Configuring a Global Whitelist Rule to Ignore False Positives
When EdgeSec detects a malicious attack that matches the basic web protection rule or custom rules you configure, it processes the attack event based on the protective action in the hit rule.
You can add false alarm masking rules to let EdgeSec ignore certain rule IDs or event types (for example, skip XSS checks for a specific URL).
- If you select All protection for Ignore EdgeSec Protection, all EdgeSec rules do not take effect, and EdgeSec allows all request traffic to the domain names in the rule.
- If you select Basic Web Protection for Ignore EdgeSec Protection, you can ignore basic web protection by rule ID, attack type, or all built-in rules. For example, if XSS check is not required for a URL, you can whitelist XSS rule.
Prerequisites
A protected website has been added. For details, see Adding a Website to EdgeSec.
Constraints
- If you select All protection for Ignore EdgeSec Protection, all EdgeSec rules do not take effect, and EdgeSec allows all request traffic to the domain names in the rule.
- If you select Basic web protection for Ignore Protection, global protection whitelist rules take effect only for events triggered against EdgeSec built-in rules in Basic Web Protection and anti-crawler rules under Feature Library.
- Basic Web Protection
Basic web protection defends against common web attacks, such as SQL injection, XSS attacks, remote buffer overflow attacks, file inclusion, Bash vulnerability exploits, remote command execution, directory traversal, sensitive file access, and command and code injections. Basic web protection also detects web shells and evasion attacks.
- Bot Protection
Feature-based anti-crawler identifies and blocks crawler behavior from search engines, scanners, script tools, and other crawlers.
- Basic Web Protection
- It takes several minutes for a new rule to take effect. After the rule takes effect, protection events triggered by the rule will be displayed on the Events page.
- You can configure a global protection whitelist rule by referring to Handling False Alarms. After handling a false alarm, you can view the rule in the global protection whitelist rule list.
Procedure
- Log in to the EdgeSec console.
- In the navigation pane on the left, choose . The Website Settings page is displayed.
- In the Policy column of the row containing the domain name, click the number to go to the Policies page.
Figure 1 Website list

- In the Global Protection Whitelist configuration area, change Status if needed.
Figure 2 Global Protection Whitelist configuration area
- In the upper left corner of the Global Protection Whitelist page, click Add Rule.
- Add a global whitelist rule by referring to Table 1.
Figure 3 Add Global Protection Whitelist Rule
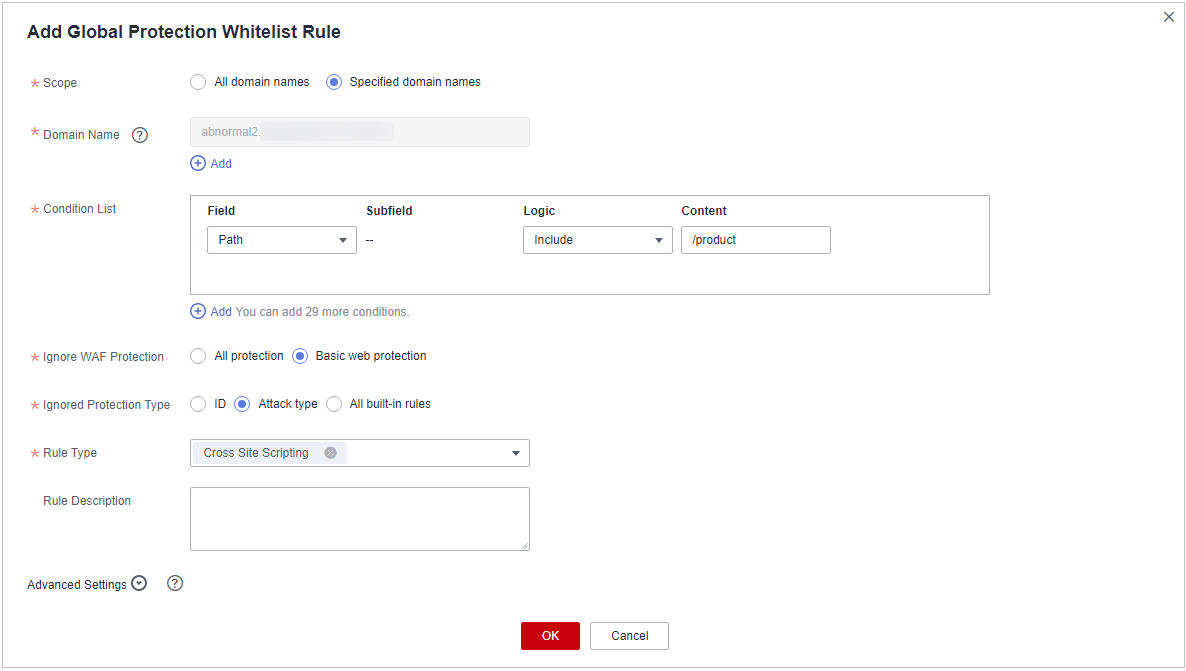
Table 1 Parameters Parameter
Description
Example Value
Scope
- All domain names: By default, this rule will be used to all domain names that are protected by the current policy.
- Specified domain names: This rule will be used to specific domain names.
Specified domain names
Domain Name
This parameter is mandatory when you select Specified domain names for Scope.
Enter a single domain name that matches the wildcard domain name being protected by the current policy.
www.example.com
Condition List
Click Add to add conditions. At least one condition needs to be added. You can add up to 30 conditions to a protection rule. If more than one condition is added, all of the conditions must be met for the rule to be applied. A condition includes the following parameters:
Parameters for configuring a condition are described as follows:- Field
- Subfield: Configure this field only when Params, Cookie, or Header is selected for Field.
NOTICE:
The length of a subfield cannot exceed 2,048 bytes. Only digits, letters, underscores (_), and hyphens (-) are allowed.
- Logic: Select a logical relationship from the drop-down list.
- Content: Enter or select the content that matches the condition.
Path, Include, /product
Ignore EdgeSec Protection
- All protection: All EdgeSec rules do not take effect, and EdgeSec allows all request traffic to the domain names in the rule.
- Basic Web Protection: You can ignore basic web protection by rule ID, attack type, or all built-in rules. For example, if XSS check is not required for a URL, you can whitelist XSS rule.
Basic Web Protection
Ignored Protection Type
If you select Basic web protection for Ignored Protection Type, specify the following parameters:
- Attack type: Configure the rule by attack type, such as XSS and SQL injection. One type contains one or more rule IDs.
- All built-in rules: all checks enabled in Basic Web Protection.
Attack type
Attack type
This parameter is mandatory when you select Attack type for Ignored Protection Type.
Select an attack type from the drop-down list box.
EdgeSec can defend against XSS attacks, web shells, SQL injection attacks, malicious crawlers, remote file inclusions, local file inclusions, command injection attacks, and other attacks.
SQL injection
Rule Description
A brief description of the rule. This parameter is optional.
SQL injection attacks are not intercepted.
Advanced Settings
To ignore attacks of a specific field, specify the field in the Advanced Settings area. After you add the rule, EdgeSec will stop blocking attack events of the specified field.
Select the target field from the first drop-down list box on the left. The following fields are supported: Params, Cookie, Header, Body, and Multipart.- If you select Params, Cookie, or Header, you can select All or Specified field to configure a subfield.
- If you select Body or Multipart, you can select All.
- If you select Cookie, the Domain Name and Path can be empty.
NOTE:If All is selected, EdgeSec will not block all attack events of the selected field.
Params
All
- Click OK.
Other Operations
- To modify a rule, click Edit in the row containing the rule.
- To delete a rule, click Delete in the row containing the rule.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





