Meeting Database Audit Compliance Requirements
To meet compliance requirements, DBSS allows you to configure the retention period for audit logs, audit reports, and privacy audit logs
Configuring Audit Log Retention Duration
According to relevant audit laws and regulations, audit logs must be retained for at least half a year. DBSS automatically predicts whether the remaining storage space of the audit instance meets the compliance requirements. If the remaining storage space is insufficient, a message is displayed.
If the message shown in Figure 1 is displayed, enable automatic backup. For details, see Automatically Backing Up Database Audit Logs.
If automatic backup is enabled, set Backup Period to Hourly.
If the total size of backup files generated every day is less than 50 MB, you are advised to select Daily.
Configuring Audit Reports
To check whether compliance requirements are met in a timely and accurate manner, you are advised to enable audit report for schedule tasks.
You are advised to configure reports as shown in Figure 2.
Locate a report and click Schedule Task in the Operation column. For more information, see Table 1.
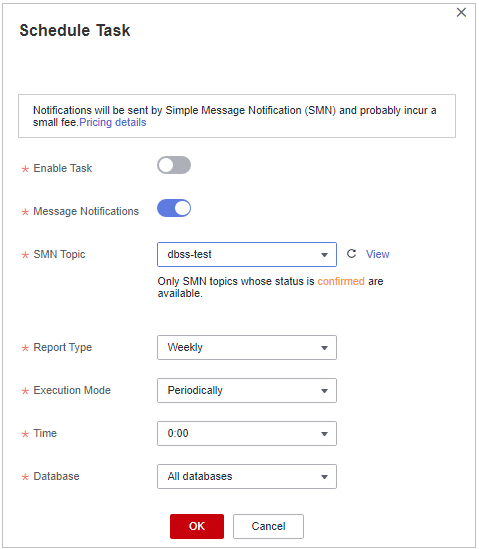
|
Parameter |
Description |
Example Value |
|---|---|---|
|
Enable Task |
Whether to start the current task.
|
|
|
Message Notifications |
Whether to send a notification after a report is generated.
|
|
|
SMN Topic |
If Message Notifications is enabled, select a message notification topic. |
- |
|
Report Type |
Select the frequency for generating reports.
|
Weekly |
|
Execution Mode |
Number of times a scheduled task is executed.
|
Periodically |
|
Time |
Select an execution time, which can only be the top of an hour. A task will be automatically executed after being created. You are advised to select off-peak hours, for example, in the early morning. |
2:00 |
|
Database |
Select the database where the task is to be executed. You can select all databases or a specified database. |
All databases |
Configuring Privacy Data Protection
The SQL request statements and result sets in audit logs may contain users' privacy data. Therefore, you are advised to enable privacy data protection for audit logs.
Configure the following functions to meet privacy data compliance requirements:
- Toggle on Mask Privacy Data. Privacy data in audit logs is masked for storage.
- Toggle off Store Result Set. Result sets that contain privacy information will not be stored in audit logs.
- Enable all privacy protection rules.

Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot













