Halaman ini belum tersedia dalam bahasa lokal Anda. Kami berusaha keras untuk menambahkan lebih banyak versi bahasa. Terima kasih atas dukungan Anda.
- Service Overview
- User Guide
-
FAQs
-
Product Consulting
- What Does SA Do?
- Why Is There No Attack Data or Only A Small Amount of Attack Data?
- What Is the Data Source of Situation Awareness?
- How Do I Get Information About the Most Vulnerable Assets?
- What Are the Dependencies and Differences Between SA and Other Security Services?
- What Are the Differences Between SA and HSS?
- Why Cannot the Total ECS Quota Be Less Than the Number of Existing ECSs?
- Can SA Be Used Across Accounts?
- How Do I Update My Security Score?
- How Do I Handle a Brute-force Attack?
- How Do I Assign Operation Permissions to an Account?
- How Do I Handle the 403 forbidden Error Reported by SA?
- Why Is the Event Data in SA Inconsistent with That in WAF and HSS?
- What Are Differences Between SA and SecMaster?
- Purchase Consulting
- Regions and AZs
-
Product Consulting
- General Reference
Show all
Copied.
Configuring Alarm Monitoring
You can configure alarm types you want to monitor under the Alarm Monitoring Settings tab. After you complete the configuration, SA detects and pushes only alarms of configured types.
- Currently, you can configure alarm monitoring information in the List Settings, Type and Level Settings, and Alarm Source Settings areas.
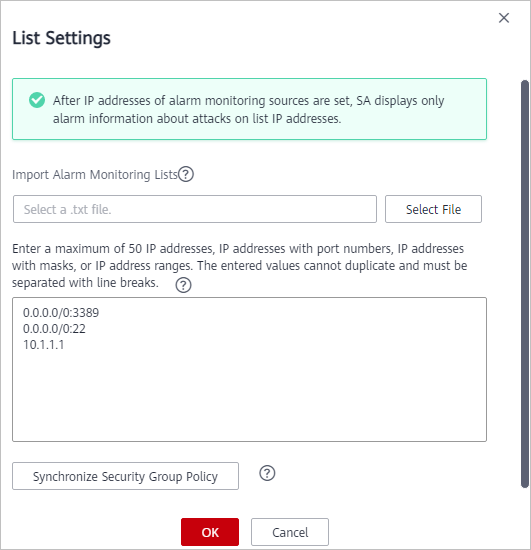
- List Settings: You can set a maximum of 50 pieces of information. The information must be IP addresses, IP addresses with port numbers, IP addresses with masks, or IP address ranges. Each piece of information must be different from others. Every two pieces of information must be separated with a line break.
- Type and Level Settings: You can select Brute-force attack, Web Attack, Exploit, Abnormal behavior, and/or Zombie and specify risk severity, including Critical, High, Medium, Low, and Informational.
- Alarm Source Settings: You can select IDS, IPS, DDoS, HSS, and WAF as your alarm sources.
- After alarm monitoring settings are completed, only the alarms that meet the configured conditions are listed on the Threat Alarms page. The alarm monitoring settings take effect only for alarms generated after the settings are completed.
- By default, no alarm monitoring settings are configured, so SA monitors attacks on all ports and IP addresses of assets and displays threat alarms of all assets across your account.
Constraints
- Select at least one alarm type and one alarm risk severity for each alarm type. Otherwise, the alarm monitoring settings will not work.
- Select at least one alarm source. Otherwise, the alarm monitoring settings will not work.
Prerequisites
Your professional edition SA is available.
Procedure
- Log in to the management console.
- Click
 in the upper left corner of the page and choose Security & Compliance > Situation Awareness.
in the upper left corner of the page and choose Security & Compliance > Situation Awareness. - In the navigation pane on the left, choose Settings > Notifications. On the displayed page, choose Alarm Settings > Alarm Monitoring Settings.
- Configure an alarm monitoring list.
In the List Settings area, click Configure in the Operation column and complete configuration in the displayed dialog box.
To set the alarm monitoring source list, perform the following steps:- Import a monitoring list.
Click Select File and select the target file in TXT format. The selected file is displayed in the text box.
- Enter required IP addresses, IP addresses with port numbers, IP addresses with masks, or IP address ranges in the text box.
If you enter 0.0.0.0/0:3389, 0.0.0.0/0:22, and 10.1.1.1 in the text box, SA only displays the alarm information of attacks to these objects. Figure 1 shows an example.
- Synchronize security group policies.
Click Synchronize Security Group Policy to synchronize security group policies into the text box of List Settings. After the synchronization is complete, the objects to be monitored are automatically displayed in the text box.
- Click OK.
- Import a monitoring list.
- Select the alarm monitoring type and risk severity.
In the Type and Level Settings area, select the notification items and alarm risk severity options of the alarm types you want to monitor. For unselected Notification Item and Risk Severity, SA will stop monitoring related alarm types.
SA then monitors the alarm information of the selected threat types and risk severity options.Figure 2 Selecting the notification items and alarm risk severity options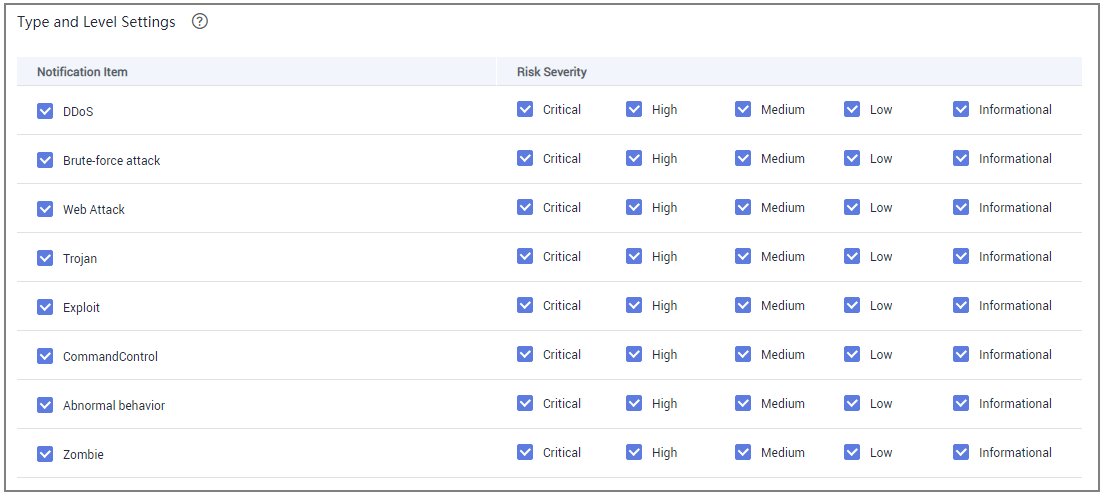
- Set the alarm sources.
In the Alarm Source Settings area, select the Notification Items.
SA then monitors the alarm information from the selected options.
Figure 3 Selecting notification items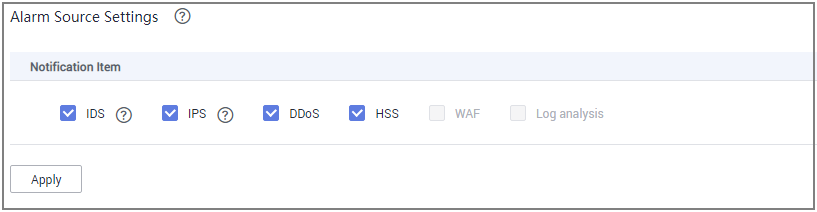
- Click Apply. It takes 3 to 5 minutes for the alarm monitoring settings to take effect.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot