Configuring Security Group Rules
Scenarios
Similar to firewall, a security group is used to control network access. You can define access rules for a security group to protect the FlexusX instances in the group.
- Inbound rules allow or deny incoming network traffic to FlexusX instances in the security group.
- Outbound rules allow or deny outgoing network traffic from FlexusX instances in the security group.
Procedure
- Log in to the FlexusX console, in the upper left corner, click
 , and select a region and project.
, and select a region and project. - On the FlexusX Instances page, locate the target FlexusX instance and click its name.
The details page of this instance is displayed.
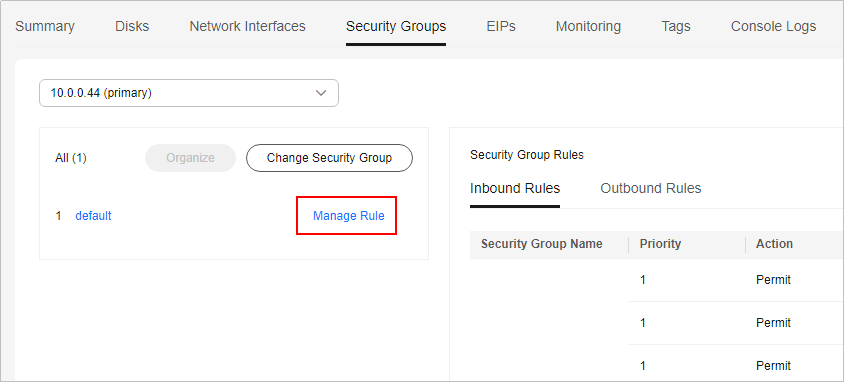
- On the detailed page, click the Security Groups tab and view security group rules.
- Click Manage Rule.
The page for configuring security group rules is displayed.
- On the Inbound Rules tab, click Add Rule.
The Add Inbound Rule dialog box is displayed.
- Configure required parameters.
You can click + to add more inbound rules. For details about the parameters, see Adding a Security Group Rule.
Figure 1 Adding an inbound rule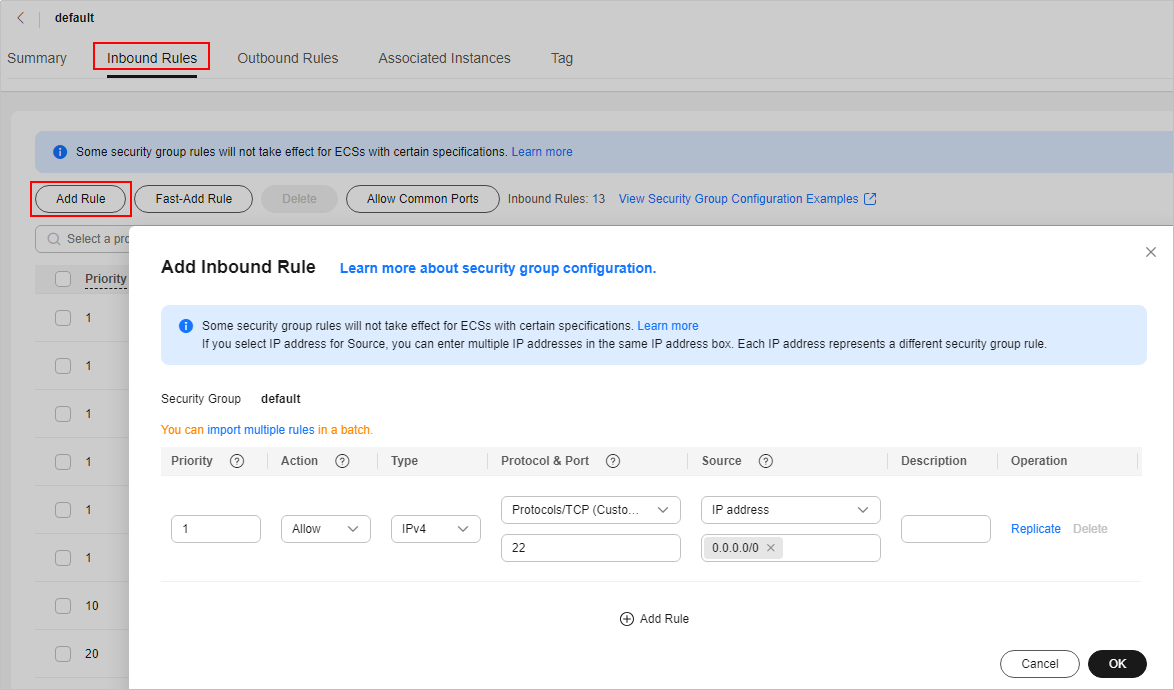
- On the Outbound Rules tab, click Add Rule.
The Add Outbound Rule dialog box is displayed.
- Configure required parameters.
You can click + to add more outbound rules. For details about the parameters, see Adding a Security Group Rule.
- Click OK.
Verifying Security Group Rules
After adding inbound and outbound rules, you can verify whether the rules have been applied. Assume that you have deployed a website on a FlexusX instance. To enable users to access your website through HTTP (80), you need to add an inbound rule to the security group of the FlexusX instance to allow access over this port. Table 1 shows the rule details.
Linux
If the instance runs Linux, perform the following operations to verify whether the security group rule has been applied:
- Log in to the FlexusX instance.
- Check whether TCP port 80 is listened on:
If command output shown in Figure 2 is displayed, TCP port 80 is listened on.
- Enter http://EIP bound to the FlexusX instance in the address box of the browser and press Enter.
If the requested page can be accessed, the security group rule has taken effect.
Impacts of Deleting Common Security Group Rules
On the Inbound Rules and Outbound Rules tabs, you can also modify, replicate, or delete existing rules.
Deleting security group rules will disable some functions.
- If you delete a rule with Protocol & Port specified as TCP: 20-21, you will not be able to upload files to or download files from servers using FTP.
- If you delete a rule with Protocol & Port specified as ICMP: All, you will not be able to ping the servers.
- If you delete a rule with Protocol & Port specified as TCP: 443, you will not be able to connect to websites on the servers using HTTPS.
- If you delete a rule with Protocol & Port specified as TCP: 80, you will not be able to connect to websites on servers using HTTP.
- If you delete a rule with Protocol & Port specified as TCP: 22, you will not be able to remotely connect to Linux server using SSH.
- If you delete a rule with Protocol & Port specified as TCP: 3389, you will not be able to remotely connect to Windows server using RDP.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot






