Automatic Handling of High-Risk WAF Alerts (Automatic handling of high-risk WAF Alert)
Playbook Overview
The Automatic handling of high-risk WAF Alert playbook has been associated with the Automatic handling of high-risk WAF Alert workflow. This playbook automatically obtains WAF IP indicators from CloudTIC (Huawei Cloud built-in intelligence center) and performs the following operations on risky IP indicators (The IP indicators whose severity is Black and confidence is greater than 70 are classified as risky):
- Action 1: WAF automatically blocks the source IP addresses that match IP indicators in SecMaster.
- Action 2: The playbook checks whether SecMaster has recorded the IP indicator. If not, the playbook adds a new indicator to SecMaster. The indicator source is CloudTIC (Huawei Cloud built-in intelligence center).
- Action 3: The Automatic handling of high-risk WAF Alert playbook automatically associates IP indicators with the alerts that trigger it and adds the indicator information to alert comments.
If the severity of an indicator is White or its confidence is less than 30, the indicator is classified as low-risk. For low-risk IP indicators, the playbook performs the following operations:
- Action 1: The Automatic handling of high-risk WAF Alert playbook automatically closes WAF alerts that trigger the playbook on SecMaster.
- Action 2: The playbook checks whether SecMaster has recorded the IP indicator. If not, the playbook adds a new indicator to SecMaster. The indicator source is CloudTIC (Huawei Cloud built-in intelligence center).
- Action 3: The playbook associates alerts that trigger the Automatic handling of high-risk WAF Alert playbook with IP indicators and add them to alert comments.
Playbook trigger conditions:
- Condition 1: The alert severity is High or Critical.
- Condition 2: The Alert Name contains [Application], indicating that the alert is a WAF alert generated by the system built-in model.
You need to enable this playbook manually.
Prerequisites
- You have enabled access to WAF attack logs in the workspace in SecMaster. For details, see Enabling Log Access.
- Your SecMaster professional edition is available.
- You have used the built-in model templates Application - WAF Key Attack Alert, Application_SuspectedF5BIG-IPCommandExecutionVulnerability, and Application_SpringActorinformationleakagepresent to create models and enabled the models. For details, see Creating an Alert Model Using a Built-in Model Template.
Creating an Alert Model Using a Built-in Model Template
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose and select the Model Templates tab. Figure 2 Model Templates tab

- In the model template list, click Details in the Operation column of the target model template. The template details page is displayed on the right. The following uses the Application - WAF Key Attack Alert template as an example.
- On the model template details page, click Create Model in the lower right corner. The page for creating an alert model is displayed.
- On the Create Alert Model page, configure basic information about the model. If you use a built-in model template to create a model, you are advised to retain the default settings.
Table 1 Basic parameters of an alert model Parameter
Description
Pipeline Name
Name of the data table from which the model data comes.
If you use a built-in model template to create a model, retain the default settings.
Model Name
Name of the custom alert model.
If you use a built-in model template to create a model, retain the default settings.
Severity
Severity of alerts reported by the alert model. If you use a built-in model template to create a model, retain the default settings.
- Critical: A critical alert indicates that the system is severely attacked, which may cause data loss, system breakdown, or long service interruption. For example, such alerts are generated if ransomware encryption behaviors or malware is detected. You need to handle them immediately to avoid severe system damage.
- High: A high-risk alert indicates that the system may be under an attack that has not caused serious damage. For example, such alerts are generated if unauthorized login attempts are detected or unsafe commands (for deleting critical system files or modifying system settings) are executed. You need to investigate and take measures in a timely manner to prevent attacks from spreading.
- Medium: A medium-risk alert indicates that the system has potential security threats, but there are no obvious signs of being attacked. For example, if abnormal modifications of a file or directory are detected, there may be potential attack paths or configuration errors in the system. You need to further analyze and take proper preventive measures to enhance system security.
- Low: A low-risk alert indicates that a minor security threat exists in the system but does not have significant impact on your system. For example, such alerts are generated if port scans are detected, indicating that there may be attackers trying to find system vulnerabilities. These alerts do not require immediate emergency measures. If you have high requirements for asset security, you should also pay attention to alerts at this level.
- Informational: A potential error exists and may affect services. If you have high requirements for asset security, you should also pay attention to alerts at this level.
Alert Type
Alert type displayed after the alert model is triggered.
If you use a built-in model template to create a model, retain the default settings.
Model Type
The default value is Rule model. It cannot be edited or modified.
The threat model created using query rules and trigger conditions is a rule model. For details about the query rules and trigger conditions, see Configuring Model Logic.
Description
Description of the alert model.
If you use a built-in model template to create a model, retain the default settings.
Status
The alert model status. You can change the alert model status after the model is configured.
- If the Enable button is enabled, the alert model is enabled. When the model rules are met, it can generate alerts.
- If the Enable button is disabled, the alert model is disabled.
- Click Next in the lower right corner of the page. The page for configuring the model logic is displayed.
- Configure the model logic. For details about the parameters, see the following table. If you use a built-in model template to create a model, you are advised to retain the default settings.
Table 2 Configuring model logic Parameter
Description
Query Rule
Configure alert query rules. After the setting is complete, click Run and view the running result. If you use a built-in model template to create a model, retain the default settings.
A query analysis statement consists of a query statement and an analysis statement. The format is Query Statement|Analysis Statement. For details about the syntax of query analysis statements, see Overview.NOTE:If the reserved field is of the text type, MATCH_QUERY is used for word segmentation queries by default.
Query Plan
Configure an alert query plan. If you use a built-in model template to create a model, retain the default settings.
- Query Interval: Set it to xx min/hour/day.
If you select min, set this parameter to a value ranging from 5 to 59 minutes. If you select hour, set this parameter to a value ranging from 1 to 23 hours. If you select day, set this parameter to a value ranging from 1 to 14 days.
- Time Window: Set it to xx min/hour/day.
If the time window is by minute, the value ranges from 5 minutes to 59 minutes. If the time window is by hour, the value ranges from 1 hour to 23 hours. If the time window is by day, the value ranges from 1 day to 14 days.
- Execution Delay: Set it to xx min. The value ranges from 0 to 5 minutes.
Advanced Alarm Settings
If you use a built-in model template to create a model, retain the default settings.
- Custom Information: Customize extended alert information.
Click Add, and set the Key and Value information.
- Alarm Details: Enter the alarm name, description, and handling suggestions.
Trigger Condition
Set alert triggering conditions. If you use a built-in model template to create a model, retain the default settings.
The value can be greater than, equal to, not equal to, or less than xx hour.
If there are multiple trigger conditions, click Add and add them. A maximum of five trigger conditions can be added.
If there are multiple trigger conditions, SecMaster scans log data to hit each trigger condition from top to bottom and generates all types of alerts for hit trigger conditions.
Alarm Trigger
The way to trigger alerts for queried results. If you use a built-in model template to create a model, retain the default settings.
The options are as follows:
- One alarm for all query results
- One alarm for each query result
Debugging
Set whether to generate debugging alarms. If you use a built-in model template to create a model, retain the default settings.
If the alarms generated by the alarm model are used only for model debugging, you are advised to enable this function.
- If Generate debugging alarms is enabled, the value of simulation in the alarm generated by the alarm model is true, indicating that the alarm is a debugging alarm.
- If Generate debugging alarms is disabled, the value of simulation in the alarm generated by the alarm model is false.
Suppression
Whether to stop the query after an alarm is generated. If you use a built-in model template to create a model, retain the default settings.
- If Suppression is enabled, the query stops after an alert is generated.
- If Suppression is disabled, the query is not stopped after an alert is generated.
- Query Interval: Set it to xx min/hour/day.
- Complete all settings and click Next in the lower right corner of the page.
- Review all settings and click OK in the lower right corner of the page.
- After the configuration is complete, return to the page, click the Available Models tab, and view the new alert model. If the Status of the new alert model is Enabled, the alert model has been successfully added and enabled. Figure 3 Viewing the status of the Application - WAF Key Attack Alert model

