Authorizing SecMaster
Scenarios
SecMaster depends on some other cloud services. To better use SecMaster, you can authorize SecMaster to perform some operations on some cloud services on your behalf. For example, you can allow SecMaster to execute scheduling tasks and manage resources.
Your authorization is required first time you try to use SecMaster. The following table lists the permissions you need to assign to SecMaster.
| Permission | Description | Assign To | When to Use |
|---|---|---|---|
| ECS FullAccess | All permissions for ECS | SecMaster_Agency |
|
| WAF FullAccess | Web Application Firewall (WAF) administrator | SecMaster_Agency |
|
| SecMaster FullAccess | SecMaster administrator | SecMaster_Agency | Used to perform operations such as alert handling. |
| HSS FullAccess | Full permissions for HSS | SecMaster_Agency |
|
| EPS ReadOnlyAccess | Read-only permissions for EPS. | SecMaster_Agency |
|
| Anti-DDoS ReadOnlyAccess | Read-only permissions for Anti-DDoS. | SecMaster_Agency |
|
| IAM ReadOnlyAccess | Read-only permissions for IAM. | SecMaster_Agency | Used to obtain IAM usernames for executing playbook workflows of batch blocking or unblocking IAM users. |
| WAF Administrator | WAF administrator, who has all permissions for WAF. | SecMaster_Agency |
|
| SMN FullAccess | All permissions for SMN. | SecMaster_Agency | Used to execute playbook workflows related to notifications, for example, the "Automatic Notification of High-Risk Alerts" workflow. |
| RDS ReadOnlyAccess | Read-only permissions for RDS | SecMaster_Agency |
|
| EIP ReadOnlyAccess | Read-only permissions for EIP | SecMaster_Agency |
|
| Tenant Guest | Read-only permissions for all cloud services except IAM | SecMaster_Agency | Used to query resource information of cloud services except IAM in the baseline check scenario. |
| NAT ReadOnlyAccess | Read-only permissions for NAT Gateway. | SecMaster_Agency | Used to obtain asset information in NAT Gateway for asset information synchronization in the asset management scenario. |
| VPC FullAccess | All permissions for VPC. | SecMaster_Agency |
|
| OBS OperateAccess | Permissions for basic OBS operations, such as viewing the bucket list, obtaining bucket metadata, listing objects in a bucket, querying bucket location, uploading objects, obtaining objects, deleting objects, and obtaining an object ACL. | SecMaster_Agency | Used to query, upload, and download objects when the OBS plug-in is used. |
| ELB ReadOnlyAccess | Read-only permissions for ELB. | SecMaster_Agency |
|
| CFW FullAccess | All permissions for CFW. | SecMaster_Agency |
|
Prerequisites
- The IAM account has been authorized. For details, see How Do I Grant Permissions to an IAM User?
- You have purchased SecMaster.
Authorizing SecMaster
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
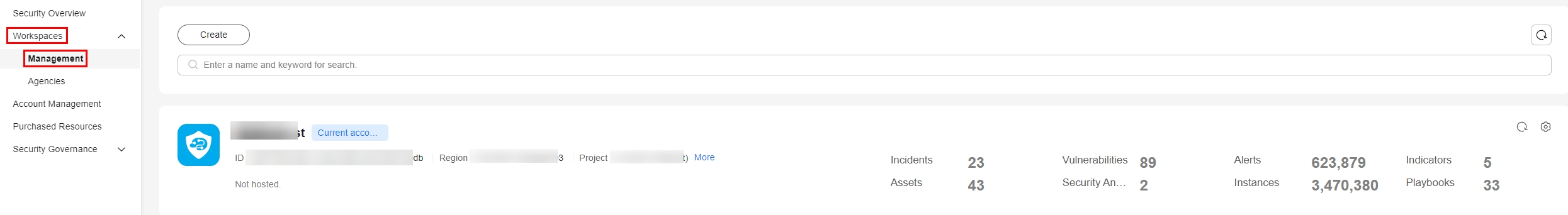
in the upper left corner of the management console and select a region or project. - In the navigation pane on the left, choose Workspaces > Management. Figure 1 Workspaces > Management
- (Optional) In the upper part of the workspace management page, click Entrusted Service Authorization - Current Tenant.
The service authorization page is automatically displayed the first time you log in.
- On the page for assigning permissions, select all required permissions (which are selected by default), select Agree to authorize, and click Confirm.
Authorization by Organization
SecMaster allows you to grant permissions to an organization in just a few clicks. After the permissions are granted, all users in the organization can use the SecMaster service.
- What is the Organizations service?
The Organizations service helps you govern multiple accounts within your organization. It enables you to consolidate multiple accounts into a created organization so that you can centrally manage these accounts. You can use Organizations to apply access policies to different accounts in your organization. This helps you better meet the security and compliance requirements of your business. Before you start, make sure you understand Basic Concepts of Organizations.
- Main functions of the Organizations service
The Organizations service provides the following functions:
- Centralized management of enterprise accounts: An enterprise can invite multiple accounts to join an organization and group the accounts by level based on the management or working structure of the enterprise.
- Centralized control of actions that each account can perform: The administrator of an organization can use service control policies (SCPs) to limit the permissions that can be assigned to an organization or the OUs in an organization. In the SCPs, you can limit which cloud services and APIs the member accounts in the organization can access.
- Integration with other Huawei Cloud services: The Organizations service integrates with other Huawei Cloud services (trusted services) to enable users to perform organization-wide operations.
Prerequisites
An organization has been created, and an account has been invited to join the organization. For details, see Creating an Organization and Inviting an Account to Join Your Organization.
Constraints and Limitations
Only the organization administrator and delegated administrators can manage permissions by organization.
An organization administrator is an account used to create an organization. An organization has only one organization administrator.
For more information about delegated administrators, see Delegated Administrator.
Procedure
- Log in to the SecMaster console.
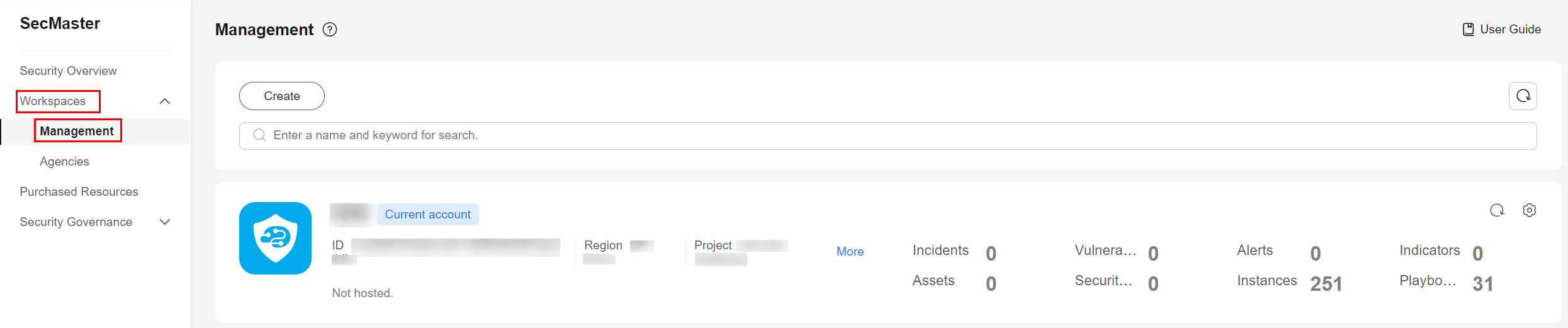
- In the navigation pane on the left, choose Workspaces > Management. Figure 2 Accessing the Workspaces page
- On the workspace management page, click Service Authorization - Organization next to .
- On the displayed Service Authorization - Organization pane, select the organizations to be authorized and select Agree to authorize.
- Click Confirm.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





