Viewing Policy Scanning Results
Scenarios
On the Policy Check page, you can view the overall check result of subscribed security compliance packs and the check result of each cloud service.
The policy check is automatically performed at 01:30 every day and the check result is generated.
Prerequisites
You have subscribed to the security compliance packs. For details, see Subscribing to or Unsubscribing from a Compliance Pack.
Viewing Policy Scanning Results
- Log in to the SecMaster console.
- Click
 in the upper left corner of the management console and select a region or project.
in the upper left corner of the management console and select a region or project. - Click
 in the upper left corner of the page and choose Security & Compliance > SecMaster.
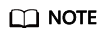
in the upper left corner of the page and choose Security & Compliance > SecMaster. - In the navigation pane on the left, choose . The Policy Check page is displayed.
Figure 1 Policy Check page
- View policy check result.
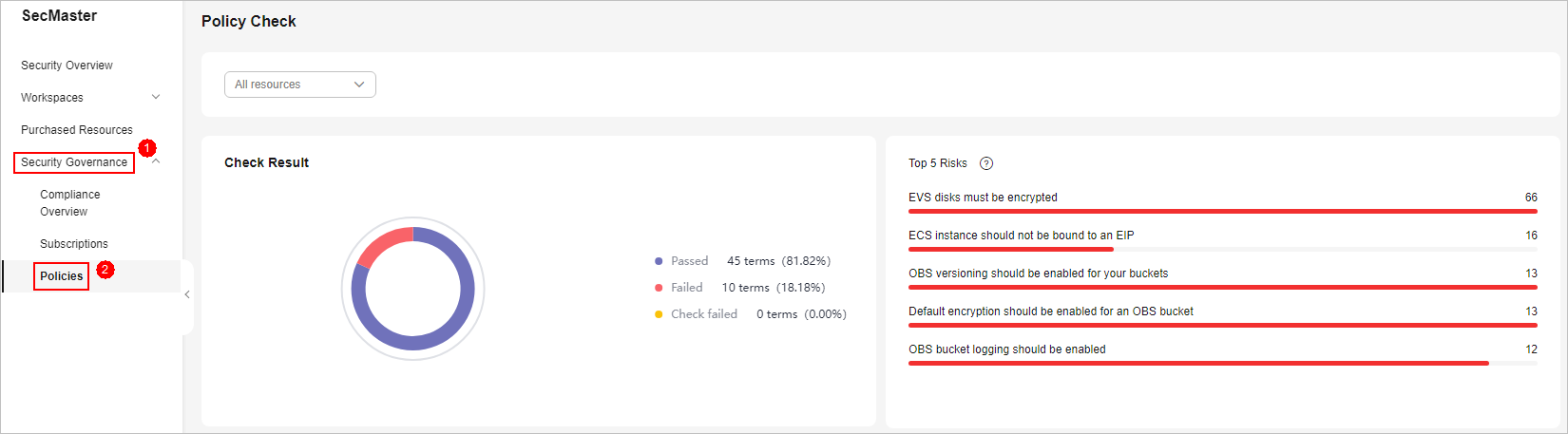
Figure 2 Policy check
- By default, the check status of all resource policies displayed.
- Check result: overall pass rate, passed policies, failed policies, and check failures.
- Top 5 risks: Top 5 policies with the most failures.
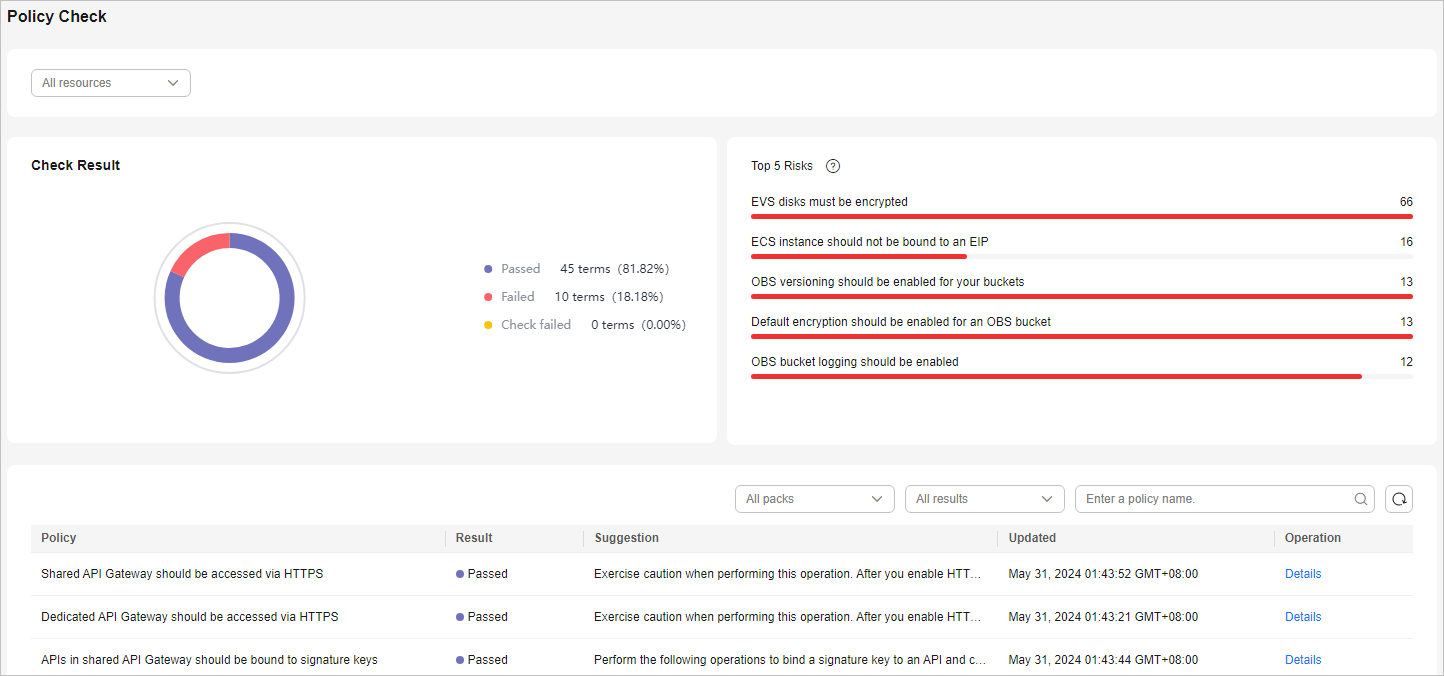
- To view the check result of all policies of a resource, select the resource from the filter box in the upper part.
Figure 3 Selecting a resource
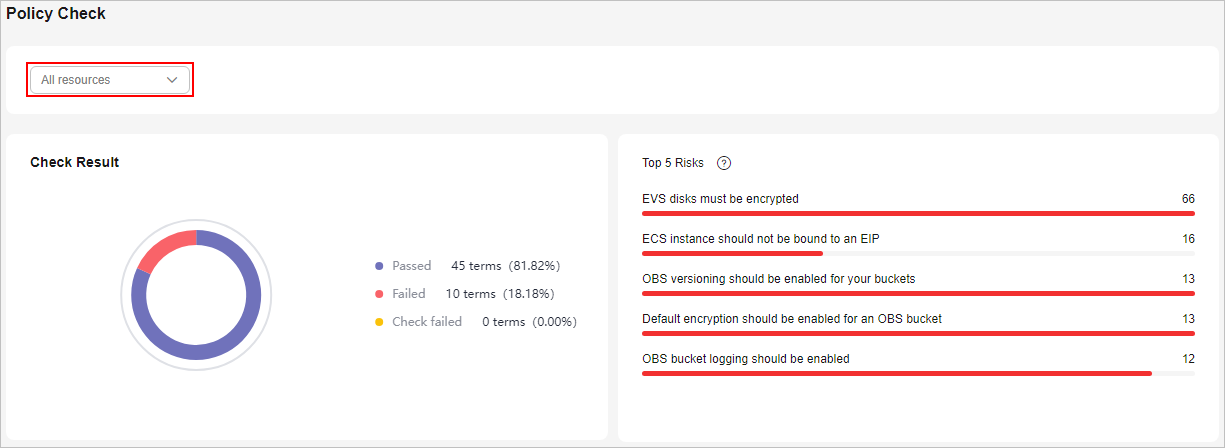
- To view the scanning status of all resources in a policy, select the corresponding compliance pack in the upper part of the table.
You can also filter the results by result type or policy name.
Figure 4 Selecting a compliance pack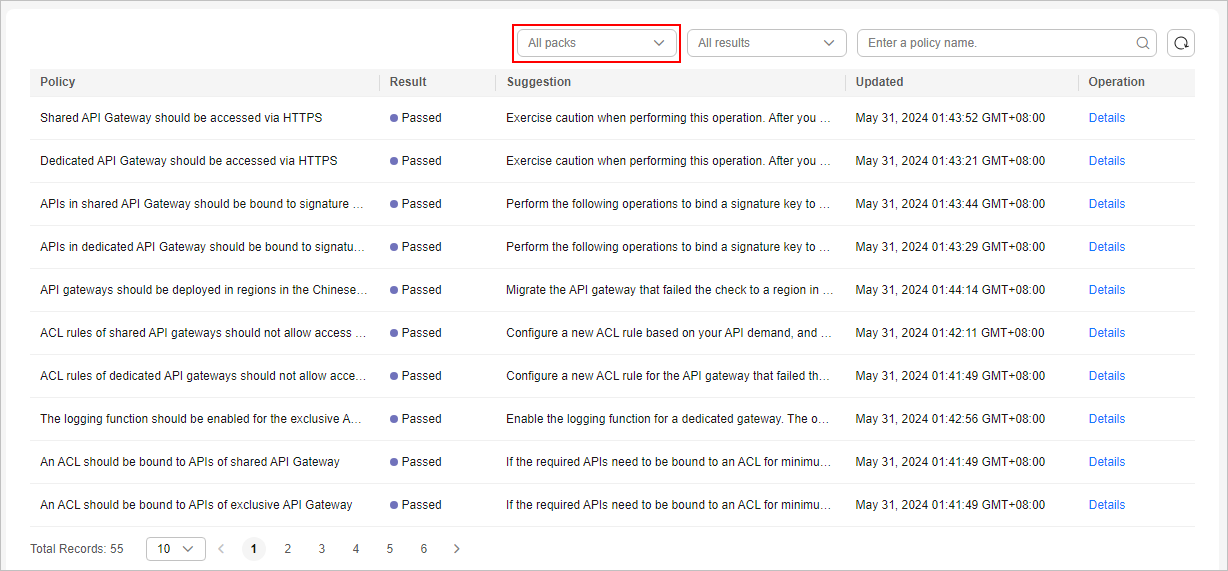
- To view the check result of a policy over a resource, select the corresponding resource from the filter box in the upper part, and then select the corresponding compliance pack in the upper part of the table.
- By default, the check status of all resource policies displayed.
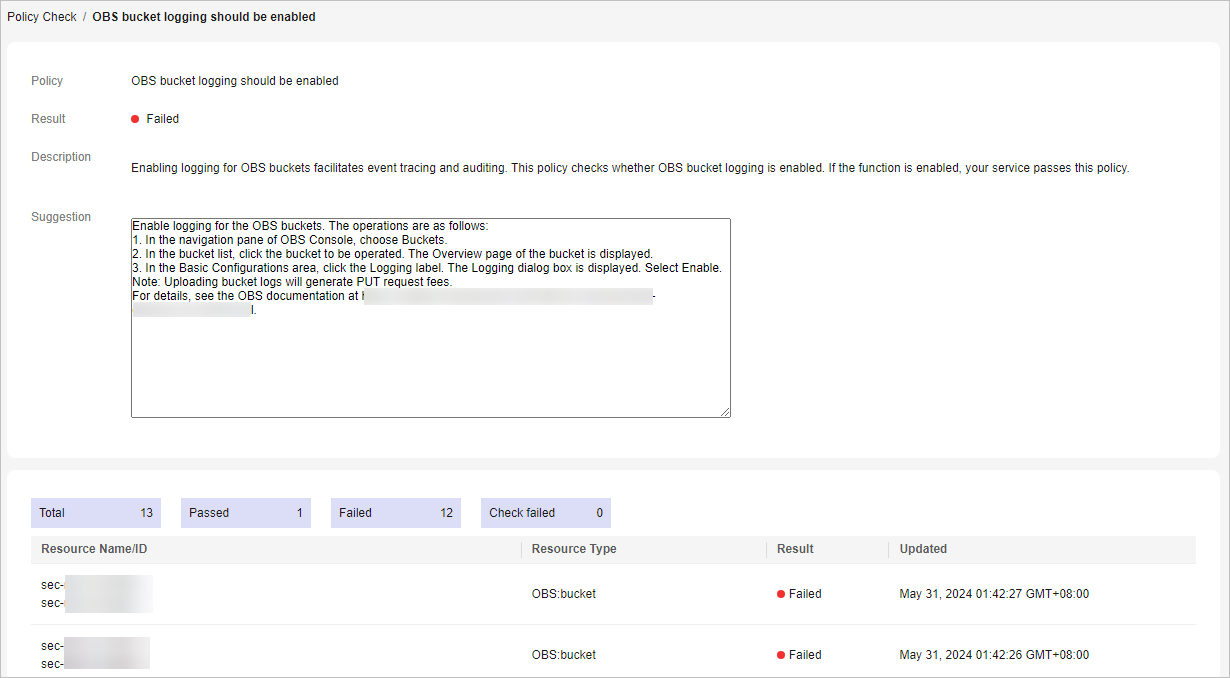
- In the policy table, click Details in the Operation column of a policy to go to the policy check result page and view improvement suggestions.
Figure 5 Details of a check
SecMaster automatically scans the resources at 01:30 a.m. every day and generates the scanning results.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot





