Billing Items
Billing Description
The billing items of SecMaster consist of the service edition, quota, and value-added package. For details, see Table 1.
|
Billing Item |
Description |
Billing Mode |
Billing Formula |
|
|---|---|---|---|---|
|
(Mandatory) Edition |
Billing factor: service edition + Quota. Different editions provide different functions. |
Yearly/Monthly and pay-per-use billing |
|
|
|
(Mandatory) Quota |
||||
|
Value-added package (optional) |
Large screen |
SecMaster large screen can display security analysis result on a large screen, making it easier for you to obtain better demonstration effects for some scenarios such as onsite presentation, reporting, and real-time monitoring. Billing factors: large screen - security situation metrics. |
Yearly/Monthly and pay-per-use billing |
|
|
Log audit |
If security data collection and storage are required, you can purchase the data collection volume and data retention volume packages separately. Billing factors: security data collection volume and security data storage volume. |
Yearly/Monthly and pay-per-use billing |
||
|
Security analysis |
If security data collection, security data retention, security data export, platform security data, and security modeling analysis are required, you can purchase security analysis quotas separately. Billing factor: security analysis data volume. |
Yearly/Monthly and pay-per-use billing |
|
|
|
Security orchestration |
Security orchestration can help you handle and investigate incidents automatically. You can buy security orchestration separately. Billing factor: You will be billed for how many times workflow nodes (including the start and end nodes, but excluding judgement nodes) are executed during playbook execution. |
Yearly/Monthly and pay-per-use billing |
|
|
Table 2 describes the functions in the value-added package.
|
Scenario |
Description |
|---|---|
|
Purchase |
|
|
Billing |
Value-added packages are billed separately. There is no impact on the service edition and quota you have purchased. |
|
Free quotas |
A certain free quota is offered for security analysis and security orchestration in the value-added package. Table 3 shows details about free quotas. If the free quotas cannot meet your business needs, you can enable corresponding functions in the value-added packages separately. |
|
Use |
If you purchase yearly/monthly security data collection, security data retention, security analysis, and security orchestration, there are some limitations you need to know. The details are as follows:
|
|
Function |
Standard Edition |
Professional edition |
|
|---|---|---|---|
|
Security analysis |
Security data collection |
120 MB/day/quota |
120 MB/day/quota |
|
Security data retention |
120 MB/day/quota |
120 MB/day/quota |
|
|
Security data export |
120 MB/day/quota |
120 MB/day/quota |
|
|
Platform security data |
40 MB/day/quota |
40 MB/day/quota |
|
|
Security Modeling Analysis |
× |
120 MB/day/quota |
|
|
Threat management |
Preset threat models |
× |
Calculation model data: 120 MB/day/quota; Preset models: 200 |
|
Preset response playbooks |
× |
Preset playbooks: 30 |
|
|
Security orchestration |
Security orchestration |
× |
Operations: 7,000 |
|
Package |
Recommended Configuration for Yearly/Monthly Subscription |
Package Specifications |
Applicable Range |
|---|---|---|---|
|
Security Data Collection |
The volume of data you expect SecMaster to collect each day. Minimum value: 5 GB. You can estimate the volume by multiplying the number of ECSs you have by 120 MB. Maximum volume for each order: 500 GB. When you make a purchase, SecMaster auto-fills this parameter based on the new log volume you specify. You do not need to configure this parameter separately. |
5 * 1 GB |
0 GB to 5 GB (included) |
|
5 * 2 GB |
5 GB to 10 GB (included) |
||
|
5 * 3 GB |
10 GB to 15 GB (included) |
||
|
... The others follow the same rule. A maximum of 500 GB can be purchased through an order. |
... The others follow the same rule. |
||
|
Security Data Retention |
The volume of data you expect SecMaster to store. The minimum volume is 100 GB. You can estimate the volume by multiplying new log volume per day by seven. The maximum volume for each order is 3,500 GB. When you make a purchase, SecMaster auto-fills this parameter based on the new log volume you specify. You do not need to configure this parameter separately. |
100 * 1 GB |
0 GB to 100 GB (included) |
|
100 * 2 GB |
100 GB to 200 GB (included) |
||
|
100 * 3 GB |
200 GB to 300 GB (included) |
||
|
... The others follow the same rule. A maximum of 3,500 GB can be purchased through an order. |
... The others follow the same rule. |
Billing Examples
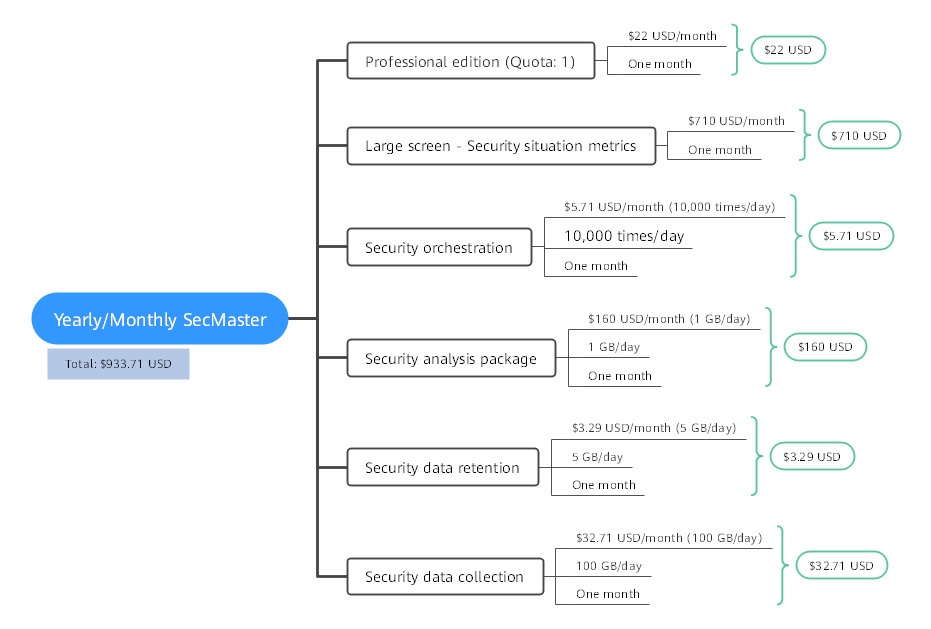
Assume that you purchased a yearly/monthly SecMaster professional edition (Quota: 1) at 15:50:04 on June 30, 2024, as well as the value-added package, including large screen, security data collection (5 GB/month), security data retention (100 GB/month), security analysis (1 GB/day), and security orchestration (10,000 operations/day). Billing resources include the professional edition, quota, and value-added package. Your subscription is one month and you manually renew the subscription for another month before the subscription expires. The billing details are as follows:
- The first billing period is from 15:50:04 on June 30, 2024 to 23:59:59 on July 30, 2024.
- The second billing period is from 23:59:59 on July 30, 2024 to 23:59:59 on Aug. 30, 2024.
Figure 1 shows how the price is calculated.
For pay-per-use billing examples, see Billing Example.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot