CREATE DIRECTORY
Description
CREATE DIRECTORY creates a directory. The directory defines an alias for a path in the server file system and is used to store data files used by users. Users can read and write these files through the dbe_file advanced package.
The read and write permissions for the directory can be granted to specified users to provide permission control for dbe_file.
Precautions
- When enable_access_server_directory is set to off, only the initial user is allowed to create the directory object. When enable_access_server_directory is set to on, users with the SYSADMIN permission and users inherited the built-in role permission gs_role_directory_create can create directory objects.
- By default, the user who creates a directory has the read and write permissions on the directory.
- The default owner of a directory is the user who creates the directory.
- A directory cannot be created for the following paths:
- The path contains special characters.
- The path is a relative path.
- The following validity check is performed during directory creation:
- Check whether the path exists in the OS. If it does not exist, a message is displayed, indicating the potential risks.
- Check whether the database initial user omm has the R/W/X permissions for the OS path. If the user does not have all the permissions, a message is displayed, indicating the potential risks.
- Ensure that the path is the same on all the database nodes. Otherwise, the path may fail to be found on some nodes when the directory is used.
- You can view existing directory objects in the pg_directory table.
- The DIRECTORY object cannot be used in a PDB.
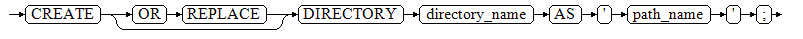
Syntax
CREATE [OR REPLACE] DIRECTORY directory_name AS 'path_name';
Parameters
- directory_name
Specifies the name of a directory.
Value range: a string. It must comply with the naming convention.
- path_name
Specifies the OS path for which a directory is to be created.
Value range: a valid OS path
Examples
-- Create a directory object. gaussdb=#CREATE OR REPLACE DIRECTORY dir AS '/tmp/'; -- View the created directory object. gaussdb=#select * from pg_directory; dirname | owner | dirpath | diracl ---------+-------+---------+-------- dir | 10 | /tmp | (1 row) -- Delete the directory object. gaussdb=#DROP DIRECTORY dir;
Helpful Links
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