Enabling the Automatic Handling of High-Risk WAF Alerts Playbook
The initial version (V1) of the Automatic handling of high-risk WAF Alert playbook is activated by default. You only need to enable the playbook.
- Log in to the SecMaster console.
- In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 4 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. Figure 5 Accessing the Playbooks tab
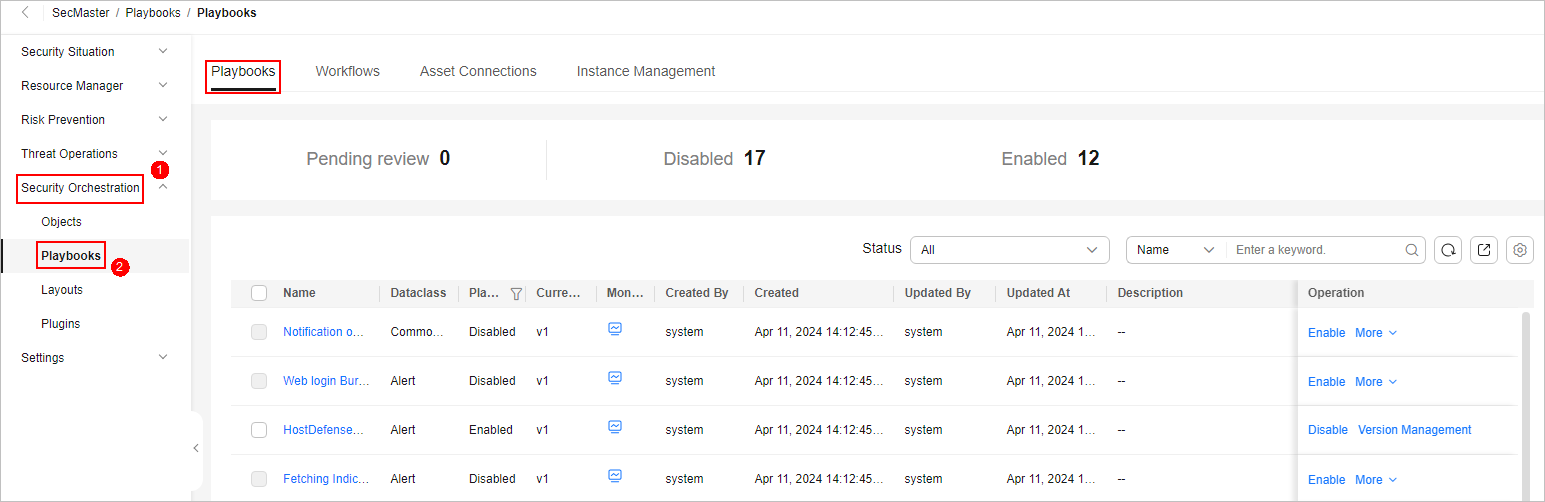
- On the Playbooks page, locate the row that contains the Automatic handling of high-risk WAF Alert playbook and click Enable in the Operation column.
- In the dialog box displayed, select the initial playbook version v1 and click OK.
- After the playbook is enabled, check whether the playbook status changes to Enabled on the Playbooks page. If yes, the operation is successful.
Implementation Effect
If an IP indicator Threat Level is Black and its Severity is greater than 70 points, it is a risky IP indicator. The following shows how this playbook automatically handles a risky IP indicator.
- Action 1: WAF automatically blocks the source IP addresses that match IP indicators in SecMaster.
- You can view the IP address group automatically created by WAF on the page in WAF.
Figure 6 Viewing the new IP address group in WAF Figure 7 Viewing details about the new IP address group in WAF
Figure 7 Viewing details about the new IP address group in WAF
- Action 2: The playbook checks whether SecMaster has recorded the IP indicator. If not, the playbook adds a new indicator to SecMaster. The indicator source is CloudTIC (Huawei Cloud built-in intelligence center).
- Log in to the SecMaster console.
- In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 8 Workspace management page

- On the displayed page, view the IP indicator added by the playbook. Figure 9 Indicator details page

- Action 3: The playbook associates alerts that trigger the Automatic handling of high-risk WAF Alert playbook with IP indicators and add them to alert comments.
- Log in to the SecMaster console.
- In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 10 Workspace management page

- On the Alerts page, click the alert name to go to the alert details page. You can view the indicators automatically associated by the system in the alert comments. Figure 11 Alert details page

Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





