Using CSMS to Prevent AK/SK Leakage
CSMS allows you to manage secrets throughout their lifecycle to prevent information leakage. You can configure an agency for ECS on IAM to obtain the temporary AK, there by protecting AKs/SKs. Temporary AKs feature shorter validity periods, frequent updates, and higher security. The following describes how to create an agency, configure policies, authorize permissions, assign permissions to ECSs, and access CSMS through APIs. ECS can automatically rotate temporary secrets.
Scenario
Application secrets are stored and can be accessed temporarily to prevent AK/SK leakage.
How It Works
You can configure an agency for elastic cloud server (ECS) on Identity and Access Management (IAM) to obtain the temporary access key (AK), thereby protecting the AK and secret key (SK).
Access secrets can be classified into permanent secrets and temporary secrets based on their validity periods. Permanent access secrets include usernames and passwords. Temporary access keys have a shorter validity period, are updated frequently, thus are more secure. You can assign an IAM agency to an ECS instance, so that applications in the ECS instance can use the temporary AK, SK, and security token to access CSMS. The temporary access keys are dynamically obtained every time they are required. They can also be cached in the memory and updated periodically.
Process Flow

Constraint
Only the administrator or an IAM user with the ECS permission can configure an agency for an ECS instance.
Procedure
- Create an ECS agency on IAM.
- Log in to the DEW console.
- Click
 on the left of the page and choose Management & Governance > Identity and Access Management.
on the left of the page and choose Management & Governance > Identity and Access Management. - In the navigation pane on the left, choose Agencies.
- Click Create Agency in the upper right corner.
- Configure the parameters on the displayed page. For details about the parameters, see Table 1. Figure 2 Creating an agency
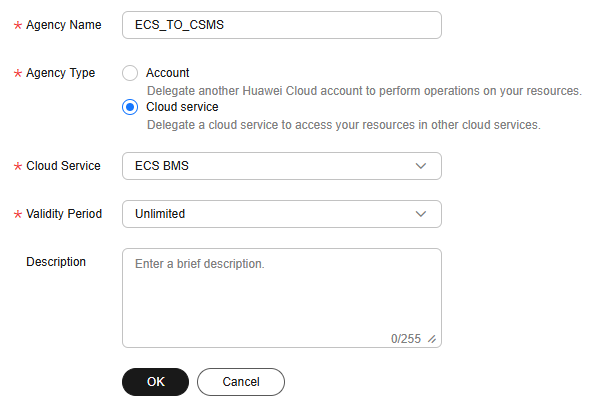
Table 1 Agency parameters Parameter Name
Description
Agency Name
Enter an agency name, for example, ECS_TO_CSMS.
Agency Type
Select Cloud service.
Cloud Service
Select ECS BMS.
Validity Period
Select a duration. The value can be Unlimited, 1 day, or Custom.
Description
(Optional) Enter agency description.
- Click OK. In the displayed dialog box, click Authorize.
- Click Create Policy in the upper right corner. If you already have a policy, skip this step.
- Configure policy parameters. For details about the parameters, see Table 2. Figure 3 Creating a policy

Table 2 Policy parameters Parameter Name
Description
Policy Name
Enter a policy name.
Policy View
Select Visual editor.
Policy Content
- Allow: Select Allow.
- Select service: Select Cloud Secret Management Service (CSMS). NOTE:
- If only the CSMS service permission is added, the KMS API may fail to be called.
- You need to add policies for services one by one. After the policies are configured for a service, click Add Permissions to add policies for other services.
- Select action: Select read and write permissions as required.
- (Optional) Select resource: Select the scope of resources.
- Specific: Access specific secrets. NOTE:
You can select Specify resource path, and then click Add Resource Path to specify an accessible secret.
- All: Access all secrets.
- Specific: Access specific secrets.
- (Optional) Add request condition: Click Add Request Condition, select a condition key and an operator, and enter values as required.
Description
(Optional) Enter policy description.
- Configure policy parameters. For details about the parameters, see Table 2.
- Click Next and select a policy for the agency. Click Next.
- Select an authorization scope. You are advised to select All resources.
- All resources: IAM users will be able to use all resources, including those in enterprise projects, region-specific projects, and global services under your account based on assigned permissions.
- Enterprise projects: The selected permissions will be applied to resources in the enterprise projects you select.
- Region-specific projects: The selected permissions will be applied to resources in the region-specific projects you select.
