Step 4: Add a Security Group Rule
Configure TCP (port 8000) and UDP (ports 7000 to 7100) in the security group inbound rule of the database audit instance to allow the agent to communicate with the audit instance.
This section describes how to configure TCP (port 8000) and UDP (ports 7000 to 7100) for a security group.

You can configure security group rules before installing an agent.
Prerequisites
The database audit instance is in the Running state.
Adding a Security Group Rule
- For details about how to add an agent, see Step 2.
- Log in to the management console.
- Select a region, click
 , and choose . The Dashboard page is displayed.
, and choose . The Dashboard page is displayed. - In the navigation tree on the left, choose Databases.
- In the Instance drop-down list, select the instance whose security group rule is to be added.
- Record the IP address of the agent node.
Locate the row that contains the target database, and click View Agent in the Agent column. In the Agents area, record the Installing Node IP Address.
Figure 1 Installing Node IP Address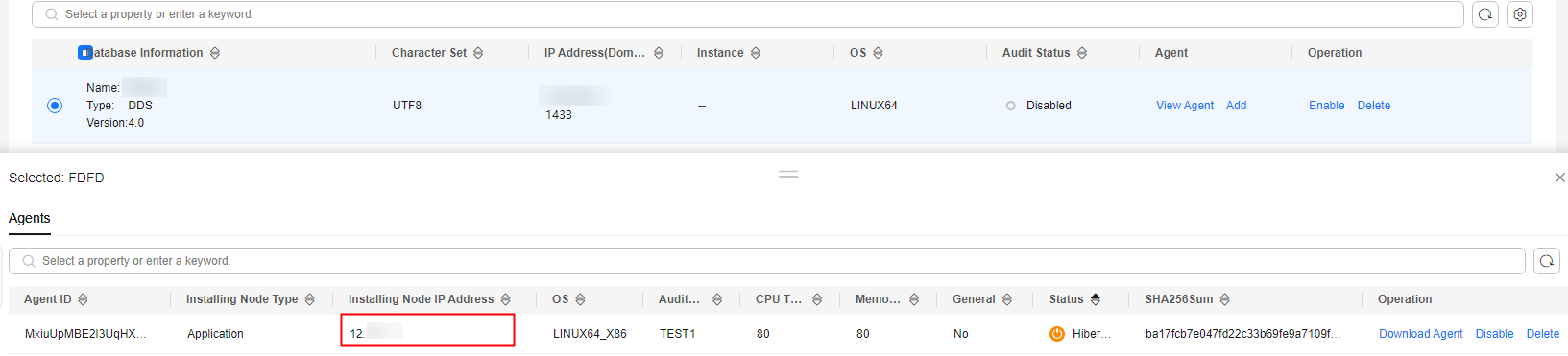
- Click Add Security Group Rule.
- In the displayed dialog box, record the security group name (for example, default) of the database audit instance, as shown in Figure 2.
- Click Go to VPC.
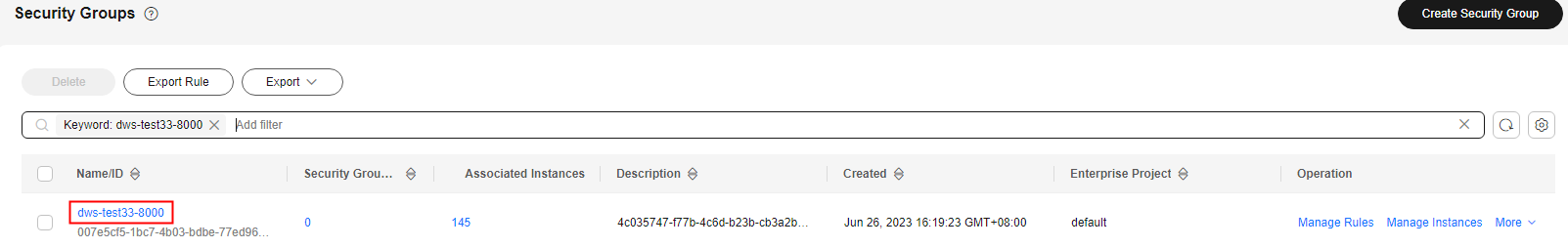
- In the search box above the list, select an attribute or enter a keyword to search for a security group. Click the security group name.
Figure 3 Security group
- Click the Inbound Rules tab.
Check whether TCP (port number 8000) and UDP protocols (port number from 7000 to 7100) are configured in the inbound rules of the security group for the IP address of the installing node.
- If the inbound rules of the security group have been configured for the installing node, go to Enabling database audit.
- If no inbound rules of the security group have been configured for the installing node, go to 20.
- Add an inbound rule for the installing node.
- On the Inbound Rules tab, click Add Rule.
Figure 4 Adding rules

- In the Add Inbound Rule dialog box, add TCP (port number 8000) and UDP protocols (port number from 7000 to 7100).

The source can be an IP address, an IP address segment, or a security group. Examples:
- IP address: 192.168.10.10/32
- IP address segment: 192.168.52.0/24
- All IP addresses: 0.0.0.0/0
- Security group: sg-abc
Figure 5 Add Inbound Rule dialog box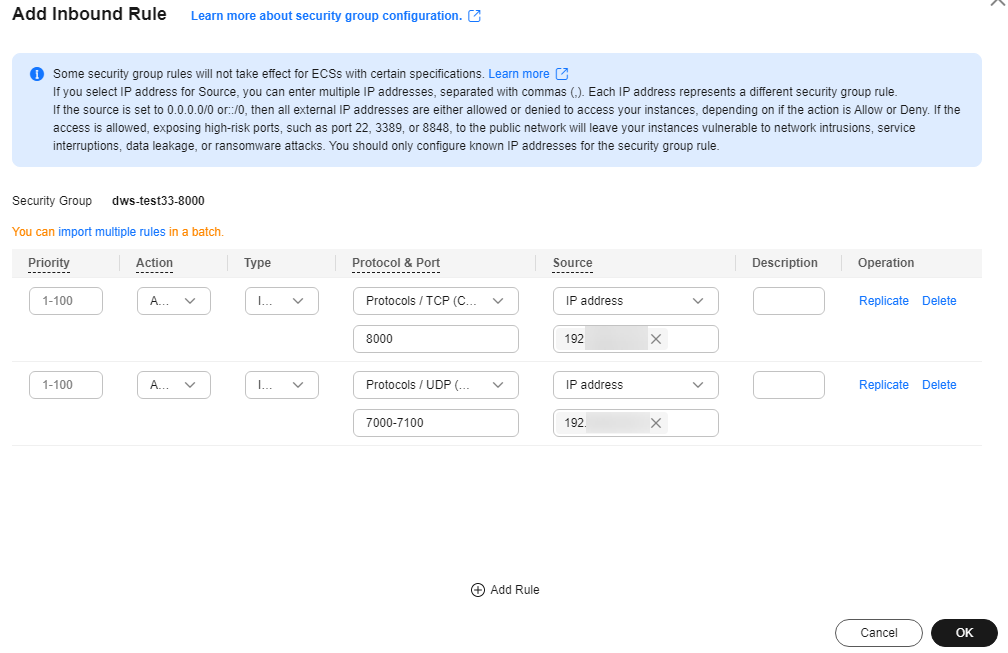
- Click OK.
- On the Inbound Rules tab, click Add Rule.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot






