes
- Configuring security group rules may interrupt your services or cause network security risks. Learn about the impact on your services in advance.
- Add as fewer rules as possible. Constraints on Using Security Groups lists the constraints on the number of rules in a security group.
- After allowing traffic over a port in a security group rule, ensure that the port used by the instance is opened. For details, see Checking Whether a Port Is Enabled on an ECS.
- If the source is set to 0.0.0.0/0 or ::/0, then the access from all external IP addresses is either allowed or denied, depending on if the action is Allow or Deny. If the access is allowed, exposing high-risk ports, such as port 22, 3389, or 8848, to the public network will leave your instances vulnerable to network intrusions, causing service interruptions, data leakage, or ransomware attacks. You should only configure known IP addresses for the security group rule.
- Security group rules are like a whitelist. If there are no rules that allow or deny specific traffic, the security group denies all traffic to or from the instances in it.
- The inbound rules in Table 1 ensure that instances in the security group can communicate with each other. Do not modify or delete these rules.
- The outbound rules in Table 1 allow instances in the security group to access public networks. If you modify or delete these rules, instances in the security group may fail to access public networks. Exercise caution when performing this operation.
- By default, instances in the same security group can communicate with each other. If instances in the same security group cannot communicate with each other, possible causes are as follows:
- The inbound rules for communication between these instances are deleted. Table 1 shows the inbound rules.
- Different VPCs cannot communicate with each other. The instances belong to the same security group but different VPCs.
You can connect VPCs in different regions using VPC peering connections.
Procedure
- Log in to the ECS console and access the ECS list page.
- On the Elastic Cloud Server page, click the name of the target ECS.
The ECS details page is displayed.
- Click the Security Groups tab, expand the information of the security group, and view security group rules.
- Click the security group ID.
The system automatically switches to the security group details page.
- Configure inbound rule parameters as prompted. You can add multiple inbound rules one by one.
Figure 1 Add Inbound Rule
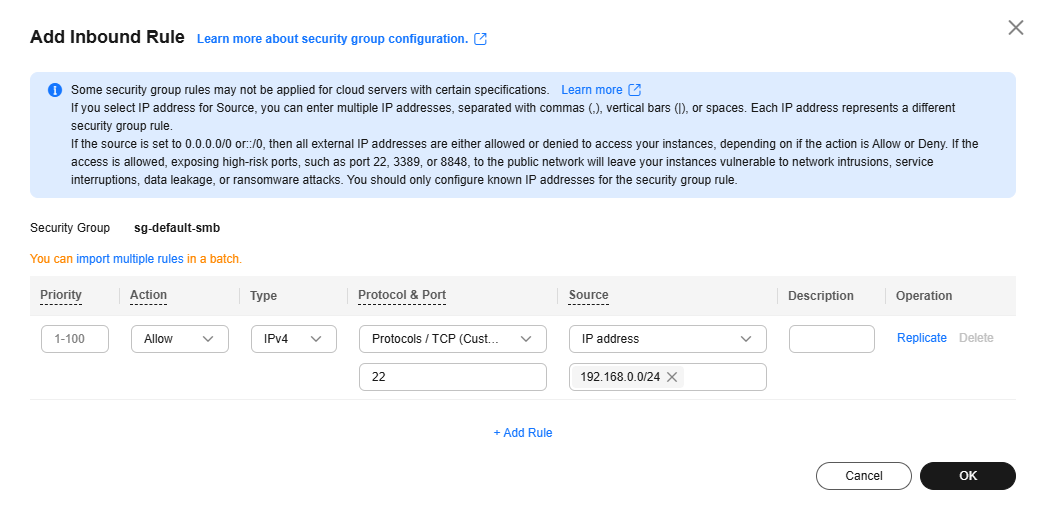
Table 2 Inbound rule parameter description Parameter
Description
Example Value
Priority
The security group rule priority.
The priority value ranges from 1 to 100. The default value is 1 and has the highest priority. The security group rule with a smaller value has a higher priority.
1
Action
The value can be Allow or Deny.- If the Action is set to Allow, traffic is allowed to access the cloud servers in the security group over specified ports.
- If the Action is set to Deny, traffic is denied to access the cloud servers in the security group over specified ports.
Security group rules are matched by priority and then by action. Deny rules take precedence over allow rules. For more information, see How Traffic Matches Security Group Rules.
Allow
Type
Source IP address version. You can select:- IPv4
- IPv6
IPv4
Protocol & Port
The network protocol used to match traffic in a security group rule. The protocol can be All, TCP, UDP, GRE, or ICMP.
TCP
Destination port used to match traffic in a security group rule. The value can be from 1 to 65535.
Inbound rules control incoming traffic over specific ports to instances in the security group.
Enter ports in any of the following formats:- Individual port: Enter a port, such as 22.
- Consecutive ports: Enter a port range, such as 22-30.
- Non-consecutive ports: Enter ports and port ranges, such as 22,23-30. You can enter a maximum of 20 ports and port ranges. Each port range must be unique.
- All ports: Leave it empty or enter 1-65535.
22, 22-30
Source
Used to match the source of an external request. The source can be:- IP address: The source is a fixed IP address. You can enter or paste multiple IP addresses separated by commas (,). Each IP address represents a different security group rule.
- Single IP address: IP address/mask
Example IPv4 address: 192.168.10.10/32
Example IPv6 address: 2002:50::44/128
- IP address range in CIDR notation: IP address/mask
Example IPv4 address range: 192.168.52.0/24
Example IPv6 address range: 2407:c080:802:469::/64
- Any IP addresses
0.0.0.0/0 represents all IPv4 addresses.
::/0 represents all IPv6 addresses.
- Single IP address: IP address/mask
- Security group: The source is from another security group. You can select a security group in the same region from the drop-down list. If there is instance A in security group A and instance B in security group B, and the inbound rule of security group A allows traffic from security group B, traffic is allowed from instance B to instance A.
- IP address group: The source is from an IP address group. An IP address group is a set of one or more IP addresses. You can select an available IP address group from the drop-down list. For IP address ranges and IP addresses with the same security requirements, you can use an IP address group to simplify management.
If no IP address groups are available, create one by referring to Creating an IP Address Group.
IP address:
192.168.52.0/24,10.0.0.0/24
Description
(Optional) Supplementary information about the security group rule.
The security group rule description can contain a maximum of 255 characters and cannot contain angle brackets (< or >).
N/A
- Configure outbound rule parameters as prompted. You can add multiple outbound rules one by one.
Figure 2 Add Outbound Rule
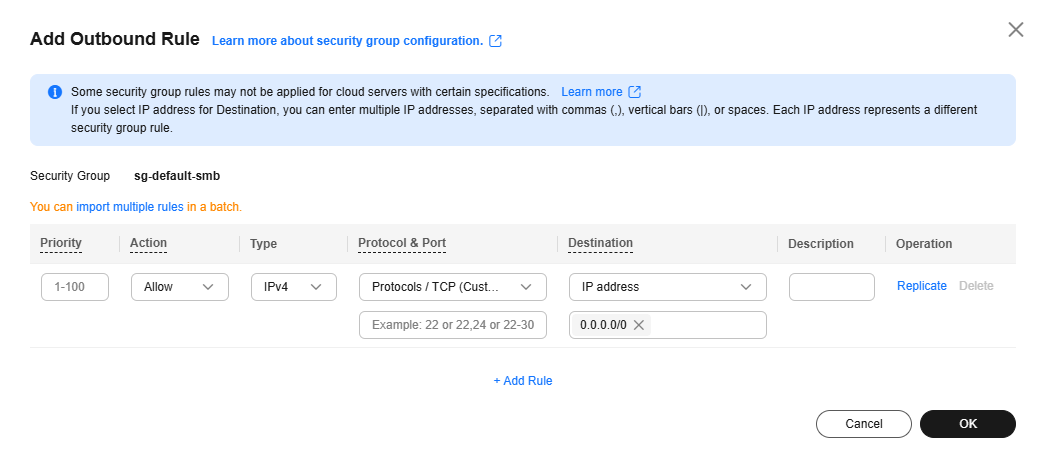
Table 3 Outbound rule parameter description Parameter
Description
Example Value
Priority
The security group rule priority.
The priority value ranges from 1 to 100. The default value is 1 and has the highest priority. The security group rule with a smaller value has a higher priority.
1
Action
The value can be Allow or Deny.- If the Action is set to Allow, access from ECSs in the security group is allowed to the destination over specified ports.
- If the Action is set to Deny, access from ECSs in the security group is denied to the destination over specified ports.
Security group rules are matched by priority and then by action. Deny rules take precedence over allow rules. For more information, see How Traffic Matches Security Group Rules.
Allow
Type
Destination IP address version. You can select:- IPv4
- IPv6
IPv4
Protocol & Port
The network protocol used to match traffic in a security group rule. The protocol can be All, TCP, UDP, GRE, or ICMP.
TCP
Destination port used to match traffic in a security group rule. The value can be from 1 to 65535.
Outbound rules control outgoing traffic over specific ports from instances in the security group.
Enter ports in any of the following formats:- Individual port: Enter a port, such as 22.
- Consecutive ports: Enter a port range, such as 22-30.
- Non-consecutive ports: Enter ports and port ranges, such as 22,23-30. You can enter a maximum of 20 ports and port ranges. Each port range must be unique.
- All ports: Leave it empty or enter 1-65535.
22, 22-30
Destination
Used to match the destination of an internal request. The destination can be:- IP address: The destination is a fixed IP address. You can enter or paste multiple IP addresses separated by commas (,). Each IP address represents a different security group rule.
- Single IP address: IP address/mask
Example IPv4 address: 192.168.10.10/32
Example IPv6 address: 2002:50::44/128
- IP address range in CIDR notation: IP address/mask
Example IPv4 address range: 192.168.52.0/24
Example IPv6 address range: 2407:c080:802:469::/64
- Any IP addresses
0.0.0.0/0 represents all IPv4 addresses.
::/0 represents all IPv6 addresses.
- Single IP address: IP address/mask
- Security group: The destination is another security group. You can select a security group in the same region under the current account from the drop-down list. If there is instance A in security group A and instance B in security group B, and the outbound rule of security group A allows traffic to security group B, traffic is allowed from instance A to instance B.
- IP address group: The destination is in an IP address group. An IP address group is a set of one or more IP addresses. You can select an available IP address group from the drop-down list. For IP address ranges and IP addresses with the same security requirements, you can use an IP address group to simplify management.
If no IP address groups are available, create one by referring to Creating an IP Address Group.
IP address:
192.168.52.0/24,10.0.0.0/24
Description
(Optional) Supplementary information about the security group rule.
The security group rule description can contain a maximum of 255 characters and cannot contain angle brackets (< or >).
N/A
- Click OK to complete the security rule configuration.
Accessing the Security Group Page
- Go to the ECS list.
- Click
 in the upper left corner and select a region and project.
in the upper left corner and select a region and project. - Locate the row that contains the target ECS and choose More > Manage Network > Configure Security Group Rule in the Operation column.
- In the displayed dialog box, click Manage Rule in the Operation column.
Configuring Security Group Rules
Configure security group rules based on service requirements.
- On the Inbound Rules tab, click Add Rule.
The Add Inbound Rule dialog box is displayed.
- Configure inbound rule parameters as prompted. You can add multiple inbound rules one by one.
Figure 3 Add Inbound Rule
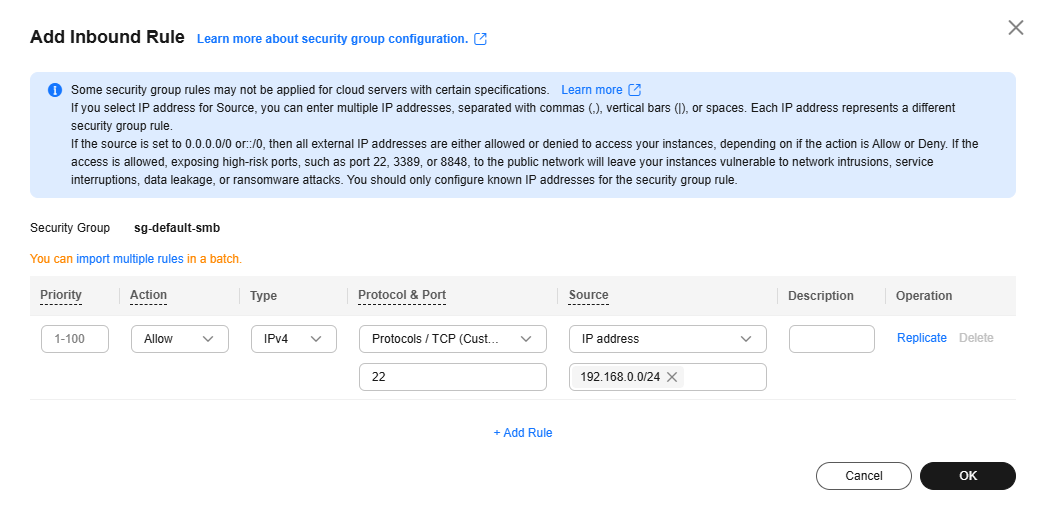
Table 4 Inbound rule parameter description Parameter
Description
Example Value
Priority
The security group rule priority.
The priority value ranges from 1 to 100. The default value is 1 and has the highest priority. The security group rule with a smaller value has a higher priority.
1
Action
The value can be Allow or Deny.- If the Action is set to Allow, traffic is allowed to access the cloud servers in the security group over specified ports.
- If the Action is set to Deny, traffic is denied to access the cloud servers in the security group over specified ports.
Security group rules are matched by priority and then by action. Deny rules take precedence over allow rules. For more information, see How Traffic Matches Security Group Rules.
Allow
Type
Source IP address version. You can select:- IPv4
- IPv6
IPv4
Protocol & Port
The network protocol used to match traffic in a security group rule. The protocol can be All, TCP, UDP, GRE, or ICMP.
TCP
Destination port used to match traffic in a security group rule. The value can be from 1 to 65535.
Inbound rules control incoming traffic over specific ports to instances in the security group.
Enter ports in any of the following formats:- Individual port: Enter a port, such as 22.
- Consecutive ports: Enter a port range, such as 22-30.
- Non-consecutive ports: Enter ports and port ranges, such as 22,23-30. You can enter a maximum of 20 ports and port ranges. Each port range must be unique.
- All ports: Leave it empty or enter 1-65535.
22, 22-30
Source
Used to match the source of an external request. The source can be:- IP address: The source is a fixed IP address. You can enter or paste multiple IP addresses separated by commas (,). Each IP address represents a different security group rule.
- Single IP address: IP address/mask
Example IPv4 address: 192.168.10.10/32
Example IPv6 address: 2002:50::44/128
- IP address range in CIDR notation: IP address/mask
Example IPv4 address range: 192.168.52.0/24
Example IPv6 address range: 2407:c080:802:469::/64
- Any IP addresses
0.0.0.0/0 represents all IPv4 addresses.
::/0 represents all IPv6 addresses.
- Single IP address: IP address/mask
- Security group: The source is from another security group. You can select a security group in the same region from the drop-down list. If there is instance A in security group A and instance B in security group B, and the inbound rule of security group A allows traffic from security group B, traffic is allowed from instance B to instance A.
- IP address group: The source is from an IP address group. An IP address group is a set of one or more IP addresses. You can select an available IP address group from the drop-down list. For IP address ranges and IP addresses with the same security requirements, you can use an IP address group to simplify management.
If no IP address groups are available, create one by referring to Creating an IP Address Group.
IP address:
192.168.52.0/24,10.0.0.0/24
Description
(Optional) Supplementary information about the security group rule.
The security group rule description can contain a maximum of 255 characters and cannot contain angle brackets (< or >).
N/A
- Click OK.
The inbound rule list is displayed.
- On the Outbound Rules tab, click Add Rule.
The Add Outbound Rule dialog box is displayed.
- Configure outbound rule parameters as prompted. You can add multiple outbound rules one by one.
Figure 4 Add Outbound Rule
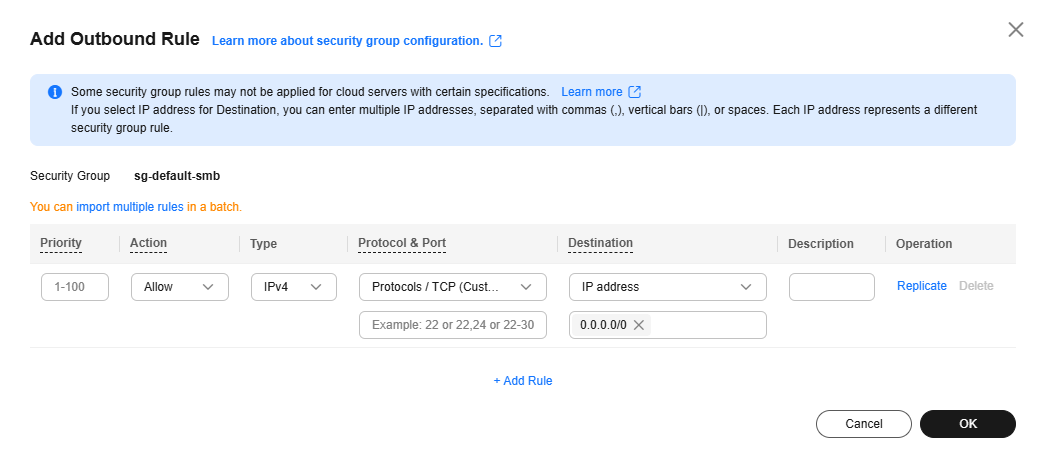
Table 5 Outbound rule parameter description Parameter
Description
Example Value
Priority
The security group rule priority.
The priority value ranges from 1 to 100. The default value is 1 and has the highest priority. The security group rule with a smaller value has a higher priority.
1
Action
The value can be Allow or Deny.- If the Action is set to Allow, access from ECSs in the security group is allowed to the destination over specified ports.
- If the Action is set to Deny, access from ECSs in the security group is denied to the destination over specified ports.
Security group rules are matched by priority and then by action. Deny rules take precedence over allow rules. For more information, see How Traffic Matches Security Group Rules.
Allow
Type
Destination IP address version. You can select:- IPv4
- IPv6
IPv4
Protocol & Port
The network protocol used to match traffic in a security group rule. The protocol can be All, TCP, UDP, GRE, or ICMP.
TCP
Destination port used to match traffic in a security group rule. The value can be from 1 to 65535.
Outbound rules control outgoing traffic over specific ports from instances in the security group.
Enter ports in any of the following formats:- Individual port: Enter a port, such as 22.
- Consecutive ports: Enter a port range, such as 22-30.
- Non-consecutive ports: Enter ports and port ranges, such as 22,23-30. You can enter a maximum of 20 ports and port ranges. Each port range must be unique.
- All ports: Leave it empty or enter 1-65535.
22, 22-30
Destination
Used to match the destination of an internal request. The destination can be:- IP address: The destination is a fixed IP address. You can enter or paste multiple IP addresses separated by commas (,). Each IP address represents a different security group rule.
