Binding a Key Pair and Logging In to an ECS Using a Private Key
A key pair, including one public key and one private key, are generated based on a cryptographic algorithm. The public key is automatically saved in Key Pair Service (KPS), while the private key can be saved to the user's local host. If you have configured the public key in a Linux ECS, you can use the private key to log in to the ECS for better security.
This section describes how to bind a key pair and log in to an ECS using a private key.
Procedure
The following uses an SSH_RSA_2048 key pair as an example to describe how to create a key pair and use the key to log in to an ECS. The following figure shows the process.
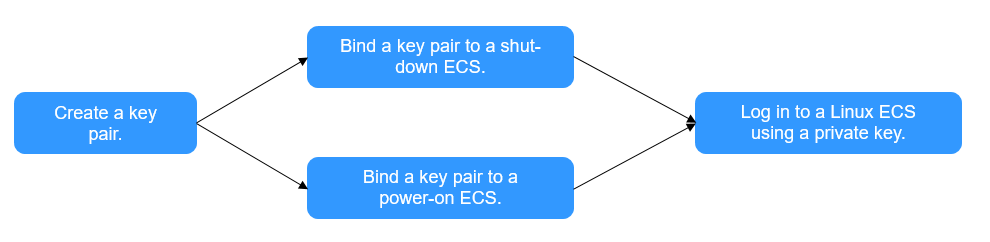
| Procedure | Description |
|---|---|
| Register a Huawei ID, enable Huawei Cloud services, top up the account, and grant KPS permissions to the account. | |
| Create a key pair and select the key pair type. | |
| Bind a key pair to the ECS. | |
| After the key pair is bound, use the private key to log in to the ECS. |
Preparations
- Before creating key pair, register a Huawei Cloud account and enable Huawei Cloud services. For details, see Signing Up for a HUAWEI ID and Enabling Huawei Cloud Services.
If you have enabled Huawei Cloud, skip this step.
- An ECS has been created. For details, see Purchasing an ECS in Custom Config Mode.
The SSH port (22 by default) of the ECS security group must allow traffic from the 100.125.0.0/16 CIDR block in advance. For details about ports and CIDR blocks, see Enhancing Security for SSH Logins to Linux ECSs.
- The KPS permission has been granted to the account. For details, see Creating a User and Authorizing the User the Permission to Access DEW.
Table 1 KPS system policies Role/Policy Name
Description
Type
Dependency
DEW KeypairFullAccess
Full permissions for KPS in DEW. Users with these permissions can perform all the operations allowed by policies.
System-defined policy
None
DEW KeypairReadOnlyAccess
Viewing permissions for KPS in DEW. Users with this permission can only view KPS data.
System-defined policy
None
Step 1: Creating a Key Pair
- Log in to the DEW console.
- In the navigation pane on the left, choose Key Pair Service.
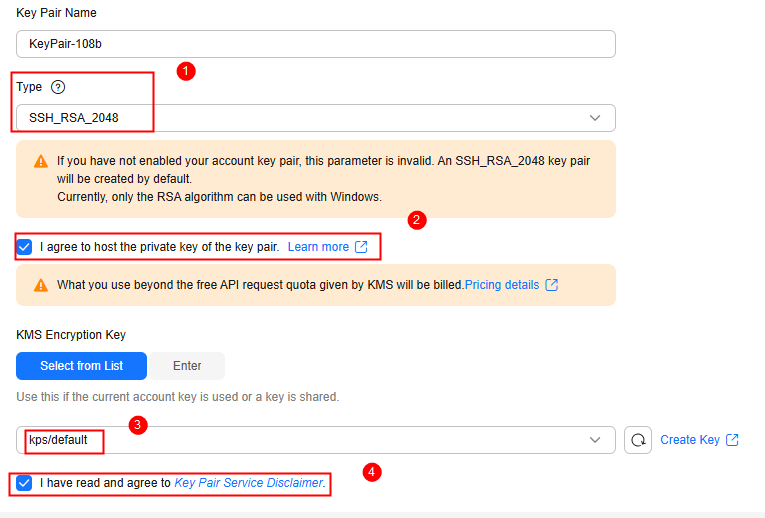
- In the Private Key Pairs tab, click Create Key Pair, and configure the parameters as shown in Figure 2. For details about the parameters, see Table 2.
Table 2 Parameters for creating a private key pair Parameter
Example Value
Description
Type
SSH_RSA_2048
Signature algorithm of the SSH key pair. RSA, ECDSA, and EdDSA are supported.
KMS Encryption Key
NOTE:Select I agree to host the private key of the key pair and select an encryption key.
kps/default
KMS supports the following encryption modes:- Select from List: Select this if you want to use the key used or shared by the current account. Select the default key kps/default or a custom key created on KMS.
- Enter: Enter the ID of the authorized key. Enter an encryption key if an authorized key is used. Only symmetric algorithm key IDs are supported. Do not enter an asymmetric key ID.
- Select I have read and agree to Key Pair Service Disclaimer and click OK. The private key file will be automatically downloaded. You need to save the file as prompted.
Step 2: Binding a Key Pair to an ECS
After a key pair is bound to an ECS, you can use the private key to log in to the ECS.
- In the navigation pane on the left, choose Key Pair Service. On the displayed page, click the ECS List tab.
- Locate the target shut-down ECS and click Bind in the Operation column.
- On the displayed page, select a key pair. Then, select Disable the password login mode and I have read and agree to Key Pair Service Disclaimer. Figure 3 Binding a key pair to a shut-down ECS
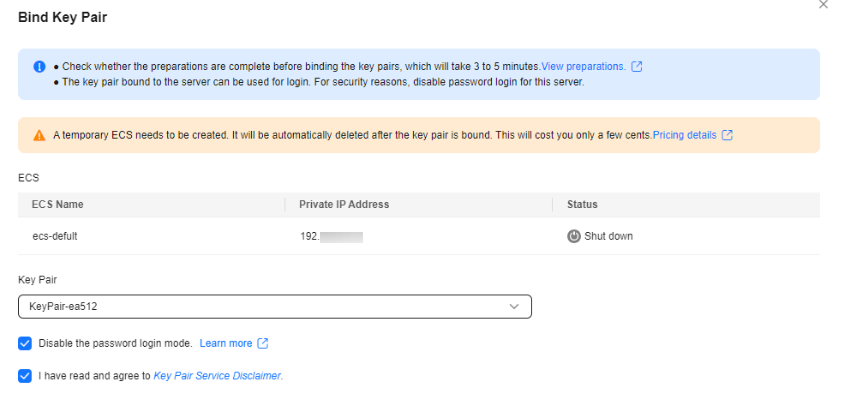
- Click OK.
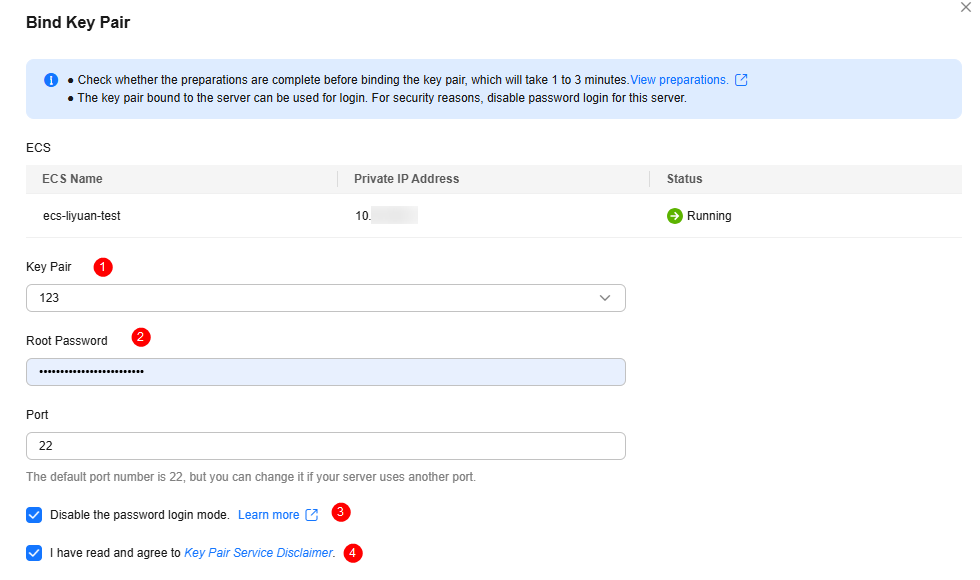
- In the navigation pane on the left, choose Key Pair Service. On the displayed page, click the ECS List tab.
- Locate the target running ECS and click Bind in the Operation column.
- On the displayed page, configure the parameters as shown in Figure 4.
- Set New Key Pair and Root Password.
- The default port is 22.
- Select Disable the password login mode and I have read and agree to Key Pair Service Disclaimer.
- Click OK.
Step 3: Logging in to an ECS Using a Private Key
- Check whether the private key file has been converted to .ppk format.
- If yes, log in to the ECS server.
- If no, perform the following operations to convert the format of the private key file and then log in to ECS.
Open the third-party PuTTY, import the .pem private key file, and export the converted .ppk private key file.
Figure 5 Converting the format of the private key file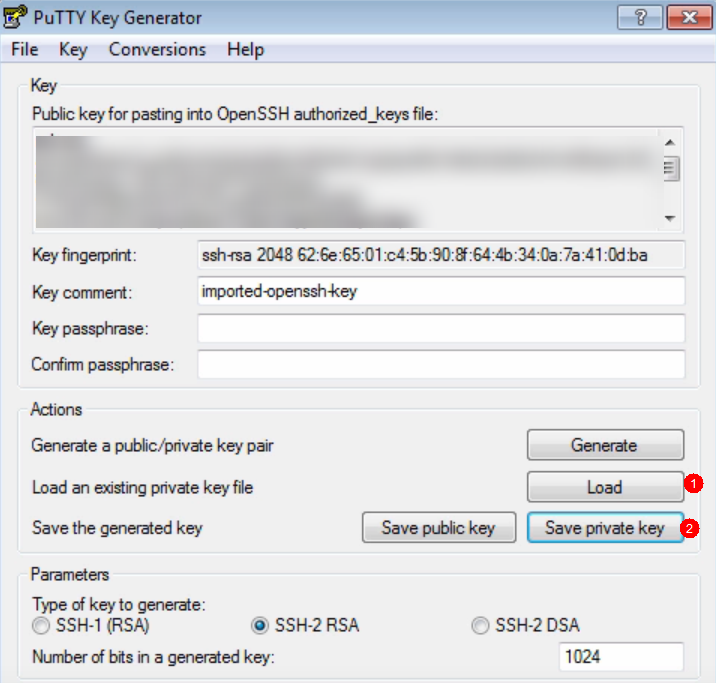
- Use PuTTY to log in to the ECS.
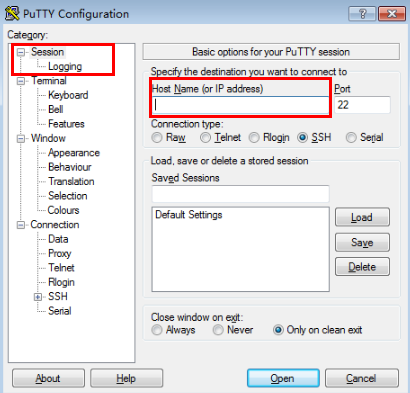
- Enter the IP address of the ECS. Port 22 is used by default. Figure 6 IP address of ECS
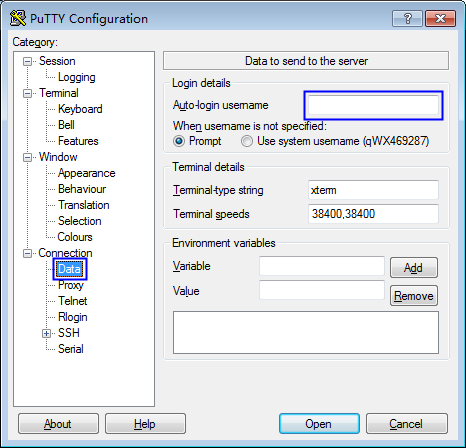
- Enter the username of the ECS image. Figure 7 Username
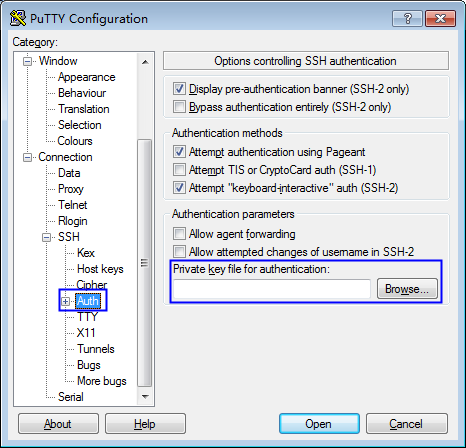
- Upload the private key file in .ppk format. Figure 8 Uploading the private key file
- Click Open.
- Enter the IP address of the ECS. Port 22 is used by default.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot