Real-time Notification of Critical Organization and Management Operations
Playbook Overview
This built-in playbook can notify you of key O&M operations by email in real time.
The Real-time notification of critical Organization and Management operations playbook has matched the Real-time notification of critical Organization and Management operations workflow. This workflow uses Simple Message Notification (SMN) to send notifications. So you need to create and subscribe to a notification topic in SMN.
You need to enable this playbook manually.
Prerequisites
- You have enabled access to CTS logs on the page in the workspace in SecMaster. For details, see Enabling Log Access.
- The corresponding O&M defense model has been enabled. For details, see Step 2: Enable the Alert Model.
- SecMaster has obtained the SMN FullAccess permission, which specifies all permissions of SMN.
Table 1 Description Permission
Description
Principal
Usage
SMN FullAccess
All permissions for SMN.
SecMaster_Agency
SecMaster uses SMN to send playbook execution notifications.
Perform the following steps to check whether SecMaster has obtained the SMN FullAccess permission: If the permission is not allocated, allocate it to SecMaster by referring to Authorizing SecMaster.
- Log in to the SecMaster console as an administrator.
- Click
 in the upper left corner of the page and choose Management & Governance > Identity and Access Management.
in the upper left corner of the page and choose Management & Governance > Identity and Access Management. - In the navigation pane on the left, choose Agencies. On the Agencies page, click SecMaster_Agency and then click the Permissions tab to view all authorization records of SecMaster_Agency.
Figure 1 Viewing Agency Authorization Records
Step 1: Create and Subscribe to a Topic
- Log in to the SecMaster console.
- In the upper left corner of the page, click
 and choose .
and choose . - Create a topic.
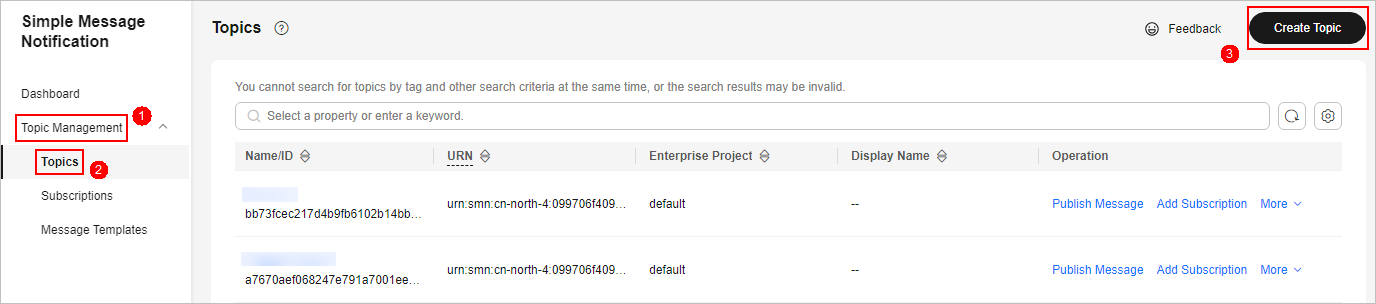
- In the navigation pane on the left, choose . In the upper right corner of the displayed page, click Create Topic. Figure 2 Create Topic
- In the Create Topic dialog box displayed, configure topic information and click OK.
- Topic Name: Set it to SecMaster-Notification.
- Display Name: SecMaster notification topic is recommended.
- Retain the default settings for other parameters.

Topic Name must be set to SecMaster-Notification, or playbooks may fail to be executed.
- In the navigation pane on the left, choose . In the upper right corner of the displayed page, click Create Topic.
- Add a subscription.
- On the Topics page, locate the row that contains the SecMaster-Notification topic and click Add Subscription in the Operation column.
- On the displayed Add Subscription slide-out panel, configure subscription information and click OK.
- Protocol: Select Email.
- Endpoint: Enter the email address of the subscription endpoint, for example, username@example.com.
- Confirm the subscription.
After a subscription is added, a confirmation email will be sent to the email address set in 4. Click the subscription confirmation link in the email. A page for a successful subscription will be displayed.
Step 2: Enable the Alert Model
Before using the Real-time notification of critical Organization and Management operations playbook, you need to enable some alert models, including the ones for O&M - Attaching NICs, O&M - Creating VPC peering connections, and O&M - Binding EIPs to resources.
- Click
 in the upper left corner of the page and choose Security & Compliance > SecMaster.
in the upper left corner of the page and choose Security & Compliance > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 3 Workspace management page

- In the navigation pane on the left, choose and select the Model Templates tab. Figure 4 Model Templates tab

- In the model template list, click Details in the Operation column of the target model template. The template details page is displayed on the right.
- On the details page, click Create Model in the lower right corner. The page for creating an alert model is displayed.
- On the Create Threat Model page, configure basic information about the model.
- Pipeline Name: Select an execution pipeline for the alert model.
Table 2 Available pipelines Alert Template
Execution Pipeline
O&M - Attaching a NIC
sec-cts-audit
O&M - Creating a VPC peering connection
O&M - Binding EIPs to resources
- Retain default values for other parameters.
- Pipeline Name: Select an execution pipeline for the alert model.
- After the setting is complete, click Next in the lower right corner of the page. The page for setting the model logic is displayed.
- Set the model logic. You are advised to retain the default settings.
- Complete all settings and click Next in the lower right corner of the page.
- Review all settings and click OK in the lower right corner of the page.
- Repeat 4 to 10 to create alert models with other templates.
- In the navigation pane on the left, choose . Figure 5 Available Models

- To enable models in batches, select all models you want to enable and click Enable in the upper left corner of the list.
If the model status changes to Enable, the model is successfully started.
Step 3: Configure and Enable the Playbook
- In the navigation pane on the left, choose Security Orchestration > Playbooks. Figure 6 Accessing the Playbooks tab
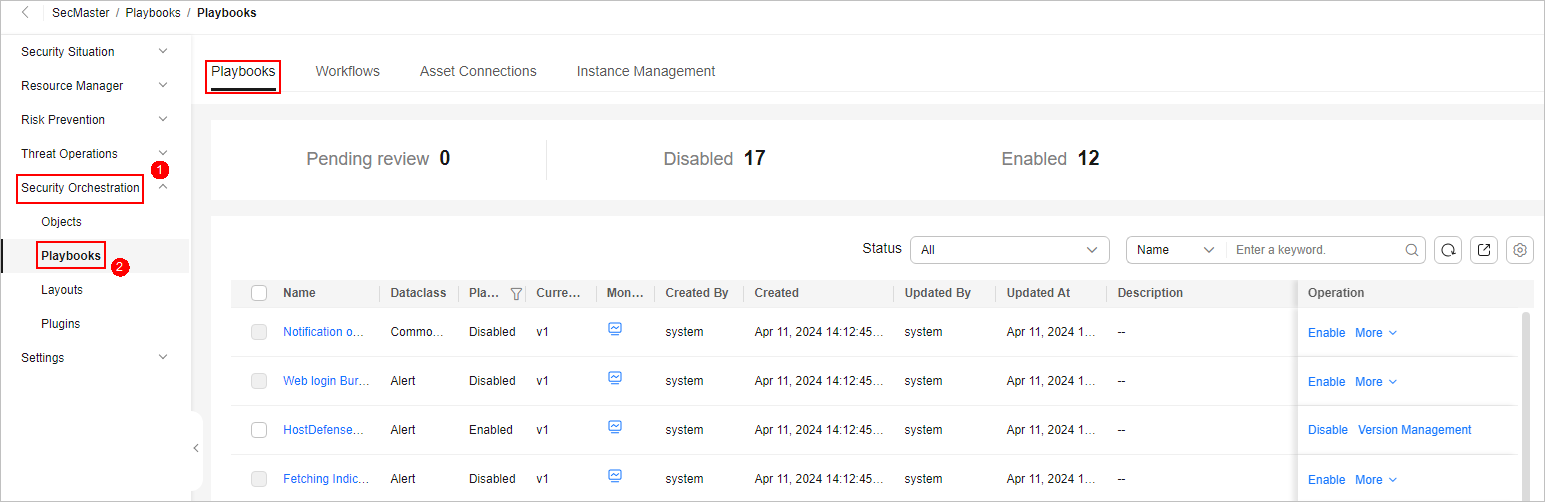
- On the Playbooks page, locate the row that contains the Real-time notification of critical Organization and Management operations playbook and click Enable in the Operation column.
- In the dialog box displayed, select the initial playbook version v1 and click OK.
Implementation Effect
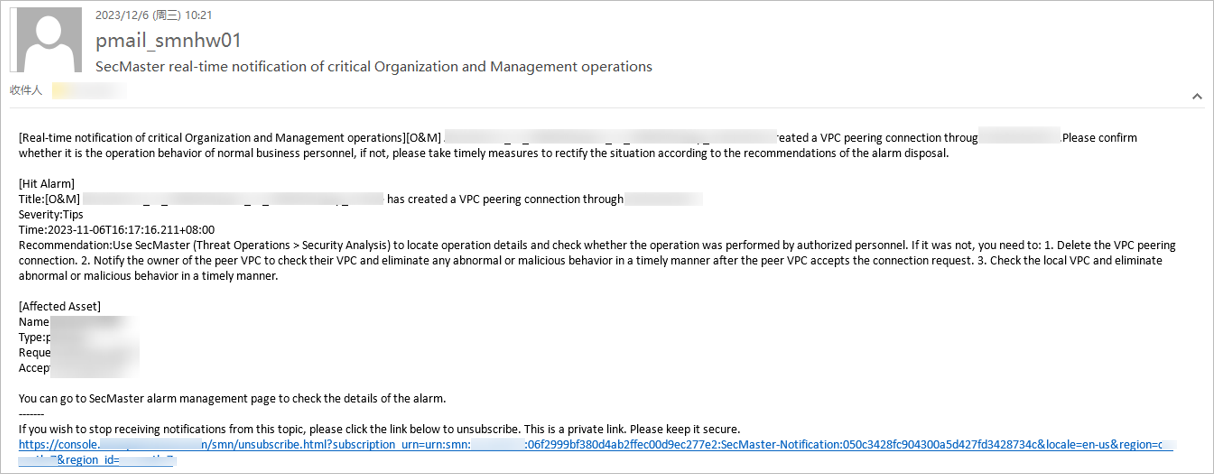
When a key O&M operation is performed, this playbook is triggered. The playbook will send an email notification as configured. The following is an example.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





