Creating a User Group and Assigning the Anti-DDoS Access Permission
This section describes IAM's fine-grained permissions management for your Anti-DDoS resources. With IAM, you can:
- Create IAM users for employees based on the organizational structure of your enterprise. Each IAM user has their own security credentials, providing access to Anti-DDoS resources.
- Grant only the permissions required for users to perform a task.
- Entrust a HUAWEI CLOUD account or cloud service to perform professional and efficient O&M to your Anti-DDoS resources.
If your HUAWEI CLOUD account does not need individual IAM users for permissions management, skip this chapter.
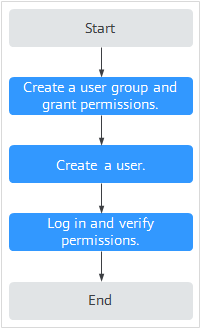
This section describes the procedure for granting permissions (see Figure 1).
Prerequisites
Before assigning permissions to a user group, you should learn about the Anti-DDoS permissions that can be added to the user group, and select the permissions based on the site requirements. For details about the permissions, see Permissions Management.
Process
- Create a user group and assign permissions.
Create a user group on the IAM console and assign the Anti-DDoS administrator permission to it.
- Create an IAM user add it to the user group.
Create a user on the IAM console and add the user to the user group created in 1.
- Log in and verify permissions.
Log in to the management console by using the user created in 2, and verify that the user only has read permissions for AAD.
In Service List on the HUAWEI CLOUD console, select any other services. If a message indicating that the permission is insufficient is displayed, the Anti-DDoS administrator permission takes effect.
Feedback
Was this page helpful?
Provide feedbackThank you very much for your feedback. We will continue working to improve the documentation.See the reply and handling status in My Cloud VOC.
For any further questions, feel free to contact us through the chatbot.
Chatbot