Ignoring and Unignoring a Vulnerability
Scenarios
Some vulnerabilities are risky only in specific conditions. For example, if a vulnerability can be exploited only through an open port, but there are no open ports on the target server, the vulnerability will not harm the server. Such vulnerabilities can be ignored. HSS will still generate alerts when next time it finds the vulnerabilities you ignore before. SecMaster will synchronize the vulnerability information as well. You can also unignore a vulnerability as needed.
This topic describes how to ignore a vulnerability and cancel ignoring a vulnerability.
Ignoring and Unignoring a Vulnerability
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - Click
 in the upper left corner of the page and choose Security & Compliance > SecMaster.
in the upper left corner of the page and choose Security & Compliance > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose Risk Prevention > Vulnerabilities. Figure 2 Accessing the Vulnerabilities page
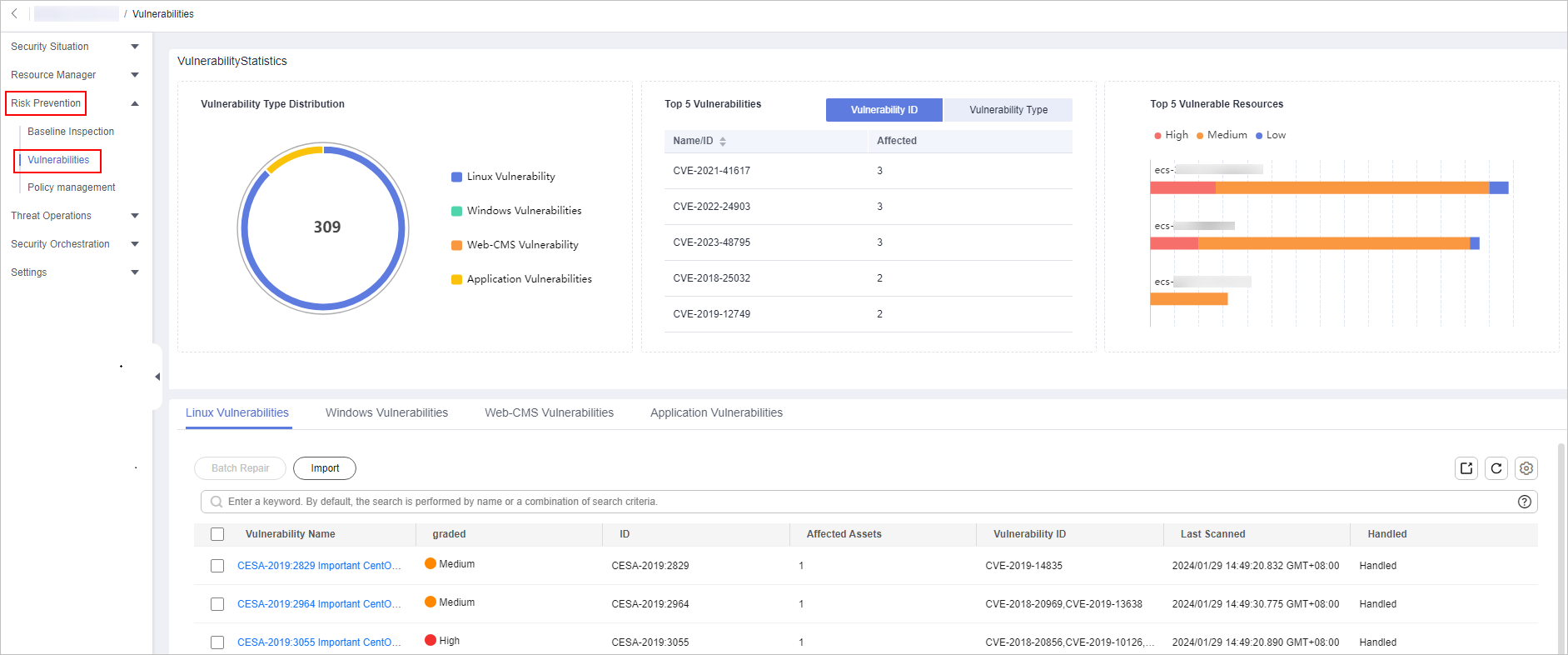
- On the Vulnerabilities page, click any vulnerability type tab. In the vulnerability list, click the name of the target vulnerability. The vulnerability details page is displayed on the right.
For example, if you want to handle a Linux vulnerability, click the Linux Vulnerabilities tab and click the target vulnerability name. Then, you can view the vulnerability details on the page displayed on the right.
- Ignore or unignore the target vulnerability.
- Ignore
On the Vulnerability Details page, go to the Affected Resources area. In the resource list, locate the row that contains the target resource and click Ignore in the Operation column.
- Unignore
- On the Vulnerability Details page, go to the Affected Resources area. In the resource list, locate the row that contains the target resource and click Cancel Ignore in the Operation column.
- In the confirmation dialog box displayed, confirm the information and click OK.
- Ignore
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.






