Credential Leak Response
Playbook Overview
Credential leakage means that the identity authentication information, such as the username, password, API key, and access token, of an individual or organization is obtained or disclosed by an unauthorized third party when the individual or organization uses online services, such as cloud services, social media platforms, and emails. The Credential Leak Response playbook has been associated with the Credential Leak Response workflow. The playbook can be used in the following scenario:
- API key leak scenario: The Credential Leak Response - AccessKey playbook automatically disables the compromised AK/SK.
| Playbook | Trigger Condition |
|---|---|
| Credential Leak Response - AccessKey | This playbook is triggered by an alert. If an alert meets the following three conditions and the playbook is enabled, the playbook will automatically disable the related AK/SK.
|
You need to enable this playbook manually.
Prerequisites
- Your SecMaster professional edition is available.
- You have connected DSC alarm logs to SecMaster and enabled auto alert conversion of DSC logs on the SecMaster console For details, see Enabling Log Access.
Notes and Constraints
- This function applies only to Huawei Cloud account credentials. It is not applicable to credentials in other service systems.
- When this playbook takes effect, it disables the compromised AK/SK. You need to add permissions for SecMaster_Agency (mandatory) and SecMaster_Account_Agency_* (optional) by referring to Creating a SecMaster Agency. SecMaster_Account_Agency_* is the agency required in the multi-account management scenario.
Creating a SecMaster Agency
- Log in to the SecMaster console.
- Click
 in the upper left corner of the page and choose Management & Governance > Identity and Access Management.
in the upper left corner of the page and choose Management & Governance > Identity and Access Management. - Add a custom policy.
- In the navigation pane on the left, choose Permissions > Policies/Roles. In the upper right corner of the displayed page, click Create Custom Policy.
- Configure a policy.
- Policy Name: Enter a policy name.
- Policy View: Select JSON.
- Policy Content: Copy the following content and paste it in the text box.
{ "Version": "1.1", "Statement": [ { "Effect": "Allow", "Action": [ "iam:users:listUsers", "iam:users:updateUser", "iam:credentials:updateCredential" ] } ] }
- Click OK.
- Create an agency.
- In the navigation pane on the left, choose Agencies. On the displayed page, click SecMaster_Agency. The Basic Information tab for SecMaster_Agency is displayed by default. (Optional) In the multi-account management scenario, you also need to add permissions for SecMaster_Account_Agency_*.
- On the Permissions tab, click Authorize.
- On the Select Policy/Role page, search for and select the policy added in 3. Creating a Custom Policy, and click Next.
- Set the authorization scope. Select All resources for Scope. After the configuration is complete, click OK.
Enabling a Playbook
- Log in to the SecMaster console.
- In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. Figure 2 Accessing the Playbooks tab
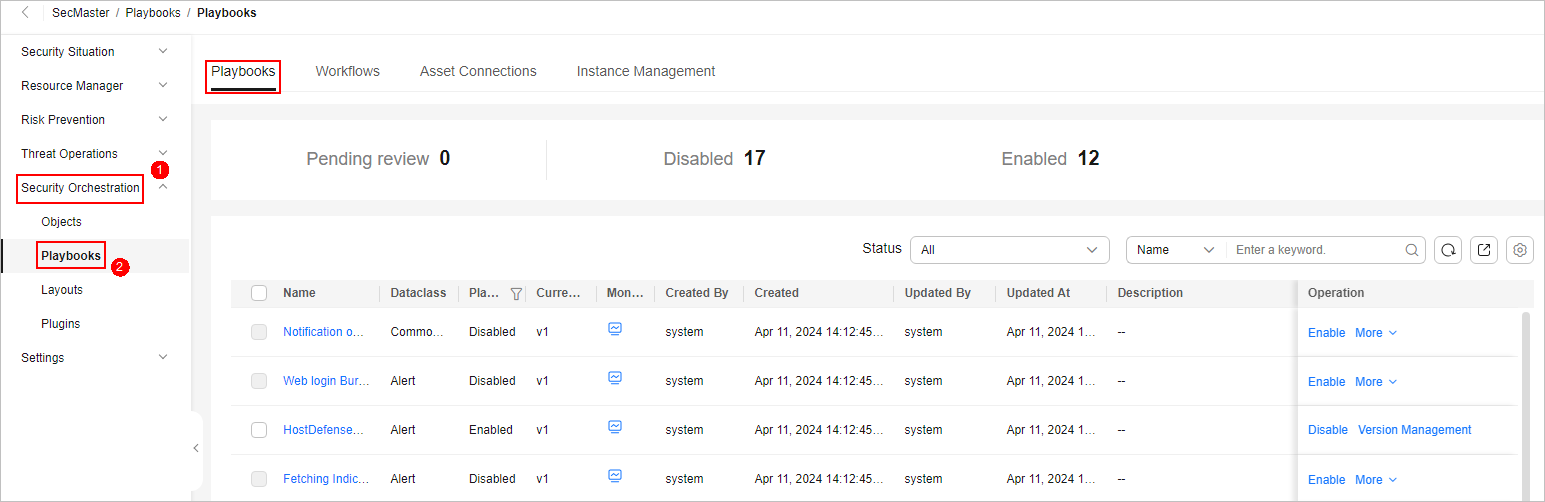
- On the Playbooks page, search for the Credential Leak Response - AccessKey playbook and click Enable in the Operation column of the playbook.
- In the dialog box displayed, select the initial playbook version v1 and click OK. If the Playbook Status of the Credential Leak Response - AccessKey playbook changes to Enabled, the playbook has been enabled successfully.
Implementation Effect
If an alert that meets the conditions is detected and the playbook is enabled, the playbook will automatically disable leaked keys.
The procedure is as follows:
- On the management console, hover the mouse over the username in the upper right corner, and select My Credentials from the drop-down list. The API Credentials page is displayed by default.
- In the navigation pane on the left, choose Access Keys.
- On the Access Keys page, check whether the Status of the key is Disabled. If yes, the key has been disabled.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





