Applying for Permissions and Approving Permissions (Some Advanced Features)
During access permission management, you can grant permissions to users through permission sets or roles, or apply for permissions and approve permission applications.
This section describes how to configure a review policy, how an applicant applies for permissions (Applying for Permissions), and how a reviewer reviews permission requests (Reviewing Permission Requests), configure and subscribe to permission review notifications, and revokes permissions (Revoking Permissions).

If you are using the new version mode, you can configure review policies, apply for field permissions, configure permission validity periods, and configure and subscribe to permission review notifications only when you use the enterprise edition. If you are using the old version mode, you can perform these operations in the basic version or an advanced version.
Prerequisites
- Before applying for permissions, you have configured a workspace permission set. For details, see Configuring Workspace Permission Sets.
- Before applying for permissions, you have collected the metadata of the data connection in DataArts Catalog. For details, see Metadata Collection Task.
Notes and Constraints
- For configuring review policies:
- Only one review policy is allowed for a security level. If no security level is selected, only one review policy is allowed.
- To create a security level-based review policy, ensure that the following conditions are met:
- Data Map is enabled.
- Metadata has been collected from the data of a specific security level.
- A sensitive data discovery task has been executed, and the security level information has been synchronized to Data Map.
- For applying for permissions and reviewing permission requests:
- You can only apply for the SELECT permission for querying data in tables. Before applying for the permission, ensure that the SELECT permission for all columns in the target table has been configured in the workspace permission set.

If you are using the new version mode, you can configure review policies, apply for field permissions, configure permission validity periods, and configure and subscribe to permission review notifications only when you use the enterprise edition. If you are using the old version mode, you can perform these operations in the basic version or an advanced version.
- If you apply for the permission of multiple tables at a time, multiple requests are generated.
- You can apply for DLI permissions for users but not for user groups.
- Only the DAYU Administrator, Tenant Administrator, data security administrator, and workspace administrator can revoke permissions from other users.
- You can only view your permission requests and review records, and cannot audit permissions.
- You can only apply for the SELECT permission for querying data in tables. Before applying for the permission, ensure that the SELECT permission for all columns in the target table has been configured in the workspace permission set.
- For configuring and subscribing to permission review notifications:
- Only the DAYU Administrator, Tenant Administrator, and data security administrator can configure permission review notifications and operate all subscriptions. Non-administrator users can operate their subscriptions, but cannot view or operate other users' subscriptions.
- To configure permission review notifications, you must grant the SMN FullAccess permission of the SMN service to the dlg_agency.
-
If a notification topic in DataArts Factory is used for review notifications, no notifications will be received because the subscriptions added in DataArts Factory have filtering policies. In this case, you must associate notifications with subscriptions apart from subscribing to notifications so that permission review notifications can be received.
- Subscriptions are associated with users through remarks. Subscriptions whose remarks are usernames are regarded as subscriptions of the corresponding users.
- The subscription list is associated a topic. If the topic is changed, you must reconfigure notifications.
- The configured endpoint information cannot be edited. If the phone number or email address changes, delete the endpoint, add it again, and request a subscription again.
- SMN can send a maximum of 100 messages to a specific phone number or email address within 10 minutes.
- A permission review notification contains the number of service tickets to be reviewed at the time when the notification is sent. During the notification cooldown period, no notification is sent even if a new service ticket is received. When the cooldown period ends, notifications are sent again for new service tickets.
- Due to concurrency and SMN performance limitations, SMN notifications may be delayed for a few minutes.
- For making permissions take effect:
- During permission synchronization, you need to configure required permissions for the dlg_agency. For details, see Authorizing dlg_agency.
- The current data permission control uses the allowlist mechanism, which adds operation conditions to the users to be authorized without affecting the permissions the users already have. If you only want to make the permissions granted by the data permission control take effect, you need to revoke the original permissions of the users to be authorized. For details, see Data Permission Management.
- During script execution and job testing in DataArts Factory, the MRS or DWS data source uses the account of the data connection for authentication by default. Therefore, permission management still does not take effect during data development. You need to enable fine-grained authentication so that the current user is used for authentication during script execution and job testing in DataArts Factory. In this way, different users have different data permissions, and permission management for roles and permission sets takes effect.
Configuring a Review Policy
Through review policies, you can set multi-level review processes or set different review processes for data of different security levels.
Note that review policies configured for a DataArts Studio instance are visible to and take effect for all the workspaces of the instance.
- On the DataArts Studio console, locate a workspace and click DataArts Security.
- In the navigation pane on the left, choose Access Permission Management > .
- On the displayed page, click the Review Policies tab and then Create. Figure 1 Creating a review policy

- In the slide-out panel, set parameters based on Table 1. You can click
 to add review nodes. Figure 2 Configuring the review policy
to add review nodes. Figure 2 Configuring the review policy
Table 1 Review policy parameters Configuration Item
Description
Basic Information
*Policy Name
Name of the review policy. It can contain a maximum of 32 characters, including letters, digits, and underscores (_).
Policy Description
Description of the policy. It can contain a maximum of 255 characters.
Data Security Level
If you want to set different review processes for the permission requests for data of different security levels, select a data security level. Only one review policy is allowed for a security level. If no security level is selected, only one review policy is allowed.
The prerequisites for selecting a data security level are as follows:
- Data Map is enabled.
- Metadata has been collected from the data of a specific security level.
- A sensitive data discovery task has been executed, and the security level information has been synchronized to Data Map.
Review Node Settings-System Role/IAM User/IAM User Group
Reviewer Type
Type of the reviewer
Role
Reviewer role matching the reviewer type
Scenario
This parameter can be configured for all nodes except the first node. The application needs to be reviewed by the reviewer configured for the node only when the conditions in this scenario are met.
- After setting the review policy, click Submit. The created review policy is disabled by default. To make it take effect, click
 in the Status column. Figure 3 Review policy list
in the Status column. Figure 3 Review policy list
Applying for Permissions
- On the DataArts Studio console, locate a workspace and click DataArts Security.
- In the navigation pane on the left, choose Access Permission Management > .
- On the Data permission request page, click Create to create a service ticket for applying for permissions. Figure 4 Creating a permission request

- On the displayed Data permission request page, fill in the service ticket by referring to Table 2. Figure 5 Filling in a service ticket

- After filling in the service ticket, click Submit to generate a service ticket to be reviewed. In the service ticket list, you can view the service ticket ID, summary, and status. You can click the service ticket ID to view the ticket details. You can also withdraw service tickets that have not been approved. Figure 6 Service ticket list

Reviewing Permission Requests
- On the DataArts Studio console, locate a workspace and click DataArts Security.
- In the navigation pane on the left, choose Access Permission Management > .
- Click the Permission Review tab. Figure 7 Permission Review

- The Permission Review page displays the service tickets to be reviewed. You can view the service ticket ID, summary, and status, and click the service ticket ID to view the ticket details. Review the service ticket based on service rationality and data security, and click Approve or Reject. You can also select service tickets and click Batch Review above the list to approve or reject service tickets in batches.
- Click the Reviewed tab to view the service tickets that have been approved. Figure 8 List of approved service tickets

Revoking Permissions
- On the DataArts Studio console, locate a workspace and click DataArts Security.
- In the navigation pane on the left, choose Access Permission Management > .
- Click the Revoking permissions tab. Figure 9 Revoking permissions

- The Revoking permissions page displays the data permissions you have obtained. You can filter permissions by Workspace, Member Name, Database Name, or Table Name (fuzzy match is supported). Locate a permission and click Reclaim in the Operation column to delete the permission. Only the DAYU Administrator, Tenant Administrator, workspace administrator and data security administrator can revoke data permissions of users in the corresponding workspace.

Change Validity Period is available only when you are using the enterprise version in the new version mode (or the basic version or an advanced version in the old version mode).
Figure 10 Revoking permissions
Configuring and Subscribing to Permission Review Notifications
The administrator can configure topics for permission review notifications. Reviewers who subscribe to the topics will receive notifications after permission requests are received.
- On the DataArts Studio console, locate a workspace and click DataArts Security.
- In the navigation pane on the left, choose Access Permission Management > Permission Review. On the Permission Review page, click the Permission Notifications tab.
- On the Permission Notifications page, click the Permission Approval Notifications tab and
 , select an SMN topic for permission review notifications, and click
, select an SMN topic for permission review notifications, and click  . Figure 11 Permission Notifications page
. Figure 11 Permission Notifications page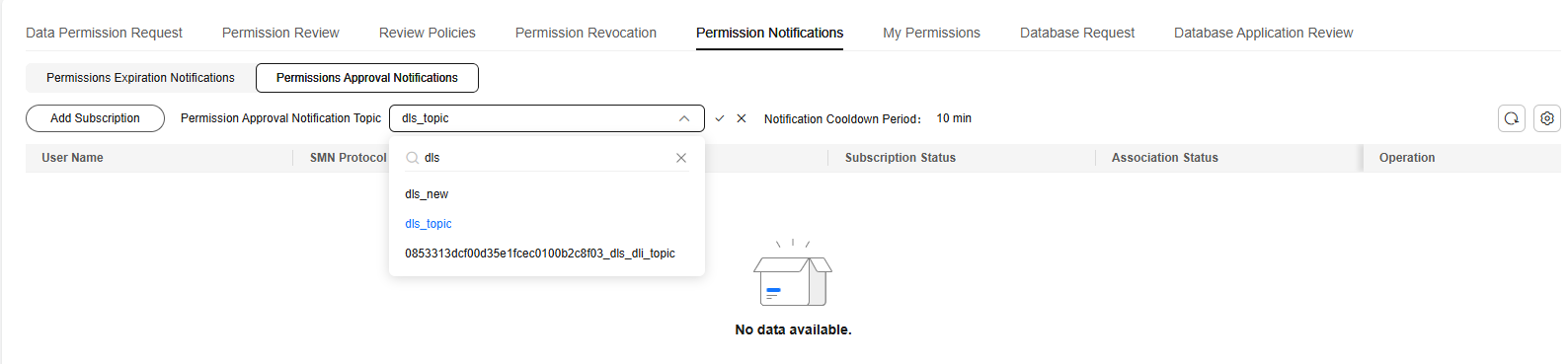
- The endpoints that have subscribed to the SMN topic are displayed in the subscription list. The usernames in the list correspond to subscription remarks. Subscribers can only perform operations on subscriptions whose remarks are the same as usernames. If there is no subscription corresponding to the current username, click Add Subscription to add a subscription. A subscriber can select an endpoint and send a subscription request. When the subscription status is Confirmed, the subscription is successful.

If a notification topic in DataArts Factory is used for review notifications, no notifications will be received because the subscriptions added in DataArts Factory have filtering policies. In this case, you must associate notifications with subscriptions apart from subscribing to notifications so that permission review notifications can be received.
Figure 12 Subscribing to permission review notifications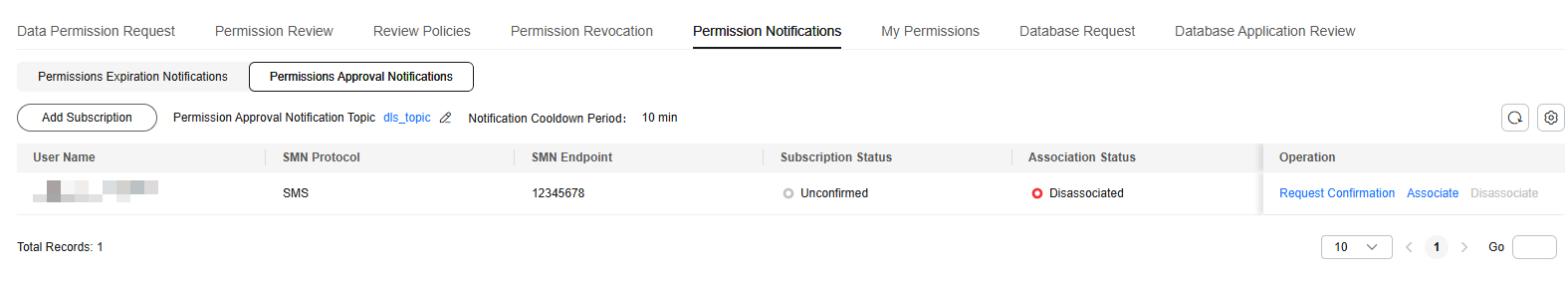
Related Operations
- Editing a review policy: On the Review Policies page, locate a policy and click Edit in the Operation column.
- Setting the review policy status: A new review policy is disabled by default and does not take effect.
To change the status of a review policy, click
 or
or  to enable or disable the policy.
to enable or disable the policy. - Deleting review policies: On the Review Policies page, locate a policy and click Delete in the Operation column. To delete multiple policies, select them and click Delete above the policy list.

The deletion operation cannot be undone. Exercise caution when performing this operation.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





