Delivering Logs to Other Data Pipelines
Scenarios
This topic walks you through how to deliver logs to other pipelines. The main steps are as follows:
Notes and Constraints
- When performing cross-account delivery, the data can only be delivered to the pipelines instead of cloud services of other accounts.
- If the new data delivery is cross-account, you need to log in to SecMaster using the destination account and authorize the delivery.
Step 1: Create a Data Delivery Task
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose . Figure 2 Accessing the Security Analysis tab

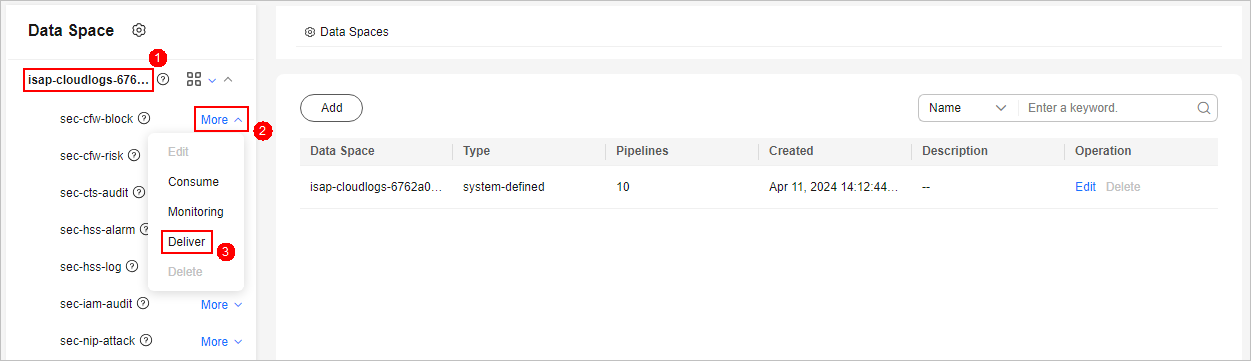
- In the data space navigation tree on the left, click the data space name to expand all pipelines. Next to the name of the target pipeline, click More > Deliver. Figure 3 Accessing data delivery settings page
- (Optional) Confirm the authorization information and click OK.
Authorization is required the first time you start a delivery to a specific destination type. If the destination type has been authorized, skip this step.
- On the Create Delivery panel, configure data delivery parameters.
- Configure basic information.
Table 1 Basic Information Parameter
Description
Delivery Name
The name you specify for the delivery.
Resource Consumption
The value is generated by default. You do not need to configure it.
- Configure the data source. In the Data Source Settings area, the details about the current pipeline are displayed. You do not need to set this parameter.
Table 2 Data source parameters Parameter
Description
Delivery Type
Data delivery type. The default value is PIPE, indicating that data is delivered from the SecMaster pipeline.
Region
Region where the current pipeline is located.
Workspace
Workspace to which the current pipeline belongs.
Data Space
Data space to which the current pipeline belongs.
Pipeline
Name of the pipeline.
Data Read Policy
Data read policy of the current pipeline.
Read By
Identity of the data source reader.
- Configure the delivery destination.
- PIPE: Deliver the current pipeline data to other pipelines of the current account or pipelines of other accounts. Set this parameter as required.
- Current: Deliver the current pipeline data to another pipeline of the current account. For details about the parameters, see Table 3.
Table 3 Destination parameters - Current account pipeline Parameter
Description
Account Type
Account type for the data delivery destination. Select Current.
Delivery Type
Delivery type. Select PIPE.
Workspace
Workspace where the destination pipeline is located.
Data Space
Data space where the destination pipeline is located.
Pipeline
Pipeline where the destination pipeline is located.
Written To
The value is generated by default. You do not need to configure it.
- Cross-account delivery: Deliver the current pipeline data to the pipeline of another account. For details about the parameters, see Table 4.
Table 4 Destination parameters - Pipelines of other account Parameter
Description
Account Type
Account type for the data delivery destination. Select Other in this case.
Delivery Type
Delivery type. Select PIPE.
Account ID
ID of the account to which the destination pipeline belongs.
Workspace ID
ID of the workspace where the destination pipeline is located. For details about how to query the workspace ID, see 6.
Data Space ID
ID of the data space where the destination pipeline is located. For details about how to query the data space ID, see 6.
Pipeline ID
ID of the destination pipeline. For details about how to query the pipeline ID, see 6.
Written To
The value is generated by default. You do not need to configure it.
- Current: Deliver the current pipeline data to another pipeline of the current account. For details about the parameters, see Table 3.
- PIPE: Deliver the current pipeline data to other pipelines of the current account or pipelines of other accounts. Set this parameter as required.
- Under Access Authorization, view the permissions granted in 6.
A delivery requires the read and write permissions to access your cloud resources. A delivery task cannot access your cloud resources unless the access is authorized by you.
- Configure basic information.
- Click OK.
Step 2: Authorize the Data Delivery
- In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 4 Workspace management page

