Network Configurations for Different Migration Scenarios
Background
For a server migration, there are two important aspects to consider: data flow directions and network requirements. A migration using SMS involves two types of traffic: control flow and data flow.
- Control flow refers to the communications between the source server and cloud service management planes. To ensure a smooth migration, verify if there are any restrictions on the outbound traffic from the source server. Additionally, confirm that the source server can access the following cloud services via their domain names: SMS, IAM, ECS, EVS, VPC, and IMS.
- Data flow refers to data transmission from the source server to the target server. To ensure smooth data transmission, confirm that the security group of the target server allows traffic from the source server's IP address over the specified migration ports. If the source server cannot directly access the Internet or cannot communicate with the target server, a proxy server must be configured. The proxy server must meet the following requirements:
- The proxy server can correctly forward traffic from the source server.
- The proxy server's security group is configured to allow traffic from the source server's IP address over the proxy port.
For a Scenario Where the Source Server Has Internet Access and Can Communicate with the Target Server over the Internet
- Download and start the SMS-Agent on the source server.
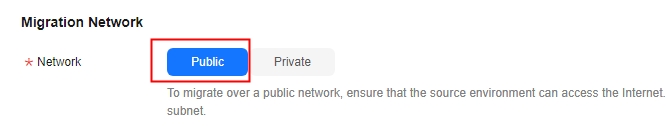
- Configure the target server. Remember to set Network Type to Public.
Ensure that the security group of the target server allows access from the source server's public IP address over the specified migration ports. For details about how to configure security group rules, see How Do I Configure Security Group Rules for Target Servers?
For a Scenario Where the Source Server Has Internet Access and Can Communicate with the Target Server over an Intranet
- Confirm the source and target servers can communicate with each other over the intranet.
- Download and start the SMS-Agent on the source server.
- Configure the target server. Set Network Type to Private during the configuration.
Ensure that the security group of the target server allows access from the source server's private IP address over the specified migration ports. For details about how to configure security group rules, see How Do I Configure Security Group Rules for Target Servers?
For a Scenario Where the Source Server Has No Internet Access and Can Communicate with the Target Server over an Intranet
- Prepare a proxy server that can access the Internet and can communicate with the source server over an intranet. Configure the security group of the proxy server to allow access from the source server's private IP address over the proxy port.
- Install proxy software on the proxy server. Squid is recommended for Linux, and WProxy is recommended for Windows.
- Download and install the SMS-Agent on the source server, modify the proxy settings in the SMS-Agent configuration file, and start the SMS-Agent. For details, see How Do I Configure a Source Server to Access Huawei Cloud Through a Proxy?
- Configure the target server. Set Network Type to Private during the configuration.
Ensure that the security group of the target server allows access from the source server's private IP address over the specified migration ports. For details about how to configure security group rules, see How Do I Configure Security Group Rules for Target Servers?
For a Scenario Where the Source Server Has No Internet Access and Cannot Communicate with the Target Server
Prepare proxy servers for forwarding control traffic and data traffic. The proxy servers must be able to communicate with the source server and the target server on Huawei Cloud.
- Configure a proxy server to forward control traffic to cloud services. For details, see step 1 in How Do I Configure a Source Server to Access Huawei Cloud Through a Proxy?
- Create at least one Nginx proxy server to forward data traffic based on the number of servers and the volume of data to be migrated. Run the following command to install the tool:
yum install nginx -y
- Configure Nginx to forward data traffic. The following uses CentOS 8 as an example:
- Open the /etc/ssh/sshd_config file, find the line containing Port 22, delete the default comment tag (#), and add a line containing Port 2222 below the line.

- Run the following command to restart the SSH service to apply the configuration:
systemctl restart sshd.service
- Run the following command to add a firewall rule:
iptables -A INPUT -m state --state NEW -m tcp -p tcp --dport 2222 -j ACCEPT
- Open the /etc/ssh/sshd_config file, find the line containing Port 22, add # to the line to restore the comment, and run the following command to restart the sshd service:
systemctl restart sshd.service
- Modify the /etc/nginx/nginx.conf configuration file.
- For a Linux file-level migration, add the following content to the end of the file. The content must be at the same identification level as http{} in the file. If multiple servers need to be migrated, add multiple mappings. default backend1 is mandatory because it is for the proxy server mapping.
stream { map $remote_addr $backend { default backend1; <IP-address of-source-server-1> backend2; <IP-address of-source-server-2> backend3; } server { listen 22; proxy_pass $backend; } upstream backend1 { server <IP-address-of-proxy-server>:22; } upstream backend2 { server <IP-address-of-target-server-1>:22; } upstream backend3 { server <IP-address-of-target-server-2>:22; } } - For a Windows migration, add the following content to the end of the file. The content must be at the same identification level as http{} in the file. If multiple servers need to be migrated, add multiple upstream backend_<x>_<xx> entries and mappings. The following is a configuration example:
stream { # Server 1 upstream backend_1_22 { server <IP-address-of-target-server-1>:22; } upstream backend_1_8899 { server <IP-address-of-target-server-1>:8899; } upstream backend_1_8900 { server <IP-address-of-target-server-1>:8900; } # Server 2 upstream backend_2_22 { server <IP-address-of-target-server-2>:22; } upstream backend_2_8899 { server <IP-address-of-target-server-2>:8899; } upstream backend_2_8900 { server <IP-address-of-target-server-2>:8900; } map $remote_addr $backend_22 { <IP-address-of-source-server-1> "backend_1_22"; <IP-address-of-source-server-2> "backend_2_22"; default X:22; } map $remote_addr $backend_8899 { <IP-address-of-source-server-1> "backend_1_8899"; <IP-address-of-source-server-2> "backend_2_8899"; default X:8899; } map $remote_addr $backend_8900 { <IP-address-of-source-server-1> "backend_1_8900"; <IP-address-of-source-server-2> "backend_2_8900"; default X:8900; } server { listen 22; proxy_pass $backend_22; } server { listen 8899; proxy_pass $backend_8899; } server { listen 8900; proxy_pass $backend_8900; } }
- For a Linux file-level migration, add the following content to the end of the file. The content must be at the same identification level as http{} in the file. If multiple servers need to be migrated, add multiple mappings. default backend1 is mandatory because it is for the proxy server mapping.
- Run the following command to check whether the Nginx configuration is correct:
nginx -t
If the message "successful" is displayed, the configuration is successful.
- After verifying that the configuration is correct, start the Nginx service.
nginx
- Run the following command to check whether Nginx is listening on the specified port:
netstat -ntpl
- Open the /etc/ssh/sshd_config file, find the line containing Port 22, delete the default comment tag (#), and add a line containing Port 2222 below the line.
- Download and install the SMS-Agent on the source server, modify the proxy settings in the SMS-Agent configuration file, and start the SMS-Agent. For details, see step 2 in How Do I Configure a Source Server to Access Huawei Cloud Through a Proxy?
- Configure the target server. Set Transit IP Address to the private IP address of the proxy server during the configuration.

Ensure that the proxy server is configured to allow inbound traffic from the source server's IP address, and the target server is configured to allow inbound traffic to the proxy server.
Figure 1 Setting a transit IP address
For a Scenario Where MgC Is Used to Batch Migrate Servers
Internet access is required for migration using MgC.
- Install the MgC Agent in the intranet environment. The MgC Agent must be able to access the source servers to be migrated. For details, see Installing the MgC Agent on Windows.
- Complete steps 2 to 5 described in Migrating On-premises Servers to Huawei Cloud Using MgC.

Ensure that the security group of the target server allows access from the source servers over the specified migration ports. For details about how to configure security group rules, see How Do I Configure Security Group Rules for Target Servers?
- Create a server migration workflow.
- If the source servers can access the Internet, set the migration network to Public.
Figure 2 Migration over the Internet
- If the source servers cannot access the Internet, prepare a proxy server that can access the Internet and install proxy software. For details, see step 1 in How Do I Configure a Source Server to Access Huawei Cloud Through a Proxy? The network requirements for the proxy server are as follows:
- Regardless whether the proxy server is on the source intranet environment or on the cloud, it must be able to access the source servers to be migrated over an intranet.
- The proxy server must be configured to allow inbound traffic from the source servers over the proxy port.
After the proxy server is configured, set the migration network to Private, and enter the private IP address of the proxy server and the port specified for the proxy software.Figure 3 Migration over a private network
- If the source servers can access the Internet, set the migration network to Public.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





