Configuring Security Group Rules
Scenarios
A security group is a collection of access control rules for ECSs and RDS DB instances that have the same security protection requirements and are mutually trusted within a VPC.
Before you can connect to your DB instance, you need to create security group rules to enable specific IP addresses and ports to access your RDS instance.
First check whether the ECS and RDS DB instance are in the same security group.
- If they are in the same security group, they can communicate with each other by default. No security group rule needs to be configured. Go to Buying a DB Instance and Connecting to It Using the mysql Client.
- If they are in different security groups, configure security group rules for them, separately.
- RDS DB instance: Configure an inbound rule for the security group with which the RDS DB instance is associated.
- ECS: The default security group rule allows all outgoing data packets. In this case, you do not need to configure a security group rule for the ECS. If not all outbound traffic is allowed in the security group, you need to configure an outbound rule for the ECS.
This section describes how to configure an inbound rule for an RDS DB instance.
For details about the requirements of security group rules, see the Adding a Security Group Rule section in the Virtual Private Cloud User Guide.
Precautions
The default security group rule allows all outgoing data packets. ECSs and RDS DB instances can access each other if they are in the same security group. After a security group is created, you can configure security group rules to control access from and to the DB instances in the security group.
- By default, you can create a maximum of 100 security groups in your cloud account.
- By default, you can add up to 50 security group rules to a security group.
- One RDS instance can be associated with multiple security groups, and one security group can be associated with multiple RDS instances.
- Too many security group rules will increase the first packet latency. You are advised to create no more than 50 rules for a security group.
- To enable access to an RDS DB instance from resources outside the security group, you need to configure an inbound rule for the security group associated with the RDS DB instance.
To ensure the security of your data and DB instances, you are advised to use the principle of least privilege for database access. Change the default database port 3306, and set the IP address to the remote server's address or the remote server's smallest subnet address to control the access from the remote server.
The default value of Source is 0.0.0.0/0, indicating that RDS DB instances in the security group can be accessed from any IP address.
For details about the requirements of security group rules, see Adding a Security Group Rule in the Virtual Private Cloud User Guide.
Procedure
- Log in to the management console.
- Click
 in the upper left corner and select a region and a project.
in the upper left corner and select a region and a project. - Click
 in the upper left corner of the page and choose Databases > Relational Database Service.
in the upper left corner of the page and choose Databases > Relational Database Service. - On the Instances page, click the DB instance name.
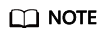
- In the navigation pane, choose Connectivity & Security. In the Security Group Rules area, click the security group name to view the security group rules.
Figure 1 Security group rules
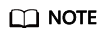
- Click Add Inbound Rule or Allow All IP to configure security group rules.
To add more inbound rules, click
 .
.
Allow All IP allows all IP addresses to access RDS DB instances in the security group, which poses high security risks. Exercise caution when performing this operation.
Figure 2 Adding an inbound rule
Table 1 Inbound rule parameter description Parameter
Description
Example Value
Protocol & Port
Protocol: network protocol. Available options: All ports, Custom TCP, Custom UDP, ICMP, and GRE.
Custom TCP
Port: the port over which the traffic can reach your DB instance.
RDS for MySQL instances can use database ports 1024 to 65535, excluding 12017 and 33071, which are reserved for RDS system use.
3306
Type
IP address type.
- IPv4
- IPv6
IPv4
Source
Source address. It can be a single IP address, an IP address group, or a security group to allow access from them to your DB instance. Examples:
- Single IP address: 192.168.10.10/32 (IPv4); 2002:50::44/128 (IPv6)
- All IP addresses: 0.0.0.0/0 (IPv4); ::/0 (IPv6)
- IP address range: 192.168.1.0/24 (IPv4); 2407:c080:802:469::/64 (IPv6)
- Security group: default_securitygroup
0.0.0.0/0
Description
Supplementary information about the security group rule. This parameter is optional.
The description can contain a maximum of 255 characters and cannot contain angle brackets (<) or (>).
N/A
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