- In the navigation pane on the left, choose . On the security analysis page displayed, click the Data Delivery tab.
- On the Data Delivery tab, click the Delivery Permissions tab. On the page displayed, click Accept in the Operation column of the target delivery task.
To accept authorization in batches, select all tasks to be authorized and click Accept in the upper left corner above the list.
Figure 5 Authorization for data delivery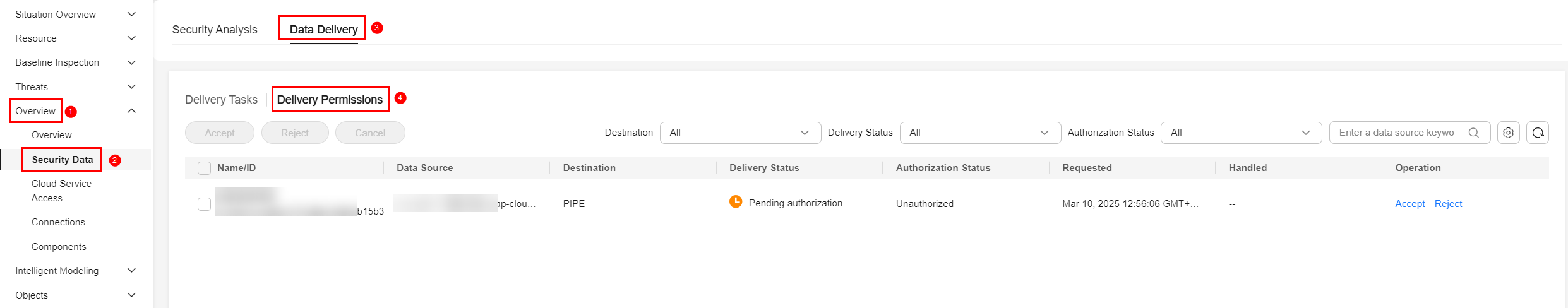
After the authorization is granted, the authorization status of the target delivery task is updated to Authorized. You can go to the delivery destination to view the delivery details.
Step 3: View Data Delivery in the Destination Pipeline
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 6 Workspace management page

- In the navigation pane on the left, choose . Figure 7 Accessing the Security Analysis tab

- In the data space navigation tree on the left, click a data space name to show the pipeline list. Click a pipeline name. On the displayed page, you can search the pipeline data. Figure 8 Pipeline data page
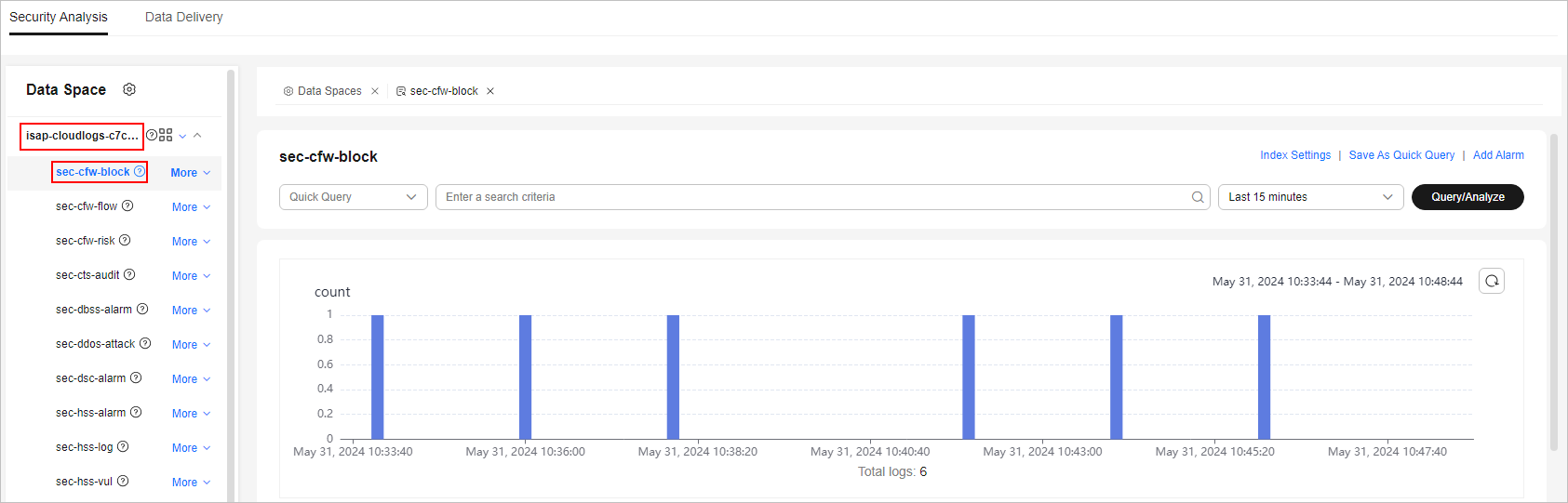
- In the target pipeline, view the delivery log.
Operations Related to Data Delivery Authorization
On the Cross-tenant Permissions tab page, you can select to Reject or Cancel the authorization.
| Operation | Description |
|---|---|
| Reject | In the row containing the target delivery task, click Reject in the Operation column to reject the authorization. To reject authorization in batches, select all tasks to be rejected and click Reject in the upper left corner of the list. |
| Cancel |
|
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





