Quickly Adding a Log Alert Model
Scenarios
SecMaster alerts are classified into the following types:
- Raw alerts from cloud services: After alert logs or attack logs of other cloud services are integrated into SecMaster, you can view the corresponding alerts or attacks on SecMaster. For details about the cloud service logs that can be integrated, see Cloud Service Log Access Supported by SecMaster. For details about how to access cloud service logs, see Enabling Log Access. For details about how to view alerts, see Viewing Alert Details.
- Model alerts: You can add query and analysis results to alert models, so that alert models can generate alerts when the conditions are met. For more details, see Overview.
This topic describes how to quickly create alert models for logs.
Prerequisites
Data access has been completed. For details, see Cloud Service Access.
Quickly Adding a Log Alert Model
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - In the navigation pane on the left, choose Workspaces > Management. In the workspace list, click the name of the target workspace. Figure 1 Workspace management page

- In the navigation pane on the left, choose . Figure 2 Accessing the Security Analysis tab

- In the data space navigation tree on the left, click a data space name to show the pipeline list. Click a pipeline name. On the displayed page, you can search the pipeline data. Figure 3 Pipeline data page
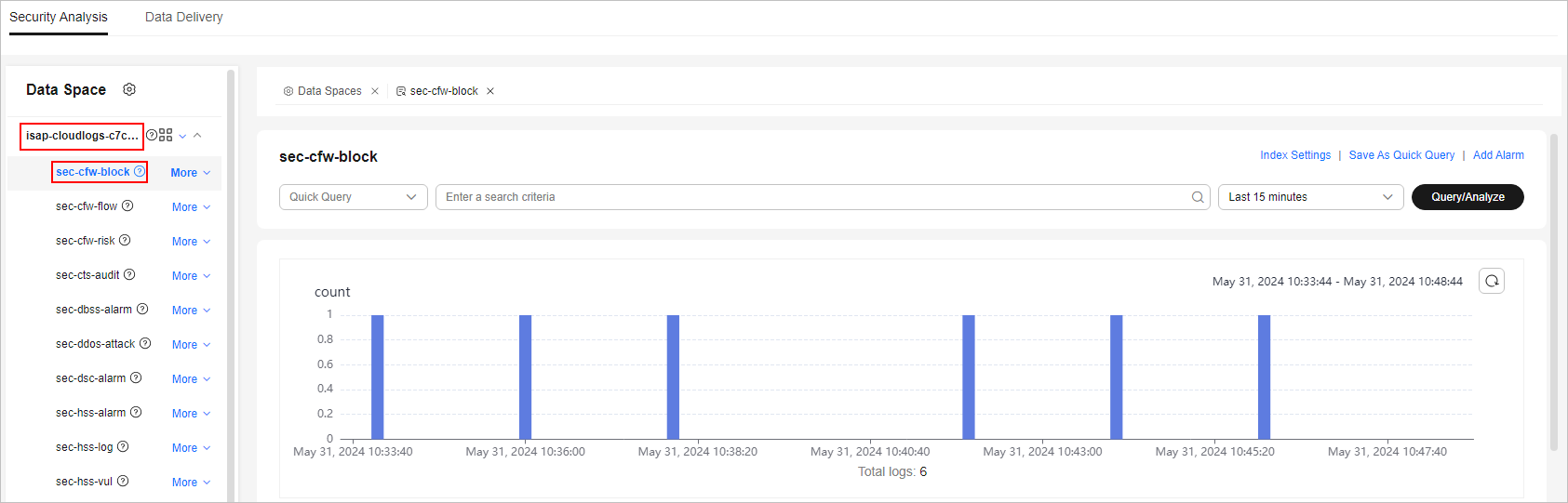
- Enter the query and analysis statement, set the time range, and click Query/Analyze. The query analysis result is displayed.
For details, see Querying and Analyzing Logs.
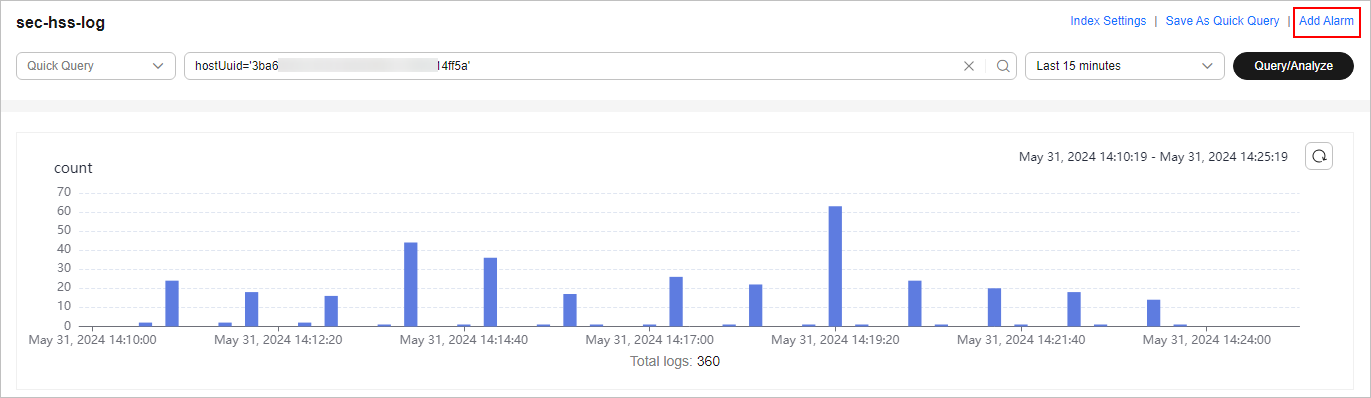
- Click Add Alarm in the upper right corner of the page. The Create Alarm Model page is displayed. Figure 4 Add Alarm
- Configure basic alarm information by referring to Table 1.
Table 1 Basic parameters of an alarm model Parameter
Description
Pipeline Name
The pipeline where the alert model is executed, which is generated by the system by default. No configuration is required.
Model Name
Name of the alarm model. The alarm model name:
- Can contain only letters, digits, spaces, and special characters.
- Can contain only the following special characters: () [] - _ / .
- Cannot contain secmaster, isap, or csb.
Severity
Severity of alerts reported by the alert model. You can set the severity to Critical, High, Medium, Low, or Informational. For details about the severity levels of alerts, see Alert Severity Levels.
Alarm Type
Alarm type displayed after the alarm model is triggered.
Model Type
The default value is Rule model. No configuration is required.
Description
Mandatory. Enter a description for the alarm model. A maximum of 4,096 characters are allowed.
Status
Status of the alarm model, which determines whether to use this model to report alarms. After the alarm model is enabled, an alarm is reported when the trigger conditions defined in the model are met.
You can change the alarm model status after the model is configured.
- After the configuration is complete, click Next in the lower right corner of the page. The page for setting the model logic is displayed.
- Set the model logic. For details about the parameters, see Table 2.
Table 2 Setting the model logic Parameter
Description
Query Rule
Set alert query rules. After the setting is complete, click Run and view the running result.
A query analysis statement consists of a query statement and an analysis statement. The format is Query Statement|Analysis Statement. For details about the syntax of query analysis statements, see Overview.NOTE:If the reserved field is of the text type, MATCH_QUERY is used for word segmentation queries by default.
Query Plan
Set an alert query plan.
- Running query interval: xx minutes/hour/day.
If the running query interval is minute, set this parameter to a value ranging from 5 to 59 minutes. If the running query interval is hour, set this parameter to a value ranging from 1 to 23 hours. If the running query interval is day, set this parameter to a value ranging from 1 to 14 days.
- Time window: xx minutes/hour/day.
If the time window is minute, the value ranges from 5 minutes to 59 minutes. If the time window is hour, the value ranges from 1 hour to 23 hours. If the time window is day, the value ranges from 1 day to 14 days.
- Execution Delay: xx minutes. The value ranges from 0 to 5 minutes.
Advanced Alarm Settings
- Custom Information: Customize extended alert information.
Click Add, and set the key and value information.
- Alarm Details: Enter the alarm name, description, and handling suggestions.
Trigger Condition
Set alert triggering conditions. The value can be greater than, equal to, not equal to, or less than xx.
If there are multiple trigger conditions, click Add and add them. A maximum of five trigger conditions can be added.
If there are multiple trigger conditions, SecMaster scans log data to hit each trigger condition from top to bottom and generates all types of alerts for hit trigger conditions.
Alarm Trigger
The way to trigger alerts for queried results. The options are as follows:
- One alert for all query results
- One alert for each query result
Debugging
Set whether to generate debugging alarms. If the alerts generated by the alert model are used only for model debugging, you are advised to enable this function.
- If Generate debugging alarms is enabled, the value of simulation in the alarm generated by the alert model is true, indicating that the alert is a debugging alert.
- If Generate debugging alarms is disabled, the value of simulation in the alarm generated by the alarm model is false.
Suppression
Specifies whether to stop the query after an alert is generated.
- If Suppression is enabled, the query stops after an alert is generated.
- If Suppression is disabled, the query is not stopped after an alert is generated.
- Running query interval: xx minutes/hour/day.
- Complete all settings and click Next in the lower right corner of the page to go to the details preview page.
- After confirming that the preview is correct, click OK in the lower right corner of the page to confirm the configuration.
- After the configuration is complete, choose in the navigation pane. On the available model page, view the created model.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





