(Optional) Step 1: Buy an ECS
This topic walks you through how to buy an ECS for installing the log collector.
To collect data, you need to prepare an ECS and install the log collector on the ECS. Make sure the system disk capacity for the ECS is not less than 50 GiB. If you already have an ECS that meets the requirements, skip this step.
Prerequisites
You have obtained the IAM administrator account information.
Buying an ECS
- View the ECS information.
- Log in to the SecMaster console as the IAM administrator.
- Click
 in the upper left corner of the management console, select a region or project, click
in the upper left corner of the management console, select a region or project, click  in the upper left corner of the page, and choose Compute > Elastic Cloud Server.
in the upper left corner of the page, and choose Compute > Elastic Cloud Server. - On the ECS list page, click the name of the target ECS to go to its details page.
- View ECS details about AZ, Specifications, Image, System Disk, and Data Disk. Figure 1 Viewing ECS information
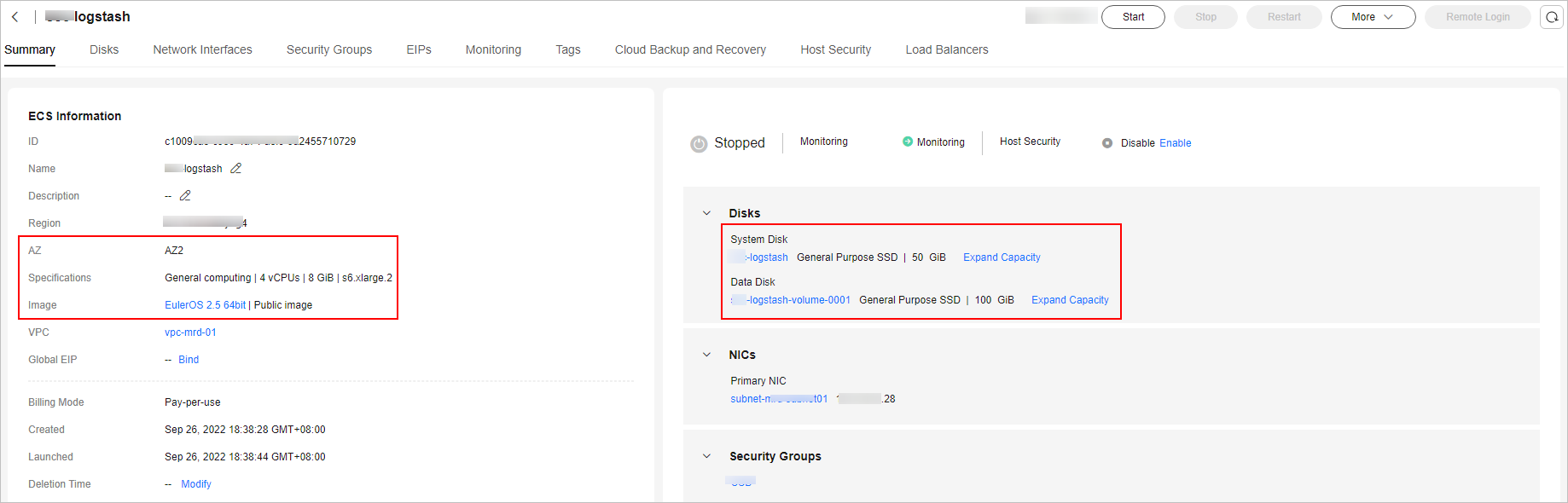
- Check whether the ECS system disk size is 50 GiB or above.
- If yes, skip (Optional) Step 1: Buy an ECS and go to (Optional) Step 2: Buy a Data Disk.
- If no, go to 2 and buy an ECS.
- Go back to the Elastic Cloud Server page and click Buy ECS in the upper right corner of the page.
- On the ECS purchase page, configure parameters.
Table 1 Parameters for purchasing an ECS Parameter
Description
Basic Configuration
Configure Billing Mode and Region based on your service requirements.
If there are no special requirements for AZ, just select Random.
Instance
CPU Architecture
Select x86.
The component controller (isap-agent) of the log collector can run on a Linux x86 or Arm ECS.
Search Filters
Select an instance that meets the requirements as required. Minimum requirements: 2vCPUs and 4 GiB Memory.
OS
Image
You are advised to select and then select the specific image as required.
Do not select images whose names contain "dedicated for making resources and not support password injection" because such images cannot be logged in to using passwords.
After selecting an image, set Host protection (HSS) if needed.
Storage & Backup
System Disk
Minimum requirements for System Disk: 50 GiB.
Select a system disk that meets the requirements.
Data Disk
Minimum requirements for Data Disk: 100 GiB.
Click Add Data Disk and select a data disk that meets the requirements.
Enable backup
Configure those parameters based on your service needs.
Network
VPC
Configure those parameters based on your service needs.
After the configuration, record the selected VPC and subnet information, which will be used later.
Primary NIC
Security Group
Configure this parameter as required.
Public Network Access
Configure this as required.
Instance Management
Configure this parameter based on your needs.
After the configuration, record the settings for ECS Name, Username, and Password.
Advanced Settings
Configure parameters as required.
Quantity
Configure this parameter as needed.
- Check the configurations, select the agreement, and click Submit.
- On the order page, select a payment method and complete the payment.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.