Figure 4 Selecting a scope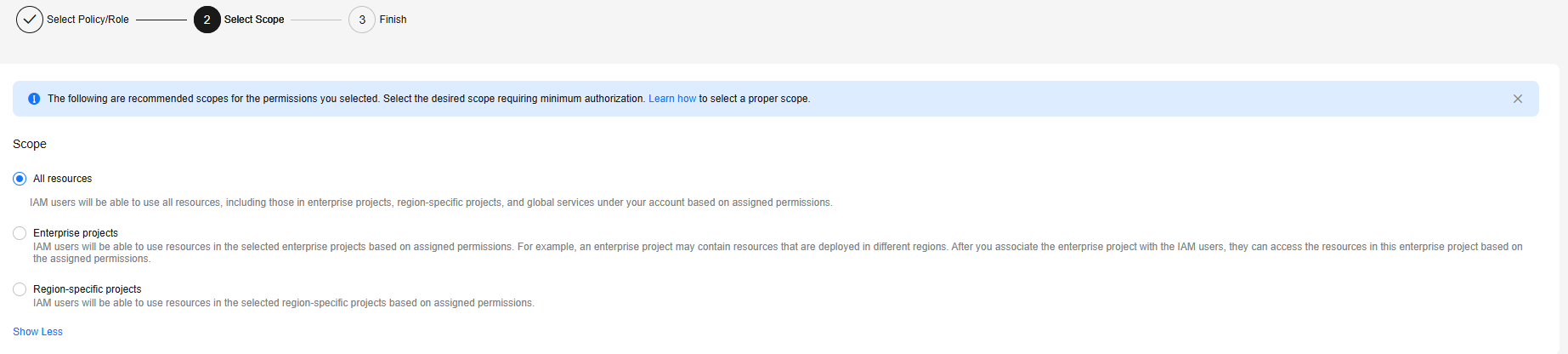
- Click OK. Confirm the information and click Finish.
- Assign an agency (for example, ECS_TO_CSMS) to an ECS instance.
- If no ECS has been created, create an agency, for example, ECS_TO_CSMS for Agency under Advanced Settings. For details, see Purchasing a Custom ECS.
- To use an existing ECS instance, perform the following steps:
- Click
 on the left and choose .
on the left and choose . - Click the name of an ECS instance to go to the Summary page.
- In the Management Information area, click
 and select an agency (for example, ECS_TO_CSMS). Figure 5 Selecting an agency
and select an agency (for example, ECS_TO_CSMS). Figure 5 Selecting an agency
- Click
- In an application running on the ECS instance, call an API to obtain the temporary agency secrets, including the temporary AK, SK, and security token, to access CSMS.
- Obtain the temporary AK and SK (in the Security Key directory). For details, see Obtaining Metadata.
- URI
- Method
- The following data is returned:
{ "credential":{ "access": "LDHZK30XXXXXXXXXXXXV", "secret":"gyqcdzVXXXXXXXXXXXXXXXXXXXXXXXMl6", "securitytoken": "El9FI2C65qXXXXXXXXXXXXXXXXXXXXXnkcaoV", "expires_at": "2022-07-14T12:09:24.147000Z" } }
- Extract the values of access, secret, and securitytoken to access CSMS.
- ECS automatically rotates temporary secrets to ensure that they are secure and valid.
- Use the temporary AK/SK and security token to access CSMS.
package com.huaweicloud.sdk.test; import com.huaweicloud.sdk.core.auth.ICredential; import com.huaweicloud.sdk.core.auth.BasicCredentials; import com.huaweicloud.sdk.core.exception.ConnectionException; import com.huaweicloud.sdk.core.exception.RequestTimeoutException; import com.huaweicloud.sdk.core.exception.ServiceResponseException; import com.huaweicloud.sdk.csms.v1.region.CsmsRegion; import com.huaweicloud.sdk.csms.v1.*; import com.huaweicloud.sdk.csms.v1.model.*; public class ListSecretsSolution { public static void main(String[] args) { String ak = "<access>"; String sk = "<secret>"; String securitytoken = "<securitytoken>"; ICredential auth = new BasicCredentials() .withAk(ak) .withSk(sk) .withSecurityToken(securitytoken); CsmsClient client = CsmsClient.newBuilder() .withCredential(auth) .withRegion(CsmsRegion.valueOf("cn-north-1")) .build(); ListSecretsRequest request = new ListSecretsRequest(); try { ListSecretsResponse response = client.listSecrets(request); System.out.println(response.toString()); } catch (ConnectionException e) { e.getMessage(); } catch (RequestTimeoutException e) { e.getMessage(); } catch (ServiceResponseException e) { e.getMessage(); System.out.println(e.getHttpStatusCode()); System.out.println(e.getErrorCode()); System.out.println(e.getErrorMsg()); } } }
- Obtain the temporary AK and SK (in the Security Key directory). For details, see Obtaining Metadata.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





