Adding a Security Policy
Scenarios
Security policies are used to quickly prevent attacks. You can select a block type based on the alert source to block attackers. Table 1 lists recommended settings. You can also block an attack source based on the comprehensive investigation of multiple alerts.
| Alert Type | Defense Layer | Recommended Policy |
|---|---|---|
| HSS alerts | Server protection | VPC policies are recommended to block traffic. |
| WAF alerts | Application protection | WAF policies are recommended to block traffic. |
| CFW alerts | Network protection | CFW policies are recommended to block traffic. |
| IAM alerts | Identity authentication | IAM policies are recommended to block traffic. |
| OBS and DBSS alerts | Data protection | You can use VPC or CFW policies based on actual attack scenarios and investigation results to disconnect attack sources from protected resources. |
This topic describes how to add a security policy.
Limitations and Constraints
- In a workspace you have, you can add up to 300 security policies that support block aging, and a maximum of 2,500 security policies in total. Limits on blocked objects you can add are as follows:
- For a policy to be delivered to CFW, each time a maximum of 500 IP addresses can be added as blocked objects by each account.
- For a policy to be delivered to WAF, each time a maximum of 500 IP addresses can be added as blocked objects by each account.
- For a policy to be delivered to VPC, every minute a maximum of 500 IP addresses can be added once as blocked objects by each account.
- For a policy to be delivered to IAM, each time a maximum of 500 IAM users can be added as blocked objects by each account.
- If an IP address or IP address range or an IAM user is added to the blacklist, CFW, WAF, VPC, and IAM will block requests from that IP address or user without checking whether the requests are malicious.
- To ensure system stability, a maximum of five security policy tasks can be executed at the same time. If there are already five ongoing tasks, no more security policies can be added, retried, or edited.
- After security policy is added, its blocked object type and blocked objects, such as IP addresses, IP address ranges, or IAM user names, cannot be modified.
- After a security policy is added, its policy object, policy type, object type, and selected operation connections cannot be modified.
Adding a Security Policy
- (Optional) Create a SecMaster agency.
If the blocked object is an IAM user, you need to create a SecMaster agency before adding an emergency policy.
- Log in to the SecMaster console.
- Click
 in the upper left corner of the page and choose Management & Governance > Identity and Access Management.
in the upper left corner of the page and choose Management & Governance > Identity and Access Management. - Add a custom policy.
- In the navigation pane on the left, choose Permissions > Policies/Roles. In the upper right corner of the displayed page, click Create Custom Policy.
- Configure a policy.
- Policy Name: Enter a policy name.
- Policy View: Select JSON.
- Policy Content: Copy the following content and paste it in the text box.
1 2 3 4 5 6 7 8 9 10 11 12
{ "Version": "1.1", "Statement": [ { "Effect": "Allow", "Action": [ "iam:users:updateUser", "iam:users:listUsers" ] } ] }
- Click OK.
- Create an agency.
- In the navigation pane on the left, choose Agencies. On the page displayed, click SecMaster_Agency. The Basic Information page of SecMaster_Agency is displayed by default.
- On the Permissions tab, click Authorize.
- On the Select Policy/Role page, search for and select the policy added in 1.c and click Next.
- Set the authorization scope. Select All resources for Scope. After the setting is complete, click OK.
- Log in to the SecMaster console.
- Click
 in the upper left corner of the page and choose Security & Compliance > SecMaster.
in the upper left corner of the page and choose Security & Compliance > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose Risk Prevention > Security Policies. On the displayed page, click the Policy View tab. Figure 2 Accessing the policy management page
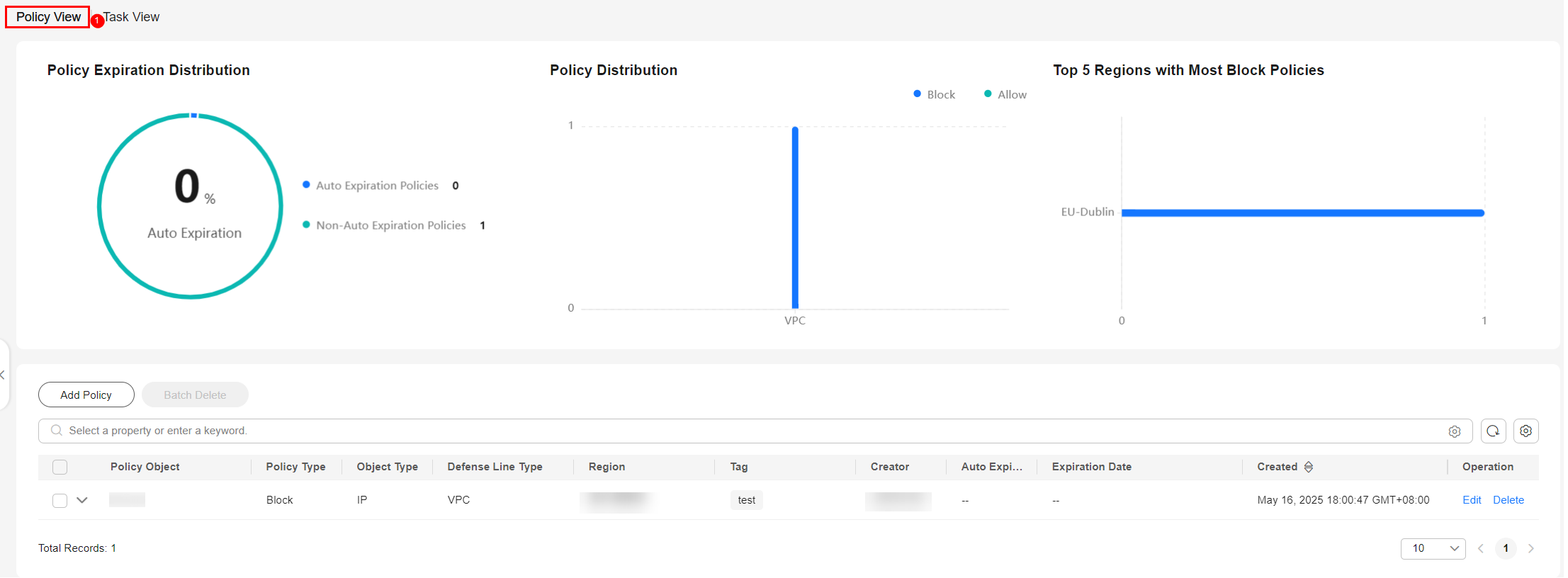
- On the Policy View tab displayed by default, click Add Policy. The page for adding a policy slides out from the right of the page.
- On the displayed page, configure policy information.
Table 2 Policy parameters Parameter
Description
Policy Type
Type of the policy. You can select Block or Allow.
- If Block is selected, the access from the policy object will be denied.
- Allow: The access from the policy object will be allowed.
Object Type
If Policy Type is set to Block, Object Type can be set to IP, Account, or Domain name.
If Policy Type is set to Allow, Object Type can be set to IP or Domain name.
Select an object type based on your needs.
- If IP is selected, the operation object of the policy is an IP address or IP address range.
- If Domain name is selected, the operation object of the policy is a domain name.
- If Account is selected, the policy is applied to a cloud service account (IAM user).
Policy Object
Enter one or more policy objects.
- If Object Type is set to IP, enter IP addresses or IP address ranges. Enter one or more IP addresses or IP address ranges and separate them with commas (,).
Example: IPv4: 192.168.0.0 or 192.168.0.0/12; IPv6: 0:0:0:0:0:0:0:0 or 0:0:0:0:0:0:0:0/128.
- If Object Type is set to Domain name, enter domain names. Enter one or more domain names. If there are multiple domain names, separate them with commas (,). Enter a maximum of 63 characters. Only letters, digits, hyphens (-), underscores (_), and periods (.) are allowed.
- If Policy type is set to Block and Object Type is set to Account, set Policy Object to the cloud service account (IAM user). Enter one or more cloud service accounts (IAM usernames). If there are multiple cloud service accounts (IAM usernames), separate them with commas (,).
Policy Application Scope
Select Current region and enterprise project or All regions and enterprise projects based on your needs.
Operation Connection
Operation connections associated with the emergency policy process. Select the operation connection of the policy based on your needs.
Auto Expiration
Auto expiration configured for the policy.
- If you select Yes, set the policy expiration time.
- If you select No, the policy is always valid.
Tag (Optional)
Tag of the custom emergency policy.
Policy Description (Optional)
Description of the custom policy.
- Click OK.
- After adding a security policy, go to the Security Policies page to check new policy information.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.






