Configuring Security Group Rules
Scenarios
Similar to firewall, a security group is a logical group used to control network access. You can define access rules for a security group to protect the ECSs that are added to this security group.
- Inbound: Inbound rules allow external network traffic to be sent to the ECSs in the security group.
- Outbound: Outbound rules allow network traffic from the ECSs in the security group to be sent out of the security group.
For details about the default security group rules, see Default Security Groups and Security Group Rules. For details about configuration examples for security group rules, see Security Group Configuration Examples.
Procedure
- Log in to the ECS console and access the ECS list page.
- Click
 in the upper left corner and select a region and project.
in the upper left corner and select a region and project. - Click
 . Under Compute, click Elastic Cloud Server.
. Under Compute, click Elastic Cloud Server. - On the Elastic Cloud Server page, click the name of the target ECS.
The ECS details page is displayed.
- Click the Security Groups tab, expand the information of the security group, and view security group rules.
- Click the security group ID.
The system automatically switches to the security group details page.
- Configure inbound rule parameters as prompted. You can add multiple inbound rules one by one.
Figure 1 Add Inbound Rule
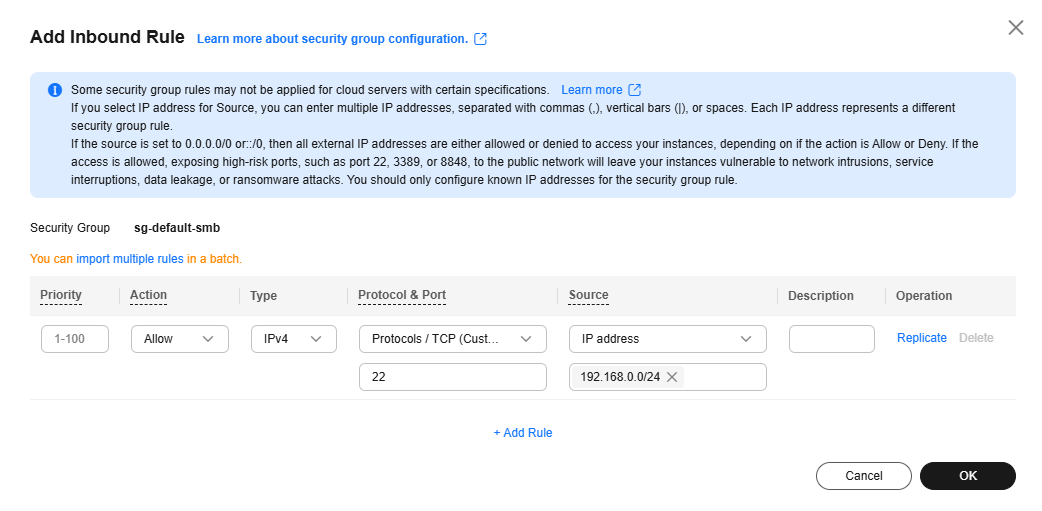
Table 1 Inbound rule parameter description Parameter
Description
Example Value
Priority
The security group rule priority.
The priority value ranges from 1 to 100. The default value is 1 and has the highest priority. The security group rule with a smaller value has a higher priority.
1
Action
The value can be Allow or Deny.- If the Action is set to Allow, traffic is allowed to access the cloud servers in the security group over specified ports.
- If the Action is set to Deny, traffic is denied to access the cloud servers in the security group over specified ports.
Security group rules are matched by priority and then by action. Deny rules take precedence over allow rules. For more information, see How Traffic Matches Security Group Rules.
Allow
Type
Source IP address version. You can select:- IPv4
- IPv6
IPv4
Protocol & Port
The network protocol used to match traffic in a security group rule. The protocol can be All, TCP, UDP, GRE, or ICMP.
TCP
Destination port used to match traffic in a security group rule. The value can be from 1 to 65535.
Inbound rules control incoming traffic over specific ports to instances in the security group.
Enter ports in any of the following formats:- Individual port: Enter a port, such as 22.
- Consecutive ports: Enter a port range, such as 22-30.
- All ports: Leave it empty or enter 1-65535.
22, 22-30
Source
Used to match the source of an external request. The source can be:- IP address: The source is a fixed IP address. You can enter or paste multiple IP addresses separated by commas (,). Each IP address represents a different security group rule.
- Single IP address: IP address/mask
Example IPv4 address: 192.168.10.10/32
Example IPv6 address: 2002:50::44/128
- IP address range in CIDR notation: IP address/mask
Example IPv4 address range: 192.168.52.0/24
Example IPv6 address range: 2407:c080:802:469::/64
- Any IP addresses
0.0.0.0/0 represents all IPv4 addresses.
::/0 represents all IPv6 addresses.
- Single IP address: IP address/mask
- Security group: The source is from another security group. You can select a security group in the same region from the drop-down list. If there is instance A in security group A and instance B in security group B, and the inbound rule of security group A allows traffic from security group B, traffic is allowed from instance B to instance A.
- IP address group: The source is from an IP address group. An IP address group is a set of one or more IP addresses. You can select an available IP address group from the drop-down list. For IP address ranges and IP addresses with the same security requirements, you can use an IP address group to simplify management.
IP address:
192.168.52.0/24,10.0.0.0/24
Description
(Optional) Supplementary information about the security group rule.
The security group rule description can contain a maximum of 255 characters and cannot contain angle brackets (< or >).
N/A
- Configure outbound rule parameters as prompted. You can add multiple outbound rules one by one.
Figure 2 Add Outbound Rule
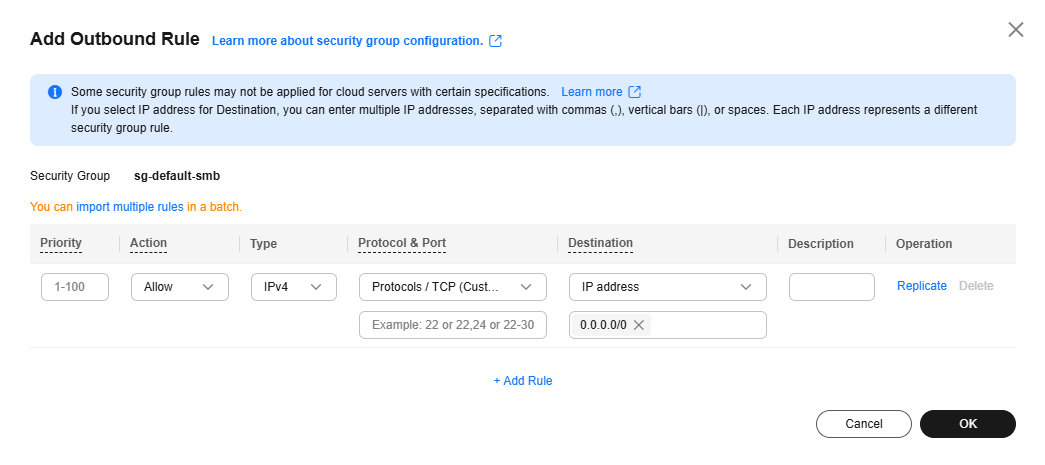
Table 2 Outbound rule parameter description Parameter
Description
Example Value
Priority
The security group rule priority.
The priority value ranges from 1 to 100. The default value is 1 and has the highest priority. The security group rule with a smaller value has a higher priority.
1
Action
The value can be Allow or Deny.- If the Action is set to Allow, access from ECSs in the security group is allowed to the destination over specified ports.
- If the Action is set to Deny, access from ECSs in the security group is denied to the destination over specified ports.
Security group rules are matched by priority and then by action. Deny rules take precedence over allow rules. For more information, see How Traffic Matches Security Group Rules.
Allow
Type
Destination IP address version. You can select:- IPv4
- IPv6
IPv4
Protocol & Port
The network protocol used to match traffic in a security group rule. The protocol can be All, TCP, UDP, GRE, or ICMP.
TCP
Destination port used to match traffic in a security group rule. The value can be from 1 to 65535.
Outbound rules control outgoing traffic over specific ports from instances in the security group.
Enter ports in any of the following formats:- Individual port: Enter a port, such as 22.
- Consecutive ports: Enter a port range, such as 22-30.
- All ports: Leave it empty or enter 1-65535.
22, 22-30
Destination
Used to match the destination of an internal request. The destination can be:- IP address: The destination is a fixed IP address. You can enter or paste multiple IP addresses separated by commas (,). Each IP address represents a different security group rule.
- Single IP address: IP address/mask
Example IPv4 address: 192.168.10.10/32
Example IPv6 address: 2002:50::44/128
- IP address range in CIDR notation: IP address/mask
Example IPv4 address range: 192.168.52.0/24
Example IPv6 address range: 2407:c080:802:469::/64
- Any IP addresses
0.0.0.0/0 represents all IPv4 addresses.
::/0 represents all IPv6 addresses.
- Single IP address: IP address/mask
- Security group: The destination is another security group. You can select a security group in the same region under the current account from the drop-down list. If there is instance A in security group A and instance B in security group B, and the outbound rule of security group A allows traffic to security group B, traffic is allowed from instance A to instance B.
- IP address group: The destination is in an IP address group. An IP address group is a set of one or more IP addresses. You can select an available IP address group from the drop-down list. For IP address ranges and IP addresses with the same security requirements, you can use an IP address group to simplify management.
IP address:
192.168.52.0/24,10.0.0.0/24
Description
(Optional) Supplementary information about the security group rule.
The security group rule description can contain a maximum of 255 characters and cannot contain angle brackets (< or >).
N/A
- Click OK to complete the security rule configuration.
Checking Whether a Port Is Enabled on an ECS
After allowing traffic over a port in a security group rule, you need to ensure that the port used by the instance is also opened.
- Log in to the ECS and check whether the ECS port is enabled.
- Checking a Linux ECS port
Run the following command to check whether TCP port 80 is being listened on:
netstat -an | grep 80
If the following figure is displayed, TCP port 80 is enabled.
Figure 3 Command output for the Linux ECS
- Checking a Windows ECS port
- Checking a Linux ECS port
- Enter http://ECS EIP in the address box of the browser and press Enter.
If the requested page can be accessed, the security group rule has taken effect.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.







