Importing and Exporting Vulnerabilities
Scenarios
SecMaster can integrate vulnerability scan results from Host Security Service (HSS) and vulnerability data you import into SecMaster, so that you can quickly locate vulnerable assets and fix vulnerabilities.
Importing Vulnerabilities: For some cloud services or assets, SecMaster cannot automatically synchronize vulnerabilities on them. You can manually import such vulnerabilities into SecMaster for centralized management.
Exporting Vulnerabilities: SecMaster allows you to export the vulnerability list and customize vulnerability parameters to view details about all vulnerabilities.
This section describes how to import and export vulnerabilities.
Limitations and Constraints
- Only files in .xlsx can be imported. Each time you can import a file no larger than 5 MB with a maximum of 100 records.
- A maximum of 9,999 vulnerability records can be exported from SecMaster.
Importing Vulnerabilities
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - Click
 in the upper left corner of the page and choose Security & Compliance > SecMaster.
in the upper left corner of the page and choose Security & Compliance > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

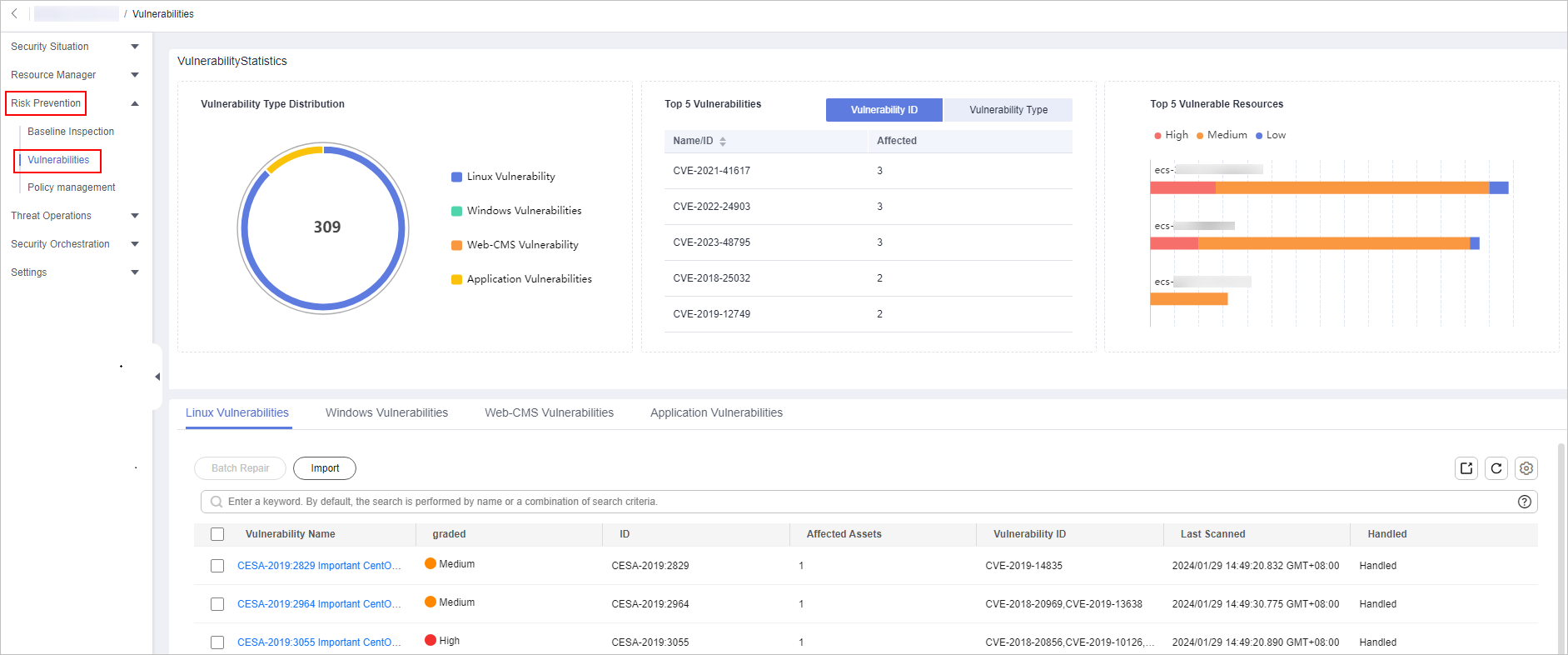
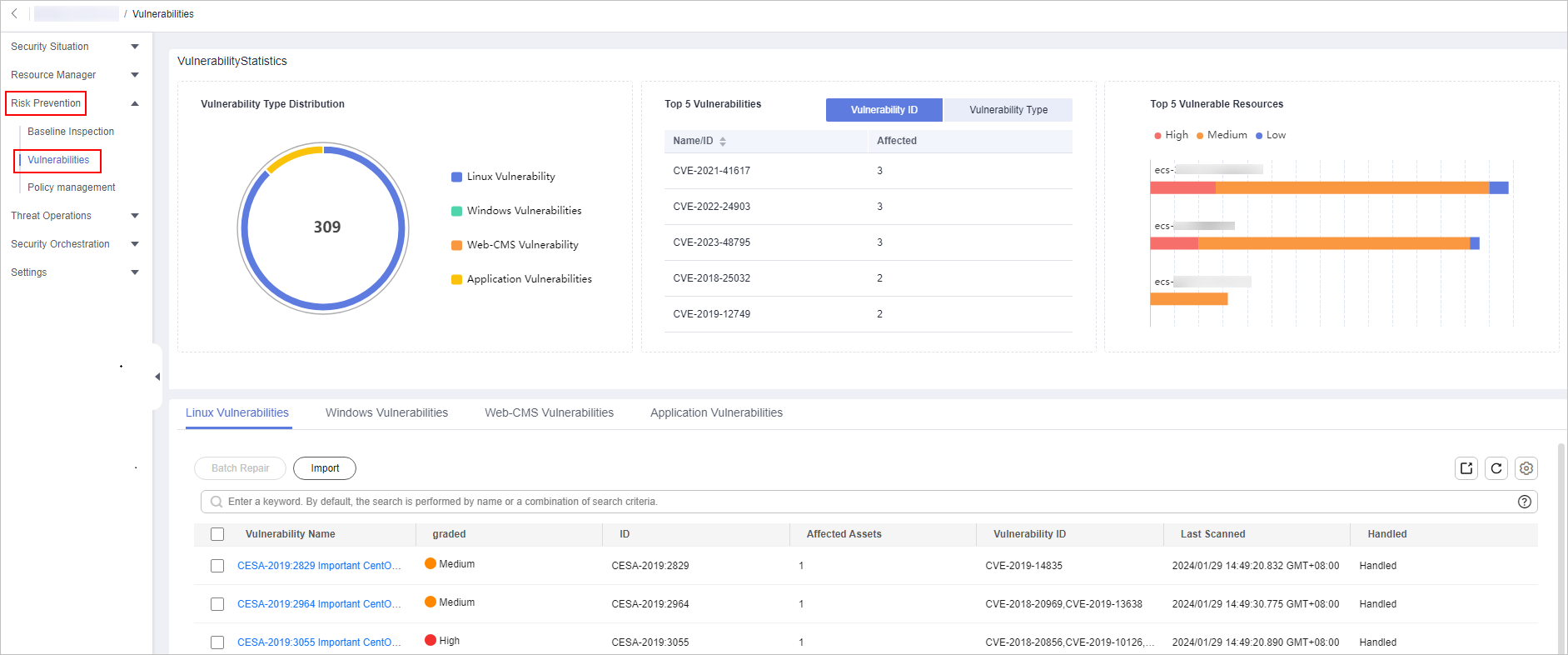
- In the navigation pane on the left, choose Risk Prevention > Vulnerabilities. Figure 2 Accessing the Vulnerabilities page
- On the displayed page, select a tab to go to the corresponding vulnerability management page.
For example, to import Linux vulnerabilities, click the Linux Vulnerabilities tab.
- Click Import above the vulnerability list. The Import dialog box is displayed.
Only files in .xlsx can be imported. Each time you can import a file no larger than 5 MB with a maximum of 100 records.
- In the Import dialog box, click Download Template to download a template, and fill in the downloaded template according to the requirements.
- After the vulnerability file is ready, click Select File in the Import dialog box, and select the Excel file you want to import.
- Click OK.
- After the import is complete, choose to view vulnerability information. You can filter vulnerabilities by vulnerability name or ID.
Exporting Vulnerabilities
A maximum of 9,999 vulnerability records can be exported.
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - Click
 in the upper left corner of the page and choose Security & Compliance > SecMaster.
in the upper left corner of the page and choose Security & Compliance > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 3 Workspace management page

- In the navigation pane on the left, choose Risk Prevention > Vulnerabilities. Figure 4 Accessing the Vulnerabilities page
- On the Vulnerabilities page, click the target vulnerability tab.
For example, if you want to export Linux vulnerabilities, click the Linux Vulnerabilities tab.
- Click
 in the upper right corner above the vulnerability list. The Export dialog box is displayed.
in the upper right corner above the vulnerability list. The Export dialog box is displayed. 
A maximum of 9,999 vulnerability records can be exported.
- In the Export dialog box, set vulnerability parameters.
Table 1 Exporting vulnerabilities Parameter
Description
Format
By default, the vulnerability list is exported into an Excel.
Columns
Select the parameters included in the exported file.
- Click OK.
The system automatically downloads the Excel to your local PC.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.






