Managing Workflows
Scenario
This section describes how to manage workflows, including Viewing Workflows, Exporting Workflows, Deleting Workflows, and Disabling a Workflow.
Viewing Workflows
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 1 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. On the displayed page, select the Workflows tab.
Figure 2 Workflows tab

- On the Workflows page, view details about the created workflow.
Figure 3 Viewing workflows
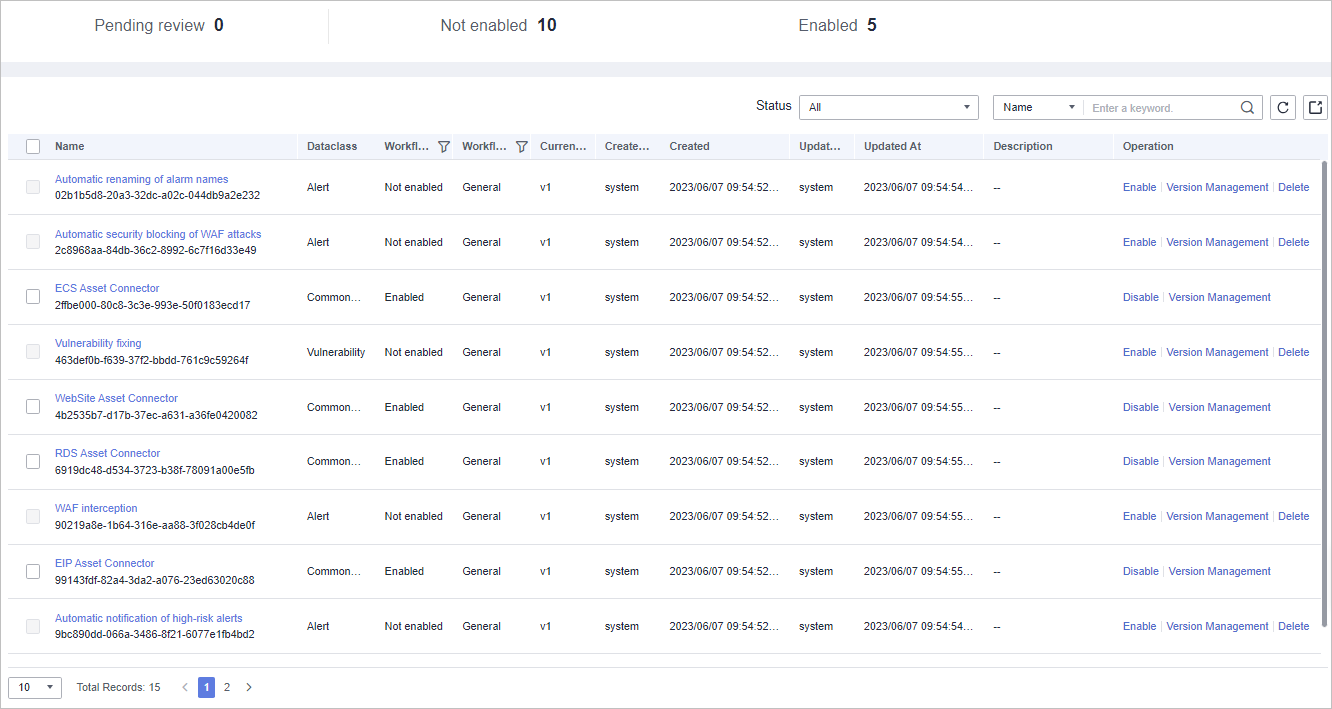
- The numbers of Pending review, Not enabled, and Enabled workflows are displayed above the workflow list.
- View information about existing workflows in the workflow list.
If there are many workflows displayed, use filters to search for a specific one.
Table 1 Workflow parameters Parameter
Description
Name
Workflow name
Dataclass
Data class corresponding to a workflow.
Workflow Status
Current status of a workflow. The status can be Enabled or Disabled.
Workflow Type
Current type of a workflow.
Current Version
Current version of a workflow.
Created By
User who creates the workflow.
Created
Time when a workflow was created
Updated By
User who modifies the workflow last time.
Updated At
Time when a workflow is last updated.
Description
A description of the workflow.
Operation
You can perform operations such as enabling and managing versions in the Operation column.
- To view details about a workflow, click its name to access its details page.
Exporting Workflows
Workflows in the Enabled state can be exported.
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 4 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. On the displayed page, select the Workflows tab.
Figure 5 Workflows tab

- On the Workflows tab page, select the workflows to be exported and click
 in the upper right corner of the list.
in the upper right corner of the list. - In the dialog box that is displayed, click OK. The system exports the workflows to the local host.
Deleting Workflows
- The workflow is in the Disabled state.
- The workflow does not contain an activated workflow version.
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 6 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. On the displayed page, select the Workflows tab.
Figure 7 Workflows tab

- On the Workflows tab page, locate the row containing the target workflow and click Delete in the Operation column.
- In the displayed dialog box, click OK.
During deletion, all historical versions in the current workflow are deleted by default. Deleted versions cannot be restored.
Disabling a Workflow
- Log in to the management console.
- Click
 in the upper part of the page and choose Security > SecMaster.
in the upper part of the page and choose Security > SecMaster. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace.
Figure 8 Workspace management page

- In the navigation pane on the left, choose Security Orchestration > Playbooks. On the displayed page, select the Workflows tab.
Figure 9 Workflows tab

- In the row containing the target workflow, click Disable in the Operation column.
- In the dialog box that is displayed, click OK.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





