Connecting to an Instance Using Jedis
This section describes how to access a GeminiDB Redis instance using the Java client, Jedis.
The proxy cluster architecture of GeminiDB Redis API provides a unified load balancing address and high availability. So, JedisPool is recommended for easy access.
JedisSentinelPool and JedisCluster can also be used to connect to GeminiDB Redis instances.
Prerequisites
- A GeminiDB Redis instance has been created and is running properly. For details about how to create a GeminiDB Redis instance, see Buying a GeminiDB Redis Cluster Instance.
- An ECS is available. For details, see Purchasing an ECS.
- GNU Compiler Collection (GCC) has been installed on the ECS.
- The created ECS is in the same region, AZ, VPC, and security group as the GeminiDB Redis instance.
Dependencies on the POM File
<dependency>
<groupId>redis.clients</groupId>
<artifactId>jedis</artifactId>
<version>4.3.2</version>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-data-redis</artifactId>
<version>2.3.6.RELEASE</version>
</dependency>
Example code:
import org.apache.commons.pool2.impl.GenericObjectPoolConfig;
import redis.clients.jedis.Jedis;
import redis.clients.jedis.JedisPool;
public class JedisPoolTests {
private static void testPool() {
// There will be security risks if the username and password used for authentication are directly written into code. Store the username and password in ciphertext in the configuration file or environment variables.
// In this example, the username and password are stored in the environment variables. Before running this example, set environment variables EXAMPLE_USERNAME_ENV and EXAMPLE_PASSWORD_ENV as needed.
String pwd = System.getenv("EXAMPLE_PASSWORD_ENV");
JedisPool pool = new JedisPool(new GenericObjectPoolConfig(), "172.xx.xx.xx", 6379,
2000, pwd);
Jedis jedis = pool.getResource();
try {
System.out.println(jedis.hgetAll("676296"));
System.out.println(jedis.set("key1", "value1"));
} finally {
jedis.close();
}
pool.destroy();
}
public static void main(String[] args) {
testPool();
}
}
- In the preceding code, 172.xx.xx.xx indicates the load balancer IP address of the GeminiDB Redis instance that you want to connect to.
You can click the instance name to go to the Basic Information page and obtain the load balancer IP address in the Network Information area.
Figure 1 Viewing the load balancer IP address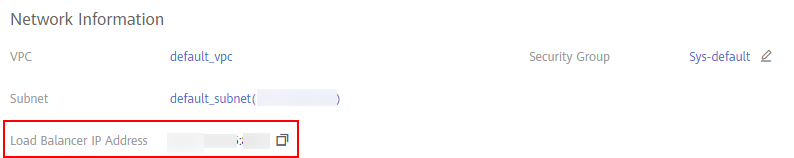
- 6379 in the preceding code is the port of the instance to be connected. Replace it with the actual port number. For details about how to obtain the port number, see Viewing the IP Address and Port Number of a GeminiDB Redis Instance.
- For details about the supported and restricted commands, see Development and O&M Rules.
- Redis Cluster and GeminiDB Redis API use different hash algorithms. Adding hashtags to keys in some commands of GeminiDB Redis API can avoid unexpected exceptions. For details about how to use hashtags, see Development and O&M Rules.
Example code:
import org.apache.commons.pool2.impl.GenericObjectPoolConfig;
import redis.clients.jedis.HostAndPort;
import redis.clients.jedis.JedisCluster;
public class ClusterTests {
private static void testCluster() {
String pwd = "a";
JedisCluster cluster = new JedisCluster(new HostAndPort("172.xx.xx.xx", 6379),
200, 2000, 5, pwd, new GenericObjectPoolConfig());
System.out.println(cluster.hgetAll("676296"));
System.out.println(cluster.set("key1", "value1"));
}
public static void main(String[] args) {
testCluster();
}
}
- In the preceding code, 172.xx.xx.xx indicates the load balancer IP address of the GeminiDB Redis instance that you want to connect to.
You can click the instance name to go to the Basic Information page and obtain the load balancer IP address in the Network Information area.
Figure 2 Viewing the load balancer IP address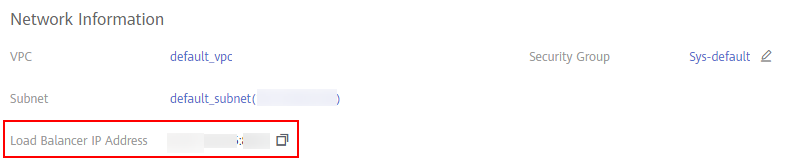
- 6379 in the preceding code is the port of the instance to be connected. Replace it with the actual port number. For details about how to obtain the port number, see Viewing the IP Address and Port Number of a GeminiDB Redis Instance.
- For details about the supported and restricted commands, see Development and O&M Rules.
- Redis Cluster and GeminiDB Redis API use different hash algorithms. Adding hashtags to keys in some commands of GeminiDB Redis API can avoid unexpected exceptions. For details about how to use hashtags, see Development and O&M Rules.
Example code:
import org.apache.commons.pool2.impl.GenericObjectPoolConfig;
import redis.clients.jedis.Jedis;
import redis.clients.jedis.JedisSentinelPool;
import java.util.HashSet;
import java.util.Set;
public void SentinelTest {
public static void main(String[] args) {
GenericObjectPoolConfig<Jedis> config = new GenericObjectPoolConfig<Jedis>();
Set<String> mySentinels = new HashSet<String>();
mySentinels.add("172.xx.xx.xx:6379");
JedisSentinelPool pool = new JedisSentinelPool(master-name, mySentinels, config, 1000, password, 0);
Jedis jedis = pool.getResource();
jedis.auth(password);
jedis.set("foo", "bar");
String s = jedis.get("foo");
System.out.println(s);
jedis.close();
pool.close();
}
}
- In the preceding code, 172.xx.xx.xx indicates the load balancer IP address of the GeminiDB Redis instance that you want to connect to.
You can click the instance name to go to the Basic Information page and obtain the load balancer IP address in the Network Information area.
Figure 3 Viewing the load balancer IP address
- 6379 in the preceding code is the port of the instance to be connected. Replace it with the actual port number. For details about how to obtain the port number, see Viewing the IP Address and Port Number of a GeminiDB Redis Instance.
- In the preceding code, master-name can only be set to mymaster.
- For details about the supported and restricted commands, see Development and O&M Rules.
- Redis Cluster and GeminiDB Redis API use different hash algorithms. Adding hashtags to keys in some commands of GeminiDB Redis API can avoid unexpected exceptions. For details about how to use hashtags, see Development and O&M Rules.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





