Managing Models
Scenarios
This topic walks you through how to manage models, such as enabling, disabling, and deleting a custom model.
- Enabling a model: SecMaster can use models to monitor log data in pipelines. If SecMaster detects the data that hits trigger conditions in a model, SecMaster generates an alert. After creating a model, you need to enable the model to use it to generate alerts.
- Disabling a model: If you do not need the model to generate alerts, you can disable the model.
- Deleting a model: If the model rules are no longer applicable and will not be used in the future, you can delete the model.
Limitations and Constraints
Only custom models can be enabled, disabled, and deleted.
Managing Models
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - Click
 in the upper left corner of the page and choose Security & Compliance > SecMaster.
in the upper left corner of the page and choose Security & Compliance > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose . Figure 2 Available Models
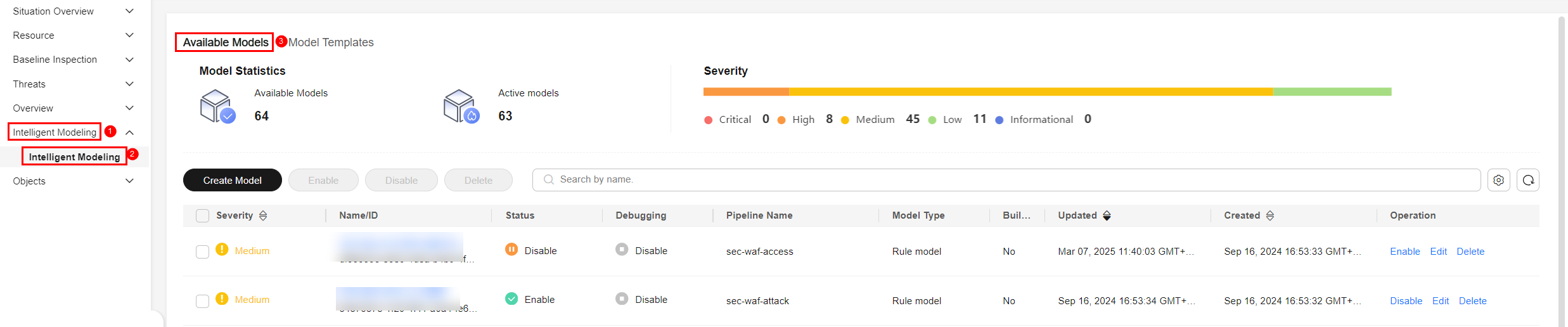
- On the Available Models tab, manage models.
Table 1 Managing models Operation
Description
Enable
In the model list, click Enable in the Operation column of the target model.NOTE:To enable models in batches, select all models you want to start and click Enable in the upper left corner of the list.
If the model status changes to Enable, the model is successfully started.
Disable
In the model list, locate the row that contains the target model and click Disable in the Operation column.
NOTE:To disable models in batches, select all models and click Disable in the upper left corner of the list.
When the alert model status changes to Disable, the model is disabled.
Delete
- In the model list, locate the row that contains the target model and click Delete in the Operation column. NOTE:
To delete models in batches, select all models to be deleted and click Delete in the upper left corner of the list.
- In the displayed dialog box, click OK.
- In the model list, locate the row that contains the target model and click Delete in the Operation column.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.