- Single IP address: IP address/mask
Example IPv4 address: 192.168.10.10/32
Example IPv6 address: 2002:50::44/128
- IP address range in CIDR notation: IP address/mask
Example IPv4 address range: 192.168.52.0/24
Example IPv6 address range: 2407:c080:802:469::/64
- Any IP addresses
0.0.0.0/0 represents all IPv4 addresses.
::/0 represents all IPv6 addresses.
- Single IP address: IP address/mask
- Security group: The destination is another security group. You can select a security group in the same region under the current account from the drop-down list. If there is instance A in security group A and instance B in security group B, and the outbound rule of security group A allows traffic to security group B, traffic is allowed from instance A to instance B.
- IP address group: The destination is in an IP address group. An IP address group is a set of one or more IP addresses. You can select an available IP address group from the drop-down list. For IP address ranges and IP addresses with the same security requirements, you can use an IP address group to simplify management.
If no IP address groups are available, create one by referring to Creating an IP Address Group.
IP address:
192.168.52.0/24,10.0.0.0/24
Description
(Optional) Supplementary information about the security group rule.
The security group rule description can contain a maximum of 255 characters and cannot contain angle brackets (< or >).
N/A
- Click OK.
The outbound rule list is displayed and you can view the rules you added.
- Click the Inbound Rules tab.
The security group rule list is displayed.
- Locate the target rule and click Modify in the Operation column.
- Modify the security group rules as needed.
Table 6 Inbound rule parameter description Parameter
Description
Example Value
Priority
The security group rule priority.
The priority value ranges from 1 to 100. The default value is 1 and has the highest priority. The security group rule with a smaller value has a higher priority.
1
Action
The value can be Allow or Deny.- If the Action is set to Allow, traffic is allowed to access the cloud servers in the security group over specified ports.
- If the Action is set to Deny, traffic is denied to access the cloud servers in the security group over specified ports.
Security group rules are matched by priority and then by action. Deny rules take precedence over allow rules. For more information, see How Traffic Matches Security Group Rules.
Allow
Type
Source IP address version. You can select:- IPv4
- IPv6
IPv4
Protocol & Port
The network protocol used to match traffic in a security group rule. The protocol can be All, TCP, UDP, GRE, or ICMP.
TCP
Destination port used to match traffic in a security group rule. The value can be from 1 to 65535.
Inbound rules control incoming traffic over specific ports to instances in the security group.
Enter ports in any of the following formats:- Individual port: Enter a port, such as 22.
- Consecutive ports: Enter a port range, such as 22-30.
- Non-consecutive ports: Enter ports and port ranges, such as 22,23-30. You can enter a maximum of 20 ports and port ranges. Each port range must be unique.
- All ports: Leave it empty or enter 1-65535.
22, 22-30
Source
Used to match the source of an external request. The source can be:- IP address: The source is a fixed IP address. You can enter or paste multiple IP addresses separated by commas (,). Each IP address represents a different security group rule.
- Single IP address: IP address/mask
Example IPv4 address: 192.168.10.10/32
Example IPv6 address: 2002:50::44/128
- IP address range in CIDR notation: IP address/mask
Example IPv4 address range: 192.168.52.0/24
Example IPv6 address range: 2407:c080:802:469::/64
- Any IP addresses
0.0.0.0/0 represents all IPv4 addresses.
::/0 represents all IPv6 addresses.
- Single IP address: IP address/mask
- Security group: The source is from another security group. You can select a security group in the same region from the drop-down list. If there is instance A in security group A and instance B in security group B, and the inbound rule of security group A allows traffic from security group B, traffic is allowed from instance B to instance A.
- IP address group: The source is from an IP address group. An IP address group is a set of one or more IP addresses. You can select an available IP address group from the drop-down list. For IP address ranges and IP addresses with the same security requirements, you can use an IP address group to simplify management.
If no IP address groups are available, create one by referring to Creating an IP Address Group.
IP address:
192.168.52.0/24,10.0.0.0/24
Description
(Optional) Supplementary information about the security group rule.
The security group rule description can contain a maximum of 255 characters and cannot contain angle brackets (< or >).
N/A
- Click Confirm.
- Click the Outbound Rules tab.
The security group rule list is displayed.
- Locate the target rule and click Modify in the Operation column.
- Modify the security group rules as needed.
Table 7 Outbound rule parameter description Parameter
Description
Example Value
Priority
The security group rule priority.
The priority value ranges from 1 to 100. The default value is 1 and has the highest priority. The security group rule with a smaller value has a higher priority.
1
Action
The value can be Allow or Deny.- If the Action is set to Allow, access from ECSs in the security group is allowed to the destination over specified ports.
- If the Action is set to Deny, access from ECSs in the security group is denied to the destination over specified ports.
Security group rules are matched by priority and then by action. Deny rules take precedence over allow rules. For more information, see How Traffic Matches Security Group Rules.
Allow
Type
Destination IP address version. You can select:- IPv4
- IPv6
IPv4
Protocol & Port
The network protocol used to match traffic in a security group rule. The protocol can be All, TCP, UDP, GRE, or ICMP.
TCP
Destination port used to match traffic in a security group rule. The value can be from 1 to 65535.
Outbound rules control outgoing traffic over specific ports from instances in the security group.
Enter ports in any of the following formats:- Individual port: Enter a port, such as 22.
- Consecutive ports: Enter a port range, such as 22-30.
- Non-consecutive ports: Enter ports and port ranges, such as 22,23-30. You can enter a maximum of 20 ports and port ranges. Each port range must be unique.
- All ports: Leave it empty or enter 1-65535.
22, 22-30
Destination
Used to match the destination of an internal request. The destination can be:- IP address: The destination is a fixed IP address. You can enter or paste multiple IP addresses separated by commas (,). Each IP address represents a different security group rule.
- Single IP address: IP address/mask
Example IPv4 address: 192.168.10.10/32
Example IPv6 address: 2002:50::44/128
- IP address range in CIDR notation: IP address/mask
Example IPv4 address range: 192.168.52.0/24
Example IPv6 address range: 2407:c080:802:469::/64
- Any IP addresses
0.0.0.0/0 represents all IPv4 addresses.
::/0 represents all IPv6 addresses.
- Single IP address: IP address/mask
- Security group: The destination is another security group. You can select a security group in the same region under the current account from the drop-down list. If there is instance A in security group A and instance B in security group B, and the outbound rule of security group A allows traffic to security group B, traffic is allowed from instance A to instance B.
- IP address group: The destination is in an IP address group. An IP address group is a set of one or more IP addresses. You can select an available IP address group from the drop-down list. For IP address ranges and IP addresses with the same security requirements, you can use an IP address group to simplify management.
If no IP address groups are available, create one by referring to Creating an IP Address Group.
IP address:
192.168.52.0/24,10.0.0.0/24
Description
(Optional) Supplementary information about the security group rule.
The security group rule description can contain a maximum of 255 characters and cannot contain angle brackets (< or >).
N/A
- Click Confirm.
Checking Whether a Port Is Enabled on an ECS
After allowing traffic over a port in a security group rule, you need to ensure that the port used by the instance is also opened.
- Log in to the ECS and check whether the ECS port is enabled.
- Checking a Linux ECS port
Run the following command to check whether TCP port 80 is being listened on:
netstat -an | grep 80
If the following figure is displayed, TCP port 80 is enabled.
Figure 5 Command output for the Linux ECS
- Checking a Windows ECS port
- Checking a Linux ECS port
- Enter http://ECS EIP in the address box of the browser and press Enter.
If the requested page can be accessed, the security group rule has taken effect.
Helpful Links
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot






